Since the release of the Galaxy S5 back in April, the process of converting older models, like the Galaxy S4, to replicate the look and feel of the newest S-family member was inevitable. Galaxy users didn't want to be left out, and for good reason. The revamped interface of the S5 introduced a new color palette that was a definite improvement from the flat boring colors on older models.
With all of the top-notch specs that the Galaxy S5 sports, the only minor quibble users have had with its hardware is the speaker situation. A front-facing earpiece is used for phone calls, but all other media is restricted to a single rear-firing speaker.

Many Android games use large, storage-heavy OBB files to store supplemental data. Generally, games with high-end graphics download these extra files when you install them from the Google Play Store.

Most Android devices allow you to simply replace a ZIP file in your /system/media folder if you want to change your boot animation. Unfortunately, though, this isn't the case for the Galaxy S5, as it's been buried deep in Samsung's TouchWiz skin.

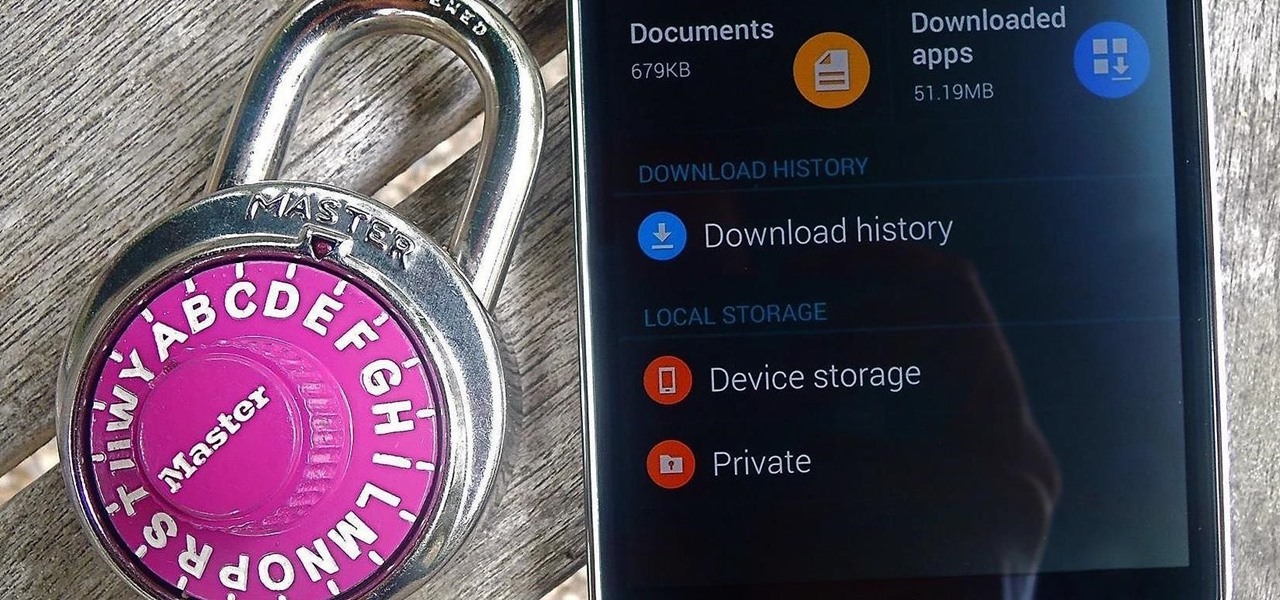
We live in a time where privacy is rare and our files can be easily accessed by just about anyone. Having your phone protected by a passcode is great, but if someone figures it out, they can easily access anything on your phone.

