We don't know exactly what form 5G cellular technology will take, but it intends to bring faster Wi-Fi-like performance to mobile devices. While that'll provide major advantages to lots of connected technology, PC Magazine notes that it could be what augmented and mixed reality needs to become widely adopted.
Complex games in mixed reality require a pretty detailed scan of the room, and getting this process right can be both time-consuming and annoying. Computer science students at the University of Washington decided to fix that by turning it into a game.

Netflix has become the subject of heavy buzz this week, and not due to the latest season of Daredevil (which gets two thumbs up, btw). The online video entertainment provider is drawing fire over its admission that it has been throttling video streams for its AT&T and Verizon customers for years.
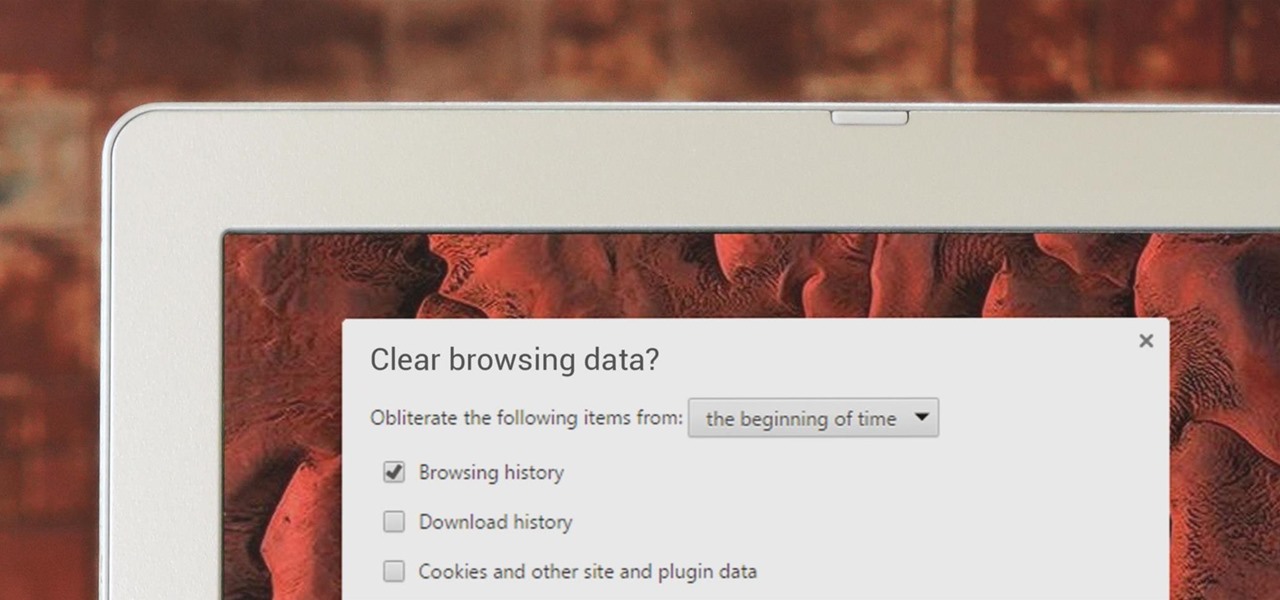
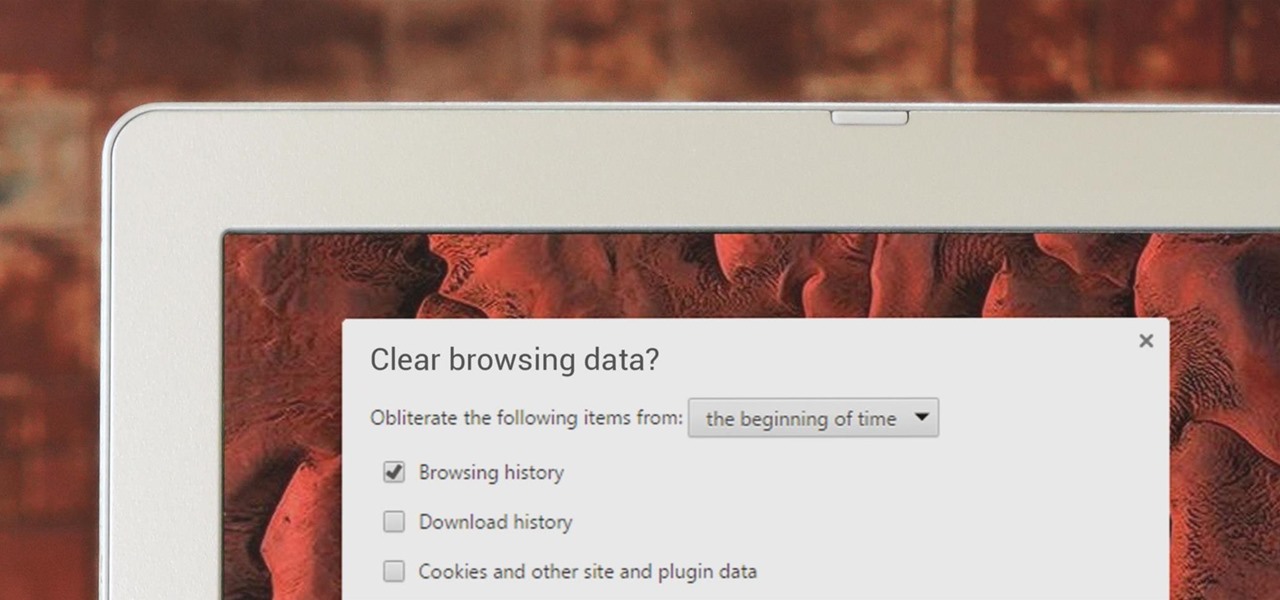
If you've been visiting websites of ill repute, or if you've been Christmas shopping and don't want to spoil the surprise, it would be a disastrous situation if anyone were to come across your browsing history. Visited sites, cookies, and cache can paint a very clear picture of your recent internet activity, and depending on the situation, you may only have a few seconds to delete your history before someone else barges in.

