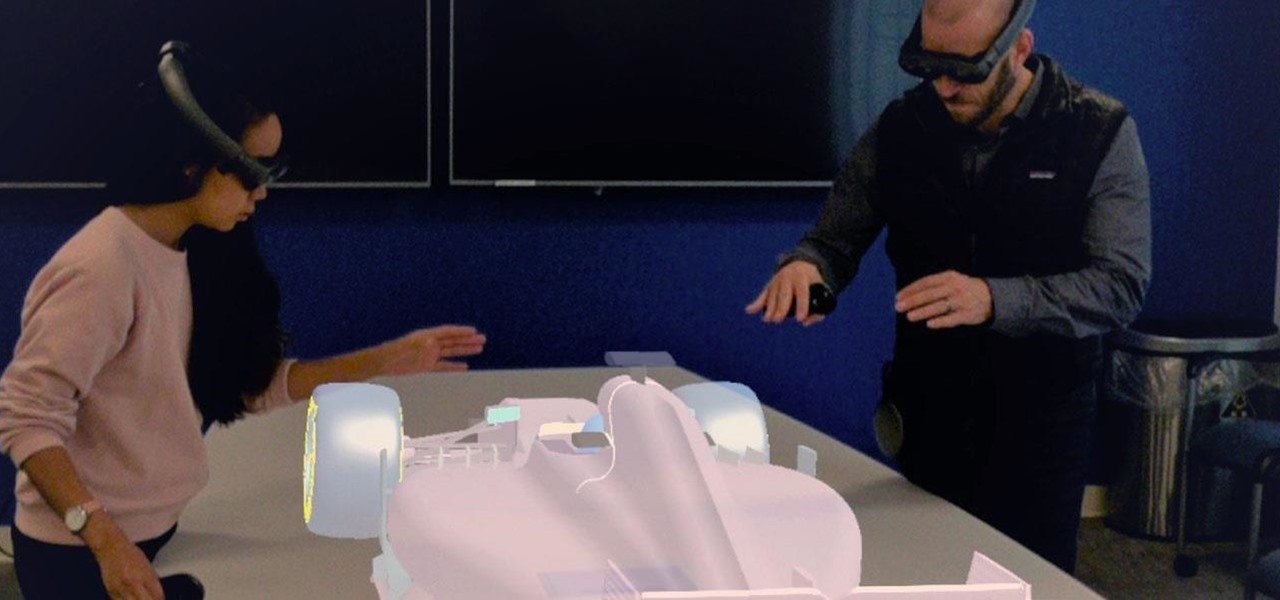
With HoloLens and its enterprise-focused software offerings, Microsoft continues to make an impression on companies looking to adopt augmented reality, with Toyota Motor Corporation among the latest.

With barely a whisper of augmented reality during the first day of its developer's conference, Samsung came out swinging on day two with the introduction of its version of the AR cloud and a partnership with Wacom that turns Samsung's S-Pen into an augmented reality magic wand.

With the iPhone XS, XS Max, and XR, Apple introduced dual-SIM capabilities to iOS, made possible by eSIM technology. If you recently picked up one of these three new iPhones and need to utilize your eSIM while traveling abroad, you might want to take a look at the data plans offered by GigSky.

In the waning days of October, at the Innovation Tokyo 2018 conference, attendees got their hands on some of the new augmented reality experiences that Niantic is working on through its Real World Platform.

Have you ever browsed through Lenses on Snapchat and got bummed out when the app recommends that you "try this with a friend" and you're all alone? Well, now you can take AR snaps with your cat!

Adding another arrow to its quiver of augmented reality acquisitions, Apple has reportedly acquired Spektral, a computer vision company with technology for real-time compositing (otherwise know as the "green screen" technique in broadcast TV and film).

Departing from the long string of entertainment-focused partnerships released in recent weeks and months, a new, enterprise-focused Magic Leap app has finally emerged in the form of Onshape.

