The high limit thermostat can be found in gas and electric dryers and serves as a safety feature that helps to prevent the dryer from becoming too hot when it’s running. The thermostat is designed to shut off power to the dryer’s heater when the dryer vent is blocked or clogged. The high limit thermostat on your dryer is something that does need to be replaced from time to time. Fortunately, it is a job that you can do on your own with basic tools.

The shortest distance between two points is a straight line, but the shortest way to launch an app on an iPhone can be a much more complicated process.

For someone used to the old-style HTC Sense, upgrading to an HTC One with Sense 5 is a pretty intuitive experience, but there's one thing that some users find obtrusively different. Blinkfeed, an app which aggregates newsworthy articles from various sources and pins them in a scrolling feed on your home screen. If you don't like staying current on news, or don't like how much RAM it eats up, you probably want to get rid of it. There's been some questions about removing Blinkfeed in our forum,...
With CyanogenMod 10.2 recently released and the Samsung Galaxy S4 still waiting on Android 4.3, it only makes sense that the coveted features from both firmwares are highly desired by Android owners all over. We've already brought you a feature from each firmware—the cLock home/lock screen widget from CyanogenMod and the Google Play Edition Camera and Gallery from Android 4.3. Now we're bringing you another in the form of an updated text messaging application, ported from both Android 4.3 and...

Welcome, my hacker novitiates! As part of my series on hacking Wi-Fi, I want to demonstrate another excellent piece of hacking software for cracking WPA2-PSK passwords. In my last post, we cracked WPA2 using aircrack-ng. In this tutorial, we'll use a piece of software developed by wireless security researcher Joshua Wright called cowpatty (often stylized as coWPAtty). This app simplifies and speeds up the dictionary/hybrid attack against WPA2 passwords, so let's get to it!
Anyone who is familiar with Linux knows that to use your OS to the max, you will need to use the terminal every now and then. Whether it is to install a package or update the system or even delete a file.

Probably the most favorite custom ROM among softModders is CyanogenMod, a theme-friendly take on stock Android that not only makes it easier to customize your device, but also increases performance using a variety of system tweaks and enhancements.

The new Moto X may not have a lot going for it when it comes to hardware, but there are some pretty cool software features that makes it a tempting device. One of these cool features is its Active Display notifications that appear on the lock screen.

The NSA's massive internet spying efforts will continue. In President Obama's latest press conference, he went public to (in so many words) say that the NSA's spying efforts will continue uninterrupted. This, coming just weeks after the Amash Amendment which would have defunded the program, was narrowly defeated in the House (you can check if your congressmen voted against it here).

I'm constantly browsing the web, taking pictures, and playing games on my Samsung Galaxy Note 2, but there's one thing that I'm always doing—playing music. No matter what I'm doing on my smartphone, I'm always playing my music in the background at the same time.

I've already showed you how to magically unlock your Samsung Galaxy S3 with the simple wave of a hand, but why stop there? Sure, you could go out and purchase a Samsung Galaxy S4 so you have Air Gestures that let you control the lock screen, SMS, sound, wireless, and more.

Due to its enormously awesome size, the Samsung Galaxy Note 2 usually takes two hands to maneuver through photos and texts, write emails, and get directions on the map.

