
How To: Crochet beret reggae rasta cap
Check out this how-to video to learn how to crochet a beret reggae rasta cap. Wonderhowto.com has many videos in the knitting and crochet genre. Feel free to explore the site.


Check out this how-to video to learn how to crochet a beret reggae rasta cap. Wonderhowto.com has many videos in the knitting and crochet genre. Feel free to explore the site.

Matt covers some lines with a black ...Bg4. He found the first game with analysis on the Kenilworth Chess Club site. Most of the analysis he gave for this game is taken verbatim, but he does mention a couple side variations that you should be curious about. So watch!

If you are afraid to cook fish, this is this demo for you! This has to be the easiest “gourmet” method for fish you have ever seen. This will work for any thin, flaky white fish fillets, but Sole is the traditional choice.We topped the fish with is a simple lemon, caper butter sauce. Chef John will also demo this on the site and you would be well-served to learn this classic and versatile sauce.

Here, Mark Rotblat of Tubemogul shows how simple and easy it is for you to e-mail your tracking reports to yourself and other people.

If you're putting your email address online on your own website, or sites like facebook or myspace, you may want to be a bit clever about it. Check out this tutorial and see how to protect your email address from spam.

Tim Carter shows how to use a table saw and explains its benefits at a project site. Tim's table saw has wheels on it showing the portability of the table saw.

The Citrix Receiver is an app that allows you to securely access your desktop and business applications directly from your Droid Bionic smartphone. You will first need to make an account at the Citrix site, and from there you can decide what you want to have access to on your phone. On the Android app launcher, be sure to pick the Citrix Receiver app so that you can login with your Citrix account.

Skarner is a crystal scorpion style champion in League of Legends that fights in melee range. Take a look at this guide from Riot Games to learn how to use his abilities, including his ultimate--impale, which allows you to drag your opponent with you.

Google is the biggest and best search engine on Earth, and if you are a webmaster and want your website to be a big success it would really behoove you to know as much about how it works as possible. The Google Webmasters series of videos and website were created to teach webmasters, SEO professionals, and others how Google works by answering their questions and giving them insights into how they can best integrate and utilize Google's functionality to improve their business. This video will ...

If you want to mod your XBox 360 at all, you're going to have to learn how to take your precious baby apart. This video will show you how to do so quickly and easily using only two simple tools: a flathead screwdriver and a Torx T-10 screwdriver. Now you can add a bigger hard drive, flash you disc drive and install new firmware that allows you to play burned copies of games, or cut a big friggin X-shaped hole in the side of the case. You can learn how to do all of that on our site by the way.
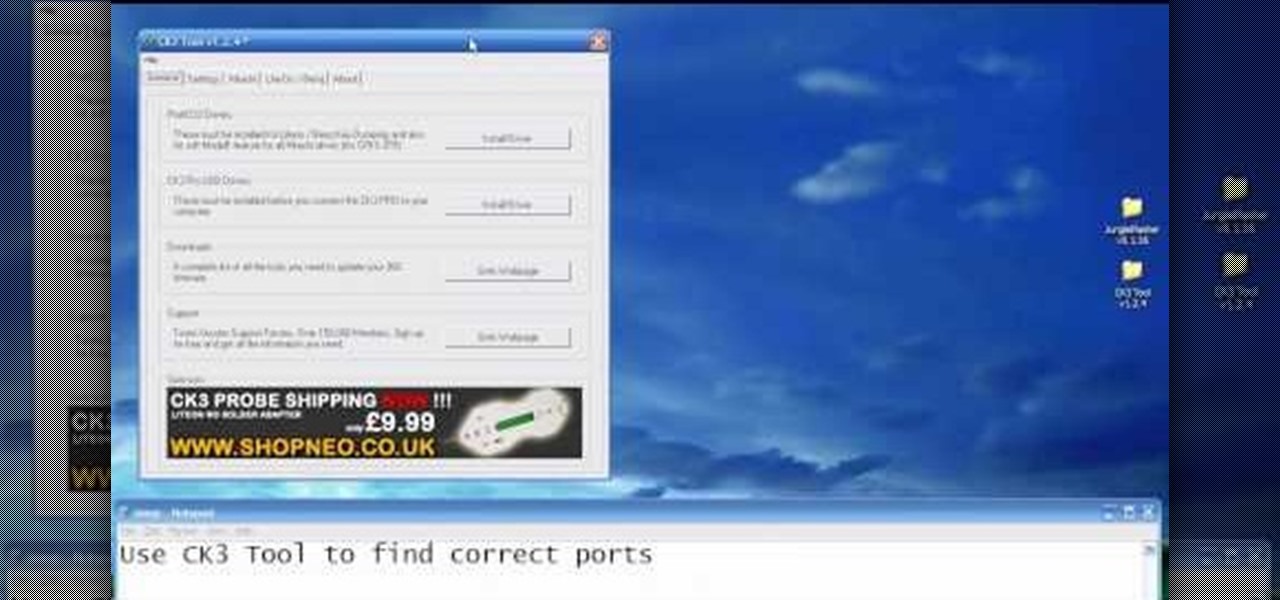
Flashing the disc drive on an XBox 360 and putting new firmware on it so that it can read burned discs is the most challenging and most important part of modding your console. It will allow you to play burned copies of any game and load all sorts of nefarious software onto your hard drive. This video will show you how to do it if your XBox 360 has the Liteon DG-16D2S drive used in many of the consoles.

