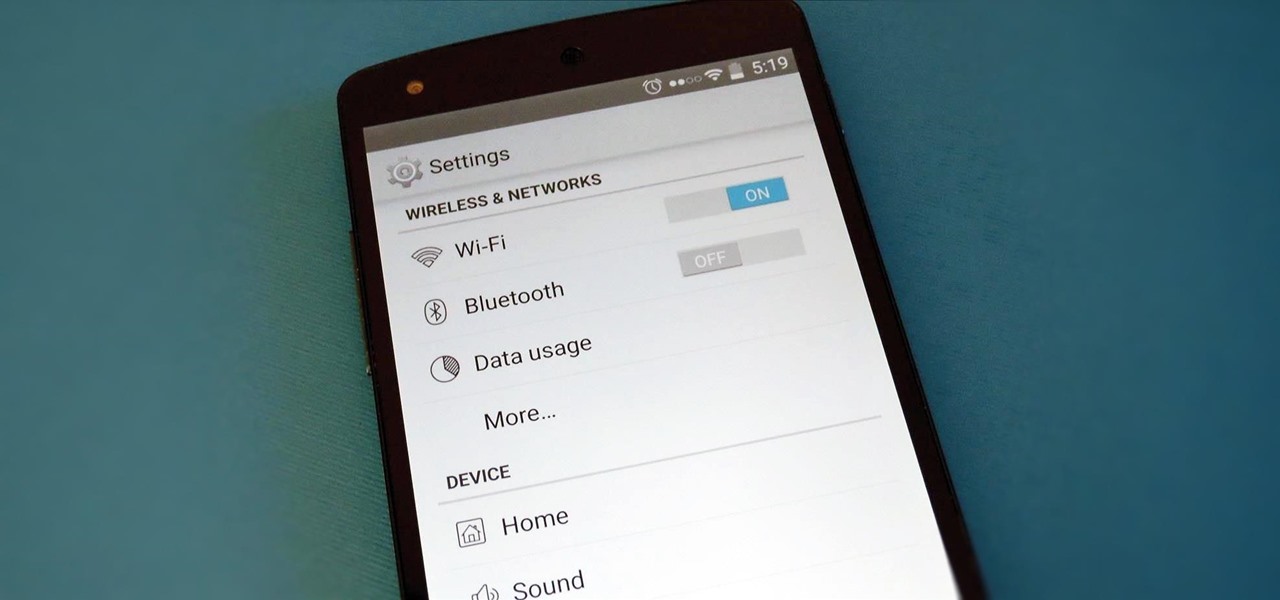
If you have a custom recovery installed on your Nexus 5, you're able to flash custom ROMs and lots of other cool Gadget Hacks. But when it comes time to receive and Over-the-Air (OTA) update directly from Google, having a custom recovery installed can be a fairly big hindrance—and for the upcoming Android L release, you're going to want to alleviate that.
When Android 4.4 was released, the massive changelog led to some awesome new features getting lost in the virtually endless list of new tweaks. One such change was the ability to set a default text messaging app, which streamlined the existing process of installing a third-party SMS client.
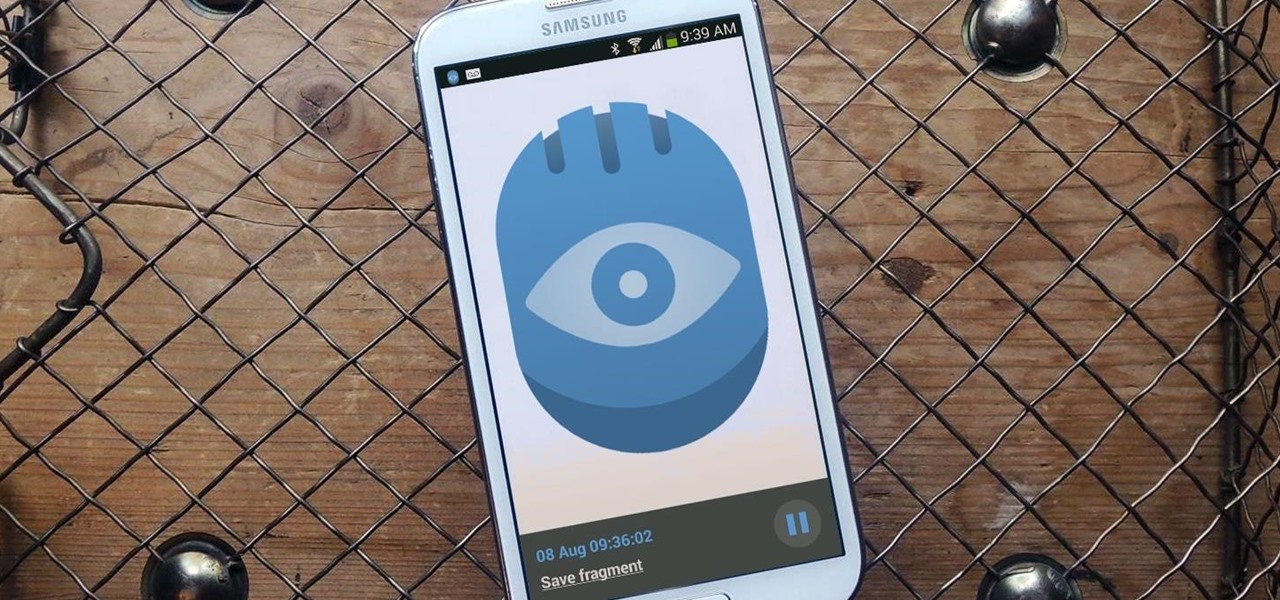
Whenever you need to record a quick message to yourself or someone else, the stock Voice Recorder app on the Galaxy Note 2 does a fine job. However, the situations when you need it the most are when you forget or don't care to actually use it, like during a heated argument or a random police stop where your words can be misconstrued or altogether unheard.

