Snapchat popularized personalized stickers for social media and messaging with Bitmoji, followed by walled-garden versions from Apple with Memojis and Samsung with AR Emojis. Even Google has gotten into the game, integrating an emoji generator for Gboard.

Users are often the weakest link when probing for vulnerabilities, and it's no surprise they can be easily fooled. One way to do this is called clickjacking. This type of attack tricks the victim into clicking something they didn't mean to click, something under the attacker's control. Burp Suite contains a useful tool called Clickbandit to generate a clickjacking attack automatically.

Beginners learning brute-forcing attacks against WPA handshakes are often let down by the limitations of default wordlists like RockYou based on stolen passwords. The science of brute-forcing goes beyond using these default lists, allowing us to be more efficient by making customized wordlists. Using the Mentalist, we can generate millions of likely passwords based on details about the target.

While ARKit and ARCore are poised to bring AR experiences to millions of mobile devices, one company is poised to anchor those experiences anywhere in the world with just a set of geographic coordinates.

In my previous article, we learned how to generate a vulnerable virtual machine using SecGen to safely and legally practice hacking. In this tutorial, we will put it all together, and learn how to actually hack our practice VM. This will provide some insight into the methodology behind an actual attack and demonstrate the proper way to practice on a VM.

Once we recover from the respiratory infection pneumonia, our lungs are better equipped to deal with the next infection — thanks to some special cells that take up residence there.

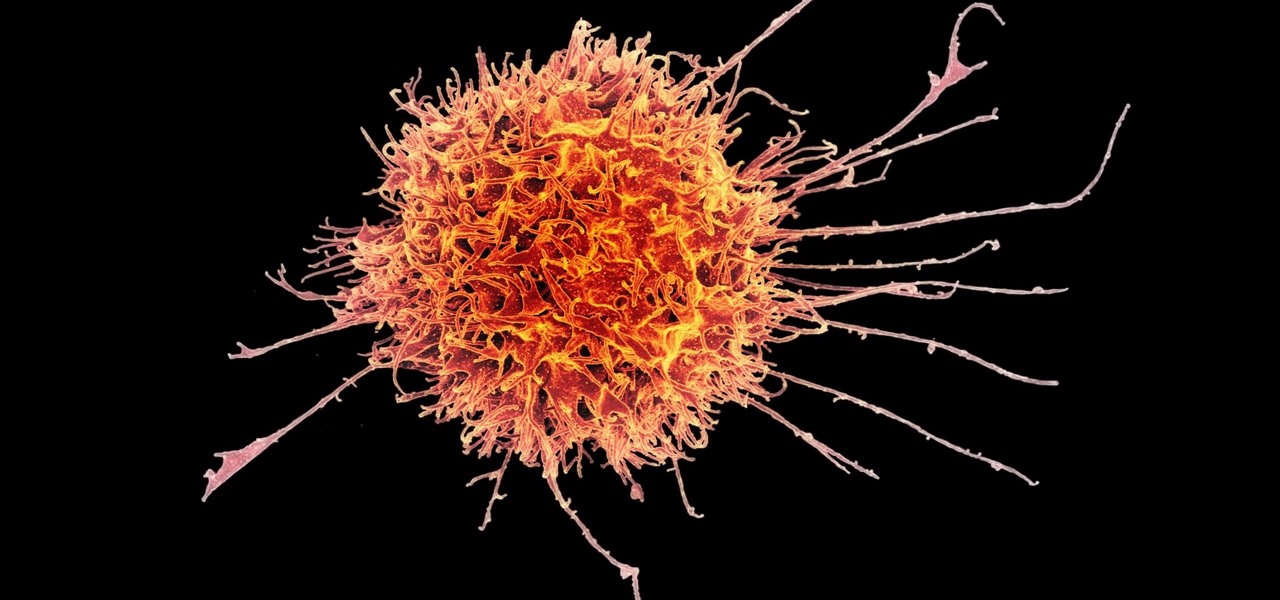
Cancer cells do a pretty good job of flying under the radar of our immune system. They don't raise the alarm bells signaling they are a foreign invader the way viruses do. That might be something scientists can change, though.

Flu vaccines can help prevent us from getting or suffering the most severe effects of the flu. But, each vaccine only protects us from three different strains of the flu. If we don't have a vaccine against all types of flu, it leaves us open for an epidemic with a flu virus we didn't expect.

Now that we've learned about keeping all our data safe with encryption, it's time to continue progressing through getting your Mac set up for hacking.

Hello people again, I wrote my last post about crypto about 10 months ago, now I will introduce something not fresh for the science, but fresh for the people who wants to learn. In my http://null-byte.wonderhowto.com/forum/cryptography-0161538/ post of crypto concepts, there is just basics, today we will see something that targets wide concepts like Symmetric crypto, Public Key Cryptography, Hashing, Keys etc...