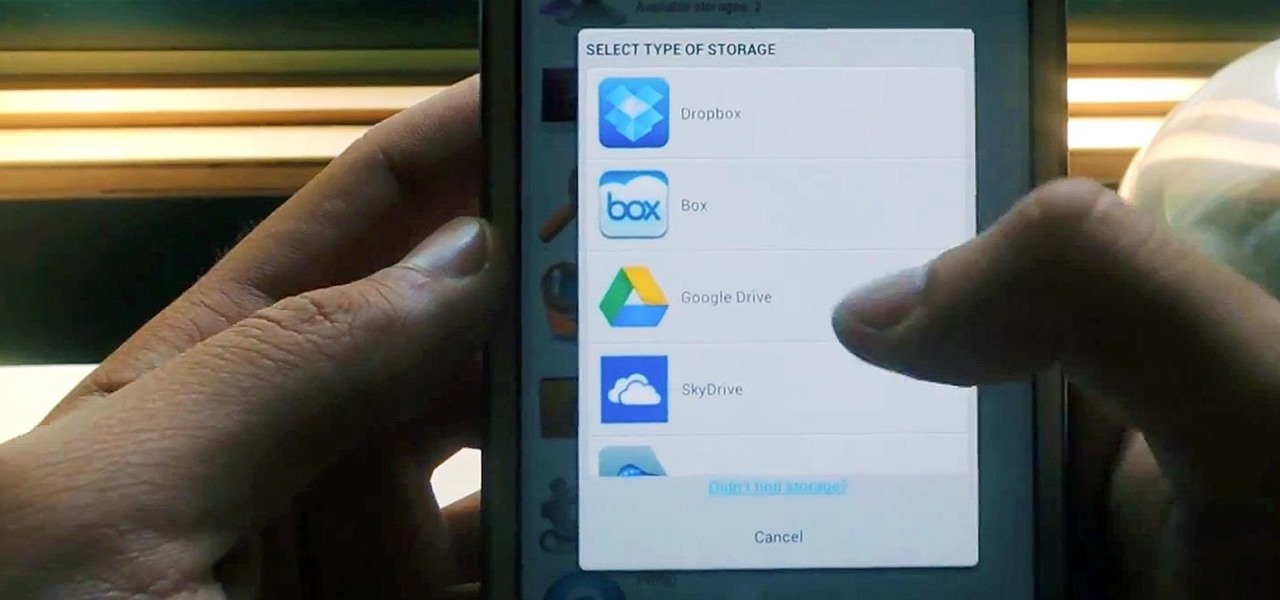
Cloud storage looks pretty good compared to the heavy restrictions that hard drives and other types of external memory carry. The cloud is not only limitless in what it can hold, but it can also easily be accessed from any device that has Internet—your smartphone, work computer, personal laptop, tablet, and more. While accessing a specific cloud storage system like Dropbox or Google Drive may be easy on your Samsung Galaxy Note 2, managing all of them individually can not only get confusing, ...

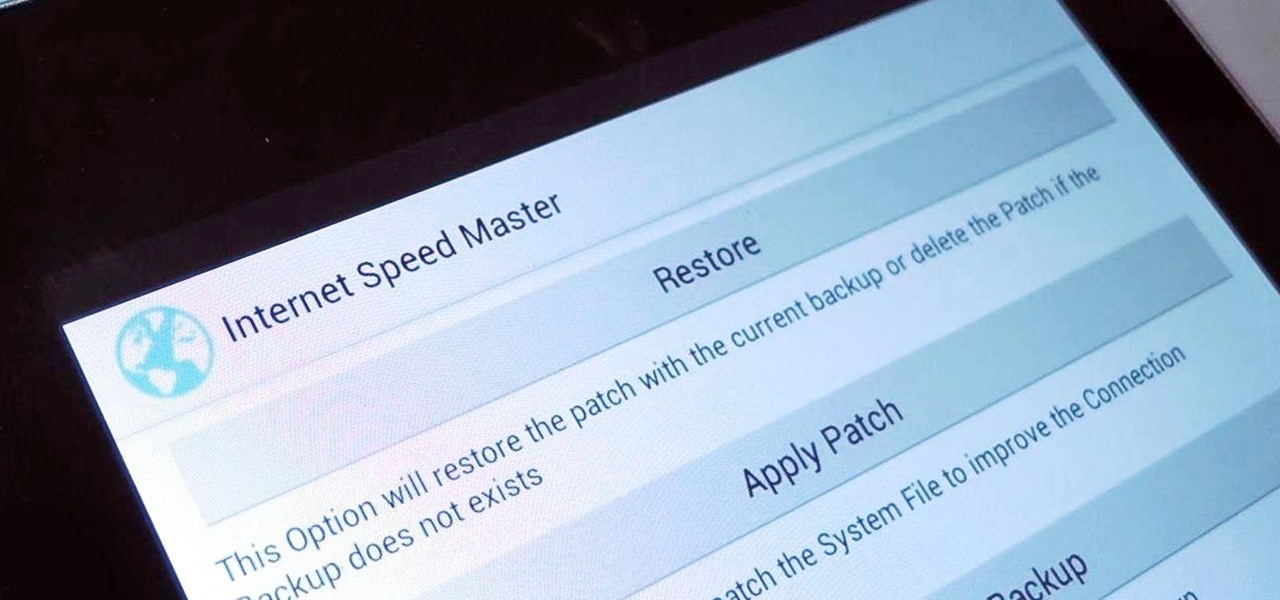
Even if you have the fastest internet connection in the world, it's not going to be fast if your Android device isn't optimized to use all of the bandwidth. I have pretty fast speeds at home, but every now and then my web surfing on my Nexus 7 tablet is halted in its tracks—for seemingly no reason.