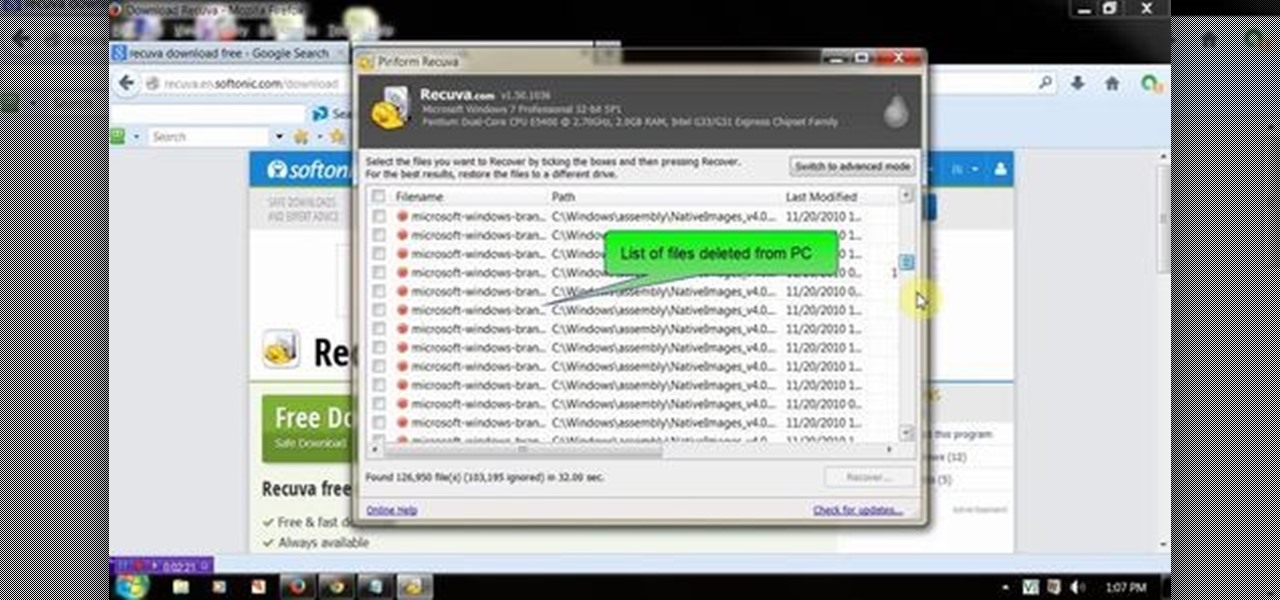
Losing important data is the modern-day equivalent of misplacing your wallet or keys. We have tons of vital information stored in our digital worlds, and losing any of it can be devastating. But if you've accidentally deleted something important from your Android device, there's still hope.

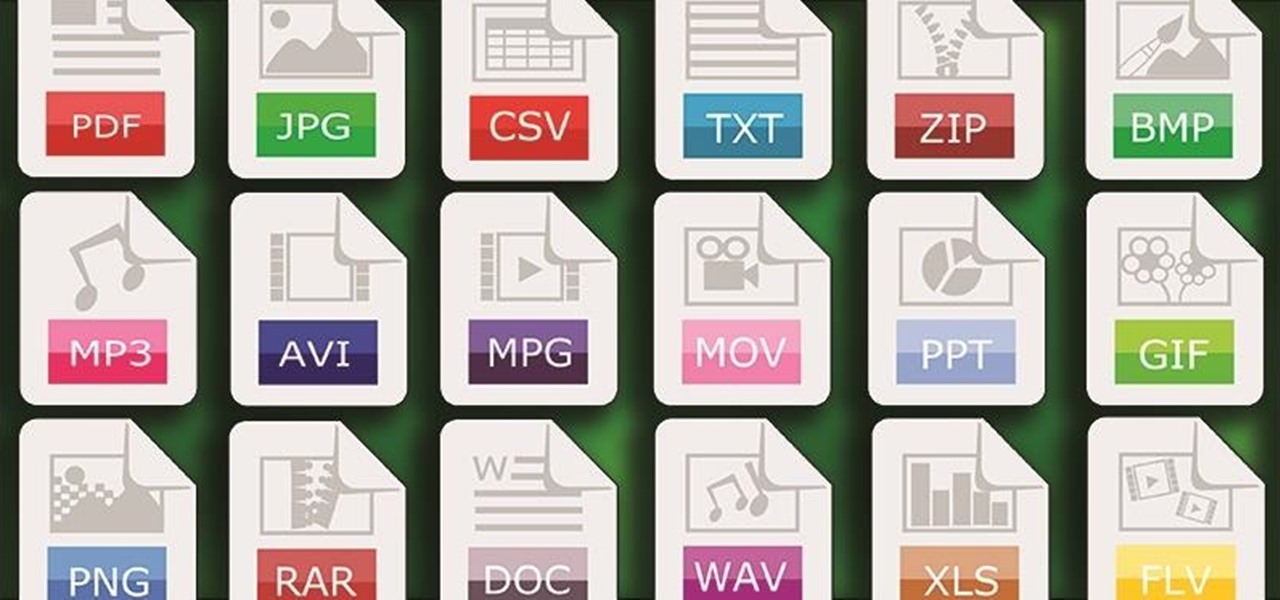
One of Android's strengths when compared to other mobile operating systems is its ability to set third-party apps as the default handler of certain file types. Instead of being stuck with pre-installed system apps when it comes to opening files and links, you're free to choose a better-fitting alternative.

Certain files contain sensitive data that you don't want being shared with just anybody. Even still, it would be nice to be able to send such a file to a certain confidante without fear of it falling into the wrong hands.

Transition animations are an essential element of any mobile operating system. They give the user a sense of what's happening on the screen, where the apps are coming from, and where they're going.