In the recent hit movie Furious 7, the storyline revolves around the acquisition of a hacking system known as "God's Eye" that is capable of finding and tracking anyone in real time. Both the U.S. spy agencies and an adversarial spy agency (it's not clear who the adversary is, but the location is "beyond the Caucasus mountains," which could imply Russia?) desperately want their hands on this system.
T-Mobile's credit-checking system was recently hacked, and this one is about as bad as it gets. The names of 15 million customers, their date of birth and social security number, as well as driver's license numbers and additional information was illegally accessed, meaning the potential for identity theft here is huge.

Hi , Today i will show you how to do HID Keyboard Attacks With Android BUT without using Kali NetHunter BUT You will need to install custom kernel to your Android device, that will add keyboard+mouse functions to it's USB port,So Lets Get Started

If you're just starting out with Android—or smartphones in general, for that matter—there are a lot of little things to learn. One of the first terms you'll likely encounter is "Wi-Fi," which is a wireless internet connection served up by a router in your home, office, or local coffee shop. This differs from your smartphone's regular "Mobile Data" connection, which is provided by your cellular carrier and included as part of your monthly bill.

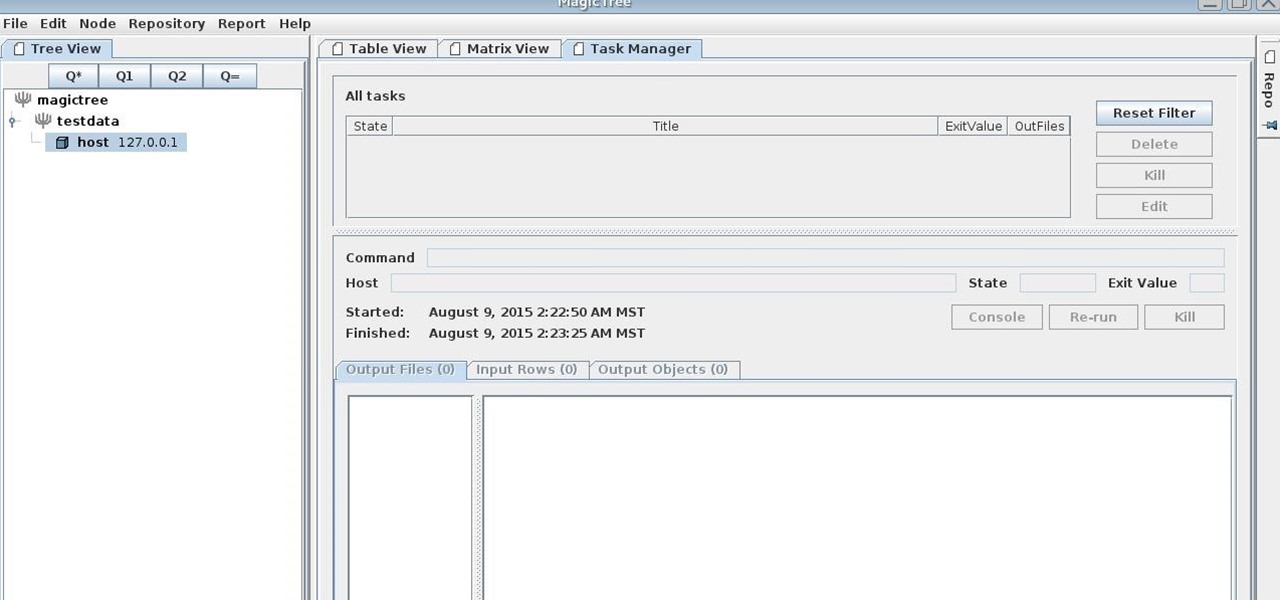
MagicTree is often the go-to tool for data collection and reporting for many pentesters. It organizes data in nodes in a tree-structure which is very efficient at managing host and network data. Reports can be completely customized to meet the user's needs. Also, MagicTree allows you to import XML data and has XSLT transforms for Nessus, Nmap, OpenVas, Burp, Nikto. MagicTree comes pre-installed in Kali.

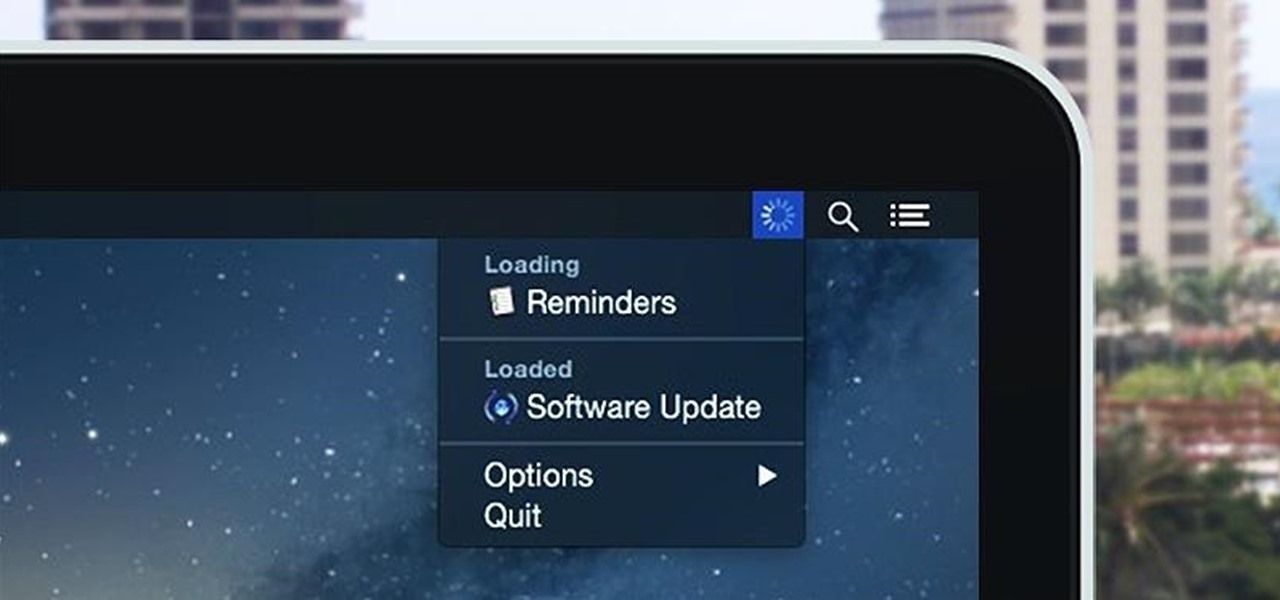
Monitoring your Mac with widgets can be the first step in identifying bandwidth issues, but finding the root of the problem can be a completely different story. Usually you will have to open up Activity Monitor in Mac OS X to look for apps hogging your bandwidth, but with Loading, you can get a detailed data usage report right from your menu bar.

