
How To: Use Magic iMovie
Magic iMovie is designed to import a movie from your camera and create a movie file with an opening title and other options. Learn how to use Magic iMovie.


Magic iMovie is designed to import a movie from your camera and create a movie file with an opening title and other options. Learn how to use Magic iMovie.

A tutorial on how to "break in" to your Windows machine after you have lost the password. This works in Windows NT, 2000, and XP machines without an encrypted file system. I then show you how to wipe a hard disk to assure no one can gain access to your data once the drive is sold or discarded.

USB flash drives are great for moving files on and off of a linux server, but how do you do it? This quick tutorial shows you how easy it is!

This tutorial shows you how to hold and fetch a scene in 3D Studio Max. This is very similar to a quickly saved file but without actually saving it.

Here’s a video on how to process your panos in Lightroom. Learn how to take those raw files and process them with a panorama in mind (it’s really a lot like processing a regular photo with just a small change at the end). We’ll process them in Lightroom and then take it through the Photomerge feature in Photoshop to finish things off.

This tutorial teaches you how to save your photos after you've edited them in Photoshop! Tutorial taught using Photoshop CS3 and recorded with Camtasia Studio v5.

This Sony Vegas 7 tutorial talks up about many topics such as: -Explorer
This video shows how to modify Mama's Sparkles Action for Photoshop to accommodate sparkle size to a smaller resolution file or smaller area of the image.

Chad west covers some basic masking concepts to add a pre-made border file to a photograph.
This video shows you how to download and play TV and movie files on your computer using two programs: Joost and Miro.
Learn how to change the default action that the Firefox web browser takes when opening a type of file including .mp3, .midi, and others.

PDFs are the industry standard for document sharing. However, sometimes PDFs generated by non-Adobe apps can tend to be larger than they need to be. In this video you’ll learn how to make your PDF files smaller even if they were not generated by an Adobe product.
The application Acrobat 3D comes with an associated utility called Acrobat 3D Toolkit, which allows the 3D content in the PDF file to be enhanced by editing lighting, adding textures and materials, and creating animations. In this video tutorial you will learn to set up the Acrobat 3D Toolkit environment for technical illustration. Learn about the shortcuts and quick keys to quicken your workflow!

In After Effects 6.5, Adobe introduced Incremental saves. Rather than waiting for the auto-save to catch the latest revision to your project, incremental save allows you to manually save a new file, incrementing the name of your project in numeric integers. CINEMA 4D does the same. And with a little configuration, you can make it act exactly the same as in After Effects.
R4DS is a cartridge-based system that fits right into SLOT-! on a NIntedo DS. Here's how to install R4DS and be able to support ROMS, multimedia files, and homebrew games on your Nintendo DS.

Learn how to use Virtualdub - a free video editing program available online. Learn how to use Virutualdub to edit videos and convert video file formats.

Lillian Garcia demonstrates how to remove the polish from you nails and how to file your nails. The video explains how to apply nail polish remover and how to shape you nails with an Emory board.

Kuler is a beta Adobe application at labs.adobe.com. It allows you to choose color schemes using rules or completely at random, then export the colors as an Adobe Swatch Exchange file for use in all of the Creative Suite applications. In this video tutorial you will learn how to create color schemes using Kuler.

In this Podcast you’ll see how to make a form using Adobe InDesign CS2 and then export it as a PDF file. After your form is in PDF form, you can open it in Acrobat 7 Professional and create fields on top of the PDF. This enables users to fill out the form right inside their web browsers with the Free Adobe Reader. Check out this video and learn how to do it now!

Need to move your my documents folder in windows xp because you have 2 drives for video editing and want to keep files on one drive and the operating system on the other, or maybe you just have an older computer to which you've added a new drive? Find out how to use Tweak UI to change some the hidden settings to move your my documents folder.

One of the most promising avenues of attack in a web application is the file upload. With results ranging from XSS to full-blown code execution, file uploads are an attractive target for hackers. There are usually restrictions in place that can make it challenging to execute an attack, but there are various techniques a hacker could use to beat file upload restrictions to get a shell.

Everybody knows not to store sensitive information in unencrypted files, right? PDFs and ZIP files can often contain a treasure trove of information, such as network diagrams, IP addresses, and login credentials. Sometimes, even certain files that are encrypted aren't safe from attackers. That's where Zydra comes in — a tool for cracking RAR files, ZIP files, PDF files, and Linux shadow files.

TWRP is the premiere custom recovery for Android because of how many devices it supports and how simple it is to use. But installing it in the first place hasn't always been the easiest thing to do — until now. With the help of a Magisk module, you can finally use one Android device to flash TWRP on another.

