Every time you log in to a website in Safari on iOS, you're also asked if you would like to save the username and password—a great feature of just about all browsers that makes it so that don't have to enter your credentials each time you access website in the future. While this feature is great for quickly getting into all your favorite websites, have you ever wondered where all those passwords are saved on your device? In this guide, I'll be showing you where to find all of the stored usern...

Taking care of your car requires effort, whether you take it to the pros for washes, waxes, and detailing, or you spend time to make it shine yourself—and it often seems that, right after your car is sparkling again, rain or midnight moisture appears to cover its surface in water spots. With a small tweak to your typical car care routine, you may be able to keep your car's surface and windows shining longer and better: you just need to add a little hair conditioning liquid.
Hi guys, I'm gonna keep this short because I got assignments and a lot of notes to study and also other how-tos and forums to reads. lol...Since I'm keeping this short...no story time just scenario. And I want to thank n3stor for giving me the idea to post this.
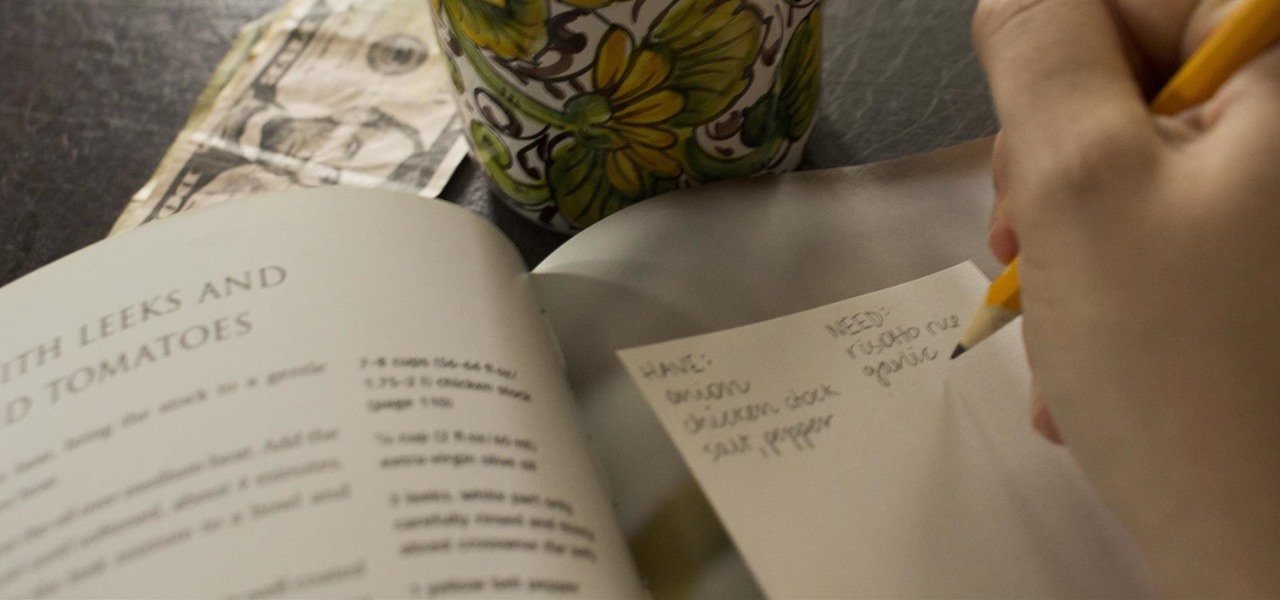
To be twentysomething is an awkward time for entertaining. As we graduate college and begin to work in “the real world,” there is a yearning to transition from keg parties into dinner soirées. However, though the desire is there, often the bank account is not. Here are some ways to do in the kitchen what twentysomethings do best: fake it until you make it. (In other words, host a fabulous dinner party for four and still be able to make rent this month!)