In this tutorial, learn how to use YouTube's new video editor to combine, slice, edit and add effects to your YouTube clips. You can add music, create montages, cut pieces that you don't want and polish your videos right inside the site. This tutorial, from the experts at YouTube will walk you through everything you need to know.
In this video tutorial, viewers learn how to make custom drawer icons for their stacks in Mac OS X. Users will need to go to the site provided in the video. There users will need to follow the instructions and download the icon sets. Once downloaded, place the icons into the appropriate folders. Users may need to restart the computer. Once restarted, the icons will be neatly overlapped in drawer icons. To add a folder to Stack, simply drag it to the dock. This video will benefit those viewers...
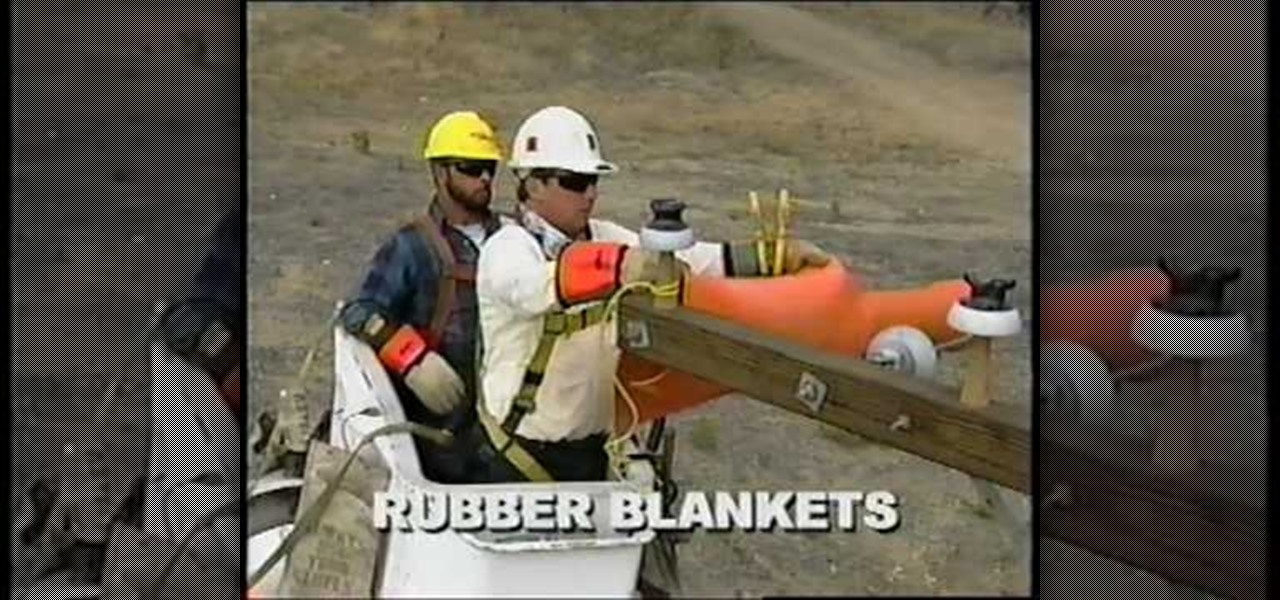
This educational safety video is geared toward public and private utility workers and linemen who need to remove pole tops while dealing with high-voltage electrical cables and electrical insulators. It discusses the proper pole topping removal procedure and demonstrates effective procedures for removal.

