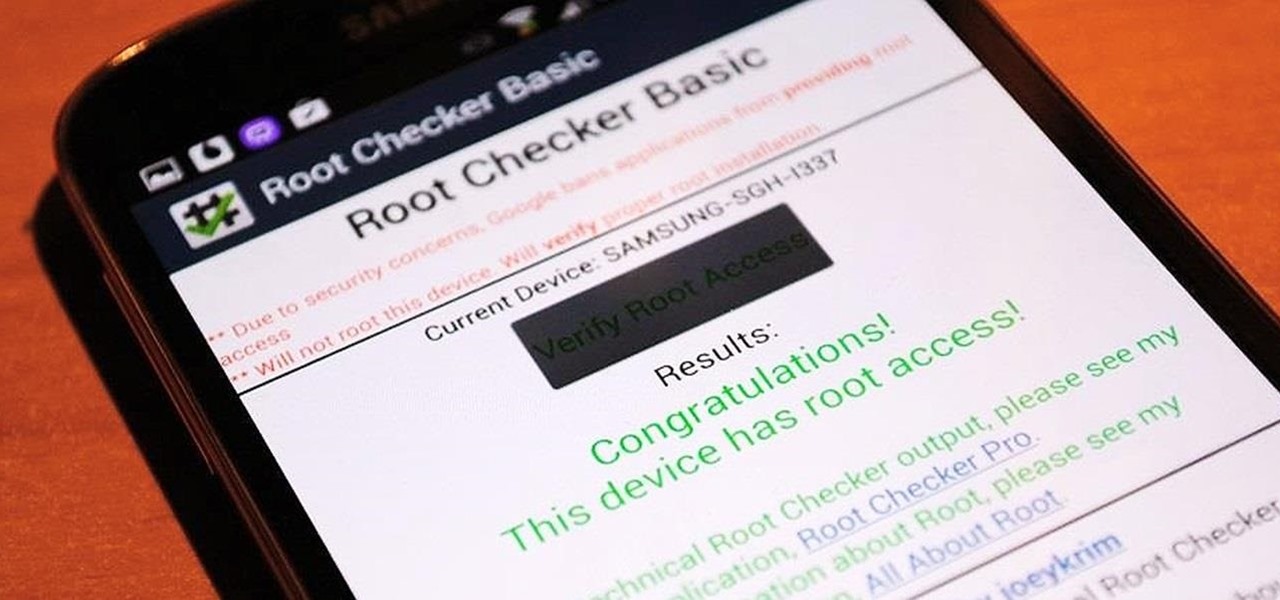
It's time. You've experimented with apps from the Play Store, you've switched your lock screen, and maybe you've taken different launchers out for a spin. If, throughout your tinkering, you've found yourself chanting, "More. More. Give me more!" then now is the time. It's time to root.

Welcome back, my fledgling hackers! It's been awhile since we did a Metasploit tutorial, and several of you have pleaded with me for more. I couldn't be happier to oblige, as it's my favorite tool. For the next several weeks, I'll intersperse some new guides that'll help expand your Metasploit skills and keep you abreast of new developments in Metasploit, so look for them in the near future.