The latest business move by Magic Leap could result in a significant boost to its spatial computing platform's performance and headset design.

While many of the latest content partnerships announced by Magic Leap appear to lean towards entertainment and gaming, a new partnership with medical technology provider Brainlab has Magic Leap getting down to more serious business.

Despite Huawei's ongoing battle with the US government, the Chinese company has continued to release phones in the US under its Honor brand. The Honor X series has been consistently released for several years, offering midrange specs at ridiculously low pricing, and the Honor 8X is no exception.

Snapchat has officially unveiled its Visual Search service for Amazon (teased a month ago), a tool the company began testing on Monday.

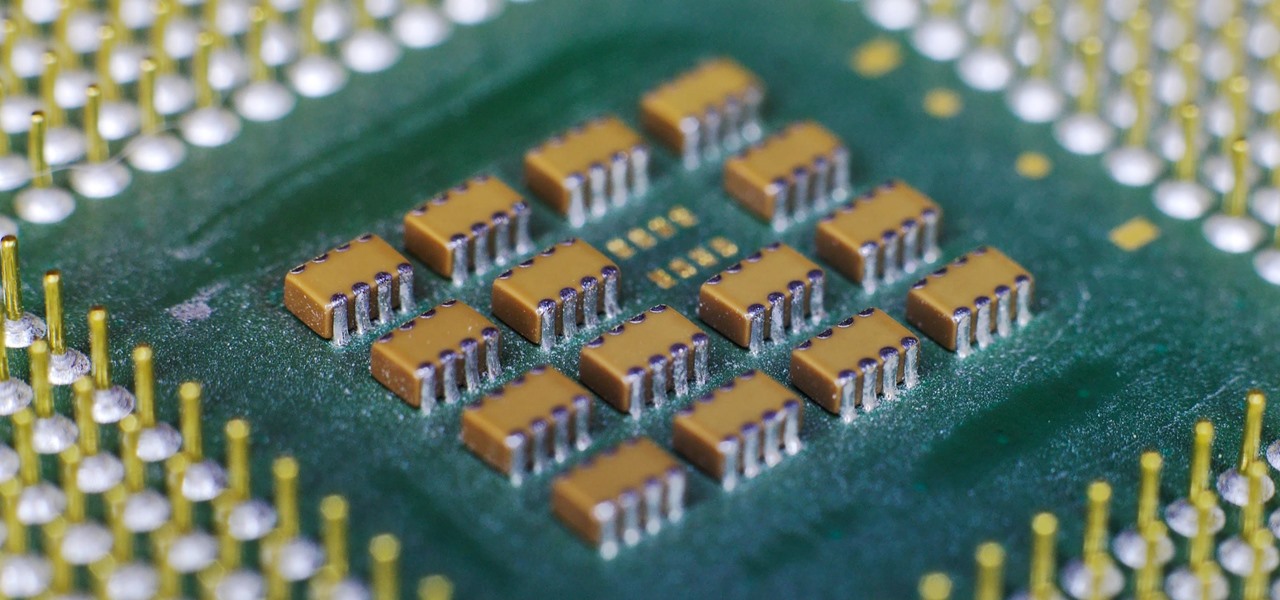
Apple often cites its tight integration of hardware and software for its success. Startup Illumix is looking to do the same thing for AR gaming by building an AR platform for its apps.

A simple security flaw can allow an attacker to gain a strong foothold with little effort on their part. When a web application permits remotely hosted files to be loaded without any validation, a whole can of worms is opened up, with consequences ranging from simple website defacement to full-on code execution. For this reason, RFI can be a promising path to obtaining a shell.

Better known among consumers for its virtual reality apps, Jaunt is now pivoting toward solutions for augmented reality developers.

After a series of hints revealed by CEO Rony Abovitz via Twitter, Magic Leap looks like it is ready to launch Magic Leap One on Thursday at 8:08 a.m. ET.