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

Animal lovers, especially dog owners, know that pets are a part of the family, but it's often incredibly frustrating to know if and when something just isn't right with our furry companions. If you're out and about most of the day, your dog will be so happy to see you when you come home that you may have no idea they were tired and listless all day long, which can be a sign of health problems for your pup. This is where FitBark comes in.

While I do enjoy the vanilla Android Lollipop experience that comes with the Google Play Edition HTC One, I do miss the sweet camera that ships with Sense. Luckily, the people behind Liberty ROMs found a way to port that camera over and now we can enjoy the best of both worlds... well, sort of.

Before you head to class, work, or sleep, you're probably doing the same thing over and over again—toggling off system settings like Wi-Fi, sound, data, or brightness, depending on the circumstances. Schedules and routines can help increase efficiency, so while you abide to a particular schedule, so should your Android.

With an Android device left at its default settings, your location history is automatically recorded. You can view and manage this data, but the simple interface of points plotted on a map leaves a lot to be desired.

Your Galaxy S5 is jammed to the brim with all sorts of electronic sensors. These are capable of reading humidity levels, ambient temperature, air pressure, and much more. Yet, while this data is constantly being collected by your phone, there aren't any built-in apps that are capable of displaying much of it.

We've already shown you how to free up internal space on your iPhone, and now it's time to tackle another problematic storage issue—your iCloud account.

It used to be easy to hack tethering—root your device and install a third-party or modded tethering app. But snuck in amongst the changes in Android 4.3, a new data-monitoring service of sorts made its debut. There used to be a time when your data connection was yours. You paid for it, so you were free to use it for whatever you wanted. Unfortunately, those days are long gone.

"Millions of us have smartphones with the power to speed up research that will benefit billions of people around the world." - Professor Francois Grey

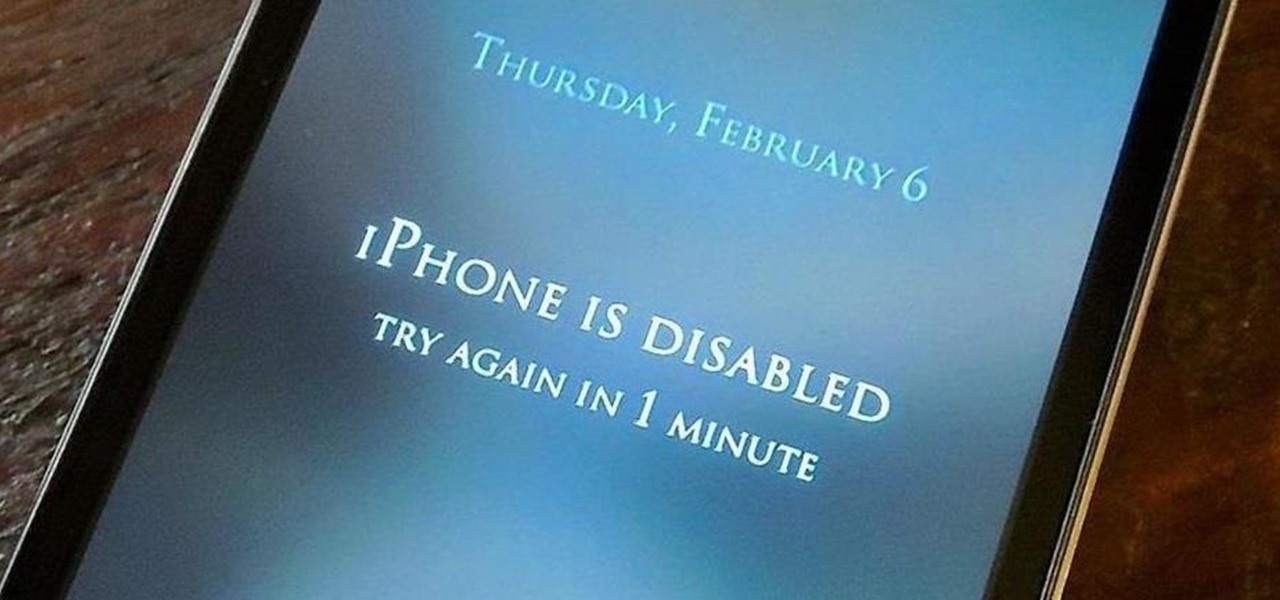
The lockout feature in iOS 7, which securely locks your device after a few incorrect passcode entries, can be a real pain in the ass sometimes.

