Don't want to see the nine millionth request to join Farmville? Tired of some people sending you stuff on Facebook? Stop the madness with this video! Go to the requests at the top page, right side of the site. Click the requester you received then you can see the options below. Block this application and ignore all invites from this friend. Then click the ignore button if you want to ignore that requester.

There may be a time when you want to run a program for 24 hours straight. If that app happens to quit unexpectedly, you have some options to get it going again without having to manually reopen it. Check out this video on how to restart a crashed program automatically on Windows. You need WatchDOG.

How does one fertilize plants? Well, a fertilizer is a material that supplies the essential elements for plant growth. Most fertilizers are concerned with nitrogen, phosphorous and potassium. It isn't always easy to know which type of fertilizer to use. In this video tutorial, you'll find a guide to selecting the right fertilizer type for your application. Grow strong, healthy plants for a green garden with this how-to.

Once in a great while something comes along on the internet that’s so unbelievably simple and yet works so well. Twitter is one of them. On the video conferencing side, now we have MeBeam. MeBeam, which requires no software or drivers to be installed, is a web application that will permit you and up to 15 of your closest friends to hold a video/audio conference (provided you and said friends all have webcams or, at the very least, microphones). For further details consult this simple how-to!

In this installment of her Work Smart series, Gina Trapani returns to explain how to use three diverse applications to better synchronize the contents of your home, office, and whatever other computers you might have. They are Googledocs, Dropbox, and Evernote, and each one can help your files become easier to access from wherever you might be computing.

PEX, or cross-linked polyethylene, is a common alternative to copper piping. If you're looking to save time on your project (or have an aversion to soldering), PEX might be for you. In this tutorial, you'll learn what PEX is and how to decide what type of PEX is best for your application.

Traditional makeup is too boring for special occasions, so why not try something a little more fun to ring in the new year? This how-to video goes through the intensive process of applying a vibrantly colorful and ornate harlequin mask, using just makeup. The cosmetic products used to create this look are N.Y.C Yellow Concealer, Clinique Super Powder Double Face Make Up # 10 Matte Medium, N.Y.C Black Pencil Eye Liner, Graftobian Crème Foundation Yellow, Graftobian Crème Foundation #89092 Augu...

The augmented reality passthrough abilities of Facebook's Oculus Quest were only fully opened to independent developers recently.

The past year has revealed a gaping hole of opportunity in the world of business called virtual meetings. Some existing players like Zoom hopped on that opportunity, while others like Skype seemed stuck on the sidelines, and Google Meet just managed to catch up in time to snag some of the shift in remote work.

If you've ever needed to prove you have remote access to a device, or simply want a way to convince someone their computer is haunted, SSH can be used to make a device begin to show signs of being possessed.

While MacOS computers have been spared from some of the most famous malware attacks, there is no shortage of malicious programs written for them. To keep your computer safe from some of the most common types of malware, we'll check out two free tools. These tools can automatically detect ransomware encrypting your files and watch for unauthorized access to your microphone and camera.