With the rise of website encryption (TLS), sniffing passwords from network activity has become difficult. However, it's still possible to quietly exfiltrate a target's network traffic in real time to extract passwords and sensitive information. Pertaining to macOS, there are two methods for retrieving traffic from a backdoored Mac.

When you drive along the deceptively sedate streets of Silicon Valley, there are few hints that all those nondescript office parks and low-rise buildings contain the very future of the planet, but they really do. On a recent trip to tech's epicenter, I found that out firsthand when I got to visit the offices of Meta, the startup that produced the Meta 2 augmented reality headset.

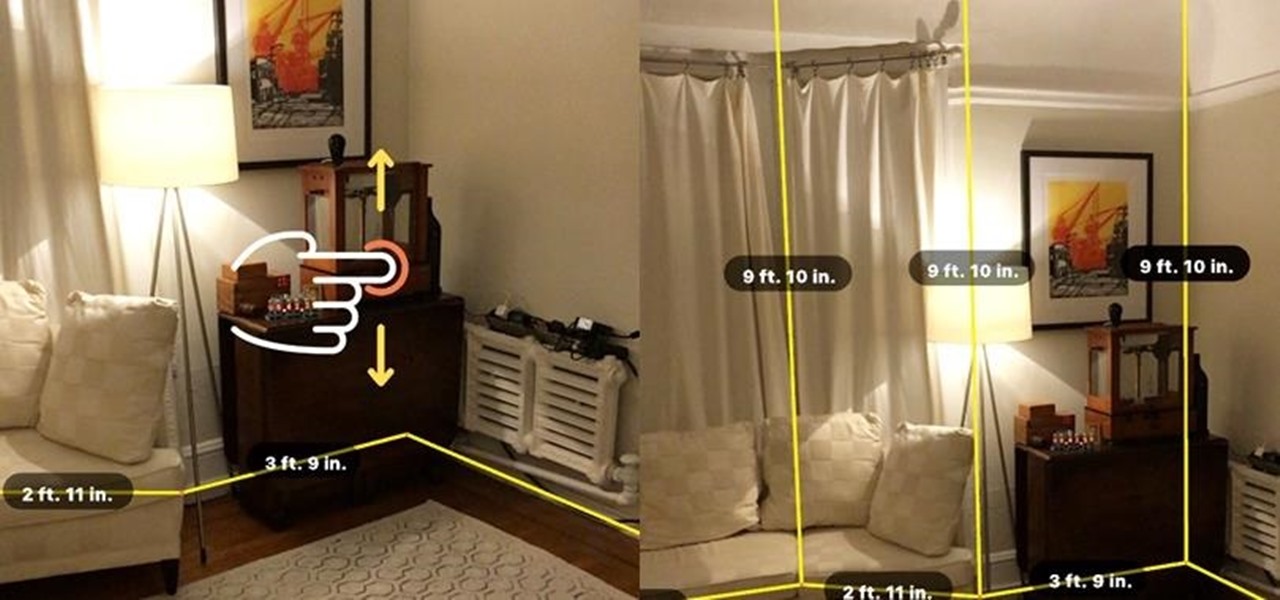
With developers chomping at the bit to play with ARKit 2.0, Unity has updated its ARKit plugin to enable access to the new augmented reality superpowers of the toolkit.

Its official: On May 8, T-Mobile finally released the Android Oreo update for the LG V30 and V30+. Now, every major US wireless carrier has pushed the update. For me, this update is a big deal. Not only does Android Oreo bring some new tools and features, but LG has also included a few additions as well.

French automaker Renault is tapping into the promotional machine for Solo: A Star Wars Movie by deploying an AR experience through Shazam that's triggered via synergistic advertising.

What's black and white, sounds like actress Kristen Bell, and is standing in your living room talking to your kids right now? Don't worry, that's just Genius the Panda, an augmented reality character from the Yakables app for iPhones and iPads.