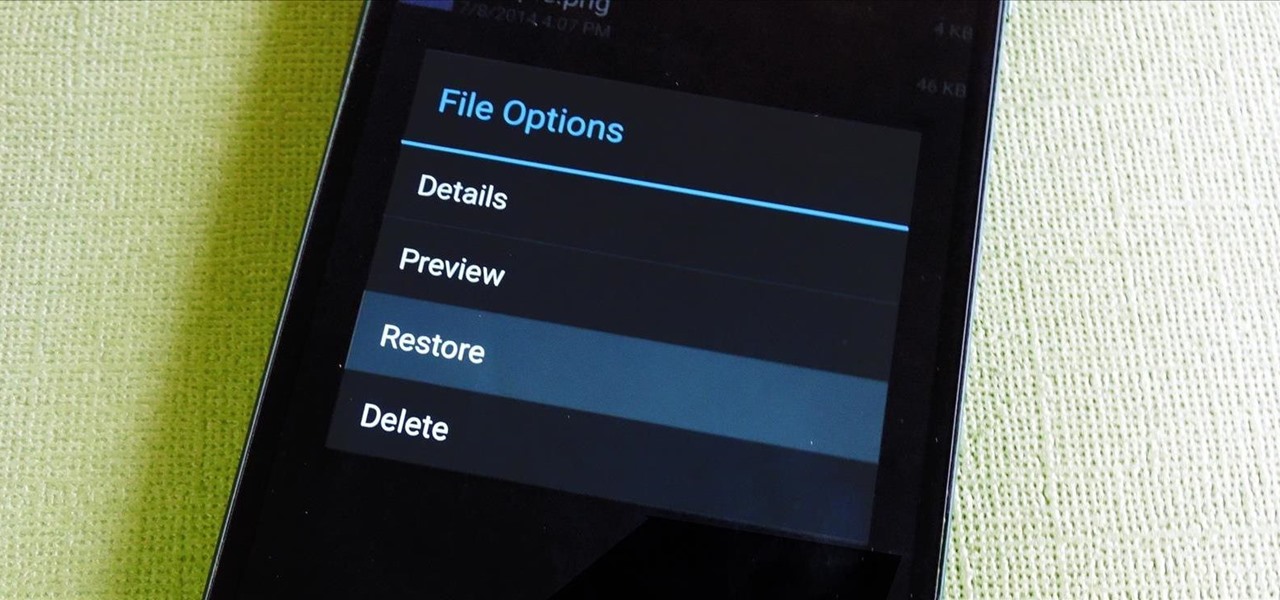
If you've ever used a computer, you're surely familiar with the concept of a Recycle Bin (Windows) or Trash Can (Mac). To sum it up, files that you've deleted are not actually gone from your storage, they've just been moved to a different location. You can then restore the files if need be, or empty them, permanently deleting them forever to free up space.

This video will show you how to recover permanently deleted file which you have deleted from recycle bin. But if any new file allocated to those positions then the files could not be recovered with this tool. Watch the video from the installation to execution of the tool to recover deleted data.

With limited storage options available on the Nexus 5, cloud storage can definitely come in handy. But sometimes, with the seemingly endless options of cloud services for us to choose from, our online data can get a bit disorganized.

This video will describe you how to hide your important files, system files and folders hidden from common users in windows 7

Welcome back, my greenhorn hackers! My preference for Linux as a hacking platform is well documented, and I have even created a series of tutorials to train new hackers. Without being proficient in Linux, you can't really call yourself a hacker.

