In an early morning blog post, Microsoft announced the expansion of the Microsoft HoloLens Agency Readiness Partner Program. This announcement comes on the tail of an expanded HoloLens release over the last few months to many countries outside the initial US and Canada.

Crayon, a free 3D drawing application by the mysteriously named arkalian, showed up in the Windows Store recently, so I gave it a try like I do all new apps for Windows Holographic. Truthfully, I loaded it up not expecting much, but wow, was I wrong. It's a simple idea, but it's executed well enough to make it a truly great experience on the HoloLens.
Meta's long-awaited Meta 2 development kit finally began shipping in late-December last year, after having been delayed about six months. While very few have received a dev kit at this point, some more information about the headset has just been announced; Depth-sensing technology from pmdtechnologies is included in the dev kit headset.

A few days ago, I pulled up the Windows Store on my HoloLens and saw a few new applications. One that caught my attention was Oriental Museum, which lets you explore China's Forbidden City, and the other one is very similar free demo app called Secrets of Ancient Egypt by Link Development.

Visualization is one of the obvious commercial applications for technology such as Microsoft's HoloLens. The ability to see the assets of a project in different scales—from micro to larger-than-life—with a quick air tap will play a large part in the coming augmented reality revolution. Whether the assets are art for a game, interior design, raw financial data, or architecture, data visualization will play an important role in the future. This is due, in part, to our ability to absorb informat...

If you've ever made graphs and charts, you know it can be a struggle to represent a large amount of data. It's something that just doesn't work very well on a flat surface. In virtual and mixed reality, however, the data can exist all around you.

In my last tutorial I very briefly introduced Zanti , but in this tutorial I will start to show its many features. The first step on hacking is recon . You could use Nmap , but the problem with Nmap on Android is that by itself, in order to gain full functionality your phone must be rooted. Thank goodness for a few geniuses in Zanti's dev team whom managed to implant full fuctionality of Nmap in Zanti without rooting your phone. With that being said, boot up your Android phone and lets start ...

Scanners are much too cumbersome to fit in a pocket, but with the use of just one application, you can replace all that bulky hardware with your Android smartphone and take it with you wherever you go. All you need to do is find the scanning app that fulfills your needs. Here are our five favorites that are good for business pros and average joes alike.

Hello guys, its been quite a while since my last post. (sorry for the lack of images)

Developing GUI apps in python is really cool. I ask those who understand the language to help convert some of the command-line or console programs or apps ( I mean programs that are useful to a hacker ) to GUI. I know GUI makes us lazy and not wanna learn but we should all know its fast. Today's tutorial is on p2p chat app I developed last week and decided to share it with the community since its kinda cool.

Welcome back, my hacker novitiates! In the previous two posts in this series, we looked at the basics of buffer overflows. In this post, we will look at one technique for finding buffer overflows. We will try to send random, oversized, and invalid data at a variable to see whether we can make it crash or overflow. This process is known as fuzzing. It is often the first step to developing an exploit, as we need to find some variable that is susceptible to overflowing.

Apple announced the release of their newest Mac OS X version at this year's Worldwide Developer's Conference, and it's called "El Capitan." Like the majestic rock formation it's named after (located within Yosemite National Park), El Capitan promises to emphasize and expand on some of the great features we used on 10.10 Yosemite.

Google recently announced the beta release of a developer tool called ARC Welder for Chrome, which allows developers to run and test their Android apps on any computer with the Chrome browser installed.

Is your Mac starting to feel messy and sluggish after using iOS 8 on your iPhone every day? Even with all of the iOS-friendly features built in to Mac OS X Yosemite, your Mac can still feel kind of "old" in comparison to an iOS device—but it doesn't have to. Using the tips and tricks below, you can easily make your Mac desktop or laptop look and feel like iOS 8 in no time.

Some third-party keyboards, like SwiftKey for example, include a convenient feature that suggests emojis as your type based on the content of what you're saying. Unfortunately, many keyboards, including most stock ones, don't include this function.

Welcome back, my aspiring hackers! Although this article may have been better placed first in this series, I doubt that anyone would have read it when just starting out studying Linux. Now, that you are well into your Linux studies and have some familiarity with how it operates, I'd like to take this moment to explain the philosophy around the Linux operating system.

With the release of the Nexus 5 back in 2013 came the Google Now Launcher, which has become the go-to choice for many Android users, especially those who prefer the Nexus line. With its integration of the Google Now page and the always-listening hotword detection, you'd be hard-pressed to find a more complete and useful launcher.