A report from app data firm Sensor Tower reveals that more than 13 million ARKit apps have been installed on iPhones and iPads within the first six months since the toolkit launched with iOS 11.

Mobile augmented reality developer Blippar's mission is to construct a computer vision map the world, with visual recognition of thousands of notable buildings, bridges, castles, holy places. A major step toward that goal has been taken by the company this month with the announcement of its landmark recognition API.

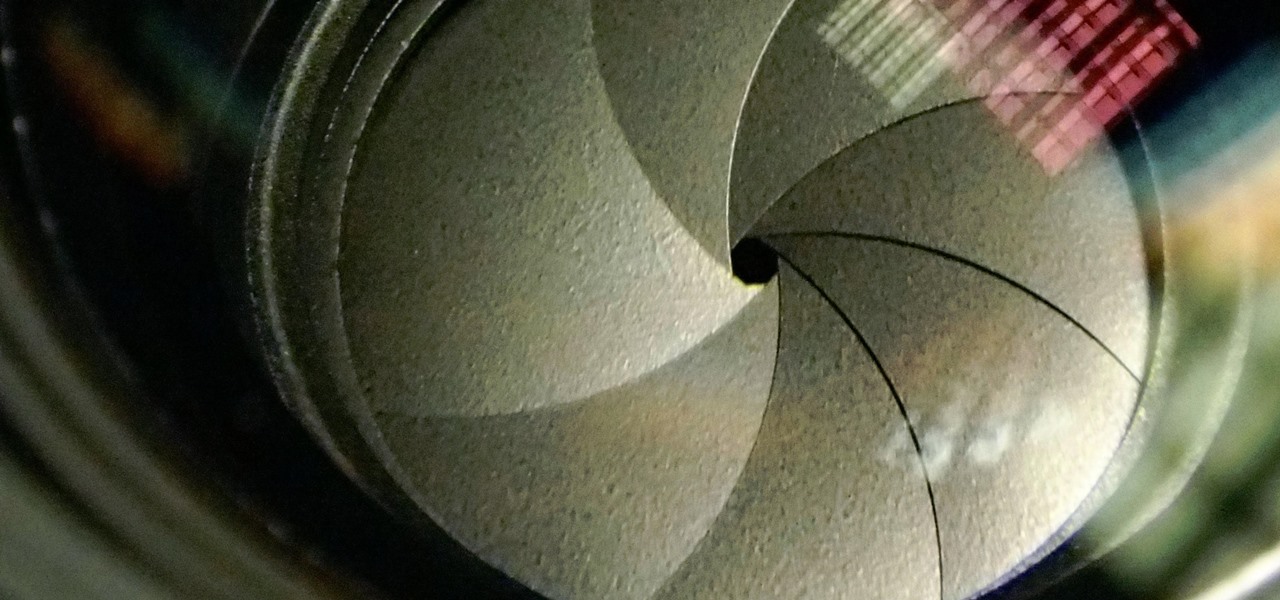
The Galaxy S9 and S9+ have a new camera feature that Samsung is calling "Dual Aperture." On the surface, that may sound like your typical techno-jargon, but it actually has some significant implications for the future of smartphone photography.

The latest and greatest in Qualcomm's long line of mobile processors, the Snapdragon 845, is now set to touch down along with the Galaxy S9 and S9+. And as gorgeous as Samsung's newest flagships are, the processor that powers them under the hood is just as highly anticipated.

Last year, Motorola released their Moto G5 Plus, a fantastic mid-tier machine that earned praise from both reviewers and consumers. Starting at $229, it was well-built and inexpensive considering everything Motorola managed to jam into it. This year, Motorola is looking to replicate the success of their G series with the G6 Plus.

Thanks to iCloud and AirDrop, it's really easy to sync photos between an iPhone and a Mac. But if you have an Apple phone and a Windows computer, this process isn't quite as simple. Thankfully, Microsoft has just released a new iPhone app that makes it a breeze to move photos and videos from your iPhone to your PC.