Creating a website using Flash CS4 is one of the most challenging and rewarding ways that you can utilize the internet. This video is chapter 5 of a comprehensive series of videos on designing your own website from scratch using Flash CS4. This chapter covers creating and using motion tweens to improve the animations on your site.
In this Computers & Programming video tutorial you will learn how to make a favicon for your site in Photoshop CS3. A favicon is a little symbol that shows up on url bars and also on browser tabs. Open a new project in Photoshop by pressing ctrl+N. Select height and width to 64 pixels and click OK. Now open the title tool and type in whatever you want. In the video, it is ‘F’. Open the background layer and do a color overlay of black. Now change the color of the title to white so that it ...

This training video will show you easy techniques to monetize fan pages and groups on the social networking site Facebook! To earn money, you must first crate an account on YouTube, then you need to upload a video. Also you have to sign up for Google Adsense, which will allow you to earn money from people clicking on the ads in your video. Then just create a Facebook fan page with a link to your video. Invite all your friends, and let the ball roll! If a video has 1000'000 views, and ONLY 1 i...

What to do if you're lost & freezing in Antarctica? Build a fire to keep warm! Yes, fires can be built successfully in cold and wet conditions with the right tools & preparation. In this eight-part series of short videos, Fitclimb survival instructor Ali teaches how to build a fire in the snow in 15 minutes. You can build this fire with just two tools: a knife and a metal match (magnesium stick). In part one, Ali talks about site preparation and how to choose and prepare the right site for a ...
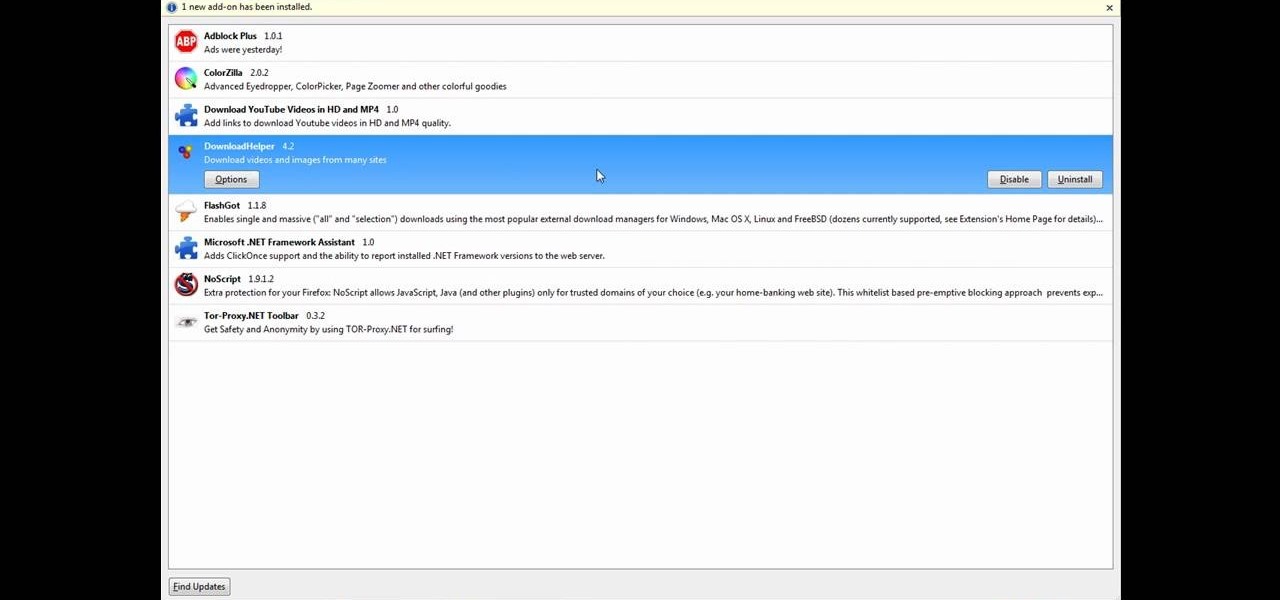
This tutorial will make you think step by step how to add a plug-in (Firefox Add-on) to your Mozilla Firefox browser that will allow you to download videos and music from YouTube and similar sites. The add-on that is used is called Video Downloadhelper. This is a trusted author and a trusted download. To begin this tutorial you will first need Mozilla Firefox and flash. This will enable you to go through the video and help ensure that YouTube will play the video you are trying to download.

Create some cool comic vectored effects! Watch this Illustrator video tutorial to learn how to make some comic styled text. You will learn how to break text down and add gradients. You will also learn how to create a fake 3D effect as well as some stroke options. All of these techniques will come together in the end as we create a comic book cover worthy logo.