With the Android 4.4 KitKat update slated for release sometime in October (according to Nestle), I'm sure you're excited to get your hands on and test out all of the new features of Google's latest mobile operating system.
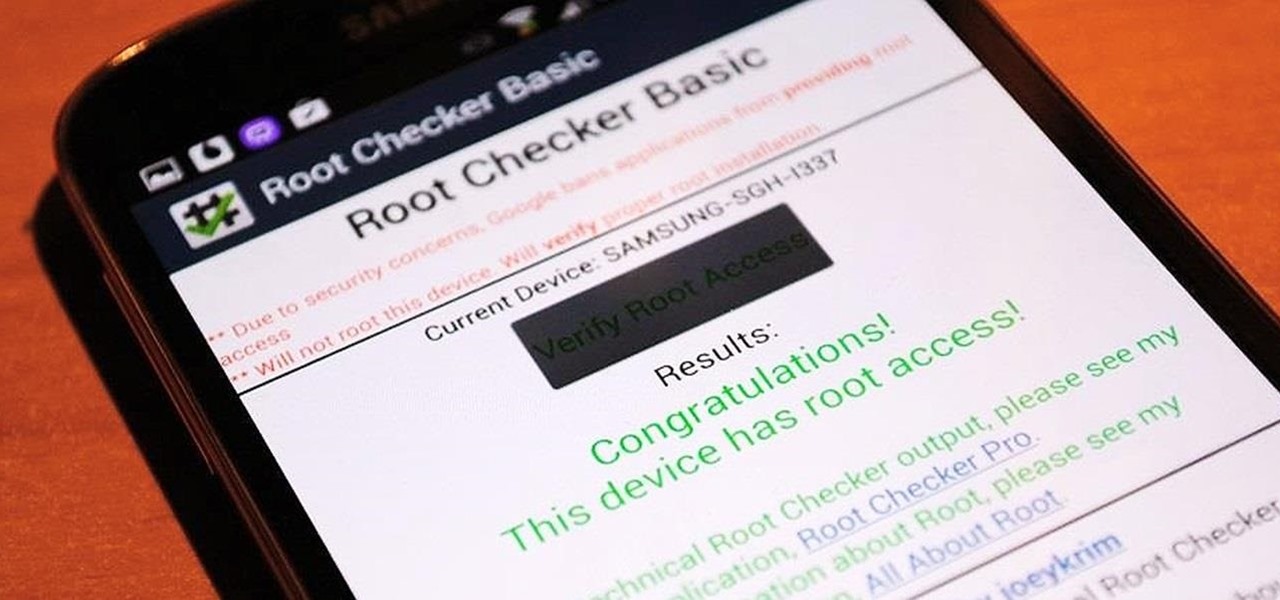
Rooting is usually the first thing on the to-do list whenever one of us softModders gets a new Android device. Unfortunately our efforts are sometimes hindered by certain obstacles; a common one is a locked bootloader.

Welcome back, my aspiring hackers! As mentioned several times in previous Linux tutorials, nearly everything in Linux is a file, and very often they are text files. For instance, all of the configuration files in Linux are text files. To reconfigure an application in Linux, we simply need to open the configuration file, change the text file, re-save, and then restart the application and our reconfiguration is applied.

Welcome back, my fledgling hackers! Nearly every commercial enterprise worth hacking has an intrusion detection system (IDS). These network intrusion detection systems are designed to detect any malicious activity on the network. That means you!

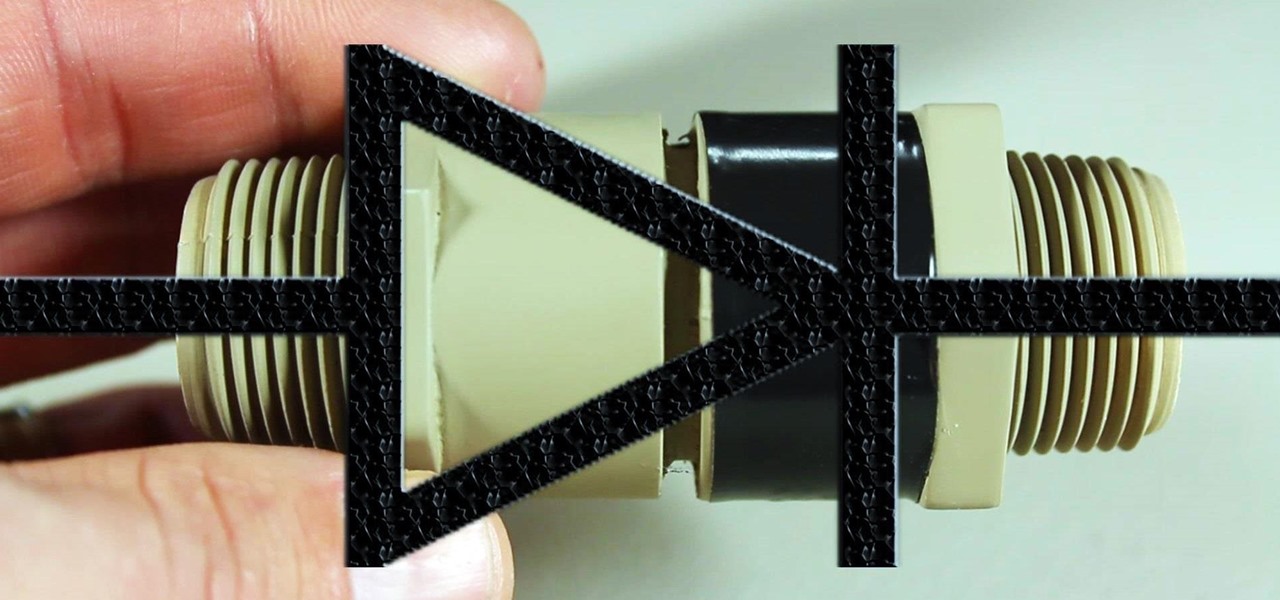
If you're going to build yourself a water gun to cool down this summer, or maybe just a useful water pump, you'll need some check valves. However, the most expensive parts of a water pump or DIY super soaker are usually the check valves. So, let's make some from scratch for as little as $0.35 each.

