
How To: Make Peppa Pig from Play-Doh
Want to learn how to make Peppa Pig with Play-Doh? Here is our attempt on showcasing a tutorial on how to make Peppa Pig with Play-Doh.


Want to learn how to make Peppa Pig with Play-Doh? Here is our attempt on showcasing a tutorial on how to make Peppa Pig with Play-Doh.

Welcome back, my aspiring hackers! In previous tutorials, I have shown you how to scan the globe for vulnerable servers and write simple scripts in BASH and Perl to perform other reconnaissance tasks. In a very recent guide, I taught how to scan vulnerable servers for Heartbleed.

Whether it's bad timing, or some trying-to-be-funny photobomber, it sucks having a photo ruined by someone or something getting in the way. While you can always retake the photo, it's simply impossible to capture the moment you intended, no matter how much restaging you do. But with an HTC One, there's no need to retake anything, as we have access to built-in features that will remove those photo intruders.
Transparent status bars and new lock screens weren't the only new additions that came with the Galaxy S3 KitKat update. Along with better battery life and a smoother user experience, we got a new toggles design and recent apps menu. Of course, Samsung's infinite wisdom left these two aesthetic features hidden away. Luckily, with root, you can easily enable them with just a few quick edits.

Let's say you're watching a video and everything's going great, but you feel the need to raise the volume a tiny bit. You hit the volume button on your Nexus 5, and all of a sudden, a giant volume slider appears that obscures half of your video for 3 seconds.

Figuring out someone's password, pattern, or PIN isn't very difficult—simply watching over their shoulder or following the oil marks left across their screen is enough to figure them out and bypass whatever lock screen security they have.

If you lend someone your phone, even if it's just for a second, there's a chance they can enter an app and see something you'd rather they didn't. Whether it's a personal email or a private photo, there are plenty of reasons why you'd want to keep snoops out of certain apps.
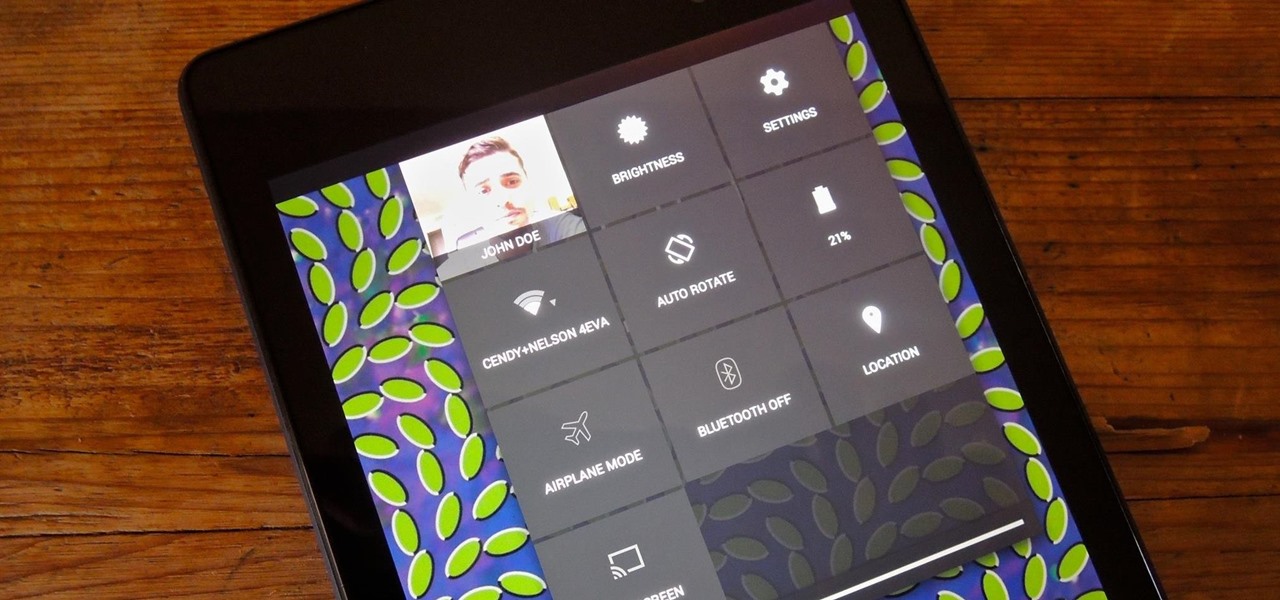
Accessing notifications and quick settings from the lock screen just makes things move quicker and more efficiently, unless of course we're using a secure lock screen. It makes sense that if we have face, pattern, or pin security enabled, we may not want notifications accessible, but really, that should be something we decide for ourselves—and now we can.