Starbucks' app is the most used mobile payment app in the U.S. because it's well-designed and convenient. But if you use the iOS version on your iPhone, your username, email address, password and location data could be compromised because the app stores them in plain text.

One of the biggest problems in data security is authentication of data and its source. How can Alice be certain that the executable in her inbox is from the venerable Bob, and not from the not-so-venerable Oscar? Clearly Alice wants to know because if this file is actually sent to her by Oscar, the file might not be a game, but a trojan that can do anything on her computer such as sift through her email and passwords, upload her honeymoon pictures, or even turn on microphones and webcams. Thi...

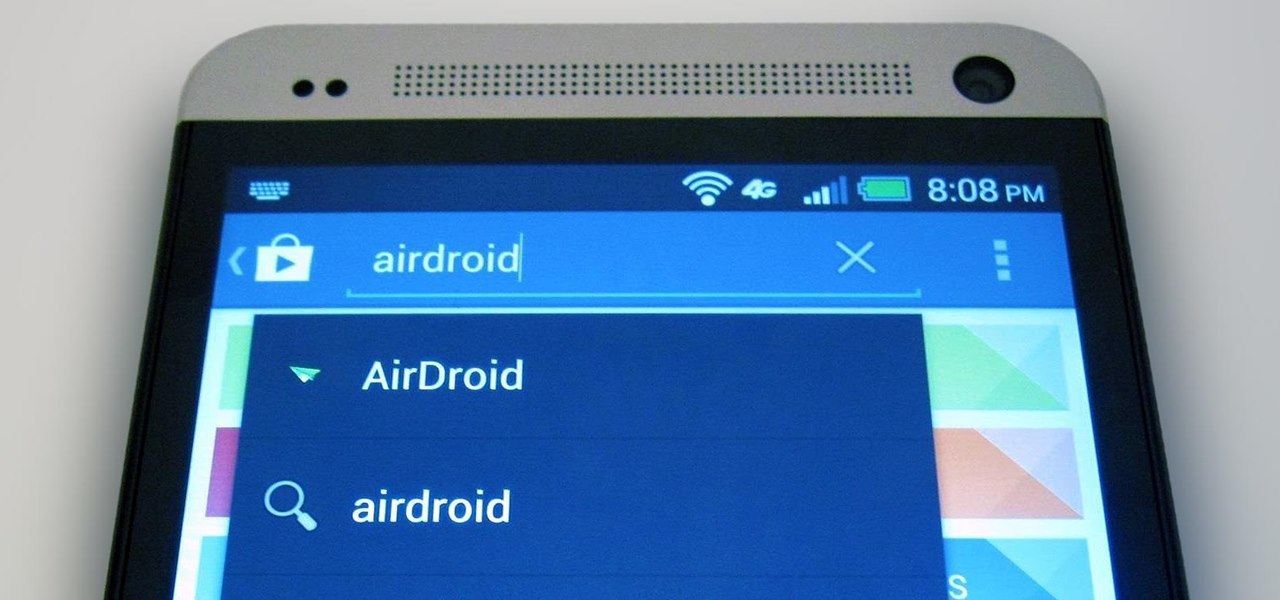
The first thing I do when I get a new phone is ditch the USB cable. At least, when it comes to data transfer. My brand new HTC One came with a USB cord that feels sturdy, but like any other cable, it will eventually fall apart from overuse. It will probably still charge just fine, but at that point it will be unreliable for transferring data. Lucky for me, there's a solution. Transfer files over the air. This will let you save that USB cord only for charging and the occasional situation when ...

Advancements to Android's open source OS come in the form of ROMs and mods, available all over the web for anyone to find. Installing any of these modifications tends to wipe your phone clean, causing you to lose all of the precious data on your device.

As if you needed another reason to lock down your Facebook profile, the company's sketchy new partnership with data mining firm Datalogix is geared towards giving advertisers more information on what you're doing—even when you're not online. It's just not enough that they can target ads based on your preferences, now they want to know how those ads are influencing your buying habits in the real world.

If you bought the new iPhone 5 or upgraded your old one to iOS 6, you may be having issues when you try to upload photos to Facebook. After updating, the first time you try to share an image from the Facebook app, it will ask you to allow access to your Camera Roll.