Hey dolls! I have to share the secret of Copper peptides with you all. I don't know why it's taken me so long to jump on this band wagon because the science and studies behind the product are amazing!

Selfies are on there way out. Not because I said so, but just because I want them to. They're both aberrant and curious. They carefully hobble between the lines of self-exploration and crippling insecurities terribly masked as blatant narcissism.

Just like the HTC One Google Play Edition, the recently released Samsung Galaxy S4 Google Play Edition ditches the manufacturer's UI in favor of a pure Google experience, i.e. AOSP, but is also optimized specifically for the device's hardware.

How much privacy are you getting as an AT&T customer? With the recent leaks confirming the National Security Agency's surveillance on AT&T users, and the ongoing trial of Jewel v. NSA, it seems not much at all.

Thanks to its dedicated ImageChip, the HTC One has one of the best cameras out of all the smartphones currently on the market. Their branded UltraPixel Camera can take full resolution photos while shooting video, has superior auto-focusing, and provides great overall quality for everything from low-light to action shots.

Facebook knows who all of your closest friends and family are. When you backpacked across Europe last summer, they went along on the trip. Remember that break up two years ago? Yeah, they were there. The breakfast you ate this morning? They probably have a picture of it. They're even right under your own feet.

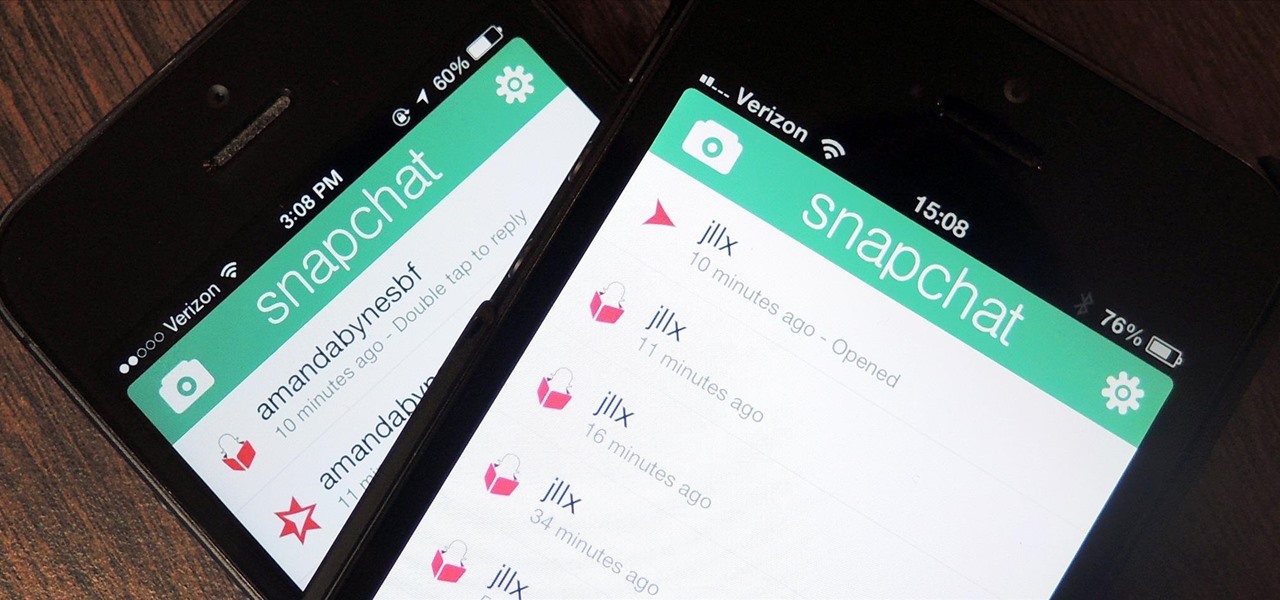
If you're a frequent Snapchatter like myself, you're probably well aware that Snapchat can't stop you or anyone else from taking a screenshot of a photo received. Instead, they notify the sender that a screenshot was taken—a greatly appreciated fair warning when impetuous photographs are involved. However, there is a loophole to this.

