
How To: Use drag-&-drop XSLT style sheet design in StyleVision
Learn about drag & drop XSLT stylesheet design using Altova StyleVision, a visual style sheet design tool. Learn to publish XML and database data in HTML, PDF, and MS Word in this video.


Learn about drag & drop XSLT stylesheet design using Altova StyleVision, a visual style sheet design tool. Learn to publish XML and database data in HTML, PDF, and MS Word in this video.

See how simple it is to create data-driven web sites using ASP.NET 2.0, Visual Web Developer 2005 Express Edition, and SQL Server 2005 Express Edition. Watch this video tutorial to learn how to create a database, add its data, and display that data on a web page.

Basic installation of Drupal on a web server from start to finish with good explanations of Drupal's framework. Tutorial assumes viewer knows basic FTP and database configuration.

A quick overview of phpMyAdmin which shows how to view the database information etc from cPanel. This video is provided to you by Scandicsoft.

How to display the data in a MySQL database table in a web page using PHP.
This video demonstrates how to discover the dating history of people by searching on the website www.rateabull.com. The site searches their own dating database, as well as several other social networking sites.

Having an efficient workflow is an integral part of any craft, but it's especially important when it comes to probing apps for vulnerabilities. While Metasploit is considered the de facto standard when it comes to exploitation, it also contains modules for other activities, such as scanning. Case in point, WMAP, a web application scanner available for use from within the Metasploit framework.

Database technology has vastly improved the way we handle vast amounts of data, and almost every modern application utilizes it in one way or another. But the widespread use of databases naturally invites a slew of vulnerabilities and attacks to occur. SQL injection has been around for awhile, and as such, there are many defense methods in place to safeguard against these types of attacks.

Hello, my web huggers! In today's tutorial we will learn how to use the Google Hacking Database (GHDB) developed by Exploit Database, to find vulnerable web servers and "juicy" information.

Welcome back, my hacker novitiates! When we are trying to find vulnerabilities in a website to attack, we need a solid web server vulnerability scanner. Internet-facing web apps can open enormous opportunities for us as they are often riven with vulnerabilities and can often offer an entire point to the internal network and resources.

For SQL injection, the next step after performing reconnaissance and gathering information about a database is launching an attack. But something seems off .. in the real world, it's usually not quite as simple as passing in a few fragments of SQL code to an input field and seeing all that glorious data displayed right in the browser. This is when more advanced techniques are needed.

Metasploit is an extremely popular pentesting tool capable of enumeration, exploitation, and injecting shell code, and is a part of almost every hacking toolkit. So there's no way I could leave this out of our series on getting your Mac set up for hacking.