Security researcher Nadim Kobeissi has discovered that the Windows 8 SmartScreen feature, meant to screen downloads for malicious software, actually reports the data about which applications users are installing to Microsoft. He also says that "the Microsoft server is configured to support SSLv2 which is known to be insecure and susceptible to interception." The two main concerns are the ability of law enforcement to subpoena Microsoft for the information and of hackers to intercept user data...

Alopecia is also known as hair loss. he most common form of alopecia or hair loss that we see is alopecia areata. It usually shows itself as round patches of hair loss on the scalp, however, it can affect the facial hair and body hair. Learn some tips on how to slow and treat the loss of hair in this medical how-to video.

This is a special four-part series on the human head, neck and skull. Medical students can greatly benefit from watch this anatomy video series. Dr. Gita Sinha "dissects" all of the information pertaining to the head and neck. Dr. Sinha is Assistant Professor for the Department of Anatomy & Neurobiology at Dalhouse University. Each of these videos cover a different topic:

This video will teach doctor and medical students how to perform a full abdomen examination. John D. Gazewood, MD, MSPH, will show you the whole process, from the first steps of inspecting the abdomen, looking for abdominal contour and symmetry, to auscultation, percussion, and palpation of the abdomen. Some common findings during the inspection phase of the exam could be scars, striae, colors, jaundice, and prominent veins.

Not every nurse can get an IV every time, that's why it's important to stay in practice for the proper technique used for inserting a peripheral IV. This is a common medical procedure that all fields related to medicine should know. Even the soldiers in the military are taught how to insert an IV — every soldiers, not just the medics.

In many situations, learning proper medical procedures is difficult due to the urgency involved in patient care, so this video aims to prepare nurses so they can learn and stay fluent with the proper urinary catheterization of a female patient.

Dr. Bob Sears explains to parents the difference between a child's fever that may be serious and one that isn't. Only when the child's fever is high and any efforts to bring it down have failed, should you seek medical attention. This means the child could have a serious infection. A temperature of 103 or more is considered high, 101-102 is medium, and 99-100 is typical. Dr. Sears recommends using a regular digital underarm thermometer to check the child's temperature. Hold the thermometer un...

Go for a bug theme this Halloween! This Halloween makeup tutorial demonstrates how to apply a fun bumblebee costume makeup look. Be a queen be this Halloween. Enjoy!

Have you always thought of Excel's grid system as kind of limited? Too small for what you need? Well, now in Excel 2008 for Mac, its grid might be too big for its own good! It's huge with plenty of room for all your data. The Microsoft Office for Mac team shows you just how to explore the bigger grid in this how-to video.

Great news! — Excel isn't just for Windows anymore. Okay, so it's been available on the Mac for awhile now, but if you haven't used it yet, why not start now? Getting started with Excel 2008 for Mac is easy, and this video overview will show beginners or even the most seasoned professional spreadsheet worker a thing or two. The Microsoft Office for Mac team shows you just how to get started in this how-to video.

Excel 2008 for Mac makes it easy to create formulas for cells. You could always do it before, but now with the new Formula Builder feature, building formulas just got one step closer to simple. The Microsoft Office for Mac team shows you just how to build formulas by using the new Formula Builder in this how-to video.

To test how fast your internet speed is an intermediate level skill. Start by picking an internet speed test. You can use Google or another search engine to find one. A service that is recommended in the video is DSLreports. This site does not require you to know a lot of information about your service. To test your speed start by picking a city that is near to you. Then shut down all tabs and every application that you have running. It's important to do this on every computer on your home ne...

This video shows you how to fix a Windows "Blue Screen of Death". You should know what to look for when you get the BSOD. You should look for the error code first and then the stock code. You should hit the F8 button upon start up to go to the last known good configuration and it will boot your computer to the last time it booted correctly. You can also start in safe mode. You will need to do a system restore. If that doesn't work do a Google search for the file name that is causing the probl...

In this video, you will be walked through the game Foreign Creature. There are human characters in this one, with word clouds, in an office setting with bulletin board, desks, rolling shelves, and tack boards. In another scene of the game, you will see a hospital setting with nurses, surgery table, patient, medical equipment, and doctors. In this setting, the patient is a foreign creature who blacks out the medical staff and proceeds to stalk the hospital. Police try to capture the humanoid-l...