The Apple iPod and iPhone are the hottest electronics on the market, so keeping up with the times means keeping up with designs people like. Apple incorporates all kinds of cool images and icons into their products, so learn how to re-create them so you can modify them or get ideas for your own designs. Watch this Illustrator video tutorial to create a gel progress / loading bar-similar to the progress bar found on an iPhone and iPod -- from start to finish.

Increasing the contrast in Photoshop could help when performing this Illustrator technique. This subject: the eyeball. Watch this Illustrator video tutorial to learn how to vector an eyeball in CS3. Vector an aye of a model of your choice using simple techniques that will be useful, not only in vectoring eyes, but tracing techniques that are used for full face and body vectoring and vexeling.

Changing the way the Bridge looks is a personal touch everybody can make to streamline their workflow. Changing layout settings in the bridge is actually quite easy and very helpful for customizing for individual needs. In this video tutorial, see the ways that you can change the Bridge's look and feel to suit your work environment and to free up the space necessary to have a comfortable working window. This video also covers the viewing options given to you by the Bridge to allow for quick a...

If you never used Adobe Bridge before, learn the basics of the Bridge now! Bridge has been around since CS2, and is a file brewing and organizing piece of software, designed to streamline your workflow using Adobe applications. This video tutorial is geared toward all you new Bridge users, with the hopes of getting you firmly situated and comfortable with Adobe Bridge, as well as understand some of the basic features it has to offer.

See how to replace a backup sensor on a Toyota FJ Cruiser. This video shows you step by step replacement of this simple repair. Everyone who owns and FJ Cruiser knows how difficult it can be to judge distance when backing up. Little cars that sit below your line of site which are impossible to see make parallel parking hell. Luckily Toyota added a set of backup sensors to tell you when you’re getting close.

There's a way to get instant access to your most-used websites and webpages on your iPhone, and these shortcuts live directly on your Home Screen. Whatever you need fast, frequent, or more convenient access to, whether it's a vital web document or a web app without a native iOS app, your browser can make it happen.
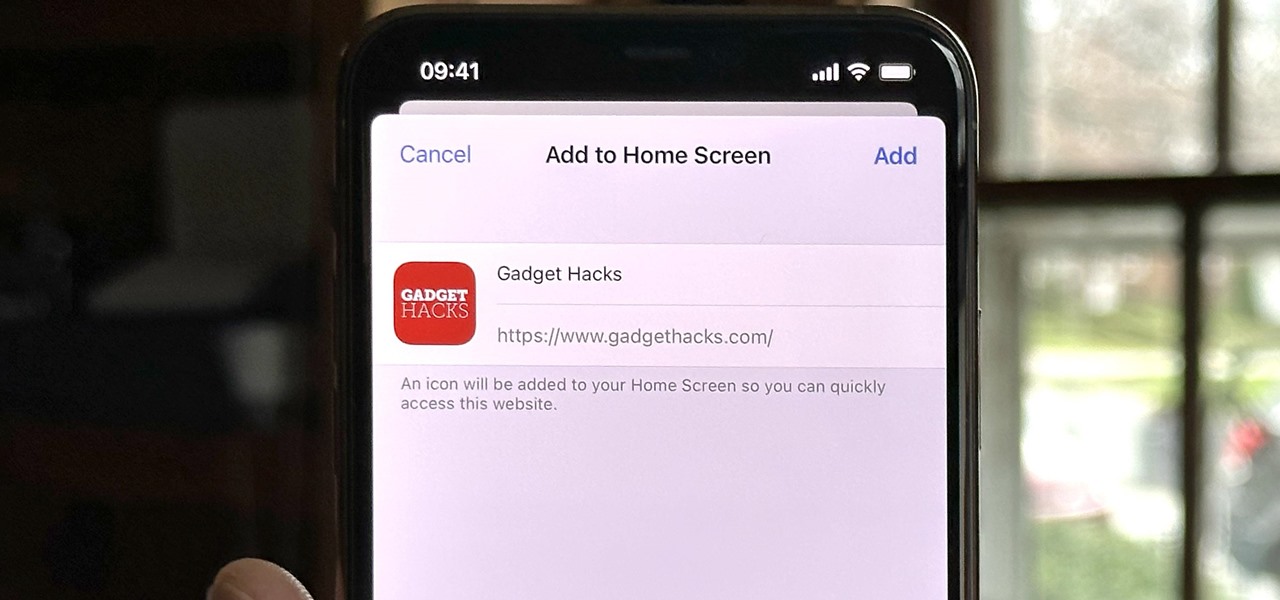
Safari isn't the only web browser on your iPhone or iPad that will let you add icons to your Home Screen for progressive web apps and website bookmarks. Apple gave developers the key to its "Add to Home Screen" feature, and your favorite iOS or iPadOS web browser may already support it.