With over a million apps and counting, it's not exactly easy to browse the iOS App Store to find fresh and interesting new apps for your iPad or iPhone. Even rummaging through the featured apps and games isn't easy.
Yes, I know. Nexus owners aren't exactly the biggest Apple fans out there. That "Pure Android" experience was one of the main reasons we bought our Nexus devices. But give the other side some credit—the iPhone's operating system has come along way, and is still the champ when it comes to aesthetic design (at least until Material Design dethrones it this fall).

The newest version of iOS 8 beta is now out. Almost three weeks ago, in the iOS 8 beta 2 release, we saw podcast integration, full-screen caller ID, new assistive touch toggles, and a "disable all" button for app notifications, among other things.

Think eating food is as easy as putting it in your mouth? It's considerably more complicated than that. Your brain plays a big role in determining what and how you eat. Understanding how your brain interprets food choices is key to managing your eating habits.

LG has really made their new G3 handset something to drool over. The hardware and software behind it can be considered as good, or even better than most flagships out there, and it has left me second guessing my decision to stick with the M8.

Merely fidgeting and shivering can burn calories, but now you can add trembling in fear to the list too. Just pop in a good horror movie and turn down the lights to burn off up to 200 calories. What would you rather do? Walk for over 30 minutes or watch a 90-minute scarefest?

Welcome back, my greenhorn hackers! Lately, much of the discussion here on Null Byte has revolved around evading detection and not getting caught hacking. Several of you have written me asking for a series on evading detection and forensics, and while I began a series 5 months ago on just that, we have changed hacking platforms from BackTrack to Kali, which has a much more highly developed forensic toolset.

Facebook is a black hole. The constant stream of baby photos, #hashtags, BuzzFeed quiz results, and unintelligible status updates is mind-numbing. I know too much about too many people I hardly know.

It started in Australia, and now seems to have made its way statewide—hackers are remotely locking iOS and Mac devices, holding them for a $100 ransom. Users awoke to the loud "lost iPhone" ringtone, with a message on their lock screen stating that "Oleg Pliss" has hacked their device, and that "they" will unlock it after being sent $100 through PayPal.