While the mainstream consumer market waits for cool augmented glasses to arrive from Magic Leap, or maybe even Snap Inc. (Spectacles 2.0??), AR headset maker DAQRI and its business customers are finding new, money-saving and time-saving use cases for the technology today.

If you love to hear yourself talk, you can now enjoy seeing your words materialize in augmented reality with an ARKit-compatible iPhone or iPad.

While Google has a water-resistant phone in the Pixel 2, its CES booth was anything but. According to Tech Crunch, Google had to shut down its two-level outdoor booth once it began to rain at the Las Vegas trade show. Even though Las Vegas is the driest city in the country, Mother Nature always has her idea of fun.

For some, going to the dentist can be a terrifying experience, but a new use of augmented reality could go a long way toward making the trip feel more like it's worth the orthodontic angst.

With today's augmented reality experiences, we can see and hear virtual content, but Ultrahaptics wants you to be able to feel those experiences, too.

With Apple Pay Cash in iOS 11.2, your iPhone potentially becomes the only form of payment you need. Whether you're sending money to a friend via iMessage or paying for your groceries, you can use Apple Pay Cash to complete those transactions. It makes sense, then, that Apple would allow you to add your Apple Pay Cash card to the lock screen, for quick access wherever you are.

A weak password is one that is short, common, or easy to guess. Equally bad are secure but reused passwords that have been lost by negligent third-party companies like Equifax and Yahoo. Today, we will use Airgeddon, a wireless auditing framework, to show how anyone can crack bad passwords for WPA and WPA2 wireless networks in minutes or seconds with only a computer and network adapter.

French manufacturer Renault Trucks is looking to the HoloLens to improve quality control processes with its engine assembly operations.

When a firm like Techstars believes that augmented reality is an attractive industry to invest in, there's a high probability that it's right.

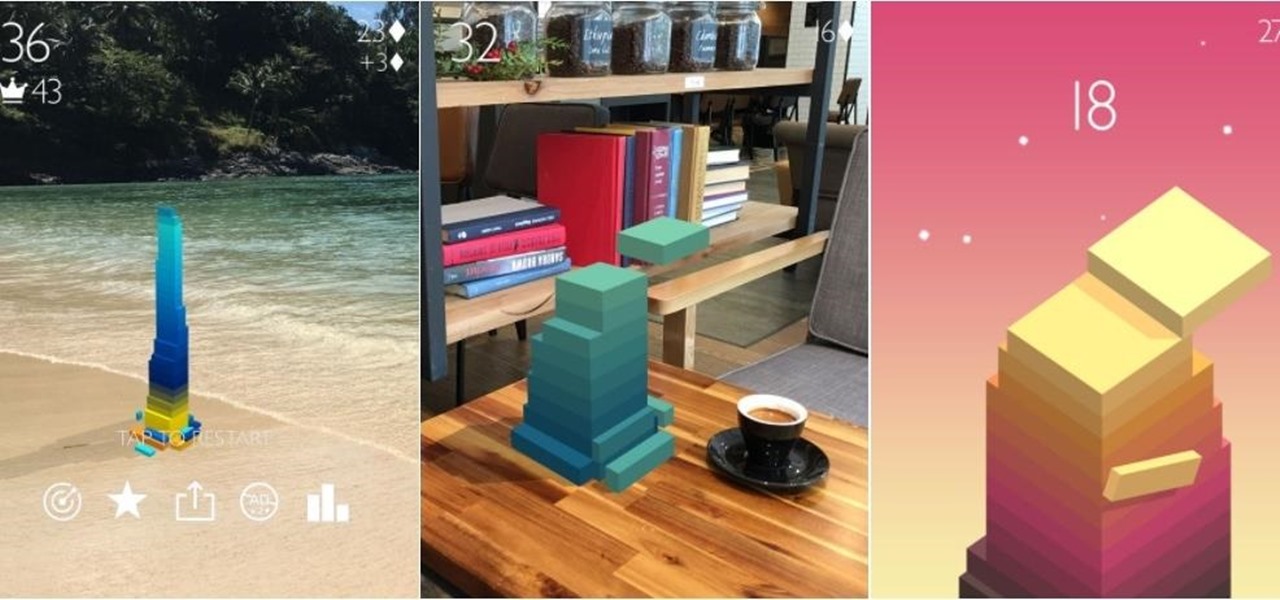
When explaining augmented reality to the uninitiated, Pokémon Go is often cited as an example. For all its popularity, though, many players would recommend disabling the AR capabilities in catching Pokémon.