Welcome back, my neophyte hackers! Digital forensics is one of the fields often overlooked by aspiring hackers. In a rush to exploit every and any system they can, they often ignore learning digital forensics—the field that may lead to them being traced.

Hello all, this is my first submission to null byte! I noticed something a little strange, particularly that whenever Meterpreter is discussed, it is virtually always in the context of Windows. Granted, the Windows Meterpreter is more powerful than the version that can run on OS X (it has several more commands/options), but I think it is still worth noting how to do it. I've even seen some people mistakenly say that Meterpreter can only be run on Windows, which is not true. Meterpreter can ea...

So, we all probably know that when you run a trojan made by Metasploit, nothing will appear to happen. This is a sign for me to immediately check my Task Manager, but for an unsuspecting victim, it will just seem like a broken file. It is likely that they will delete this "broken file" once they see that it "doesn't work." In order to prevent this, we need to disguise the trojan.

Welcome back, my greenhorn hackers! After the disaster that was Windows Vista and the limited and reluctant adoption of Windows 8 and 8.1, Windows 7 has become the de facto standard operating system on the desktop/client.

Welcome back, my hackers novitiates! As you read my various hacking tutorials, you're probably asking yourself, "What are the chances that this hack will be detected and that I'll land behind bars, disappointing my dear mother who already thinks I'm a loser?"

Want to generate experience and level up your Pet Society character the easy way? Watch this cheater's guide, which will show you how to hack Pet Society for all the EXP you could ever want.

Smash glow? What the heck is that? That's exactly what you'll find out… watch this science video tutorial from Nurd Rage on how to make smash-glow crystals (triboluminescent crystals) with Dr. Lithium.

Long-time packeteer Bob Bruninga, WB4APR, developed the Automatic Packet Reporting System (APRS), which allows packet radio to track real-time events. It deviates markedly from the usual message- and text-transfer activity. Instead, APRS concentrates on the graphic display of station and object locations and movements.

Systm is the Do It Yourself show designed for the common geek who wants to quickly and easily learn how to dive into the latest and hottest tech projects. We will help you avoid pitfalls and get your project up and running fast. Search Systm on WonderHowTo for more DIY episodes from this Revision3 show.

Read This Must Need flash player 9!!

Watch this science video tutorial from Nurd Rage on how to make a lithium thionyl chloride battery, which is capable of generating 2.8v with enough current to power a LED.

Watch this science video tutorial from Nurd Rage on how to make a chemiluminescent reaction with home chemicals. Make a chemiluminescent singlet oxygen red light pulse from two simple chemicals almost anyone can buy: pool chlorine and hydrogen peroxide.

Watch this science video tutorial from Nurd Rage on how to make silver nitrate from silver and nitric acid. They show the chemistry of making this cool chemistry, colorless solid.

Watch this science video tutorial from Nurd Rage on how to make a mirror silvering solution from silver nitrate, ammonia, sugar, and sodium hydroxide.

This video tutorial shows how fifteen dollars and a half an hour of assembly can produce a working bare-bones laminar flow nozzle that attaches to a garden hose for a makeshift fountain.

In the following series of videos we will establish a particle stream that is then used to create a surface that evolves over time in Houdini 9 software.

Win you opponent at squash. This how to video is a quick squash playing tutorial that goes over some of he basics of the sport. Learn about proper racquet grip, writs tension, and how to generate power in each stroke.

Check out this video tutorial on how to generate an Excel worksheet using XML. There's a free library from CarlosAG.net, and you need to get the free dll file from there. This video will show you how to use it. You need to use CreateExcelFile in Microsoft Visual Studio to use the XML. You will need to use Microsoft Excel 2003 or 2007 to open this file.

Minions are computer generated NPCs that spawn from the base nexus and attack enemies. You can't control your minions, but you can influence them by using smite and heal on them. Use your minions well and you'll win your games on the Fields of Justice!

Mike Callahan from Butterscotch describes how to manage the passwords on your iPhone by using the 1Password app. The application costs $5.99 for the Pro version. First, you enter an Unlock Code to give you access to the app. The icons across the bottom of the screen correspond to different features of the app. The Logins icon stores your login information. The Wallet icon stores information about your credit and bank cards. The Passwords icon holds all your passwords. The Add icon allows you ...

This Houdini 9 software video series focuses on examples of when and how to use Attribute Transfer. Part 1 covers Attribute Transfer One Point:

Selling stuff at the local flea market sounds easy enough, but it isn't anything like having a yard sale. There's a lot more to it that just getting rid of your junk, and the biggest things are being licensed and having a sales tax number. Flea market vendor may not be your first career choice but, like many, you may find it’s a lucrative full-time job or a profitable and fun sideline.