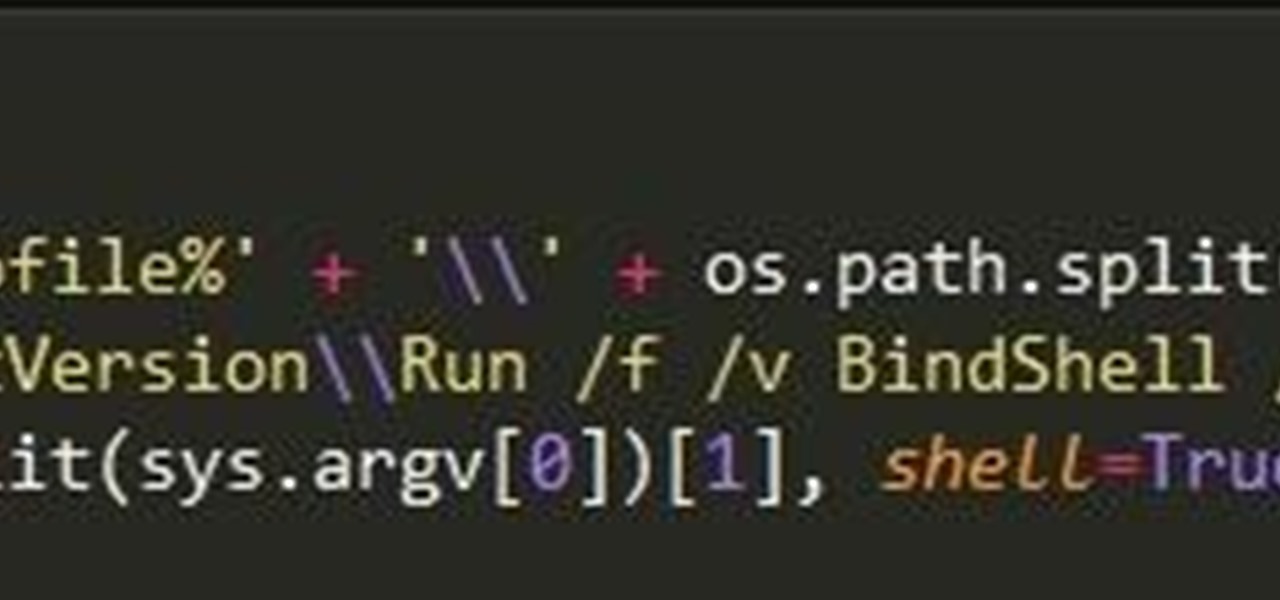
In this tutorial I will be explaining the purpose of unique encryption/decryption scripts ( I will be referring to these at "UEDS" for this tutorial). Then, I will show you how to make one. Finally I will talk about the downsides to the method I use. I will also provide links explaining the concepts and algorithms used in encryption to anyone who wants to see what is going on under the hood.

When a migraine strikes, it can be crippling. Intense and sharp pain not only at the temples, but radiating throughout the entire head; feelings of nausea and digestive discontent; an unbearable aversion to light, sound, and even the smallest of movements.

Being born with a sweet tooth and Japanese blood, my desire for dessert-style sushi is practically written into my DNA. At once delicious and adorable, these one-bite delights are the perfect way to conclude a meal. They're also a killer snack. Featured below are: 1) the Banana Nutella Nut Roll; 2) the Strawberry Kiwi Roll; 3) Mango and Sweet Rice Nigiri.

Just recently, I was experimenting with a dual-boot Windows setup, and somehow managed to wipe my primary Windows installation in the process. "Why," I asked myself, "Why didn't I make a backup before I started this?" Still to this day, I'm going through the painstaking process of installing and configuring all of my favorite programs, and I may not ever get things back exactly the way they were.

There are a bunch of new and interesting features packed inside of Windows 10, but one of the most exciting ones is the Microsoft Edge web browser, the long-awaited replacement of Internet Explorer.