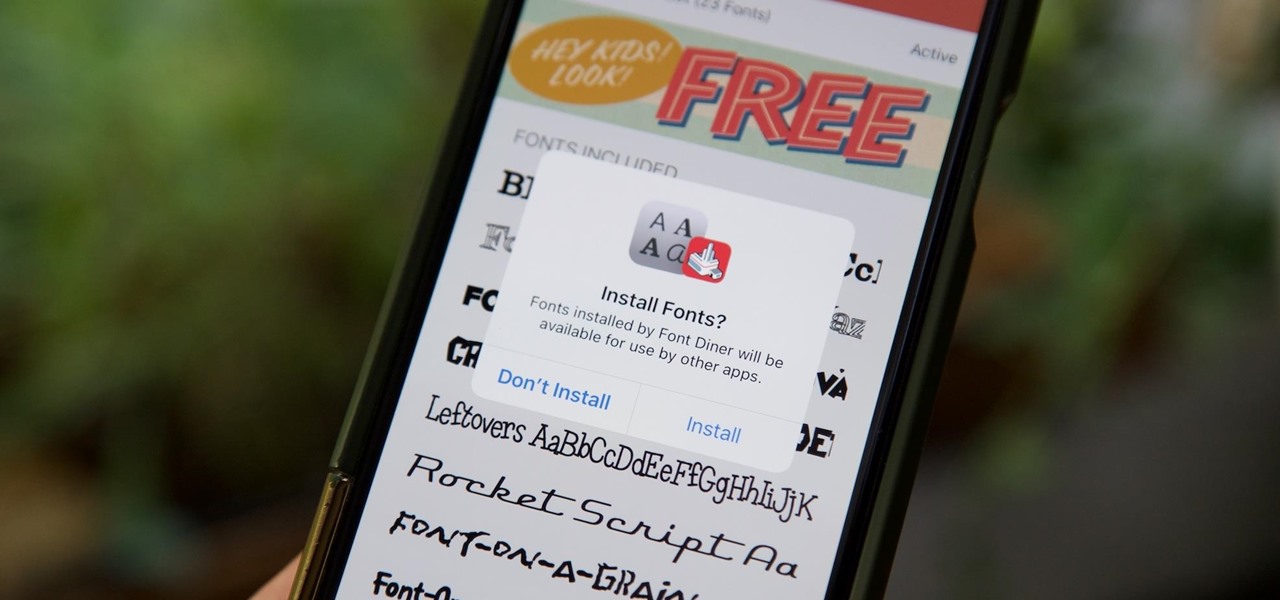
Apple added the option to install custom fonts and use them in different apps on iOS 13. The rollout has been a bit confusing, with Apple announcing partnerships with vendors such as Adobe, but also limiting the feature to work with only certain apps. Nonetheless, you can now download and install custom fonts on your iPhone.

QR codes are everywhere, from product packaging to airline boarding passes, making the scanners that read them a juicy target for hackers. Thanks to flaws in many of these proprietary scanning devices, it's possible to exploit common vulnerabilities using exploits packed into custom QR codes.

If you're worried about the security of your Mac, there are easy measures to prevent the most dangerous attacks. Named after the tactic of accessing an unattended computer in a hotel room, we can thwart "evil maid" attacks with Do Not Disturb and LuLu, free macOS tools by Objective-See that keep an eye on unattended computers and flag suspicious network connections that indicate a malware infection.

Automating port scanners, directory crawlers, and reconnaissance tools can be complicated for beginners just getting started with Kali Linux. Sparta solves this problem with an easy-to-use graphical interface designed to simplify a penetration tester's tasks.

If you have ever wanted to mod your Android device, your new best friend is easily going to be Team Win's TWRP custom recovery. This gives you access to file flashing on the fly, which can include such things as Magisk for root access, or even a custom ROM to replace the stock firmware that came with the device.

After a hacker has configured Metasploit on a remote private server, created a resource script for automation, and created a simple payload, he or she can begin the process of remotely controlling someone's Windows 10 computer with just a few moments of physical access — even if the computer is off.

Configuring onion services for the first time can be tricky. A surprising number of system administrators make seemingly trivial mistakes that ultimately lead to catastrophic cases of de-anonymizing supposedly anonymous sites on the dark web. OnionScan is a tool designed to identify common misconfigurations in onion services and aid us in understanding how to fix them.

If you need to scan a large number of domains for a specific web app vulnerability, Dorkbot may be the tool for you. Dorkbot uses search engines to locate dorks and then scan potentially vulnerable apps with a scanner module.

Due to the overnight success of smartphones, millions of people are connecting with others. Currently, over 15 million text messages are sent every minute worldwide. Most of this communication is happening in the open where any hacker can intercept and share in the discussion unbeknownst to the participants. However, we don't need to communicate insecurely.