Notifications, while certainly helpful, can at times be overbearing. There are banners plastered every which way on your smartphone for almost every application. While many of the notifications can simply be swept away or turned off, the same can't be said of persistent notifications.
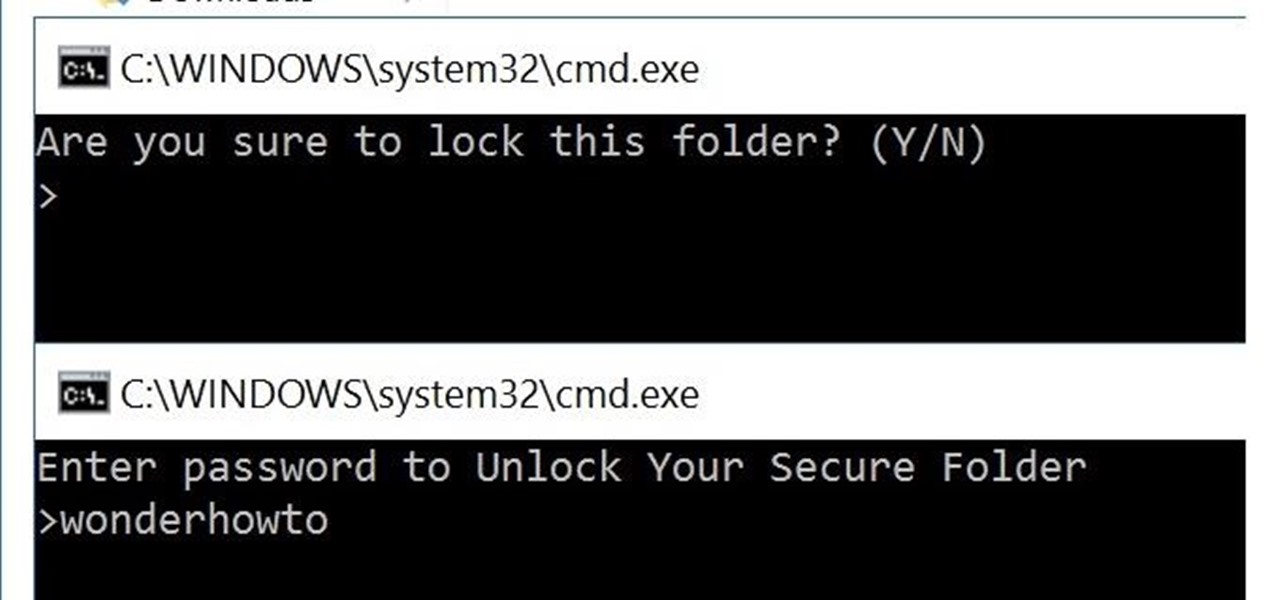
You can easily lock any folder on your Windows computer with a simple Notepad hack. By creating a batch file, you can hide a folder and require a password be entered before it becomes visible and accessible. This is a great tool for locking sensitive information, like pictures, financial statements, and a lot more.

Welcome back, my greenhorn hackers! Recently, I asked the Null Byte community what subject they would most like me to cover in future tutorials. Many of you cited scripting, and I decided it's best to cover this subject soon, so here goes.

A great aspect of using Android is having the ability to change and tweak aspects of the user experience to your liking. You can easily change things like home screens, widgets, and icons on your Nexus 7 tablet, but also core system settings if you want, like volume settings. Most stock systems come standard with a "15 step" volume control. That means simply that you have 15 levels from mute to the loudest volume settings. Whether your an audiophile or just someone who wants a little more con...
What is your Samsung Galaxy Note 2 running? More than likely, you're still rocking Jelly Bean 4.1.2, which is already pretty outdated. My grandma uses 4.1.2.