Instagram is not only a great platform to easily share some of your favorite moments with friends and family, it's a useful service for peering outside of your physical location. While you share a picture of your dog in Los Angeles, you can almost instantly view and like a picture someone posted of their breakfast in Tokyo.

Hey, coffee drinkers—your morning cup of joe is killing your metabolism.

Erudite. Barbiturate. Cacophony. Denouement. Okay, that last word is technically French, but words like these make the average person sweat, and it turns out that the key to learning how to pronounce them once and for all just might be getting them wrong.

How many times have you heard someone utter the phrase, "Now, let's break into groups"? From classroom discussions to workplace think tanks, gathering into groups to generate ideas is common practice. These forced get-togethers are intended to encourage creativity and unique thought, but they can actually do the opposite. More often than not, group brainstorming is annoying rather than encouraging, and these group sessions can actually be detrimental to your productivity. Getting together har...

The best sangria I ever had in my life was made by a Spanish friend for my birthday party. The ingredients included a giant box of Franzia red, one bottle of Bombay Sapphire Blue, one cup of sugar, a liter of 7-Up, and some cinnamon sticks. She put everything but the 7-Up in a giant zinc bucket from Home Depot and insisted that it had to sit overnight so the flavors could blend (and so the Franzia wouldn't taste so, well, Franzia-ish).

You don't always plan on getting drunk, it usually just sort of happens, right? You finish one beer, move on to the next, and all of a sudden you're a six-pack in and feelin' it. And when you're drinking in places you're not supposed to, it can get ugly.

To flip, or not to flip, that is the real question. When you're nervously standing over the stove or grill, what do you do with that steak before you?

Welcome back, my novice hackers! The worst thing that can happen to any hacker is being detected by a security admin, the security technologies (IDS, firewall, etc.), or a forensic investigator.

A few days ago I finally finished my 2 week journey into trying to get OpenVas to work properly. You all may have noticed that you can't just click the setup openvas in kali and have it working properly.

Welcome back, my greenhorn hackers! Although we have focused primarily on technical hacks here, social engineering can sometimes be especially effective. This one requires a bit of technical skill, but not too much. In addition, it's limited by how specific a target you can choose—but it will work.

What's the point of having a 1080p screen if you're not using it to get in some quality gaming time? Google Play is great for downloading games, but you probably already have an extensive library of games for your consoles, so use those!

I have a theory that chocolate chip cookies are the gateway drug to cooking. The recipe is easy, no special equipment is required, and at the end, you get warm, fresh-from-the-oven cookies that are simply irresistible. It's how I got hooked on baking and cooking, and anecdotal evidence (i.e. me asking my other kitchen-obsessed friends and a few culinary students) supports me.

A perfectly cooked roast potato is a study in contrasts: the outside should be crisp, crunchy, and salty, while the inside is tender and fluffy. Too often, however, roast potatoes come out overcooked, greasy, and tough.

Sometimes you've got a head of lettuce that you want to eat but it lacks a certain youth. In other words, it's wilted and browning at the edges. Other times, you get to the grocery store near the end of day and the only lettuce or greens available look a little on the sad side. Never fear. You're not doomed to a meal of fast food or mouthfuls of soggy salad. You can easily revive those leaves and have something crisp, green, and delicious for your next meal, so don't dump it in the trash.

The new HTC One (M8) is a large phone, no doubt about it. Still, with those BoomSound speakers, 5-inch display, and 2600mAh battery, it's a wonder they managed to cram everything in that gorgeous, unibody metal shell. By that logic, it makes sense that the M8 makes the switch from a micro-SIM card to nano-SIM to save as much space as possible.