With the Wigle WiFi app running on an Android phone, a hacker can discover and map any nearby network, including those created by printers and other insecure devices. The default tools to analyze the resulting data can fall short of what a hacker needs, but by importing wardriving data into Jupyter Notebook, we can map all Wi-Fi devices we encounter and slice through the data with ease.
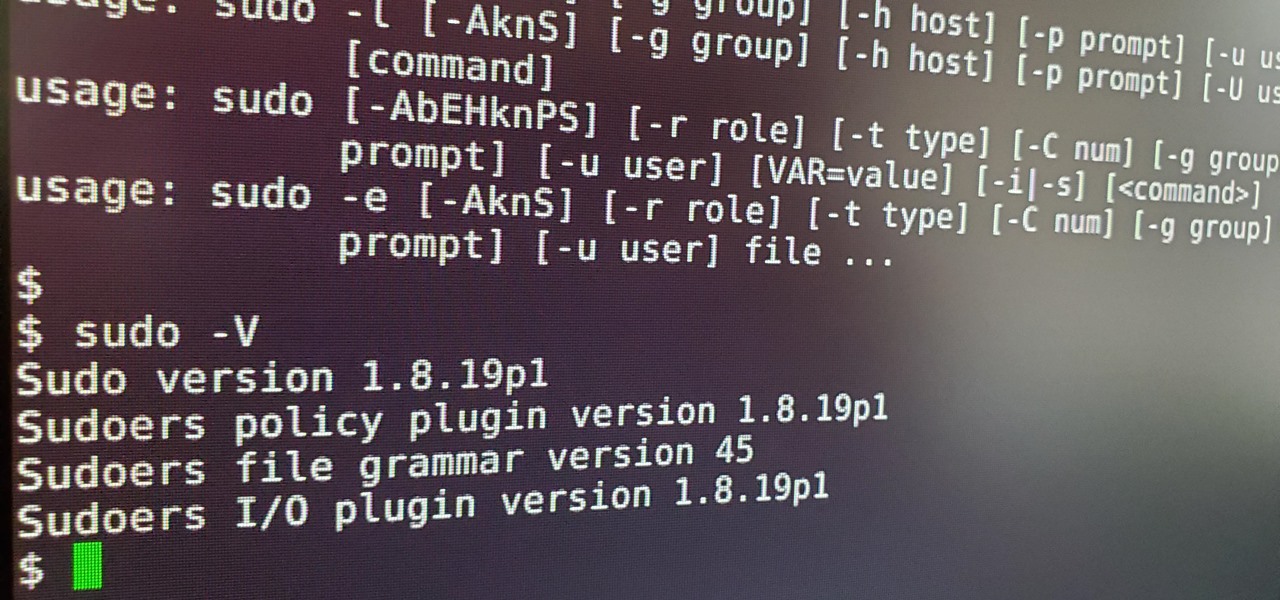
Anyone who has used Linux long enough is familiar with sudo. Short for superuser do (or substitute user do, depending on who you ask), it allows users to run commands as either root or another user on the system. From a hacker's point of view, sudo is often all that stands between them and root access. We'll be exploring an older vulnerability in sudo that allows a user to run commands as root.

Without admin privileges, installing additional software, or modifying the Windows 10 firewall, an attacker can alter a router and perform a variety of exploits. It's accomplished by forwarding requests from Kali through a backdoored Windows computer to the router gateway with simple SSH tunnels.
When it comes to sniffing Wi-Fi, Wireshark is cross-platform and capable of capturing vast amounts of data. Making sense of that data is another task entirely. That's where Jupyter Notebook comes in. It can help analyze Wi-Fi packets and determine which networks a particular phone has connected to before, giving us insight into the identity of the owner.

The USB Rubber Ducky and the Digispark board both suffer from the same issue when attacking macOS computers: a keyboard profiler pop-up which tries to identify any non-Apple USB keyboards. While it's an annoying setback, the solution is a simple modification that allows Mac computers to be targeted, which affects the ability to target Windows and Linux devices.

Reconnaissance is one of the most important and often the most time consuming, part of planning an attack against a target.

While you might suspect your MacOS computer has been infected with malware, it can be difficult to know for sure. One way to spot malicious programs is to look for suspicious behavior — like programs listening in on our keyboard input or launching themselves every time we boot. Thanks to free MacOS tools called ReiKey and KnockKnock, we can detect suspicious programs to discover keyloggers and other persistent malware lurking on our system.

Whether you're ordering a new 2019 iPhone model online or just want to know how they look in your hand before buying in person, use these printable cutouts to see which one looks and feels best.

