Welcome back, my budding hackers! In this series, I have been trying to familiarize you with the many features of the world's best framework for exploitation, hacking, and pentesting, Metasploit. There are so many features, and techniques for using those features, that few pentesters/hackers are aware of all of them.

Hello again, folks! I'm back with another (final) guide on runtime crypters which is an extension on my previous runtime crypter guide. If you have not read it yet, I highly recommend that you do since the fundamental theory of the PE format. Again, this will be a Windows-specific guide, so I'll repeat this: If you're a hater and cringe at the slightest sound of Microsoft's grotesque baby, feel free to close this tab, delete your history, exit your browser, pour some oil onto your machine and...

NMAP is an essential tool in any hacker's arsenal. Originally written by Gordon Lyon aka Fydor, it's used to locate hosts and services and create a map of the network. NMAP has always been an incredibly powerful tool, but with it's newest release, which dropped mid-November of last year, they've really out done themselves.
Welcome my aspiring hackers and programmers! Today i will introduce you to a programming language that as a hacker you should have in your set of hacking/programming skills (except if you're only interested in web hacking/programming...then you should go learn some html or PHP instead of C#).

Welcome to my tutorial where Voidx and I will be expanding on my previous article to provide more clarity into the logic of the code.

I saw many people asking for a Tutorial about writing their own Remote Administration Tool, so I now introduce you in a basic kind of RAT. This program is not for real use, but for learning how you could write this kind of tool. It will be basicly coded and not very refined. I used Python 3, so you have to install it if you want to use this program unchanged. Also this RAT is for Windows and almost all features won't work under Linux.

First of all, Merry Christmas and Happy New Year to all Null-Byters that learn and teach in this wonderful site. In this article we will explore the basics of the meterpreter's IRB (Interactive Ruby Shell).

I'm back. School's an ass. On my quest for knowledge, which started approximately 3 years ago, I can upon an interesting little artifact. It is called the Arduino.

Do you ever thought that you can't control an Internet disconnected system? I saw a funny video in Chema Alonso's youtube channel (A well-known hacker of my country and creator of Fingerprinting Organizations with Collected Archives among other security tools), and decided to post something similar.

Greetings null-bytians. Firstly, I would like to apologize for the no images thing. I guess I can't upload them.

This is my first tutorial and it is about accessing deep web for total beginner,sorry in advance if I make any mistake plz forgive me.

Hello, everyone! Many of you don't even know about my existence here on Null Byte, so I thought of contributing something rather interesting. Recently, someone asked how to make your own "Bad USB," and I promised to make a how-to on this topic. In addition, it would be nice to have something related on our WonderHowTo world. So here it is!

Since I first announced the new Null Byte recognition for excellence a few weeks ago, several of you have written me asking, "How can I study for this certification exam, and what material will be covered on the exam?" Now I have an answer for you. The White Hat Hacker Associate (CWA) will cover 14 domains or areas. Everything you need to know is here on Null Byte. There will be no questions that are not covered here on this site, guaranteed.

Black lights come in all shapes and sizes, and they're useful in a variety of ways. They can help you spot fake currency, urine stains, interesting rocks, and deadly scorpions, and they can even help you view cool fluorescent artwork.