Welcome back, my tenderfoot hackers! This is the third installment of my series on basic Linux skills that every hacker should know. Although some hacking tools are available for Windows and Mac, every real hacker uses Linux—for good reason.
There may only be a few hardware buttons on your Samsung Galaxy Note 2, but when they're not working, your phone might as well be a doorstop. A few years back, I was texting while walking to class and a student on a bicycle crashed into me. My phone was flung thirty feet—straight into a puddle. I picked it up and checked for damage, but everything seemed okay. The biker apologized profusely, but nothing was wrong, so I told him not to worry about it and proceeded to class.

Welcome back, my newbie hackers! We've already saved the world from nuclear annihilation and covered our tracks afterwards, but the world is still threatened by a malicious, megalomaniacal dictator with missiles and nuclear weapons.
You know that moment when you finally figure out something, but you figured it out years after you really needed it? Don't you freaking hate that?!
We've all had to write an essay or research paper at some point, and undoubtedly the hardest part about it is always the citation, right? If you ask me, it's a huge pain in the arse. Even more so if you're gathering your facts from a huge variety of sources.

Whether you're at work or in class, there are times when using your phone is unacceptable, regardless of that subtle yet sudden twitch in your arm that arises every time you hear the vibration of a text message.

Welcome back, my tenderfoot hackers! So many of you responded positively to my post about using the keylogger, as well as my post regarding turning on the webcam, that I decided that you might enjoy another similar hack. In this article, we will enable the audio recording capability on the remote system of your roommate.

Being politically correct on social media sites is super boring. I've had my fair share of rage tweets and angry Facebook posts with some colorful wording, but sometimes using and F-bomb just gets the point across better. Now that Facebook is pushing out their new Graph Search, it might be time to clean up your profile. FaceWash is a web app that searches your Facebook profile for common bad words. You will need to give the app permission to access all of your wall posts (or course). Once acc...

At first glance, the iOS home screen looks nearly identical to the original release back in 2007. Though those experienced with the evolving iterations of iOS will tell you that the features have changed. Furthermore, with the App Store continuing to explode with (lets face it) better options than the stock software, these included applications are only causing clutter across the springboard.

With presidential voting going down on Tuesday, November 6th, voters are beginning to anchor down on their choice for president. But with the way the media works, this may be difficult for some people because the news sites they listen to give conflicting and sporadic information on the candidates.

Did you buy your new iPhone 5 without a contract? We'll, if you bought it from Apple, AT&T or Verizon, you can have it unlocked pretty easily. Why Have It Unlocked?

Taking screen captures is a standard feature on iPhones and newer Android smartphones, but for some reason it's not very intuitive. Screenshots allow you to share your phone's screen with your friends, document technical problems for customer support, and even make how-to guides easier to follow. So, it's definitely worth remembering. Here's how you do it.