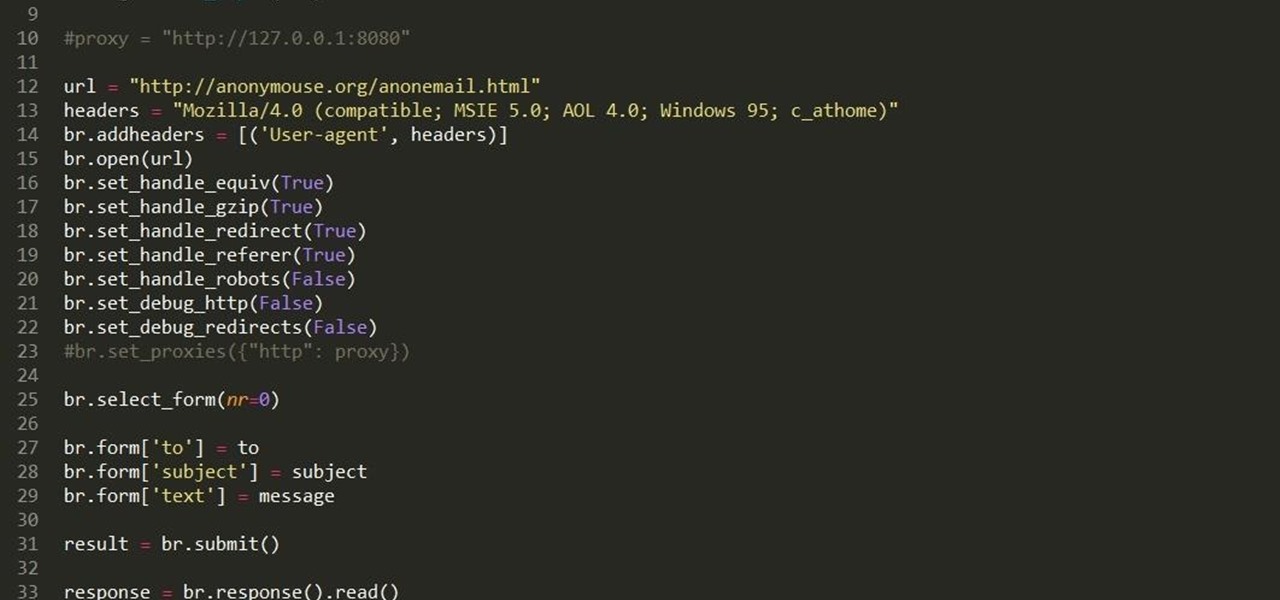
Hello fellow grey hat hackers, as hackers it becomes necessary for us to be able to send emails anonymously. Whether for whistle blowing or pranks or social engineering or whatever, it just is necessary for us to do that.

Make no bones about it—having an "undo" option is a freaking godsend. Whether you accidentally deleted an entire essay, screwed up the shading on a Photoshop job, or sent an email that wasn't quite ready, having the option to undo a click or button-press can definitely be a lifesaver.

The next time you're out camping, whether it's outdoors in the wilderness or right outside in your own backyard, try this hack out for an effortless campfire all night long. While there is definitely some prep work involved, it's well worth it if you don't need a huge bonfire, and more so if you plan on cooking meals over the flames.

Welcome back, friends! Many times, businesses, friends, and family will lock their zip files with a password to keep their files secure. It is reasonable, and understandable. Well, thanks to hackers, there are many ways to get past this wall of security.

As you might know, there are a multitude of tools used to discover internal IP addresses. Many of these tools use ARP, address resolution protocol, in order to find live internal hosts. If we could write a script using this protocol, we would be able to scan for hosts on a given network. This is where scapy and python come in, scapy has modules we can import into python, enabling us to construct some tools of our own, which is exactly what we'll be doing here.

The Galaxy S6 already has one of the best cameras on the market, but a few minor annoyances still linger. Full-sized photos are stored with heavy compression that can cause artifacting, burst mode shots aren't taken at 100% quality, and the camera flash cannot be used when your battery is below a certain threshold.