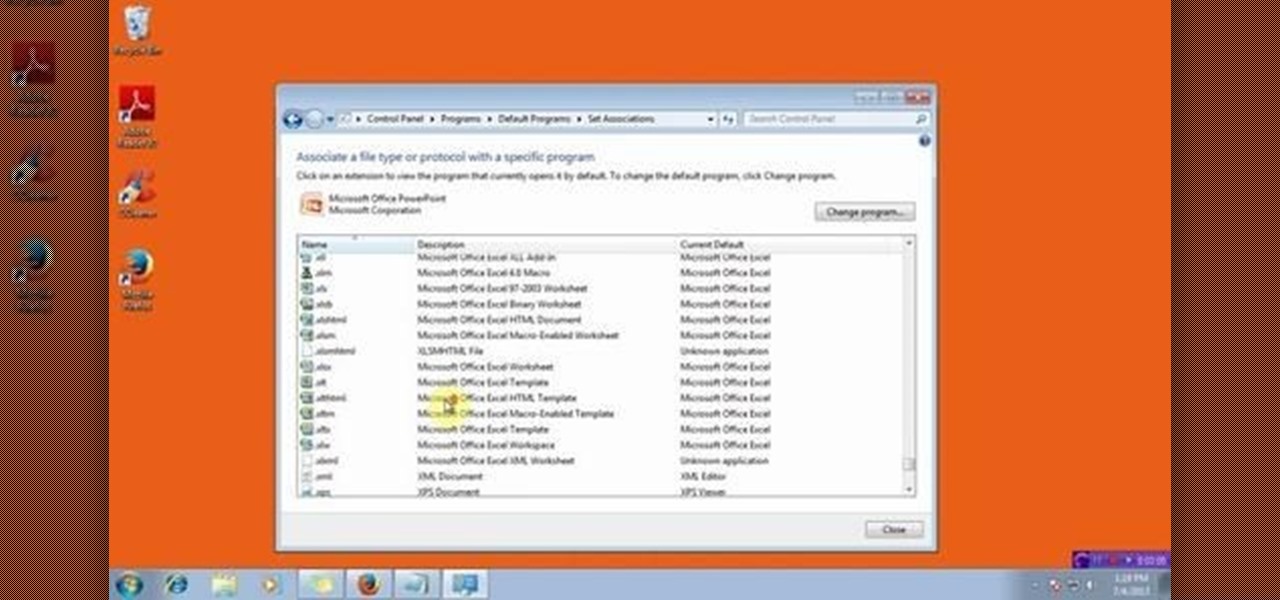
This video will show you how to change the default program for a Specific File Extension in Windows 7.

Facebook rolled out a new feature that lets your friends ask you about your current relationship status. This is great feature if you use Facebook for finding hookups, but if you use it mostly to connect with family and friends, a bunch of questions about your dating status can get annoying real quick.

Sony has been hard at work refining its Xperia line of flagship phones. With a 6-month release cycle, they've managed to slim bezels, increase viewing angles, and boost processing power in the 1.5-year span between the original Xperia Z and the Z2.

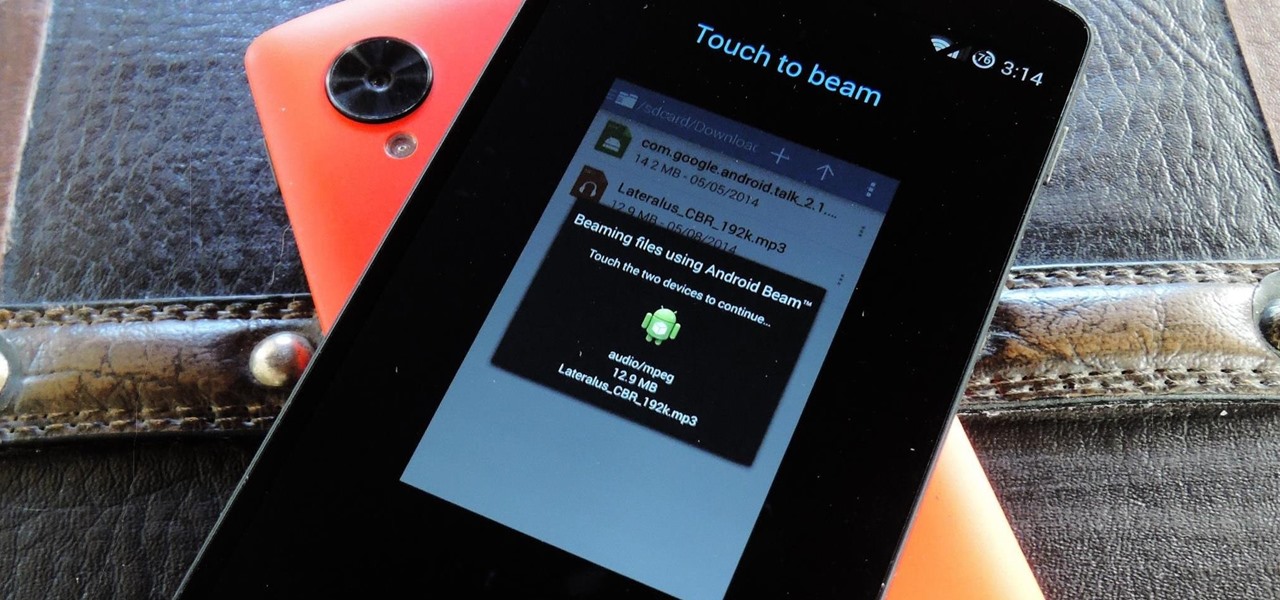
Your Nexus 5 comes with a pretty cool feature baked in called Android Beam. Using NFC, or Near Field Communication, this functionality allows you to send information to another compatible device by simply touching the two together. Most flagship devices have NFC built into them these days, so there is a broad range of devices that your Nexus 5 is capable of sharing information with wirelessly.