At the recent DefCon conference in Las Vegas, researchers opened many of the top commercially available gun safes with simple tools like a straw or a paper clip, and in one case, just by shaking it a bit. The investigation began after the researchers, Toby Bluzmanis, Marc Tobias and Matt Fiddler, learned that certain Stack-On safes, issued to some law enforcement officials to secure their firearms at home, could be opened simply by jiggling the doorknob.
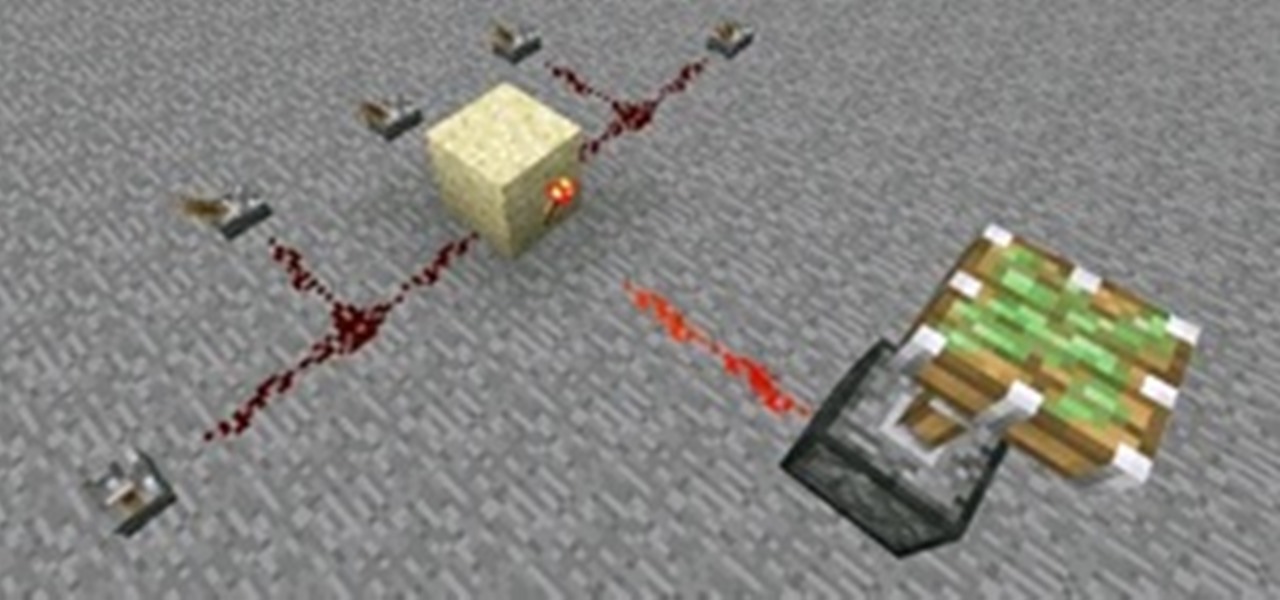
Control is important. Mankind inherently wants to control its environment, which is why we have things like indoor plumbing, electric lights, air conditioning, and more. Likewise, Minecraft has redstone, which is a way for users to control their environment and manipulate it to suit their needs.

Congradulations, you've reached the point in Dragon Age 2 where you can start your first sidequest! Simply look on Gamlen's desk for the 'Bait and Switch' letter to start it. Thisvideo series will give you a full walkthrough of this important early quest that may even net you a new companion...

Duplicating, or "duping" items has been around for as long as PC RPG's, and allows you to use glitches to duplicate your items in the game. This video will teach you how to use the stunningly easy-to-use dup glitch in Dragon Age 2 to duplicate as many of any item you have 2 or more of your want, up to 999. This essentially gives you unlimited money and items.

A lot of you are enjoying a nice winter snowfall right now. Some of you aren't enjoying the snow at all, especially if your car's stuck in it or you have to grab the snow shovel, yet again. But perhaps you'll change your distaste for snow when you try out some tasty homemade snow cream!

Don't spend all your hard-earned money on store-bought Christmas decorations this year. Spend it on cheap paper and make your own Christmas decorations, like this origami snowflake.
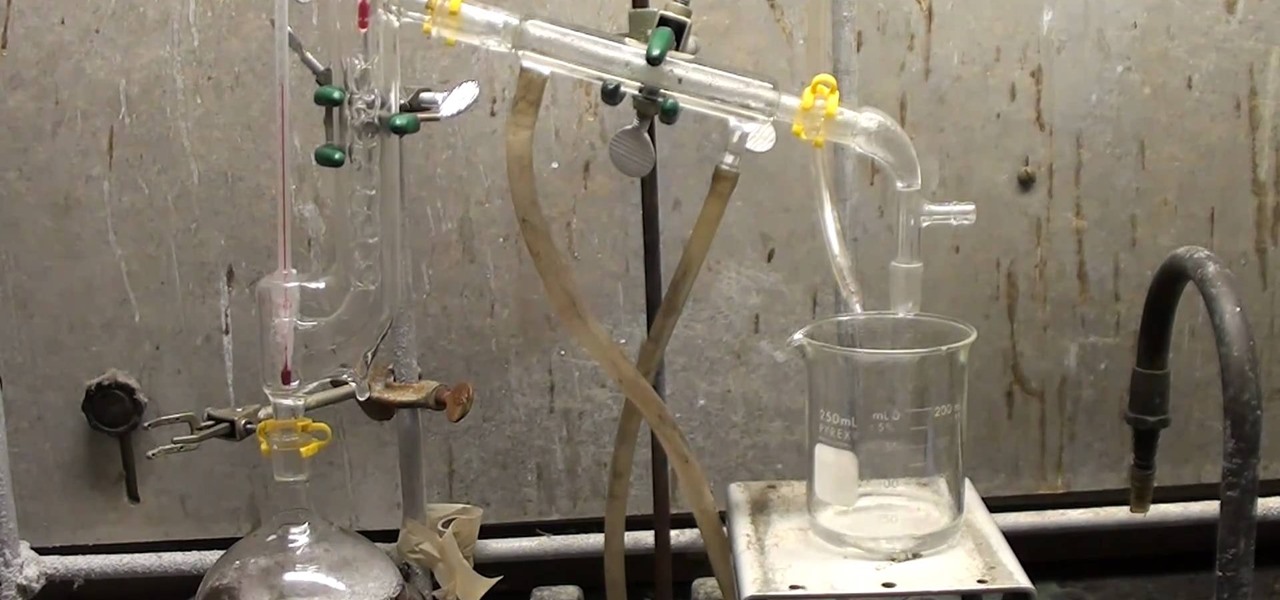
Hydrazine sulfate has many uses, but most notably, it's been used under the trade name of Sehydrin, a treatment for anorexia, cachexia and some even think cancer. But for we DIY chemists, it's useful for something entirely different— as a substitute for the more dangerous pure liquid hydrazine in chemical reactions. NurdRage shows you how to make it via some hypochlorite and the Ketazine process.
Are you addicted to Google Reader? If so, you may be looking for an even faster way to scroll through all of your favorite RSS feeds. Well, Matt Richardson has the solution…