Thanks to a couple of photoshopped images that made rounds across Twitter last year, iPhone users were duped into thinking that iOS 8 included a security feature that would lock individual apps. Of course, none of it ended up being true, but we covered other features and apps that could accomplish roughly the same thing.

If you've ever attended school or held a job, you're probably well familiar with Microsoft Office, whether you used it or not. It's the most popular office suite available, and has been for some time. Apple does have its own suite of productivity apps (iWork), but Microsoft Office has always been the industry leader for word documents, spreadsheets, and presentations.

Those of us with girlfriends understand that in order for the relationship to run smoothly, you have to keep your woman happy and let her know that you're thinking of her—even when you're not.

Using shortcuts to control the playback of your music on your computer makes life just a little bit easier. Instead of needing to open up an app, we've shown you how to use keyboard shortcuts, a Notification Center widget, and even Siri to control music on your Mac. Now we're going to show you how to use your iPad, iPhone, or iPod touch as a remote control.

WhatsApp is the go-to application for sending a message (or 100) to friends at home and abroad. And the best thing is, the service has remained true to its roots after Facebook acquired the company for $19 billion.

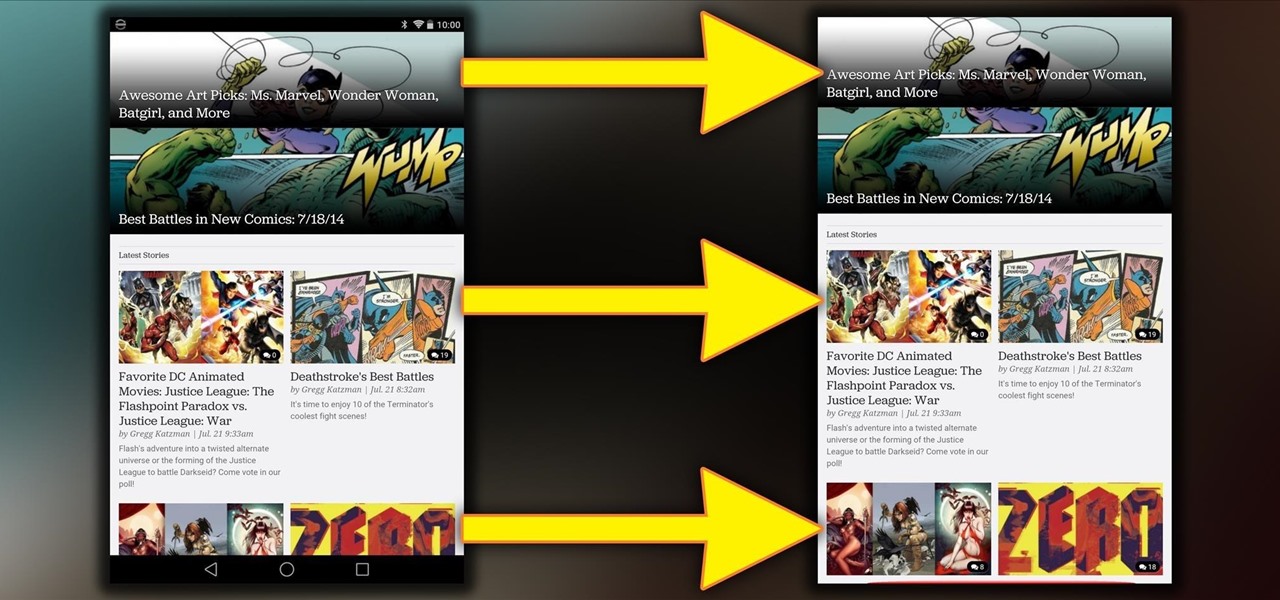
Android's beauty is in its customization; you can have widgets for anything, launchers that look and feel completely different from one another, and fonts you can change at any time. And it doesn't stop at aesthetics—you can go much deeper than looks.

The dock has been a staple of Mac OS X since its creation and not much has been needed to improve its functionality, but when you add theming to the mix, you can run into some issues.

Getting things done isn't easy when you're bombarded with alert sounds and notifications all day long on your Mac. Here's how you can quickly remove those distractions with just a single click.