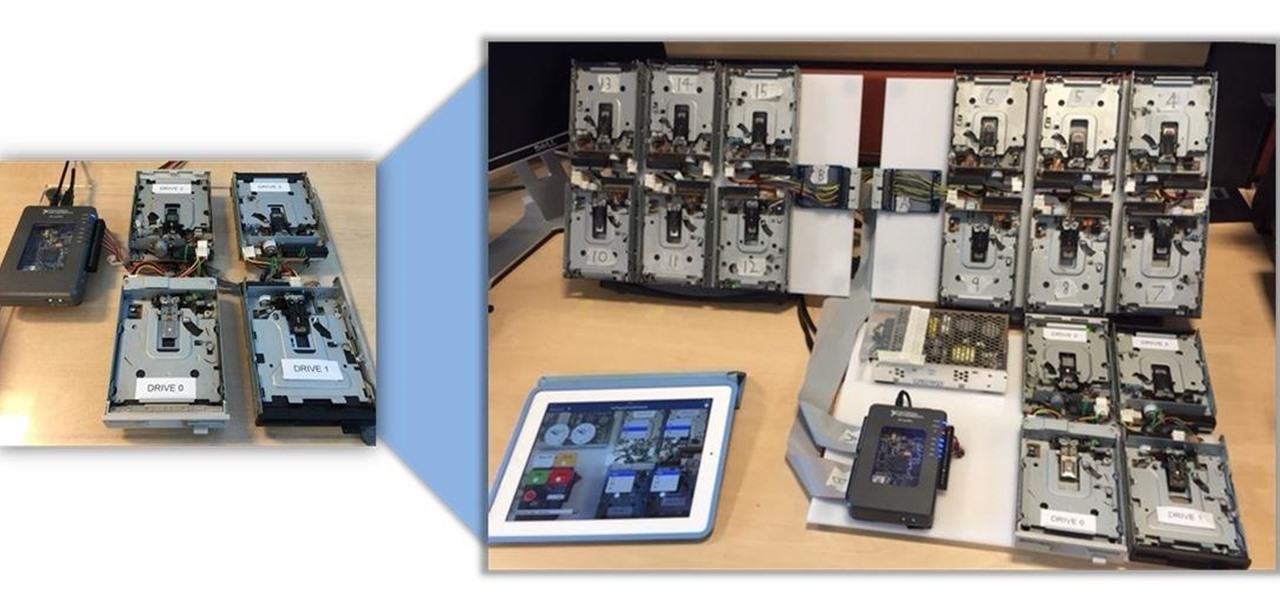
Video: . Being one of the most popular DIY/maker projects around, Musical Floppy Drives are nothing new. However, myFloppyDriveOrchestra includes a few unique features, which separate it from the crowd.

All of Apple's products are praised for being extremely easy to use. So much so, that your grandma can pick one up and be a "pro" within a few hours. However, this isn't necessarily a good thing for us real power users who want more granular control of our devices.

Hate slogging through pages and pages of weighty books and lengthy work documents? You may not be able to depend on speed-reading apps, but with the right font, you can increase the number of words you scan each second, speeding up your reading pace exponentially.

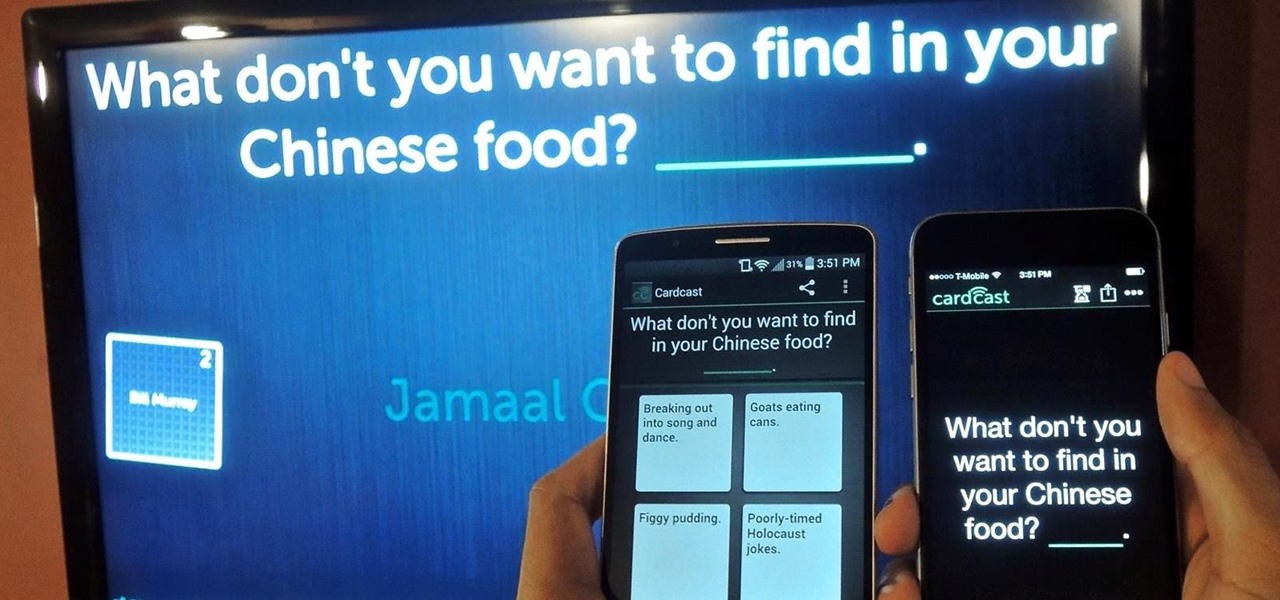
The future of game night is digital. Your Chromecast is great for watching Netflix or YouTube, but get more use out of it by making it the centerpiece for your next fun get-together.