Whether it's embarrassing pictures and videos on your smartphone, or files you just don't want anyone reading, there are plenty of ways to hide them. For most devices, that means installing third-party apps like Gallery Plus - Hide Pictures, Sectos - Photo & Video Vault, TimeLock, or Hi App Lock.

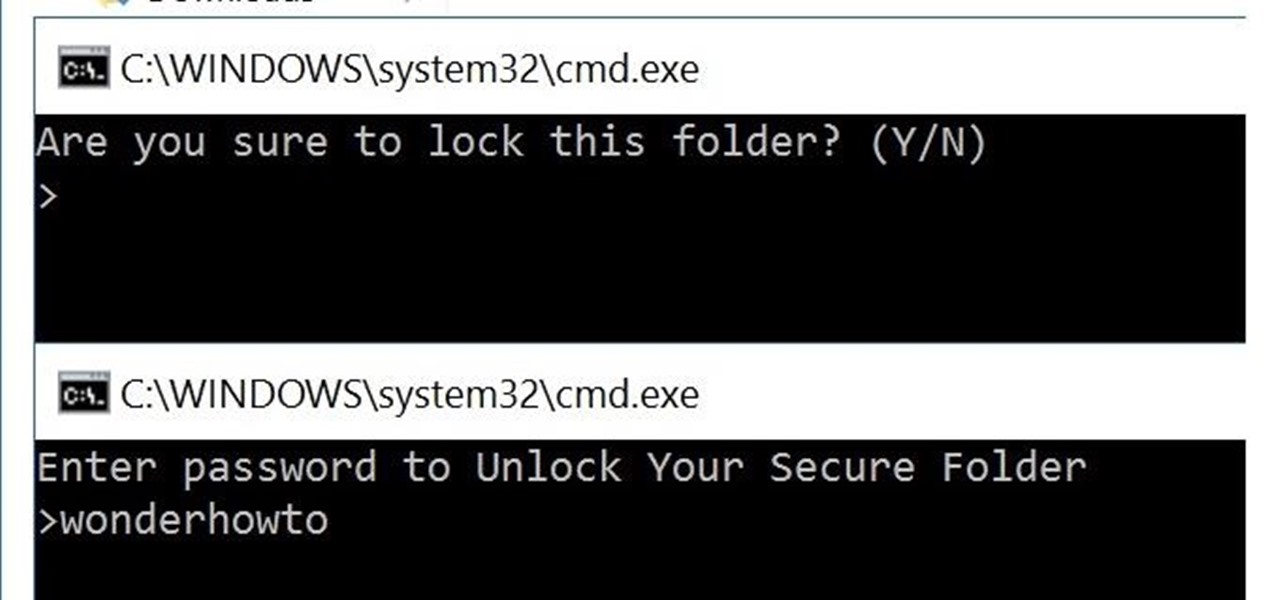
You can easily lock any folder on your Windows computer with a simple Notepad hack. By creating a batch file, you can hide a folder and require a password be entered before it becomes visible and accessible. This is a great tool for locking sensitive information, like pictures, financial statements, and a lot more.

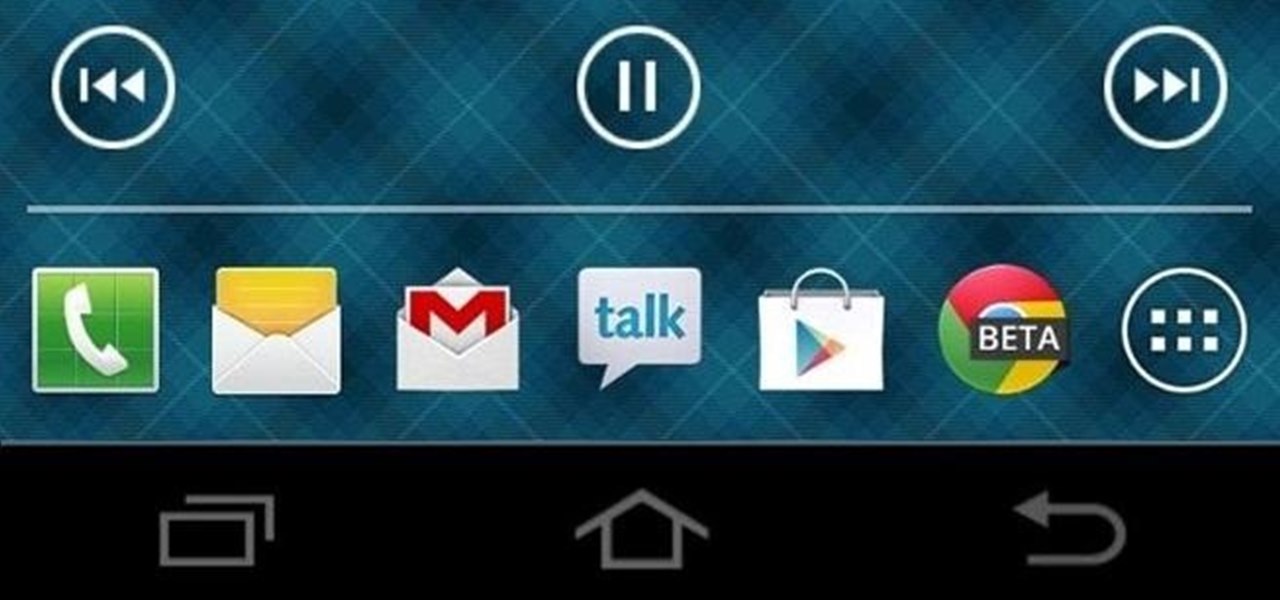
For now, the redesigned and fresh-faced Android 4.4 KitKat is exclusive to the new Nexus 5, though it will be rolling out to other Google (Nexus 4, Nexus 7, Nexus 10) and Google Play Editions (Samsung Galaxy S4, HTC One) devices in the next week or two.