If you're constantly going from dark to brightly lit areas, you've probably noticed that the stock auto brightness feature on your Samsung Galaxy Note 2 doesn't work that well. Either the screen is really dim and unreadable, or it's just way too damn bright. Sure, you can disable auto brightness, but then you have to manually adjust the brightness all of the time for that perfect comfort level. This isn't really all that bad of an option, but don't be surprised when you see this: However, the...

Welcome back, my rookie hackers! Several of you have written me asking about where they can find the latest hacks, exploits, and vulnerabilities. In response, I offer you this first in a series of tutorials on finding hacks, exploits, and vulnerabilities. First up: Microsoft Security Bulletins.

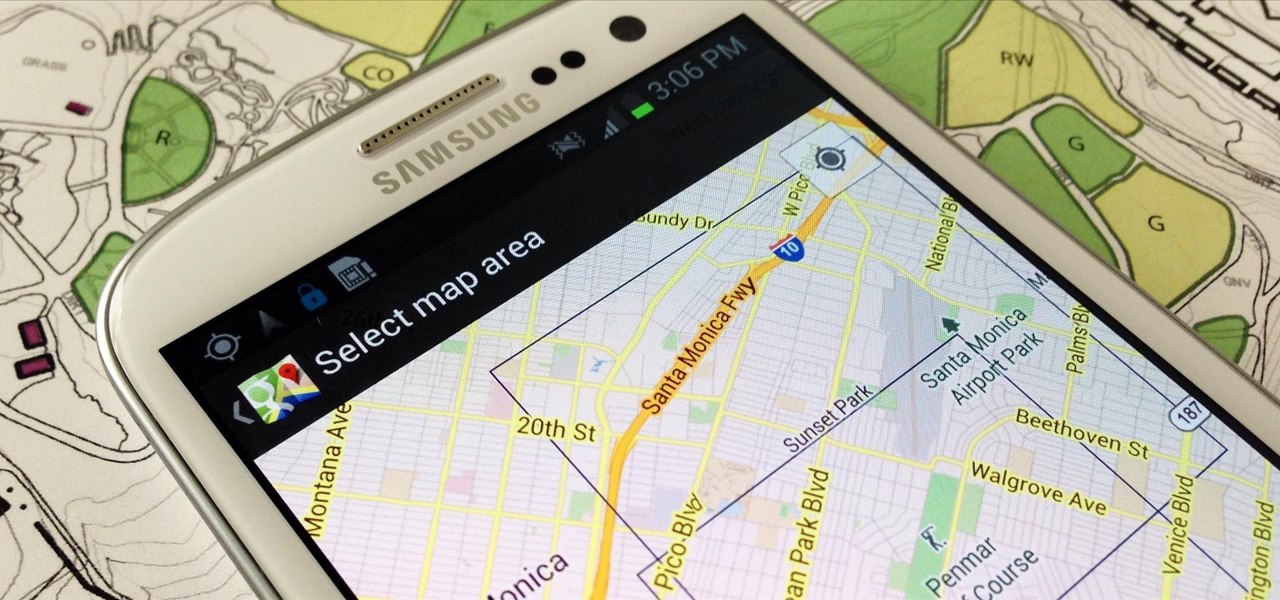
When you have to take four different freeways to go twelve miles, Google Maps becomes a very close and dear friend—especially in Los Angeles. Without my trusty Samsung Galaxy S3, I seriously don't know if I could make it back home half of the time. Of course, you'd probably get better directions using a Garmin, TomTom, or other GPS device, but when you already have a smartphone like the GS3, dedicated GPS units become nothing more than a luxury item.