Welcome back, my hacker trainees! A number of you have written me regarding which operating system is best for hacking. I'll start by saying that nearly every professional and expert hacker uses Linux or Unix. Although some hacks can be done with Windows and Mac OS, nearly all of the hacking tools are developed specifically for Linux. There are some exceptions, though, including software like Cain and Abel, Havij, Zenmap, and Metasploit that are developed or ported for Windows.

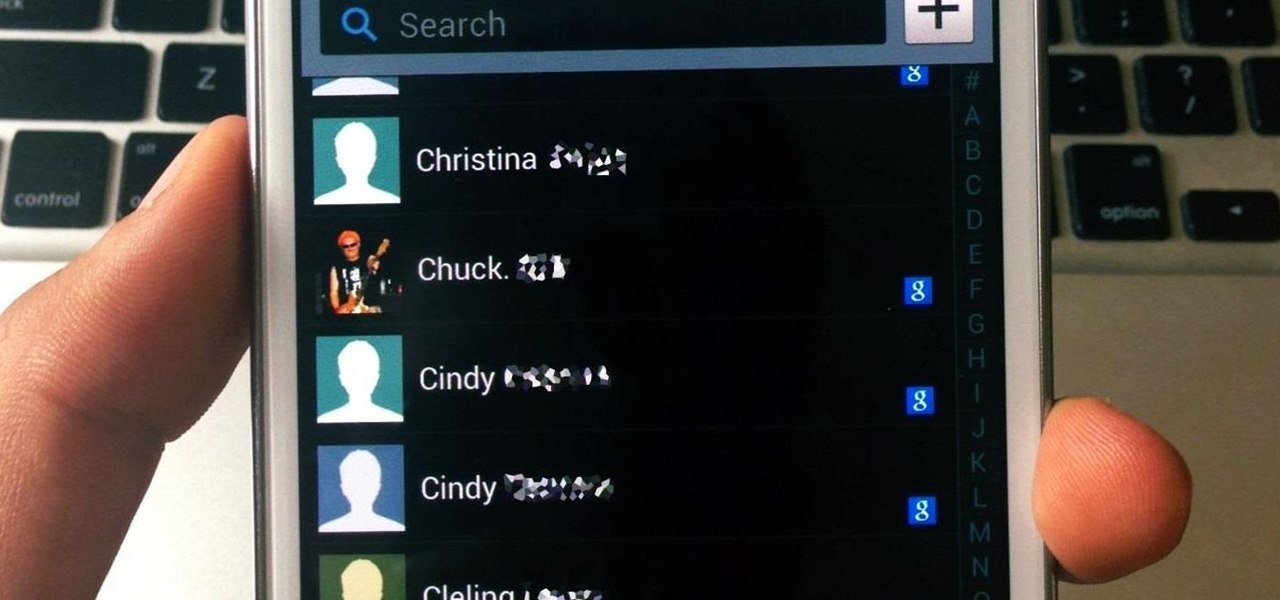
Why is transferring contacts from an old smartphone to a new one still insanely difficult? I can check my bank account, upload a picture to Instagram, email someone across the globe, and check the weather forecast on my phone—all in under five minutes.

At one point in the '90s, about fifty percent of the CDs produced worldwide had an AOL logo. About fifty percent of the CDs in my home still have that AOL promise of 500 free hours on them. Though they never got me to join their internet service, I did get a lifetime supply of coasters. Thanks to the rise of high-speed internet access and bigger and better hard drives, there's no reason for companies to snail mail any more of those obnoxious plastic discs.