Whether you want to build your own website for your business, start your new lucrative career in web development, or gain a wealth of projects to add to your portfolio, this course will help you do it. And right now, "The Complete Web Developer Course" is on sale for just $14.99 — a staggering 92% discount off the regular price of $199.
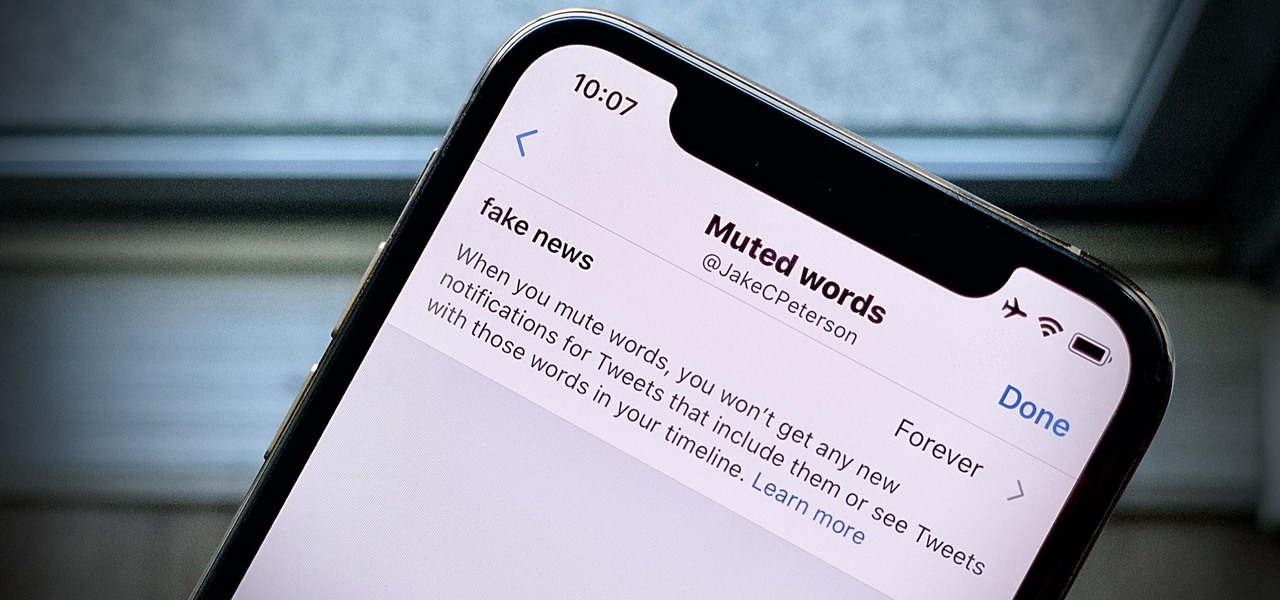
Twitter can be a wonderful place for people to express their emotions and chat with each other in brief. However, it can also be a breeding ground for hateful comments, foul language, and a whole lot of political talk.
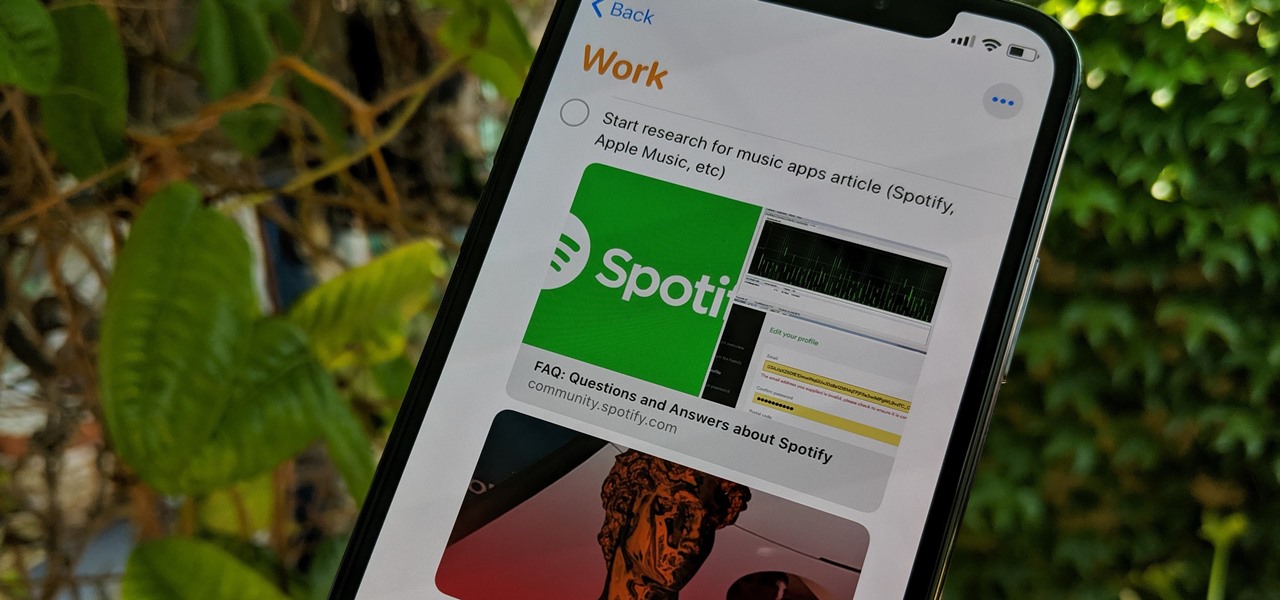
Apple's Reminders app has always been an underrated yet useful productivity tool for iPhone. It's not as powerful as many third-party to-do apps, but it makes it easy to keep track of a few basic tasks, and it's integrated deeply with iOS, macOS, and watchOS. In iOS 13, it's even better since you can now add attachments to your reminders, such as photos, documents, and webpages.