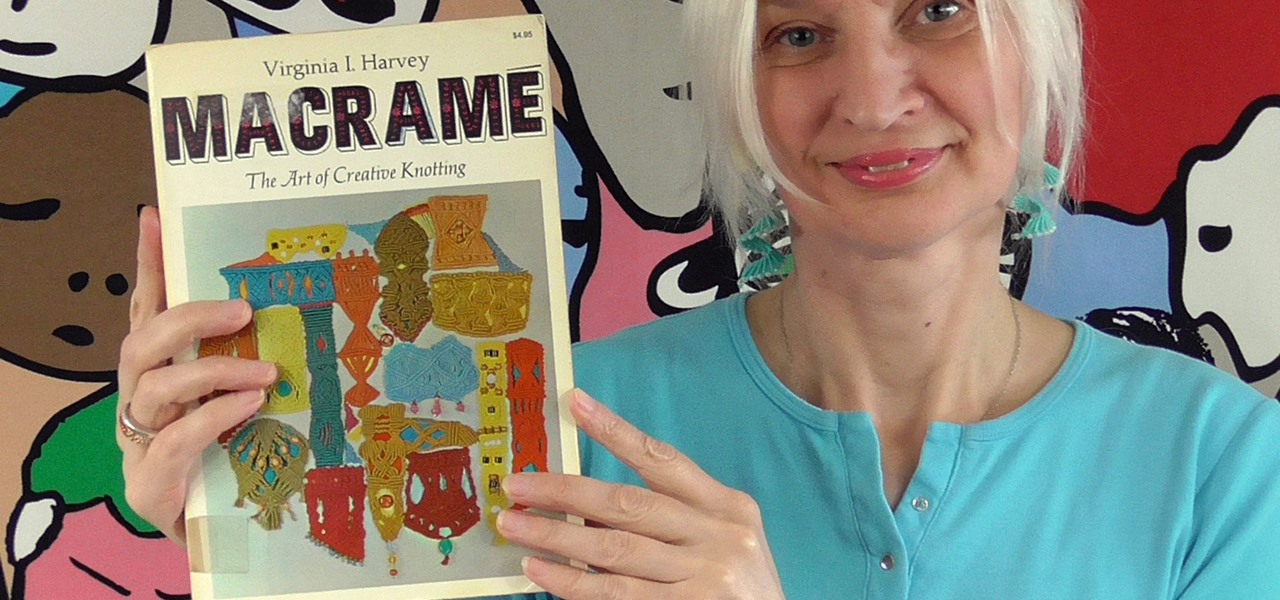
The book that started it all (published in 1967). When Virginia Harvey wrote this book, she remarked that macramé was almost a lost art...

A friend of mine has a crazy amount of Reddit karma and gold, and yesterday he let me in on his secret. This person, who will remain unnamed for obvious reasons, created a Python script called Reddit Karma Crawler that finds rising posts before they get too popular.

Autocorrect, a common feature available on most Android keyboards, helps fix fat-finger typos and even predicts the words you want to write. Without this feature, it'd take me about 5 minutes to write a sentence, and even then, it'd probably still be intelligible.

One of the down-sides of international long-haul travel is layovers between flights in unfamiliar places. We have a flight to Europe this year via Guangzhou, China, and I've been putting together my notes on how to make the best use of 7 hours between flights, which I'd like to share.

Editor's Note: The claims by Vani Hari which were originally detailed in the article below about azodicarbonamide were unscientific in nature. This article has been updated to reflect that and provide more scientific context on the issue.

Video: . Here there are some DIY gift ideas perfect for the Christmas season. They are really easy to personalize depending on what your likes are.