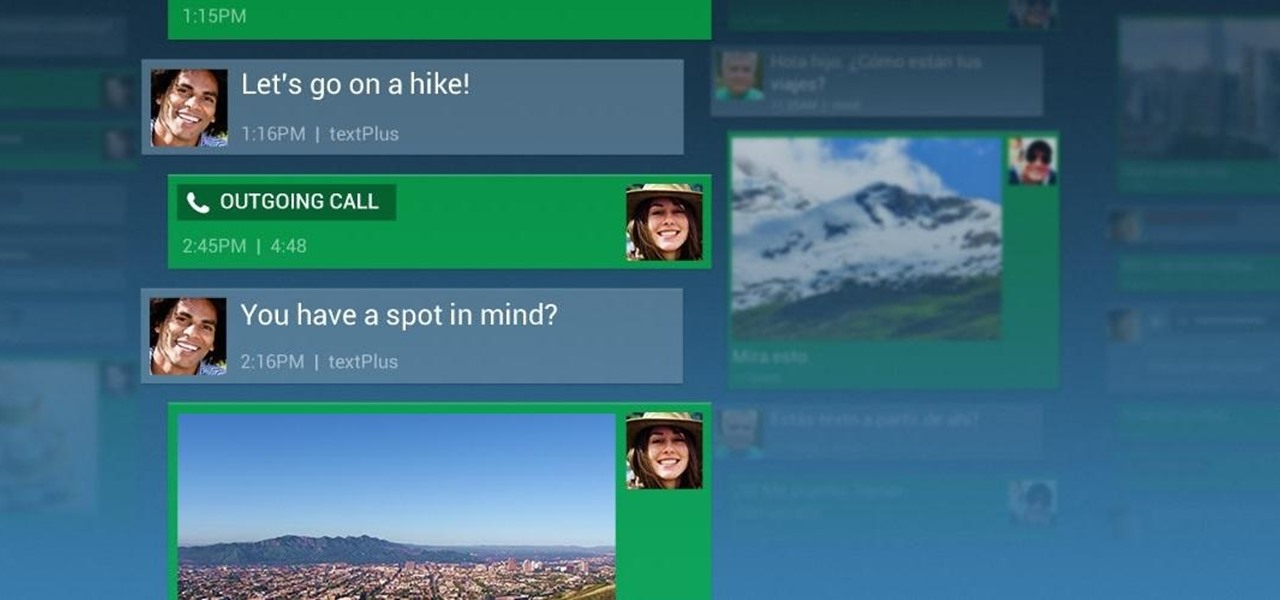
Smartphones are great. They help you keep in touch with your loved ones and stay up to date on what's going on in the world. The problem is that like everything else that's useful, they cost money to use, and between calling, texting, and data plans, it can get really expensive.

Every Windows system includes command prompt; and while a lot of people on Null Byte and WonderHowTo in general know how to use it, some people don't know anything about it, even how to access it.

PRL, or Preferred Roaming List, basically tells your phone which towers to connect to first. Changing PRLs can improve reception and data speeds, and in some cases even give you access to corporate/test towers.

This is my first contribution in an ongoing series on detailing the best free, open source hacking and penetration tools available. My goal is to show you some of the quality tools that IT security experts are using every day in their jobs as network security and pen-testing professionals. There are hundreds of tools out there, but I will focus and those that meet four key criteria:

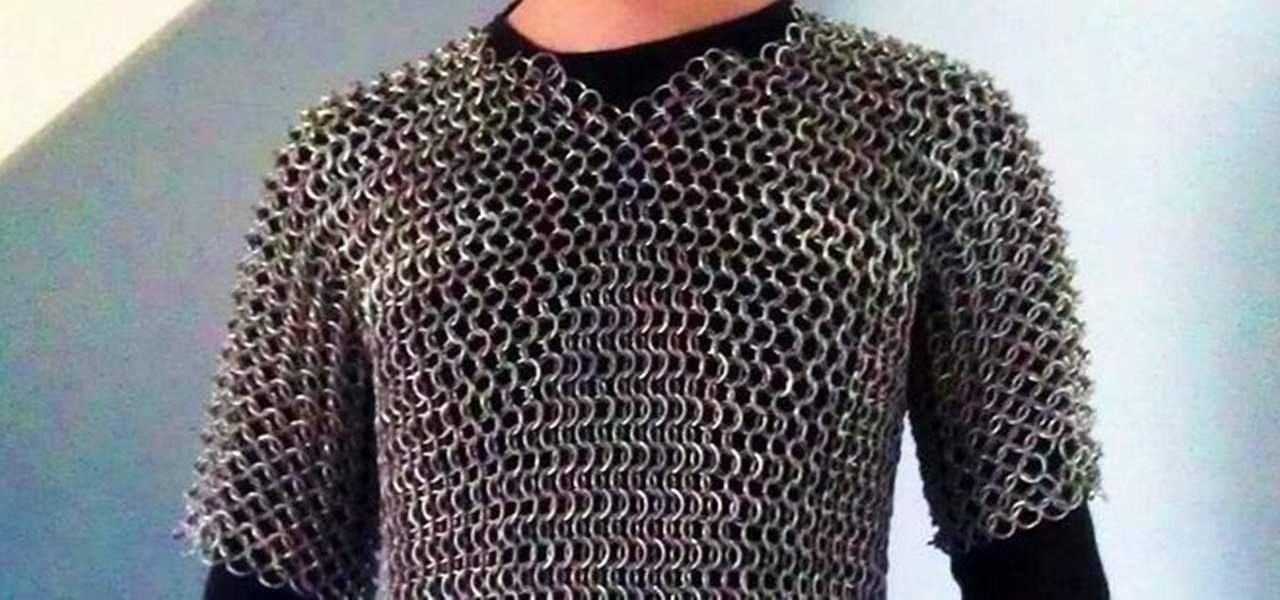
This article is a guide for making Chainmail Armor from start (simple wire) to finish (a finished chainmail shirt). We will be using the European 4 in 1 weave, as this is the most common weave. This is the weave that you usually see in movies. There are several sections to this guide: Materials, Making the Rings, Weaving the Rings, and Making the shirt.

|Choose Your View: Quick Bullet Points | Detailed Descriptions Android's newest major update is a special one — it's the tenth full version of the world's most commonly used operating system. The latest release, dubbed simply Android 10 (codename Android Q), was first showcased as a beta back in March 2019, so we've been digging around in it for several months. There's one dramatic visual change, plus there are a lot of goodies in general.

For many, phones are starting to replace televisions as the primary device for watching videos. Thanks to their portability and easy to use apps, it's often simpler to watch Netflix, Hulu, YouTube, or Prime Instant Video on the smaller screen. But not every phone is suited to fit this need, so we did some testing to find the best of the best when it comes to streaming videos.

You may have heard of a signal jammer before, which usually refers to a device that blasts out a strong enough radio signal to drown out the reception of nearby devices like cell phones. Purpose-built jammer hardware is outright illegal in many countries. Still, Wi-Fi is vulnerable to several different jamming attacks that can be done with Kali Linux and a wireless network adapter.

In five short years, three generations of ultra-low-cost Raspberry Pi devices have challenged the boundaries of what a person can do with a $35 computer — especially with Kali Linux.

Notch loves Halloween. He must, because he keeps putting scarier and scarier things into Minecraft around Halloween time!

Learn the trick to drawing a Ferrari, but not just any old Ferrari, the Ferrari 599 GTO, the mother of all Ferraris. It's the car any man or woman would love to own, and it has some serious power built into it. Not only does this car have beauty, but it has brains and muscle, too. DragoArt has this video tutorial on how to draw a Ferrari 599 GTO animated car. Get more detailed instructions on the step-by-step cartoon drawing here.

In this video series, our expert shows you how to operate the common stair step machine. Though the stair stepper has amazing potential to burn calories, it can be dangerous if not used properly. Sheila Lindsey illustrates the proper way to use the stair master machine. She also shows you how to monitor and stay within your heart rate. Shelia also gives you great advice on organizing a cardio workout routine. So, before stepping up to the challenge, learn how to get the most out of your stair...

Today, sailing is usually done for leisure or pleasure rather than traveling or moving cargo. While shipping is still the most viable way of moving goods overseas, with the advent of the airplane, sailing has transformed from a necessity to a sport. Some people put their sailing skills to the test in sailboat races; some just find it exciting to be riding the ocean waves on a non-motored vehicle, using techniques which sailors have employed for thousands of years.