Tor is an excellent obfuscation network for web traffic, and while instant messaging over the network is very useful, it can be relatively difficult to configure. In this guide, we'll look at two synchronous communications platforms (instant messengers) which can be routed over the Tor network, Ricochet and XMPP.

Tony Parisi, the global head of VR/AR at Unity Technologies, has been passionately working with virtual and immersive spaces for a long time. And while the internet world we live in now is very different than when Parisi was co-authoring VRML (Virtual Reality Modeling Language) — an early attempt at creating 3D environments that would work in a web browser — some of the questions that were assumed answered are being asked again.

The world is full of vulnerable computers. As you learn how to interact with them, it will be both tempting and necessary to test out these newfound skills on a real target. To help you get to that goal, we have a deliberately vulnerable Raspberry Pi image designed for practicing and taking your hacking skills to the next level.

One major component of Level 4 and Level 5 driverless cars is in very short supply. Venture capitalists and engineers from around the world are racing to fill the LiDAR production, price, and performance void.

In the music world, it's safe to say electric instruments are more versatile, but they lack the portability of their acoustic counterparts. However, with the aid of your smartphone plus an audio interface, you can play your electric instrument anywhere — with all the pedal effects you please — and even record your efforts.

Beginners luck is a phrase I have always hated. But really, beginners luck comes down to not letting your experience in something get in the way of the idea.

Welcome back, my aspiring hackers! In many of my earlier tutorials, I mentioned the complementary nature of hacking and forensics. Both disciplines, hacking and forensics, benefit from a knowledge of the other. In many cases, both disciplines will use the same tool. In this tutorial, we will use another tool that can be used in either discipline—Sysinternals—a suite of tools developed by Mark Russinovich.

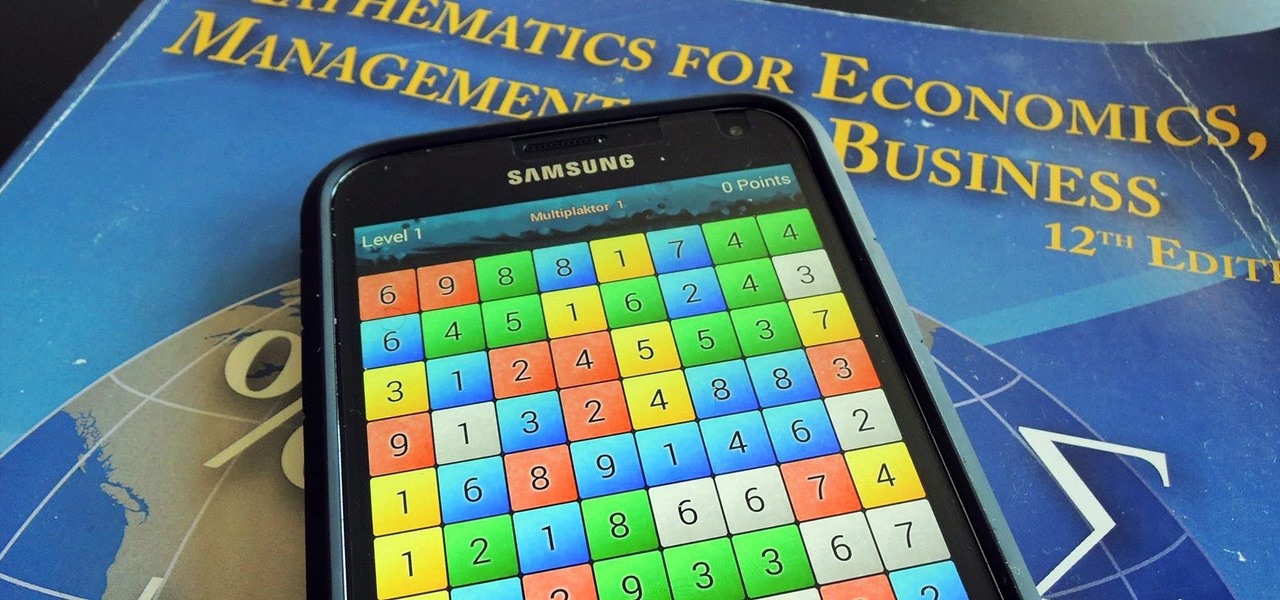
I am an English major physically allergic to all algebraic formulas, so you're unlikely to get any help from me when it comes to solving any expressions. But in the glorious technological age we live in, there are plenty of apps that actually make math and problem solving fun, even a little bit addictive.