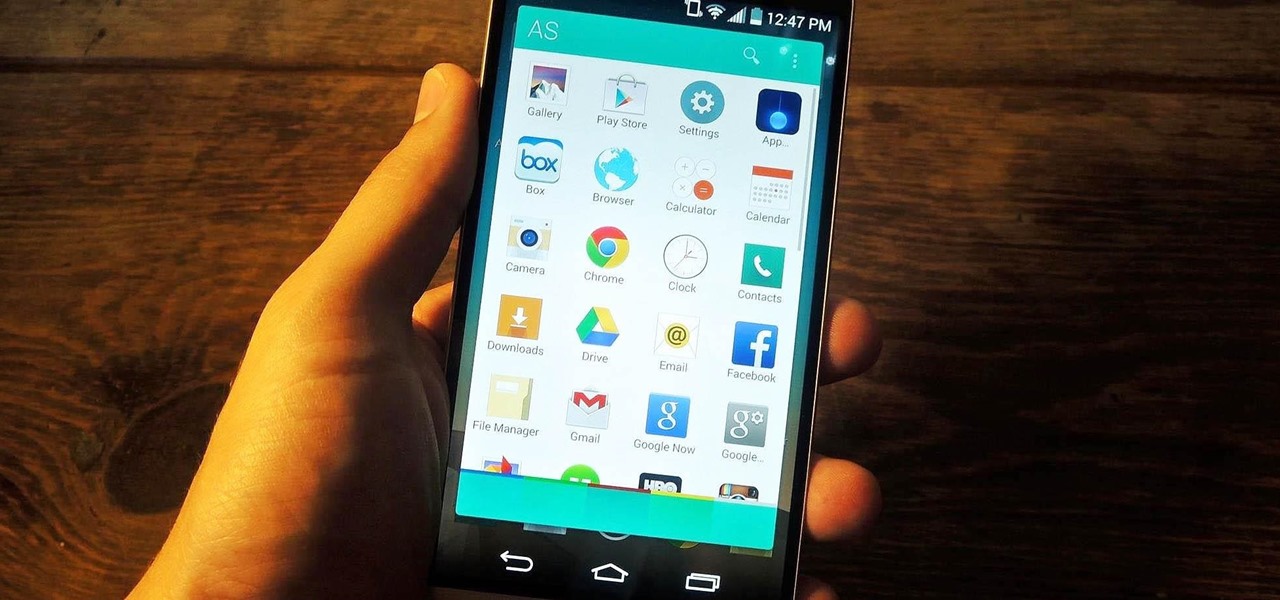
App switchers are a great way to conveniently access your favorite applications from any screen, but most limit the number of apps you can use. That means that whenever you want to switch over to another app, you have to leave your current one, and either find the one you want in recents, on your home screen, or in your app drawer.

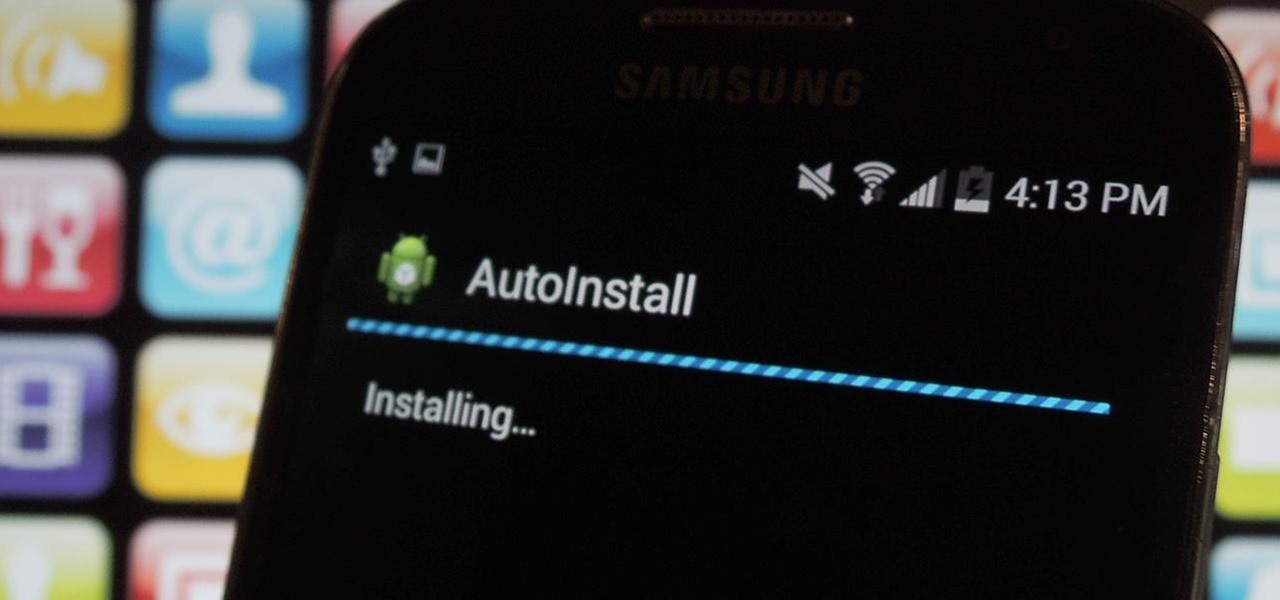
I'm always looking for the best apps and services for my Android, and that means sticking strictly to the Google Play Store is a no-go. If you're like me and tend to install a lot of APKs (application files), you're probably tired of seeing the "Install" confirmation that always pops up.