In this video you can learn how to make an easy origami fortune teller. Fold an 8 1/2 by 11 inch sheet of paper into a triangle shape. There will be a strip of paper left at the bottom of the paper after completing this step. Cut off this strip of paper and discard it. Open the paper, which is now a perfect square, and lie it on a flat surface. Notice the 12 inch crease that you have down the center of the paper. Take a ruler and measure 6 inches down that crease. Place a small dot at the 6-i...

For a car to operate normally, it must have some basic care and maintenance. In these free automotive repair videos, learn how to maintain your engine cooling system. The cooling system keeps your car from overheating on the road; a lot of heat is generated by an internal combustion engine, which must be properly dissipated. Our expert will show you how to check antifreeze levels and mix and refill your fluid if needed. He’ll also give you tips on how to find leaks, and how to flush your cool...

In this video series, watch as freelance designer Emily DeCola teaches all about marionettes. Learn how to work the strings, the different types of marionettes, how to string a marionette, how to build and operate a marionette, and how to control the puppet's face.

For a car to operate normally, it must have some basic care and maintenance. In these automotive repair videos, learn how to maintain your engine cooling system. The cooling system keeps your car from overheating on the road; a lot of heat is generated by an internal combustion engine, which must be properly dissipated. Our expert will show you how to not only spot and remove the heater core hose in a car but how to determine what is wrong with it, change it if needed and reassemble the vehic...

In this video series, learn how to make homemade hot link sausage. Karl James walks you through the step-by-step process of cutting, seasoning, and stuffing your own sausages. You will learn how to operate a meat grinder, and how to tie off sausages after they have been stuffed. He even shows you how to smoke your sausages over a grill. With this spicy sausage recipe, you will be sure to impress. So, start learning how to make homemade hot link sausages today!

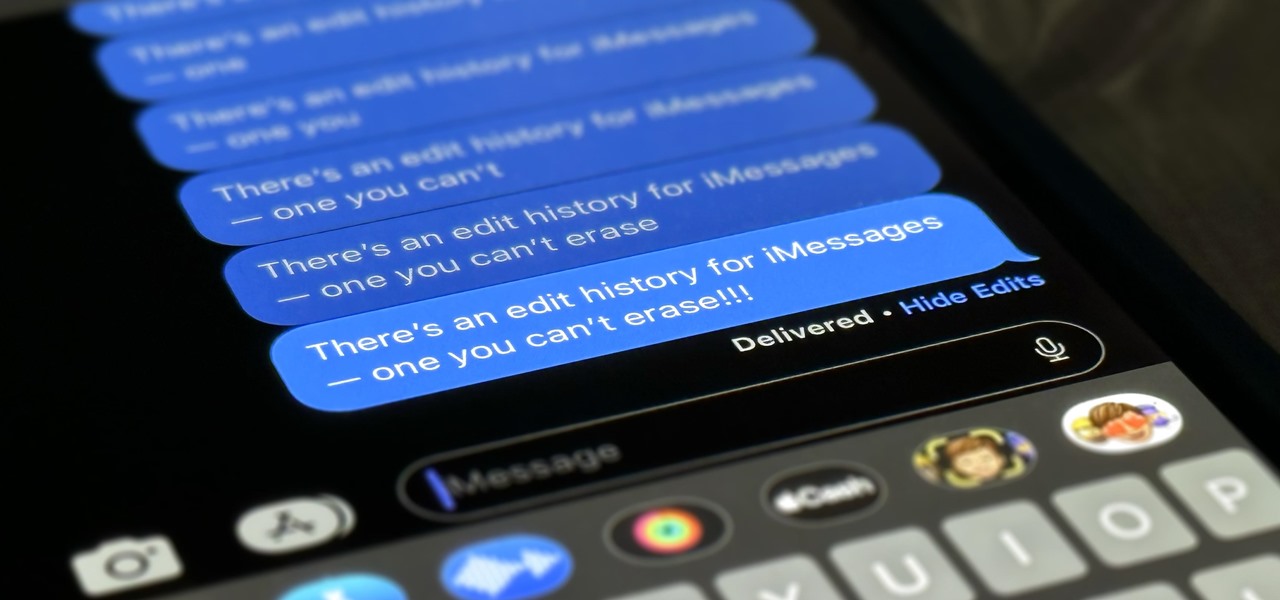
Apple lets you edit iMessages in the Messages app on iOS 16 and later, but everyone in the chat can see all the edits between the final and original text. Thankfully, there's an easy workaround to stop that from happening when you only want them to see the last message and nothing else.