My reliance on autocorrect has made me a horrible speller. I take it for granted that it'll catch all my mistakes, but it only ends up making matters worse (especially when it inadvertently makes correct words wrong). So instead of relying on autocorrect to fix typos, why not try to completely prevent mistakes from happening in the first place?

Carriers like to distinguish their Android phones from the competition by making small changes to the interface here and there. This practice is so common that Android now has a built-in system for managing these small tweaks.

Eating flowers is a time-honored culinary tradition, from nibbling on nasturtiums to grazing on candied violets. And why not? They look beautiful and lend a unique floral flavors to salads, desserts, and anything in between.

Hi there, Crackers, Welcome to my 7th post (Part-1), this tutorial will explain about the basics of Batch Scripting.

Smartphones don't generally play nice with tripods, so videos taken with our handheld devices make terrible source material for time-lapse photography.

I have a thing for black foods, whether it's mysterious, lovely black garlic (the secret to its color: fermentation) or adding charcoal powder with its reputed health benefits to cookies, cakes, and breads.

Samsung is known for its added features, but occasionally, these can cross the line between functionality and bloat. For many users, this is the case with the "S Finder" and "Quick connect" buttons that are hard-coded into the notification tray on most Galaxy S6 and S6 Edge variants.

For 365 days of the year, our mothers show their love for us by driving us places, cooking us food, doing our laundry, and being our number-one cheerleader. But for one day of the year, we all get up early in the morning and show our love for our favorite women. Often, that means cooking breakfast or making brunch, or running to the store to grab a pre-selected bouquet of flowers.

Rather than reaching for aspirin the next time a headache strikes, try grabbing a drink of lemonade instead. Not only can it help ease your head pain, but it can also help relieve stress, anxiety, and depression. But not just any old lemonade will do the trick—reach for the lavender lemonade.

Many of Google's stock Android apps are some of the best options out there—especially now that they've all been made over with Material Design. But generally, as these are pre-installed system apps, they cannot be used on non-Nexus devices.

Master Lock combination padlocks have been known to be vulnerable to an attack that reduces their 64,000 possible combinations down to 100. I've devised a new attack for cracking any Master combo lock that simplifies the process and reduces the amount of work down to only 8 combinations.

My morning just doesn't start without a cup of coffee and an incredibly hot shower. There's nothing better than sloughing off sleep with a dose of warm, cleansing water. Except, as scientists are pointing out, our habit of showering daily isn't exactly the healthiest choice. Though it feels great, if you have a shower-a-day habit like I do, you're showering all wrong.

If you've got a desktop computer, I can almost guarantee that you've got a widescreen monitor set up in landscape mode. It's how just about everyone uses their monitor these days, including myself. Except that it's not always the best way of working.

Hi everyone! After messing around a little bit with IDA and Hopper disassemblers and briefly introducing you to memory, registers and Assembly, we are going to understand what happens when a process is running, which variables join the play and especially what happens when a function is called and why is this procedure-logic so interesting and useful along with the concept of stack.

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

It can be pretty tough to fall asleep when your brain is thinking nonstop or anxiety has gotten the best of you, and it seems to only get harder when you're lying in bed listening to yourself breathe. Yet paying attention to that breathing may be exactly what you need in order to find a calm, easy entry into a good night's rest.

At first glance, mandolines seem like such a good idea. After all, who wouldn't want a tool that can create picture-perfect and paper-thin slices of fruits and vegetables that would put even the sharpest chef's knife to shame? Your French fry game would never be the same. Salads would become works of art. Your casseroles would cook perfectly evenly, since the ingredients would be cut uniformly.