With Apple ready to unleash ARKit to millions of iPhones and iPads and ARCore on its way to supporting millions of Android devices, is there room in the world for a cross-platform mobile AR platform?

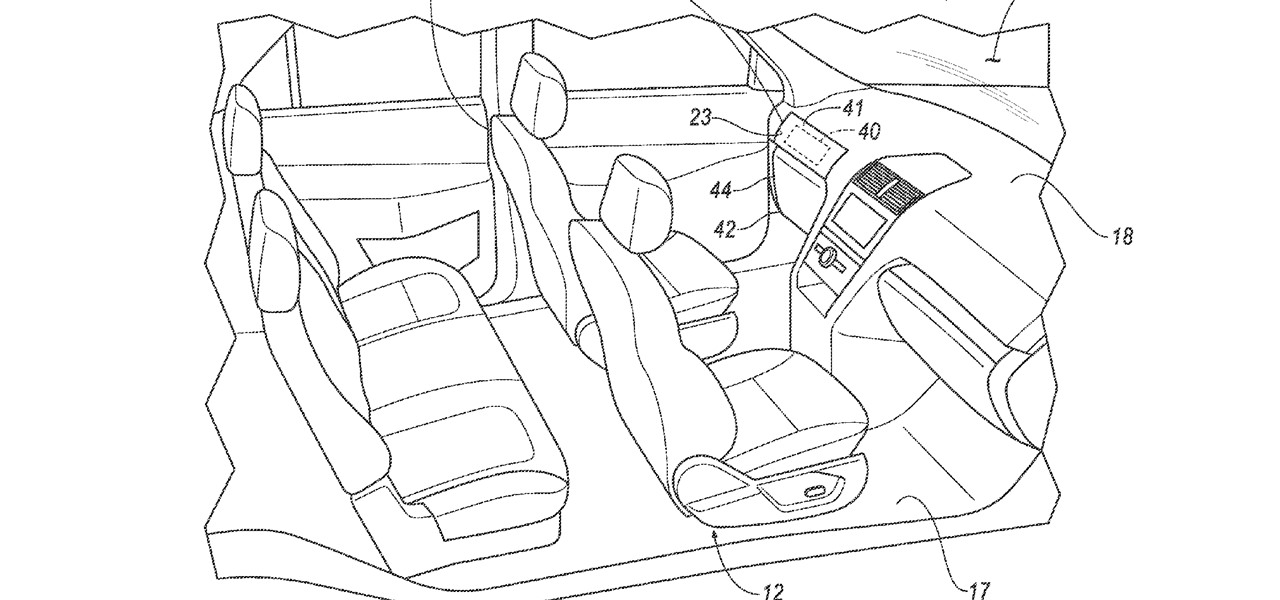
Waymo just received approval on a patent for a push-button console that replaces not only a steering wheel in a car but the brake and gas pedals, too. This reflects Alphabet's driverless arm could remain true to its original mantra of developing cars that pilot themselves without human intervention.

Google largely helped to pioneer the concept of a steering wheel- and pedal-free self-driving experience when it began testing its Firefly pod-like vehicles a few years ago.