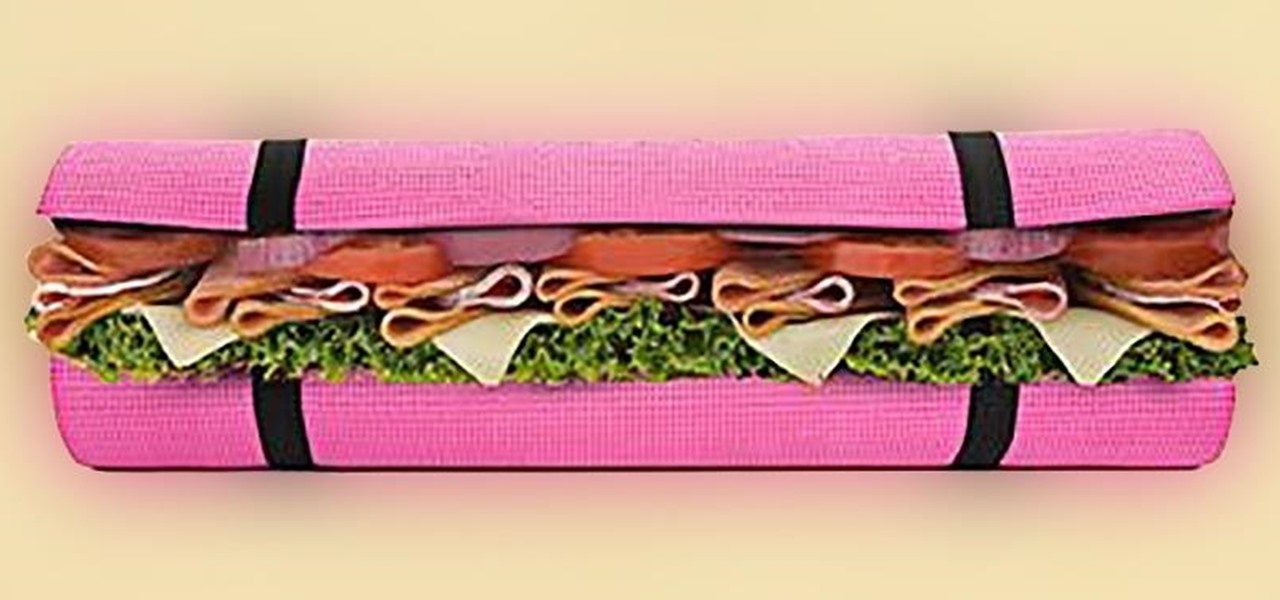
With only a few days left until Halloween, your options might be rather limited if you still don't have a costume. You may have laughed while some people spent the entire month of October painstakingly crafting their ridiculously detailed costumes, but now that the big day is so close, the joke's on you because you still have nothing to wear.

Note to admins: If there's anything wrong with the links or the article itself (legality), let me know.

Below are the official rules and guidelines for submitting content to WonderHowTo. Please look over them before publishing any articles. Ignoring the rules could result in deletion of your article or being flagged as a spammer. Most of these rules apply to comments as well.

What happens when you find your ball deflated and there's no pump or needle in sight? You could always cancel your plans of kicking around the soccer ball or starting that pickup football game in the park. Better yet, you could be terribly clever and find another way to get air into the ball. From a pen to a balloon to a gas station, there are ways to inflate it.

According to WitsView, 8-inch displays will rule the tablet scene this year at 11.9% market share, compared to yesteryear's 2.6% market share. By year's end, it'll be almost 18%.