Rooting is a great way to unleash your device's full potential, but not everyone's comfortable with it. Rooting can void a warranty, cause issues with certain apps, and the process itself can be tricky for older devices. Alas, most of the great apps or mods out there require root access, like the ability to utilize a built-in KitKat feature known as Immersive Mode.

There are countless lock screens you can apply to your Android device, but very few offer more than just quick access to apps or advanced security functionality. Since you probably unlock your device a gazillion times every day, why not use this to your advantage and let it teach you something new?

It's time for another mobile prank. The classic pranks and practical jokes are always great, but let's hit your friends where it really hurts—their precious (and expensive) smartphones. And what better way to scare the shit out of them than making them believe their phone's been infected by malware?

It's not enough for me to just listen to a mindless EDM song that can be retooled as a torturing method for Guantanamo Bay. As an actual fan of music, I yearn for substance and depth. Artists like Morrissey, Kurt Cobain, and John Lennon impacted lives with not only their music, but the subject matter of their songs.

In photography, stereographic projection is a geometric technique that projects a sphere onto a plane, which is mostly used in the mapping of spherical panoramas.

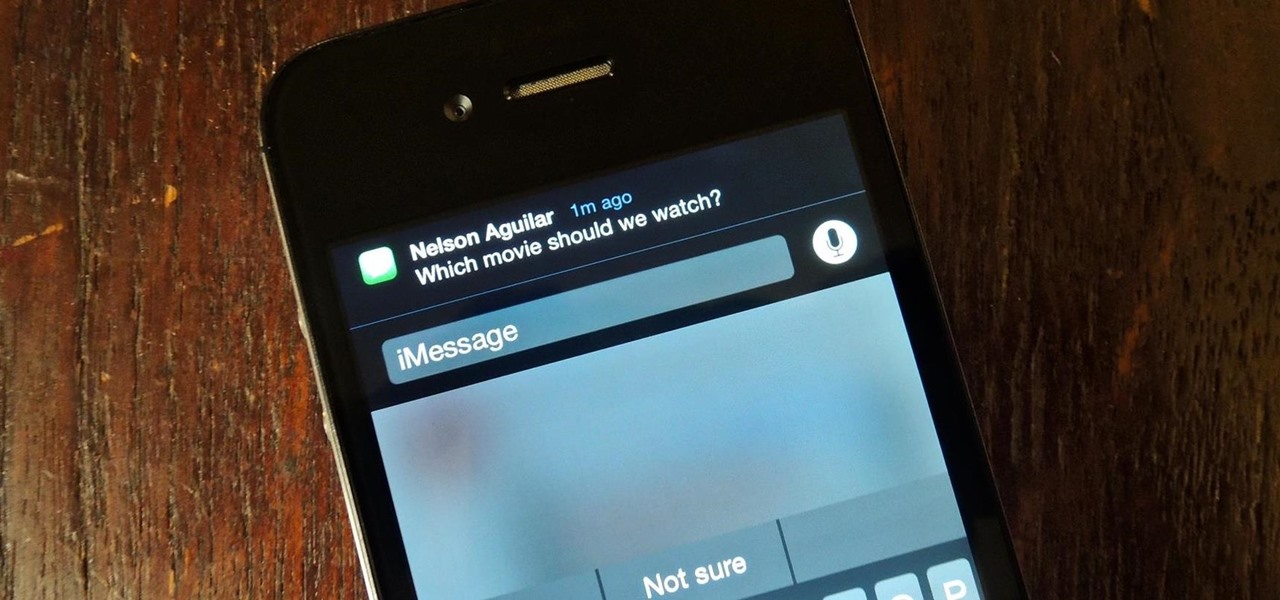
Notification banners and alerts aren't new to iOS, but the ability to expand and interact with them is. Apple's new iOS 8 has ushered in some small, yet convenient features to the banner and alert notifications that make them truly interactive. The new additions, as you will see, makes it easy to complete simple tasks without leaving the current screen you're in.