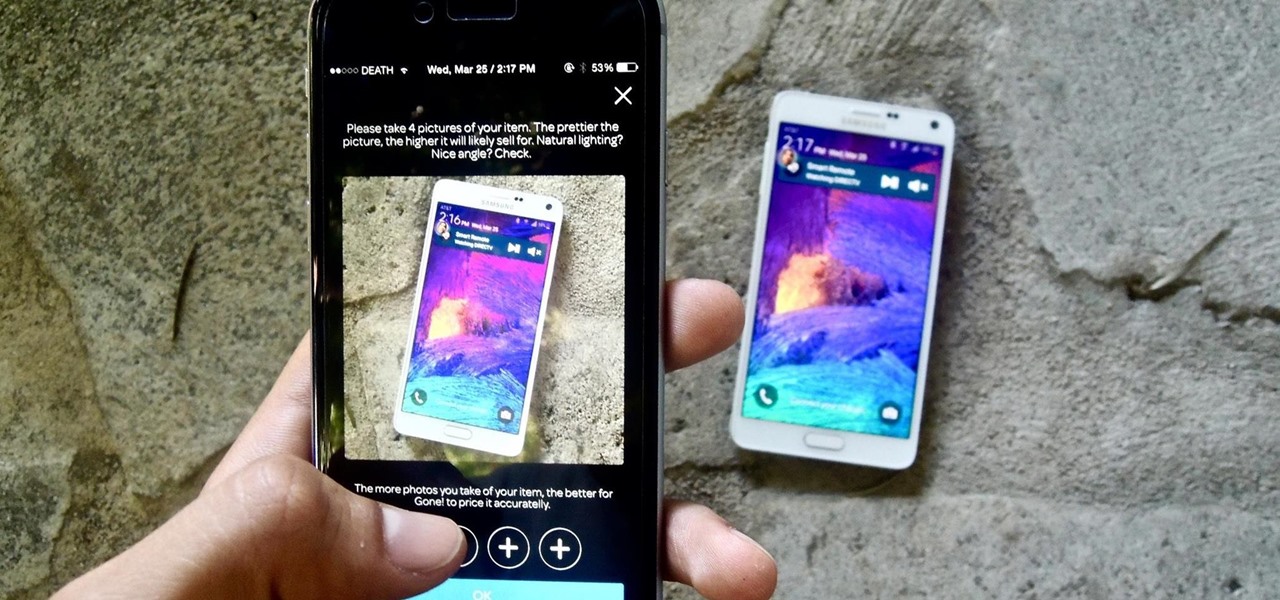
If you want to sell all of the old electronics lying around your home, it takes a lot of work. If you go the eBay route, you have to take tons of pictures, describe it accurately, wait for a week until someone bids on it (or not), then package it, ship it, and wait for feedback. Craigslist is a little bit easier, but usually requires you driving somewhere to meet the buyer in a public place (if you want to play it safe).

Edit: Some of the methods I show you may be difficult, or not work at famous or high quality hotels.

Sushi aficionados and Simpsons fans alike know all about the joys of fugu. Known also as blowfish, it's reputed for being tasty if sliced from the correct part of the animal and many even say they experience a "fugu high" after eating the fish. Alas, if you have an unskilled chef, fugu is famous for being deadly.

Welcome back, my greenhorn hackers! As hackers, we often take for granted that nearly all of our hacking tools and operating system are free and open source. I think it's important to examine a bit of background on how we arrived at this intriguing juncture in the history of computer software. After all, we pay for nearly all of our other software (Microsoft, Adobe, etc.) and nearly everything else we use in life, so how is it that Linux and all our hacking tools are free?

Eye contact is key in conversations, job interviews, and honesty, and it can help you access others' thoughts and spot heavy drinkers. Locking eyes with someone can even help you fall in love, whether you know them or not.

Welcome back, my tenderfoot hackers! Hacker newbies have an inordinate fixation on password cracking. They believe that cracking the password is the only way to gain access to the target account and its privileges. If what we really want is access to a system or other resources, sometimes we can get it without a password. Good examples of this are replay attacks and MitM attacks. Neither requires us to have passwords to have access to the user's resources.

Hello my fellow hackers, Welcome to my republished revision of the ruby programming language, Part 1.