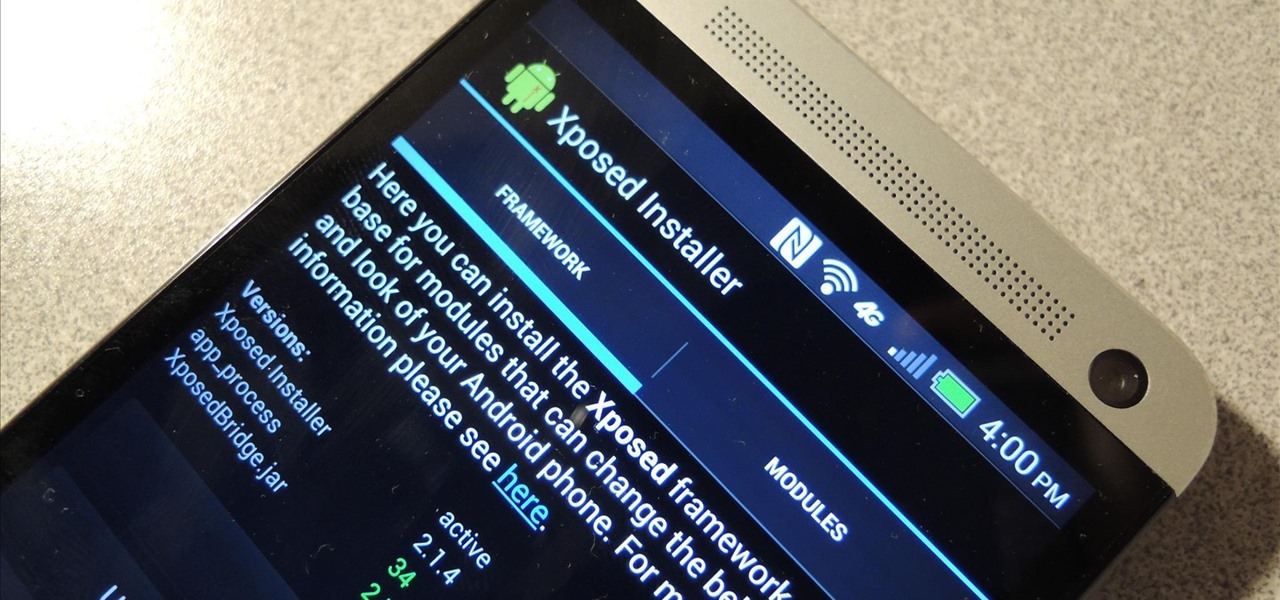
Update: The installation process for Xposed Installer is now dead simple—check out our updated guide!

Welcome back, my aspiring hackers! As mentioned several times in previous Linux tutorials, nearly everything in Linux is a file, and very often they are text files. For instance, all of the configuration files in Linux are text files. To reconfigure an application in Linux, we simply need to open the configuration file, change the text file, re-save, and then restart the application and our reconfiguration is applied.

Welcome back, my greenhorn hackers! I've been writing these Linux tutorials in an attempt to fill the void in the education of some aspiring hackers into the Linux operating system. There is a lot to know, and in this tutorial, we'll look at Linux file permissions. Step 1: Checking Permissions
There has been much talk about how unsecure the cloud is because of PRISM’s newfound ability to demand all of your data without any resistance. This has spin doctors in the Cloud Storage industry losing their mind. They suddenly went from a central hub for 10GB of your files, to an easy window for Big Brother to track you through. Centralized cloud storage is no longer a safe way to keep your files, but we still need a way to access our files anywhere we go.