Cue ball draw refers to the way a cue ball strikes a rack of balls. In particular, if the cue ball is hit low on the ball, when it strikes a rack of balls, for the break, it will have enough backspin to wind its way back to the shooter.

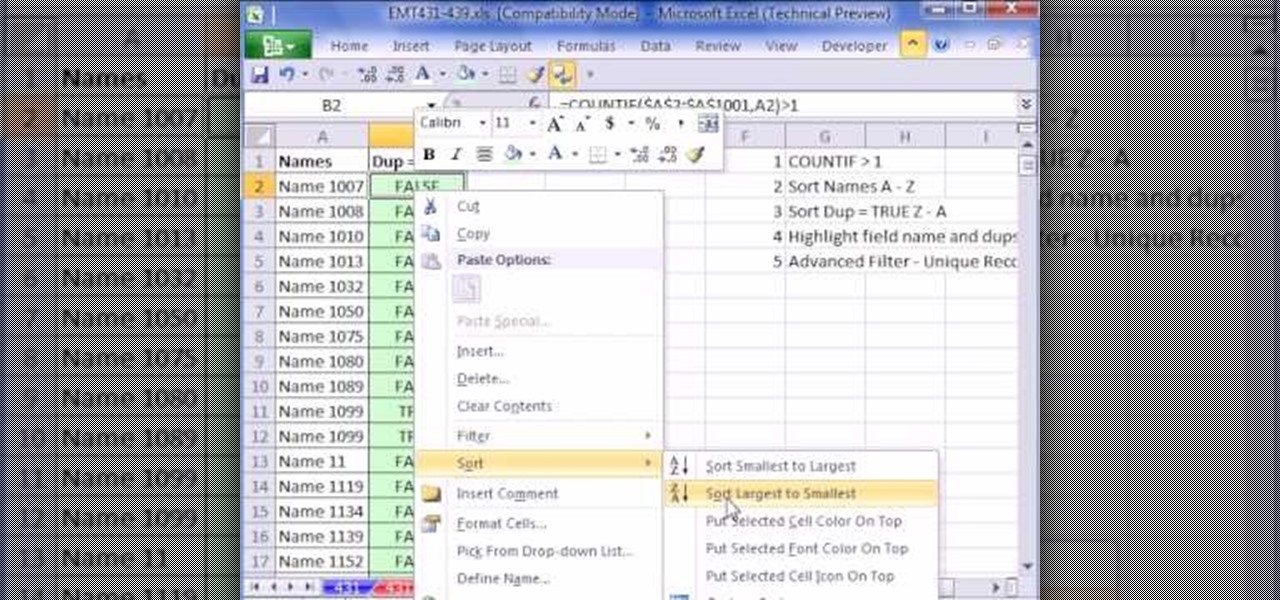
This video is about finding duplicate entries in excel sheet. The example excel sheet contains different names. There are around 1000 different names in the sample excel sheet. CountIf(range,criteria) formula has been used to do the comparison and return of results in True or False mode. Type =CountIf( now move your left arrow key, this will generate the formula like =CountIf(A2. Now press Ctrl+Shift+Down arrow, this will select all the available values in the column. Now press F4 to lock it ...

Watch this video to learn how to make a basic honey and sesame seed chicken. This delicious dish will be generating raves around the dinner table. Ingredients: A plate of sesame seeds Dark soy sauce Blossom honey Vegetable oil five pieces of skinless chicken Fresh coriander for garnish Put a frying pan onto the stove top on high. Mix in a bowl stirs equal amounts of dark soy sauce, honey and vegetable oil to make a sticky marinade. The vegetable oil stops the honey from burning. Add in chicke...

In this video the instructor shows how to upload High Definition HD videos using Camtasia Studio. Here the instructor shows how to upload the videos that you recorded using Camtasia in HD to YouTube. Now to generate a HD video you will need to record in high resolution like 1280 by 800 pixels. Now record the video at full screen. Now after recording you will have your HD video. Open the video in Camtasia and add the clip to the time line by right clicking it and selecting the option from it. ...

They say you have to be in the right place at the right time... how about an elevator? If you happen to run into your ideal employer or business partner, in an elevator – or anywhere else for that matter – you'll have about 30 seconds or less to wow them. Here's how to do it.

Attention aspiring screenwriters! In this tutorial, learn how to sell that script. You may have written the next Hollywood blockbuster – but unless you can finance the film yourself, you’ll need to sell the screenplay to a producer who can make it come to life.

You can stop being lazy by using these tips to motivate yourself to find an interest in life. You Will Need

How to hack Pet Society! Pet Society cheats, tricks, hacks. Watch this video tutorial to learn how to hack gold in Pet Society (09/29/09).