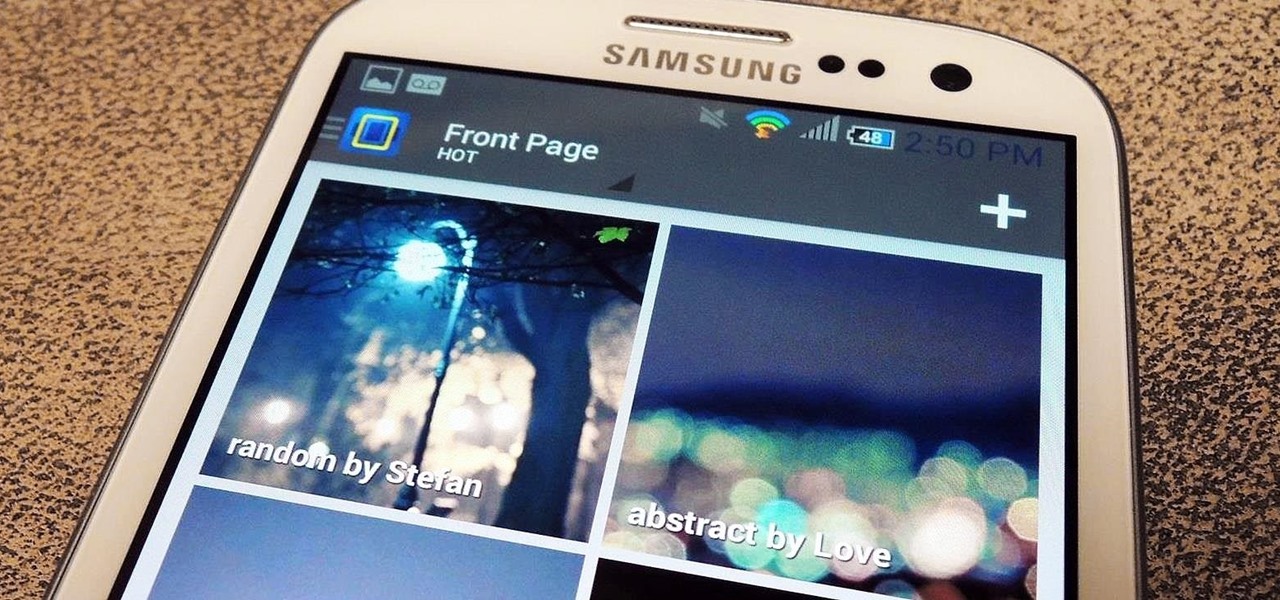
No matter how cool my 3D live wallpaper is, or how often my Google Now wallpapers automatically change, I always want more backgrounds. Zedge has made it easy for me to find new ones, and 500 Firepaper helps me keep my background lively with rotating wallpapers—but these aren't enough.

Amazon.com has been around for a long time now, but there are still a few things most people don't know about when it comes to buying products from them. Here's a quick roundup of tips to help you get the most out of Amazon and save some money in the process. The holidays are the busiest time of year for online shopping, but these tricks will work all year around.

How often do you make a pie from scratch? If your answer is "only during the holidays," you're not alone. Unless you're an experienced baker, homemade pies can be pretty tough to tackle. And the most common problems are the crusts coming out of the oven soggy or scorched.

Cryptography is the science of keeping secrets, or more specifically, the science of disguising them. As a point of fact, cryptography has progressed quite a bit farther and now encompasses file and message integrity, sender authentication, and pseudo-random number generators.

As things begin to clutter on your device, navigating through it can become much more difficult than when you first got it. The sheer number of added apps and mods that build up after time take its toll not only on the quickness and memory of your device, but also on your efficiency to access everything easily.