Welcome back, my tenderfoot hackers! This is the third installment of my series on basic Linux skills that every hacker should know. Although some hacking tools are available for Windows and Mac, every real hacker uses Linux—for good reason.

Recently, I wanted to share a large video file from my Nexus 7 to my friend's Samsung Galaxy S3, and even though he was standing right next to me, it was an extremely difficult and frustrating thing to do. Every single Nexus 7 tablet comes NFC equipped, so it can share files with other NFC-equipped devices just by tapping and holding them together. With both NFC and Android Beam enabled, sharing a small file between two devices should be fairly simple.

Samsung bucked the trend and threw hard keys onto the Galaxy S3 while most manufacturers are going the soft key route. This hack will add on-screen buttons to your TouchWiz-based ROM. You'll need a root file manager with a system writable text editor—I recommend ES File Explorer for this, but feel free to use whatever you want. If using ES, hit Menu, Settings, go down to Root Settings, and check Root Exploerer, Up to Root, and Mount File System.

There are certain files on your Mac that do not warrant encryption, but still need to be hidden. Whether it be snoopy parents trying to find pictures, or friends stumbling upon one of your love letters, there are times when you need to hide a file and have it kept secret. Obscure Your Files with Obscurity

If you're doing research that includes a lot of copy/pasting, it can get really tedious to open a new document every time you want to save something. Luckily, you can cut out the extra step and save text and images that are currently in your clipboard directly to a folder or your desktop—without the hassle of creating file after file. Here's how to do it on both Windows and Mac OS X. Windows

Attaching files to an email is way more convenient than trying to link people to third-party file transfers. Unfortunately, the standard 25MB limit is far too small to send some files, like large videos or multiple audio files.

The Zumocast app allows you to stream music, movies, or pictures directly from your work or home computer to your Droid Bionic smartphone. The Android device can also access documents or other files located on your PC using the program. This Motorola support video will walk you through the process.

In this video, you'll learn how to convert format files accurately and for free in two different ways. You can use a program called Format Factory, which you can download here, or you could use a website called Zamzar.

In this video from macmostvideo we learn how to import unsupported video in iMovie. This happens sometimes when you buy a camera that is not compatible with iMovie. You can add certain video formats to your Mac to make your Mac understand these video formats that don't work with your iMovie. A common one is called mpeg2. You can get this trough Apple. In other cases you get the software with the camera. If you need to convert a video file, try to open it through QuickTime first. If that works...

Add a background .mp3 file to play music when visitors come to your website. You can also build buttons to allow users to pause, mute or play the file while they're on your website. This tutorial shows you how to build this system using Action Script 3 and Adobe Flash CS4.

What if your PC crashed? What would you do? Everything would be gone, erased forever, and you'd be in a horrible and stressful situation, especially if all of you homework or work files were stored on your Windows PC. But why even enable yourself to be in that situation? In Windows XP, it's not uncommon to have experienced a corrupt registry or a missing DLL file, or having a blue screen of death.

Hardened steel is very durable, but nearly impossible to work with at home. If you are trying to choose a piece of steel and can't tell if it's hardened or not, you're in luck, because this video contains a quick method for doing so. All you do is try to file an indentation in the steel with a file. If that doesn't make a mark, you've probably got hardened steel.