There are several different kinds of disc drives that come in different iterations of the XBox 360, and each one has to be hacked a little differently. This video will show you how to flash the ms28 drive used in some systems, the second part of the video will show you how to determine what model of drive you have. It is very detailed, and should have you well on your way to hacking you beloved XBox 360 and maximizing its potential.

This video will show viewers how to simply make a 3 string guitar using an empty cigar box, a piece of oak, some string, and a few eyebolts. You start with a 1 by 2 piece of oak which is about 3 feet long. First, you should begin by making some markings along one side of the oak, first at 1/2 an inch and then at 1/4 inch spacing after that. Drawing 3 symmetrical lines where the strings should go, drill holes at the intersections of the lines you have drawn. The holes should be made using a 1/...

In this video, doctors can learn how to perform a full cardiac examination on a patient. The very first thing a doctor should do is visually inspect the patient, because there's a lot that can be gained by simply examining by eye. You'll want to carefully examine the respiratory pattern of the patient, the nature of their precordium, the anterior part of their chest over the heart. Feeling the pulse is also necessary when starting out this heart exam. To learn more, watch the full video.
If you want to learn how to Jerk or Reject dance first you have to skip backwards with your feet! Your first move will be to start off by jumping forward with your right foot and then come back with your right foot in the air. Next jump forward with your left leg and bend up your right leg. Then put your right leg down and your left leg up. Now repeat this same step over but with your other side. This is the simple easy jerk! Another way is to put your right leg up bent to the side and bring ...

This video demonstrates the installation of memory in a 13” Macbook Pro (mid 2009 model). It’s easy to perform and takes about 10min time. You’ll require a #00 Philips screwdriver (available in the Newer Technology 11- piece tool kit). Take care to work in an anti-static work space. Close the Macbook Pro and flip it over with the hinge side up. You can note 10 screws along the border. Start unscrewing the 3 screws on the right on the top edge, these are longer than the rest. Now unscrew the r...

This video from OWC presents how to install memory in a 17" Macbook Pro.The operation will take about 15 minutes and doesn't require an experienced user.First you need to provide all necessary anti-static precautions - discharge static electricity, use static-free surface.You'll need #00 Phillips screwdriver and nylon pry tool.You can find these in the Newer Technology 11-piece tool kit.To start, shut down the computer, close it and flip it over.You will need to remove 10 screws. Use #00 scre...

In this quick 2½-minute video Sean and Cathy are making spaghetti squash into a vegetarian dish with a hint of Italian. This a great video for you health cautions diners, it is also great for anyone on a budget looking to make a unique and simply delectable dish for you and your guest to enjoy.