While Apple has included a vibration motor in the iPhone since the beginning, it's never let us use it for haptic feedback on its default keyboard — until now.

On Monday, the social media giant Facebook suffered a massive outage that, as of this writing, is still in effect.

As if answering Apple's major iPhone event on Tuesday, Chinese mobile giant Xiaomi held its own product launch event the following day.

The fight to wrest control of apps from Apple's revenue-focused grip just took a major turn in favor of Epic Games.

Having thousands of photos and videos in your Photos gallery can make it difficult to find the best ones, but your iPhone does make it a bit easier. Memories, which have been around since iOS 10, automatically group your photos and videos into mini-movies by location, date, or person. It's a fun feature that does the work for you, and it's getting better with the release of iOS 15.

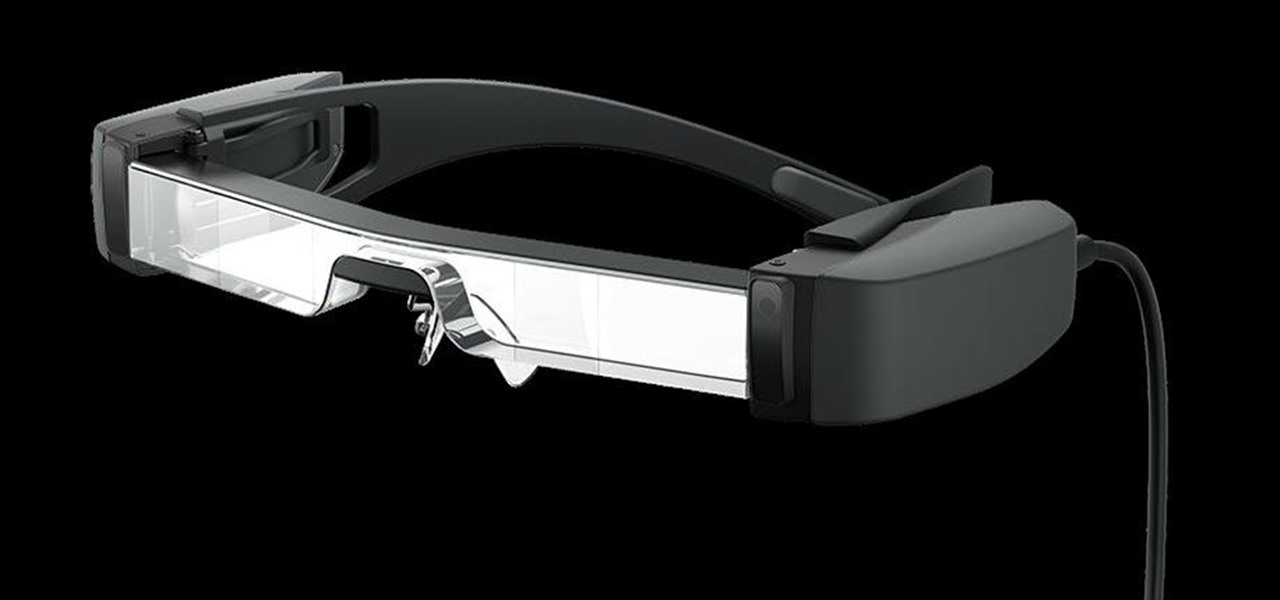
The last few weeks were fairly busy in the realm of augmented reality and remote meetings developments. Most of that activity was generated by some mammoth announcements from Snap and its Spectacles AR smartglasses, and Google, with its Project Starline experimental holographic video conferencing system.

The ability to browse the web in coffee shops, libraries, airports, and practically anywhere else you can imagine is more than convenient, but convenience has risks. Using public Wi-Fi allows others to spy on you easily. Even your own internet service provider can see every website you've ever visited. Don't fall into the trap of protecting your identity, data, and devices after it's too late.

Since its launch two years ago, the HoloLens 2 has been the best AR headset available, and nothing has come close to touching it since.

Linux is a diverse and powerful operating system that virtually every IT professional must learn and know well. Whether you realize it or not, you have likely already used a Linux device, and learning to design things for it is a key step in any Data Science career path.

The average business person likely recognizes Epson for its printers or even its projectors, not the futuristic AR wearables.