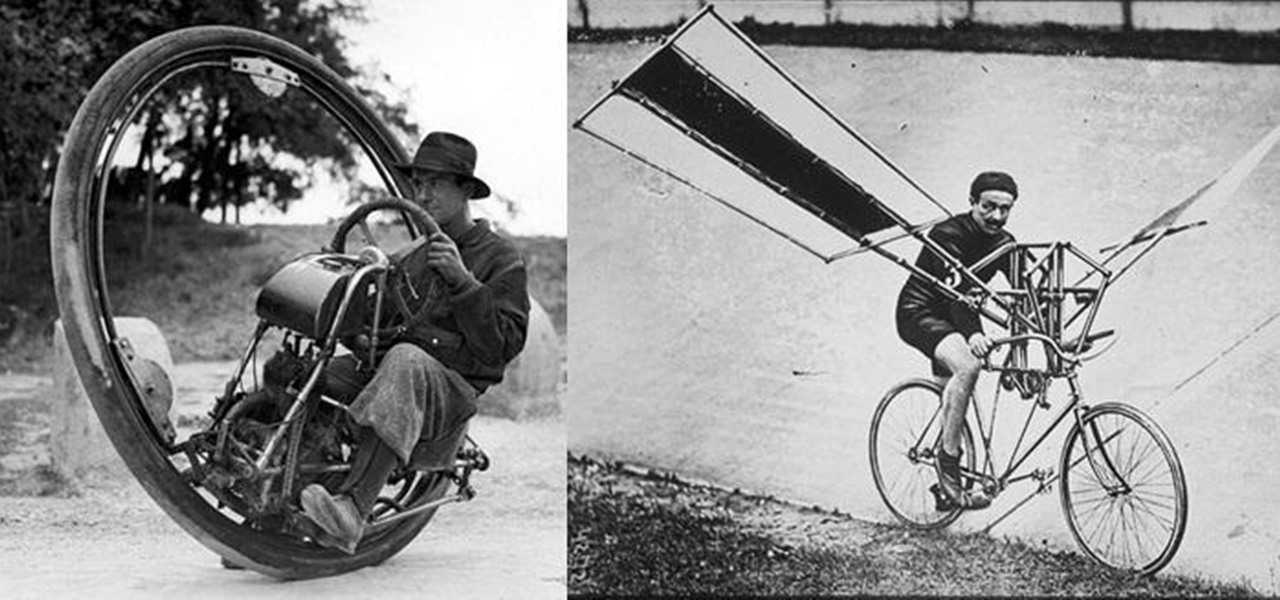
We don't spend much time thinking about bicycles today, do we? Sure, they're a "green" alternative to driving everywhere in cars, but the vast majority of America has dismissed them as simply being too much work, or more importantly—too slow. That wasn't always the case, though, I assure you!

The upcoming web series "Crypto-Historians" does for cryptohistory what Indiana Jones did for archaeology. For those who don't know, cryptohistory is the study of supernatural or alien elements throughout history, and yes—it's a "real" field.

Cross-dressing and gender-bending are nothing new, but the realm of Steampunk seems to be especially accepting of role-reversal in dress.

Many people that I know who have gone to see the Hobbit have come back unimpressed or annoyed with the film. I LOVED it. When those non-specific people, cough Loziers cough, gave me their reasons for not liking the movie, I was very annoyed... I considered the demands that they were placing on Peter Jackson and his team to be very high and unreasonable. So, as a method of venting my anger, here is how to watch the Hobbit. If you’ve read Lord of the Rings and the Hobbit, please, go back, and R...

It's no secret that there's a lot of surveillance going on these days. It's easier than ever to end up in a database, and even former government agents are speaking out about the atrocious amount of spying being done against our own citizens. They've targeted our laptops, cars, IP addresses, and now they're coming for our iPhones. AntiSec hackers managed to get their hands on a list of over 12 million Apple UDIDs (Universal Device IDs) from an FBI computer, and they published 1,000,001 of the...

Letters of recommendation are important in the business world. If you have been asked to write about a coworker, student or friend, check out this tutorial. Takes you through a step-by-step process you can use to produce a professional-looking and highly effective letter of recommendation. Includes how to structure your letter, how to personalize it for your candidate, and how to make it convincing to the recipient.

Learn how to burn an ISO file to a blank DVD or CD using Ashampoo burning studio. What you will need: - Ashampoo burning studio- A blank CD/DVD- A CD/DVD drive which can burn CDs/DVDs 1. Open up Ashampoo Burning Studio and go to "create/burn disk images" then click the first option. 2. Browse for you ISO file. 3. Click on "next" and then insert a blank DVD or CD (use a CD for files less than 700mb). 4. Select the CD/DVD drive under "CD-writer". 5. When you see a green tick, click on options a...

This video shows the viewer how to fill in a standard golf score card. The video shows a man filling in a score card with fictitious scores to demonstrate how a card should be filled in correctly. The video also shows how to incorporate a player’s handicap into a scorecard.

Bring a little magic and wonder into the lives of those around you with this easy magic trick. The best part is all you need is an envelop, pen and someone willing to reveal their age and birthday. Make sure to play up the suspense.

This video features a very handy technique for writing a cover letter in less than a minute- and all you need is a tool called Text Expander, which can be easily downloaded. The basic idea behind this program is that you can create shortcut keys to text that you commonly use, so you can enter in all of your basic cover letter information very quickly, and only have to customize small sections.

This is quite possibly the most disturbing Halloween costume ever. Seriously. It nailed creepy down to a tee. A friend of Redditor YouHadMeAtBacon did this gory unzipped zipper face makeup, and it's by far the best I've ever seen. Unzipped Zipperfaces in Action