In Apple Music, loving and disliking songs is a great way to teach Apple's subscription service what type of tunes you like and which you don't. While it also seems like it should be an excellent way to keep track of songs you enjoy in the wild, there's no clear way to view all of your loved tracks in one convenient list. There is a way, however, but easy it is not.

Automating port scanners, directory crawlers, and reconnaissance tools can be complicated for beginners just getting started with Kali Linux. Sparta solves this problem with an easy-to-use graphical interface designed to simplify a penetration tester's tasks.
During the Google I/O 2019 keynote, the latest Android Q Beta was released to the public for Pixel smartphones along with 15 other non-Pixel devices. It's the third Developer Preview for Android 10, but it's the first official public beta outside of Google's Pixel smartphones. A new public beta means good things are on the way as the future of Android continues to evolve.

Hot on the heels of all the talk about Google's newest Android Q update, known as Android 10, there's a new beta to check out. OnePlus is one of the many partners that can now offer its users a chance to test the latest version early. That means you can install the newest Android Q beta right this second on your OnePlus 6, 6T, or 7 Pro just like Google's Pixel smartphones.

The music and sound effects that play in the background of any videos you edit helps set the tone, so it's essential to get it right. Enlight Videoleap, an extremely powerful and popular mobile video editing tool for iOS, lets you quickly and easily add audio from your iPhone and the cloud, but things can still get a little confusing when you have a timeline full of clips.

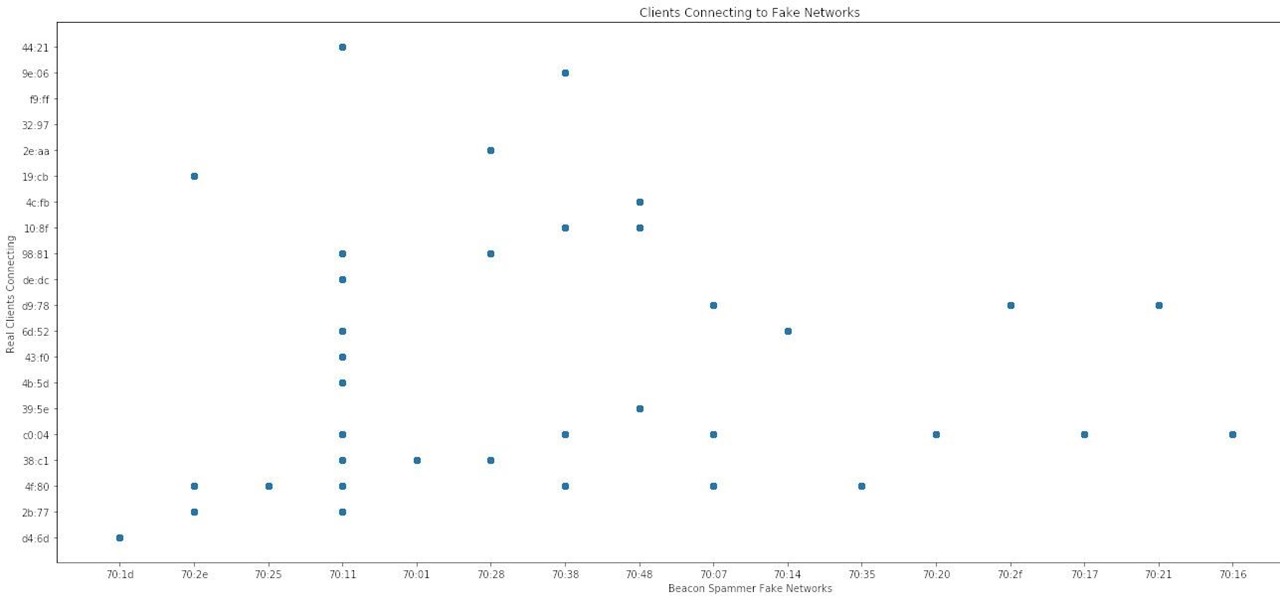
What if you could easily visualize which access point every Wi-Fi device nearby is connected to in a matter of seconds? While programs like Airodump-ng can intercept this wireless information, making it easy for hackers to use and understand is another challenge. Fortunately, a tool called Airgraph-ng can visualize the relationships between Wi-Fi devices from only a few seconds of wireless observation.

The legal drama framing the closure of Meta Company continues even after the company's assets have been sold to a new owner.
Recently, buzz for the Google Pixel 4 has been rising thanks to a patent discovered by 91mobiles. This patent appears to show an almost bezel-less phone with a screen-to-body ratio we have only dreamt of, and no notch in sight. The problem is this isn't the Google Pixel 4. It's actually the Pixel 2 XL.

New documents reveal that electric car company Tesla has filed a surprising new patent that has nothing to do with batteries or autonomous driving and everything to do with augmented reality.