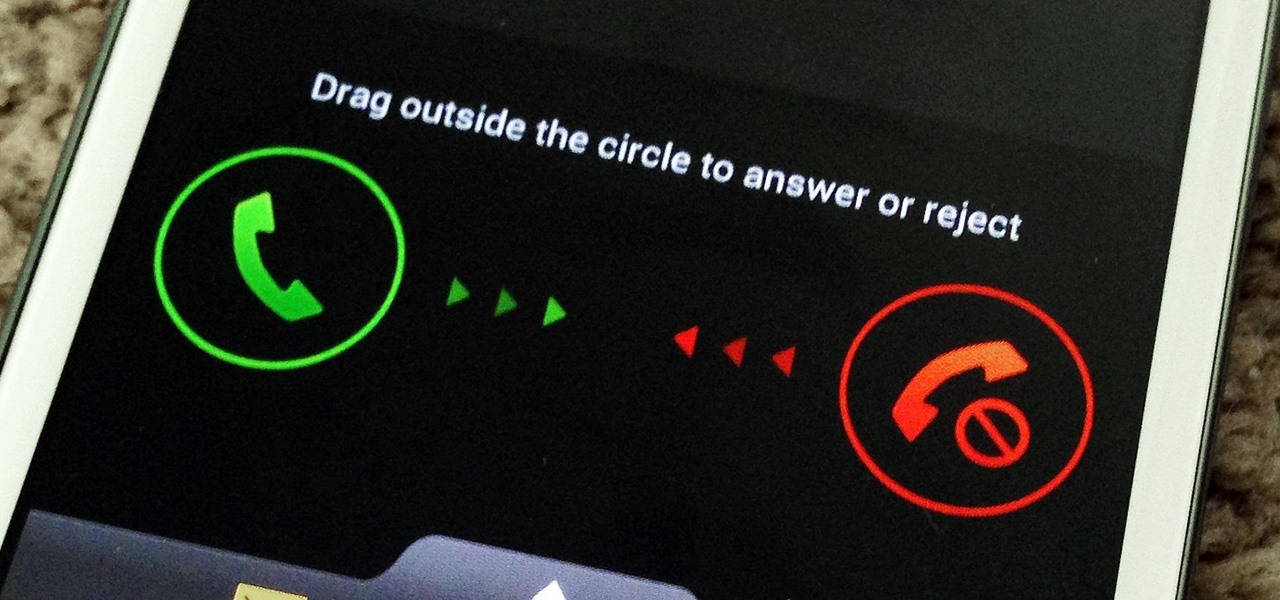
You don't have to be in debt to receive annoying calls from unwanted numbers. You may love your grandma, but if she calls you three times a day to ask how to turn on the television, you might just want to push all of her calls to voicemail.

Welcome back, my fledgling hackers! In the first part of my series on Wi-Fi hacking, we discussed the basic terms and technologies associated with Wi-Fi. Now that you have a firm grip on what Wi-Fi is exactly and how it works, we can start diving into more advance topics on how to hack Wi-Fi.

Welcome back, my greenhorn hackers! I've been writing these Linux tutorials in an attempt to fill the void in the education of some aspiring hackers into the Linux operating system. There is a lot to know, and in this tutorial, we'll look at Linux file permissions. Step 1: Checking Permissions

I've never understood gift cards. Aside from being severely restricted as to where you can use them, they're also a strange gift, especially if you don't shop at that particular store. Some even have expiration dates and service fees.

Welcome back, my tenderfoot hackers! This is the third installment of my series on basic Linux skills that every hacker should know. Although some hacking tools are available for Windows and Mac, every real hacker uses Linux—for good reason.

Ethylene is an invisible, odorless, naturally occurring gas that aids in the ripening process of fruit. As a fruit produces more ethylene, it begins to create enzymes which help break down cell walls and starches, making the fruit softer and sweeter over time. If it weren't for this small hydrocarbon gas, the shelf lives of most fruits could last well over a year.

"Ahoy-hoy." If telephone titan Alexander Graham Bell had his way, we'd all be answering phones like Mr. Burns. Thankfully, frienemy Thomas Edison had enough sense to realize we weren't always on the briny. He preferred "hello" as our standard telephone greeting, which he is credited with coining in 1877. Fellow American pioneer Davy Crockett actually used it as a greeting first in 1833 (as compared to an exclamation)—but in print, not over the phone.