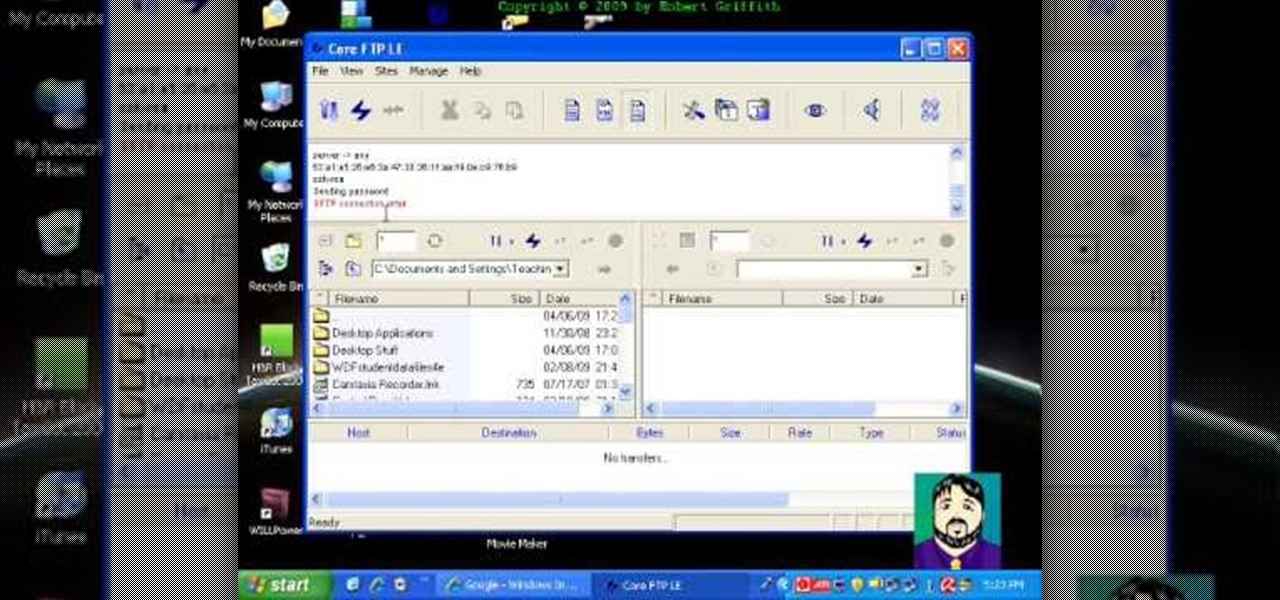
Select an FTP client that allows you to connect to the webserver. Download a free Core FTP Le software. Install the program. Use the site manager to name the internet site. Create a host/url, a user name, password and a connection. Connect to the web server. Create an index file to make files viewable. Open the Core FTP LE software. Drag files from the desktop (left side of the dialog box) to the internet server (right side of the dialog box.)

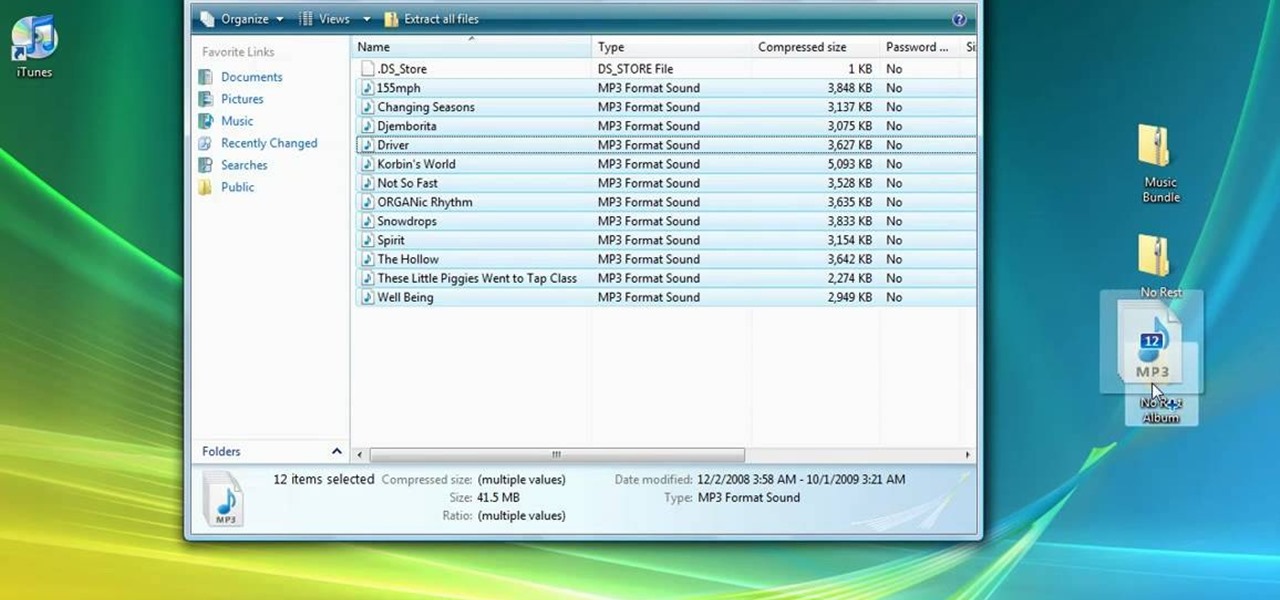
'Zipping' is a method of compressing data, such as a music album, into a zipped folder which makes it easier to send. This tutorial shows you not only how to unzip a folder, but how to then load it with iTunes and send it to your iPod or other MP3 player.

In this clip, you'll learn how to log into a Blackboard course and upload files, edit and manage files. Whether you're new to Blackboard's popular content management system or CMS or are a seasoned web instructor just looking to better acquaint yourself with the features and functions of versions 9 and 9.1, you're sure to be well served by this free video software lesson.