In one of my previous articles, I showed off how to make water freeze into ice instantaneously. In this article, I'd like to elaborate on this, and show how a glass of water can turn to ice instantly on command. What exactly is this supernatural power? Discover the secrets to ice-bending—in real life.

I'm still amazed by all the things some people just don't know. Script-kiddies often refer to Metasploit if someone asks them how to hack a computer because they think there's simply no other way. Well here I am today trying to increase your set of tools and -of course- skills.

Welcome back, my hacker trainees! A number of you have written me regarding which operating system is best for hacking. I'll start by saying that nearly every professional and expert hacker uses Linux or Unix. Although some hacks can be done with Windows and Mac OS, nearly all of the hacking tools are developed specifically for Linux. There are some exceptions, though, including software like Cain and Abel, Havij, Zenmap, and Metasploit that are developed or ported for Windows.

When you upgrade to a new Android smartphone like the HTC One, you can have browser bookmarks, Wi-Fi passwords, and other settings quickly transferred over from your old device using your Google Account backup. However, you'll still have to download apps individually from your Google Play list, and not all of your saved progress will be transferred over. Fortunately, there is a third-party app that will allow you to backup and restore your apps—with all their data.

Video: . How To Use a Tampon

Welcome back, my nascent Hackers! In my last blog, we looked at a passive way to gather information necessary for a hack. The advantage of using passive recon is that it's totally undetectable, meaning that the target never knows you're scouting them and you leave no tracks. The disadvantage, of course, is that it's limited to only some websites and not entirely reliable.

Welcome back, my novice hackers! Most of my tutorials up until this point have addressed how to exploit a target assuming that we already know some basic information about their system. These include their IP address, operating system, open ports, services running, and so on.

The new Samsung Galaxy S4 just received an update to Android 4.2.2, so why is it that my Galaxy Note 2 is still running an older version of Jelly Bean? It felt like yesterday that my device was finally updated to 4.1.2, but why even bother since 4.2 has been around since last November?

"We all want to escape our circumstances, don't we?" Benedict Cumberbatch may have been talking about acting, but the sentiment rings true for all of us at some point or another. Whether it's work, school, or just boredom at home—we all wish for an escape sometimes. If only.

Welcome back, my neophyte hackers! Several of you have written me asking how to crack passwords. The answer, in part, depends upon whether you have physical access to the computer, what operating system you are running, and how strong the passwords are.

There is no such thing as a pulled pork slider. In fact, there is no such thing as a pork slider. Or a chicken slider. Or turkey or fish. The term "slider" actually means a lot more than just a hot miniature sandwich, and if it's not beef, it automatically missed the first cut. Sorry, but that is not a slider above.

Managing multiple applications on an iPhone is as simple as double-tapping the home button, long pressing the app you want to close, and tapping on the minus sign in the red circle. If you're using Mac OS X, the dock at the bottom of the home screen plays the role of the multitasking bar on the iPhone, just not as sleek or simple.

How to remove and replace a door handle / door knob. How to install a door knob. This is a job that can be done quickly and easily without any special tools (a cordless drill with a Phillips bit or a hand held Phillips Head screw driver). Follow the steps outlined below for a hassle free experience.

Wet shoes are uncomfortable, no one can deny that. Just think about walking around with soaking wet footwear ... and each squishy step you take. Makes you cringe, doesn't it? It can happen in heavy rain, at the beach, or from an unforeseen puddle on the street. And while you can't always avoid soggy shoes, you can rest easy knowing that the next time this happens to you, you know the secret trick to drying your shoes faster without damaging them with excessive heat.

Welcome back, my greenhorn hackers! Congratulations on your successful hack that saved the world from nuclear annihilation from our little, bellicose, Twinkie-eating dictator. The rest of world may not know what you did, but I do. Good job! Now that we hacked into the malevolent dictator's computer and temporarily disabled his nuclear launch capability, we have to think about covering our tracks so that he and his minions can't track our good works back to us.

We've all seen the blue screen of death at least one time in our lives. I grew up using a Windows PC about the size of a small refrigerator and that damn screen popped up at least once a day. Thankfully, errors like these happen much less often, but now that our smartphones have basically become pocket PCs, these type of errors can and do happen.