Search engines index websites on the web so you can find them more efficiently, and the same is true for internet-connected devices. Shodan indexes devices like webcams, printers, and even industrial controls into one easy-to-search database, giving hackers access to vulnerable devices online across the globe. And you can search its database via its website or command-line library.

There's always an iPhone in our list of top phones for privacy and security, due in large part to advanced security measures like Face ID, consistent iOS updates, and easy ways to prevent unwanted access and excessive data sharing. However, some of those options actually do the opposite and hinder security. It all depends on how you use your iPhone, but you should at least know everything available.

While there are a variety of privacy-focused search engines available like StartPage and DuckDuckGo, nothing can offer the complete trust offered by creating one's own search engine. For complete trust and security, Searx can be used as free metasearch engine which can be hosted locally and index results from over 70 different search engines.

The microphone in a Windows computer is accessible to most applications running on the device at all times and completely without security limitations. Information gathered from recorded audio conversations taking place in the surrounding area of a compromised computer can be used for social engineering, blackmail, or any number of other reasons.

Screenshots taken from a compromised computer can provide hackers with access to private emails, photographs, and information found in sensitive documents. This data can be used by the attackers to build profiles of a target for social engineering attacks and blackmail or even just to release the information out in the wild.
Tony Parisi, the global head of VR/AR at Unity Technologies, has been passionately working with virtual and immersive spaces for a long time. And while the internet world we live in now is very different than when Parisi was co-authoring VRML (Virtual Reality Modeling Language) — an early attempt at creating 3D environments that would work in a web browser — some of the questions that were assumed answered are being asked again.

Welcome back, my greenhorn hackers! Over the years, I have written many articles here on Null Byte chronicling the many the hacks of the NSA, including the recent hack of the Juniper Networks VPN. (By the way, my speculation in that article has proven to be correct. The NSA did embed a backdoor on those devices.)

Welcome back, my greenhorn hackers! Many new hackers come from a Windows background, but seldom, if ever, use its built-in command-line tools. As a hacker, you will often be forced to control the target system using just Windows commands and no GUI.

Since I first announced the new Null Byte recognition for excellence a few weeks ago, several of you have written me asking, "How can I study for this certification exam, and what material will be covered on the exam?" Now I have an answer for you. The White Hat Hacker Associate (CWA) will cover 14 domains or areas. Everything you need to know is here on Null Byte. There will be no questions that are not covered here on this site, guaranteed.

Recently, I've been experimenting with BeEF (Browser Exploitation Framework), and to say the least, I'm hooked. When using BeEF, you must "hook" the victims browser. This means that you must run the script provided by BeEF, which is titled "hook.js", in the victims browser. Once you've done that, you can run commands against the victims browser and cause all kinds of mayhem. Among these commands, there is an option to use the victims webcam. This is what we'll be doing here today, so, let's g...