Keeping data private is vital in the days of smartphones and the free-floating information they carry. Justin wrote a guide on many of the deeply hidden and sometimes concerning privacy settings in iOS 7. Now we're back to cover some of the new (and old) privacy settings in iOS 8 that you need to address right now.

Changing your iPhone ringtone can be a pain, even in iTunes. Other ways to change your ringtone include downloading software that takes up hard drive space and clogs your applications folder. There is another way, and it's a website called Audiko. It's a website for free ringtones for mobile phones and the iPhone. You just need to follow the instructions on the site and you'll have a new ringtone on your cell phone in no time.

In order to delete an application, or App, in your Apple iPhone or iPod Touch device, go to the home screen, where all of your apps are displayed together. Each app icon visible here is a button. Press and hold the button for any app until all the apps start wiggling. Once the apps are wiggling, an X will appear next to any app that can be deleted (some apps, like proprietary Apple software, cannot be deleted). Press this X, and you will be prompted with the option to either delete the app or...

This video is in the Electronics category and you will learn how to add or delete applications and icons to your iPod Touch. First, if you want to add something, go to Safari. If you want to add the iPod Touch bookmark to your home page, go down to where it says ‘add’ and press it. Then select ‘add to home screen’, give it a name and press ‘add’. That’s it. In order to delete something, press down any icon till all icons start to wriggle. Then press the small circle on the left hand top corne...

To become an American citizen you would first have to fill out an application, then take a naturalization examination. Providing that you have been a legal resident in the U.S. for more than five years, you would then have to appear at a court hearing. You have to be eighteen years old, have good moral character, and be loyal to the United States. You would need to know how to read, write, understand and speak the English language; and have a general knowledge of our country's history, our go...

Want to make maximum use of your iphone/ipod-touch screen? Shrink is a software that does this by reducing the size of the application icons down to 75%, 66%, 50%, 33% or the ultra small 25% of it's original size. This video highlights the user friendliness of this app and the ease of switching from one icon size to another. There's also a mod to increase the size of the icons to increase the accessability for people with vision impediments. The iphone on the video is displayed using DemoGod ...

IMVU is a 3D avatar chat, instant messenger, and dress up game. Get help with all of your IMVU avatar needs with these IMVU tips and tricks! Watch this video tutorial to learn how to make IMVU avatar eyes in Paint.

IMVU is a 3D avatar chat, instant messenger, and dress up game. Get help with all of your IMVU avatar needs with these IMVU tips and tricks! Watch this video tutorial to learn how to edit hair and skin in IMVU (09/20/09).

Print what you want, how you want. While browsing, choose the content you want then edit and print exactly what you see on your screen..

SQLite is a small C library that implements a self-contained, embeddable, zero-configuration SQL database engine. SQLite implements a large subset of SQL-92 and stores a complete database in a single disk file. The library footprint is less than 250 KB making is suitable for use in embedded devices and applications where memory space is scarce.

In this video clip series, our expert will explain the use of fake (false) eyelashes, how to apply them, the types of glue needed for false eyelash application, as well as tips and techniques for trimming false eyelashes.

This video shows you how to control your computer from your iPod touch. 1. Go to UVNC. Click on Installation. This will take you to download options. Download the latest stable version. 2. Install Hamachi, which helps you find your computer's IP address. Click on Download Here link, fill in the registration information, and click submit. 3. Install a VNC listener on your iPod so it can connect to your desktop. Jailbreak your iPod, and open the installer. Click All Programs; scroll down until ...