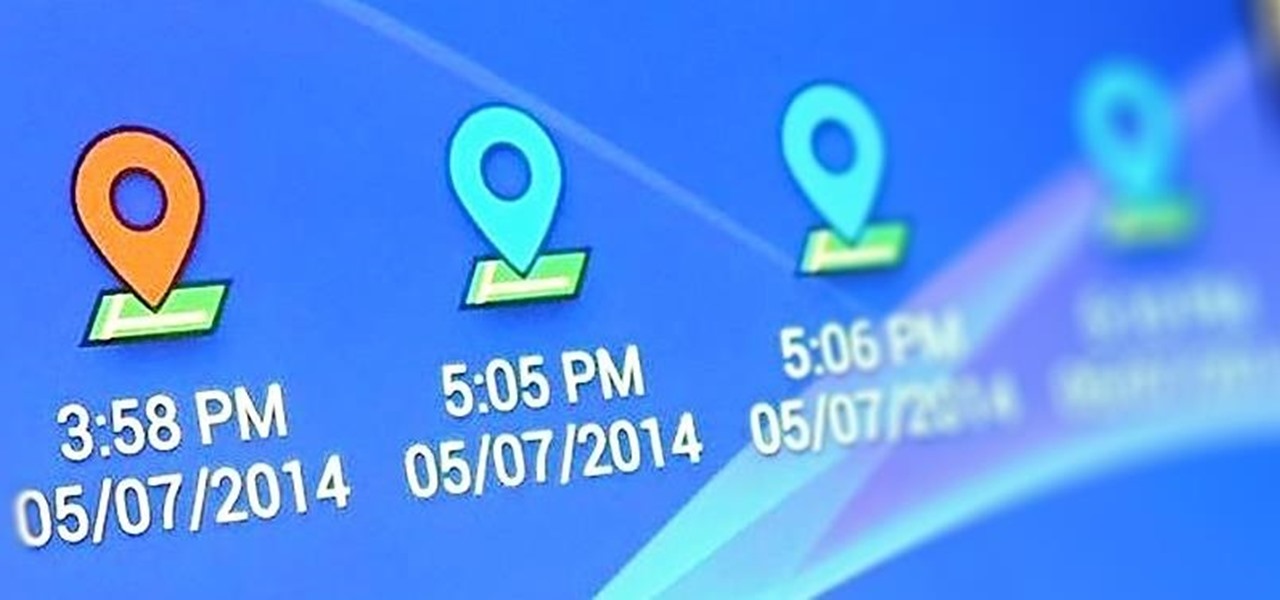
I passed a cool looking bar the other day that I wanted to check out. When the weekend came around, I was ready to go, but for the life of me couldn't remember where it was. Not wanting to retrace my steps or drive around aimlessly, I gave up.

Incorporating features such as CarPlay, UI enhancements such as the new call screen, and several bug fixes, iOS 7.1 was the first major update to Apple's operating system since iOS 7 was released in June of last year.

As an added functionality to the S Pen, the Pen Window enables you to create floating application windows on your Samsung Galaxy Note 3—a tool that's extremely useful when it comes to multitasking.

The new HTC One and Nexus series devices have already replaced their physical navigation keys with soft keys, and it's inevitable that we'll see more and more of this on future mobiles. Samsung continues to buck the trend entirely, but no manufacturer as gone as far as to remove the volume rockers.

Multi Window, a feature that was greatly improved with the release of the Samsung Galaxy Note 3, is still quite limited on the older Note 2, allowing only the use of a few stock applications to multitask with.

Allowing us to easily get features that would otherwise be available only through flashing mods and custom ROMs, Xposed Installer has been a godsend since its development, simplifying the sometimes tasking and potentially harmful process of changing the core components of Android's operating system.

If you use your Nexus 7 like me, then you're constantly downloading APKs, installing new games from Google Play, taking a million photos, and using multiple apps at the same time.