I have been on Null Byte for a long time, a very long time and. I havent always had an account here, ive like many of you also have, been looking and decided to make a profile to contribute.
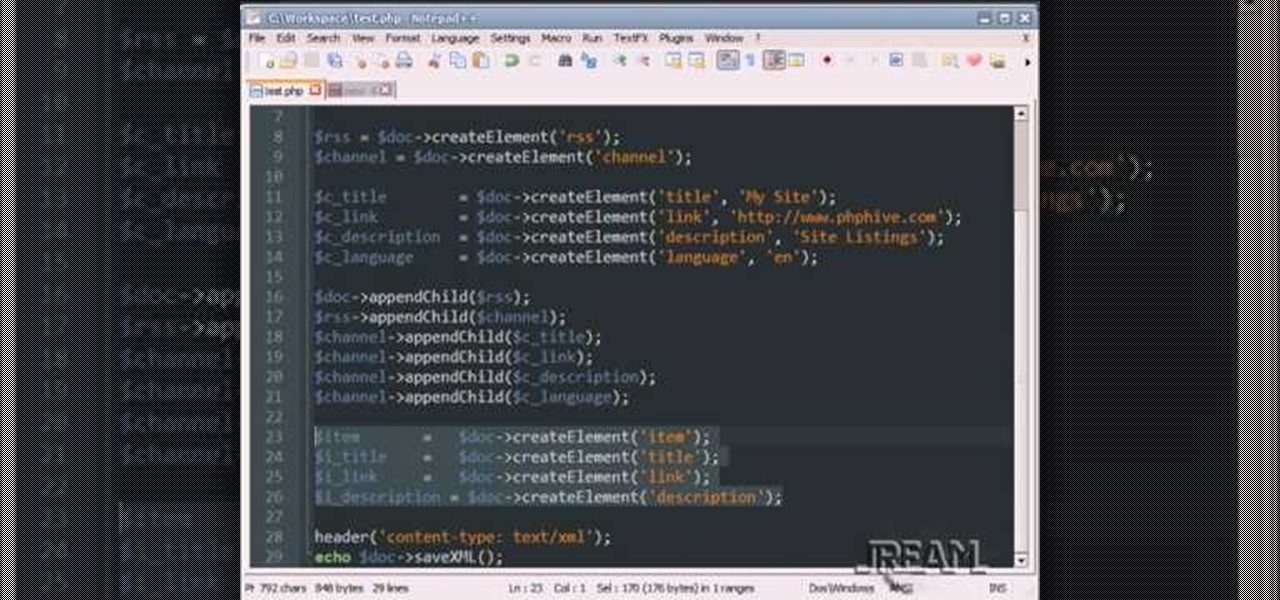
This tutorial teaches you how to create an RSS feed with PHP using DomDocument. You can generate the items with a database loop, and this example uses a very simple array. Take a few minutes and add some more knowledge to your PHP world.
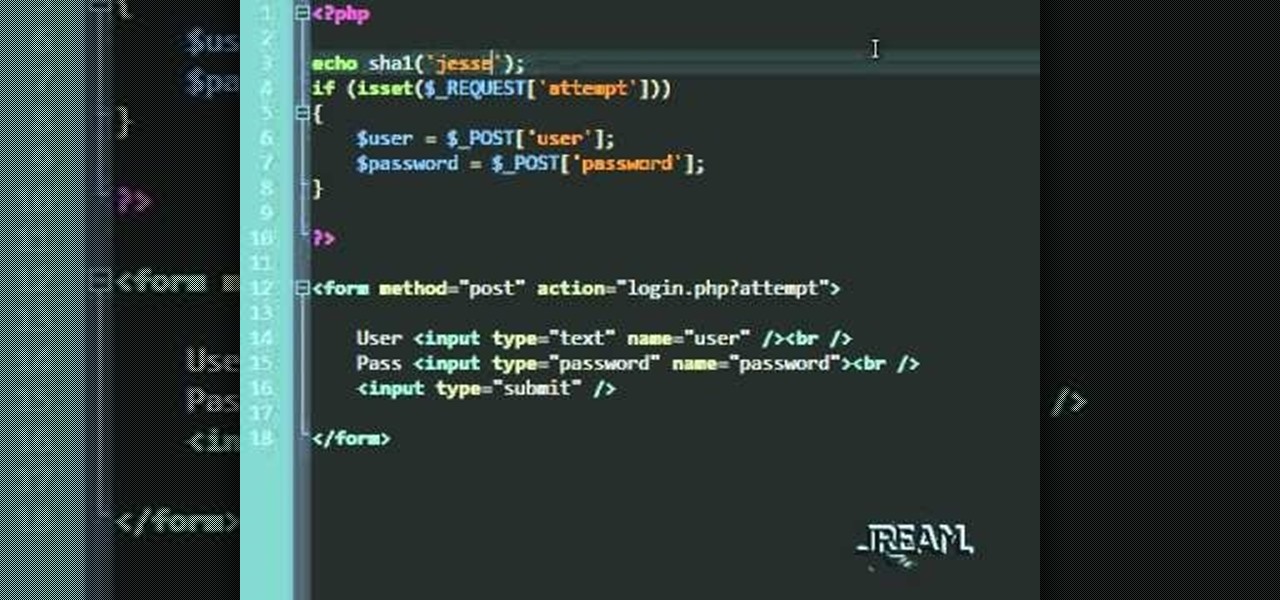
In this tutorial you'll learn about a simple PHP login script that serves to check your MySQL database against a user/password. The code in this video is a quick and dirty procedural code, but it's enough to get you going so you can try it out yourself.
In this clip, you'll learn how to reset or truncate a MySQL DB table directly with script or indirectly through PHPMyAdmin. Whether you're new to the PHP scripting language or a seasoned developer mereley looking to pick up a few new tips and tricks, you're sure to benefit from this video tutorial. Take a look.

MapForce includes support for the two most popular EDI formats, UN/EDIFACT and ANSI X12. In this how-to video, you'll learn how to use MapForce to map and convert data between EDI messages (X12 and UN/EDIFACT) and XML, databases, or text files. Learn to map EDI data with this how-to.

While editing databases with DreamCoder for Oracle, you may find that you want to manipulate master-detail. This minute-long how-to video will walk you through the process in DreamCoder for Oracle. Take a look.

This screencast from Matthew MacDonald, author of Access 2007: The Missing Manual, guides you through creating a custom switchboard in a Microsoft Access database.

INTRODUCTION Hello dear null_byters here we go again with our third part of this serie.

It used to be easy to hack tethering—root your device and install a third-party or modded tethering app. But snuck in amongst the changes in Android 4.3, a new data-monitoring service of sorts made its debut. There used to be a time when your data connection was yours. You paid for it, so you were free to use it for whatever you wanted. Unfortunately, those days are long gone.
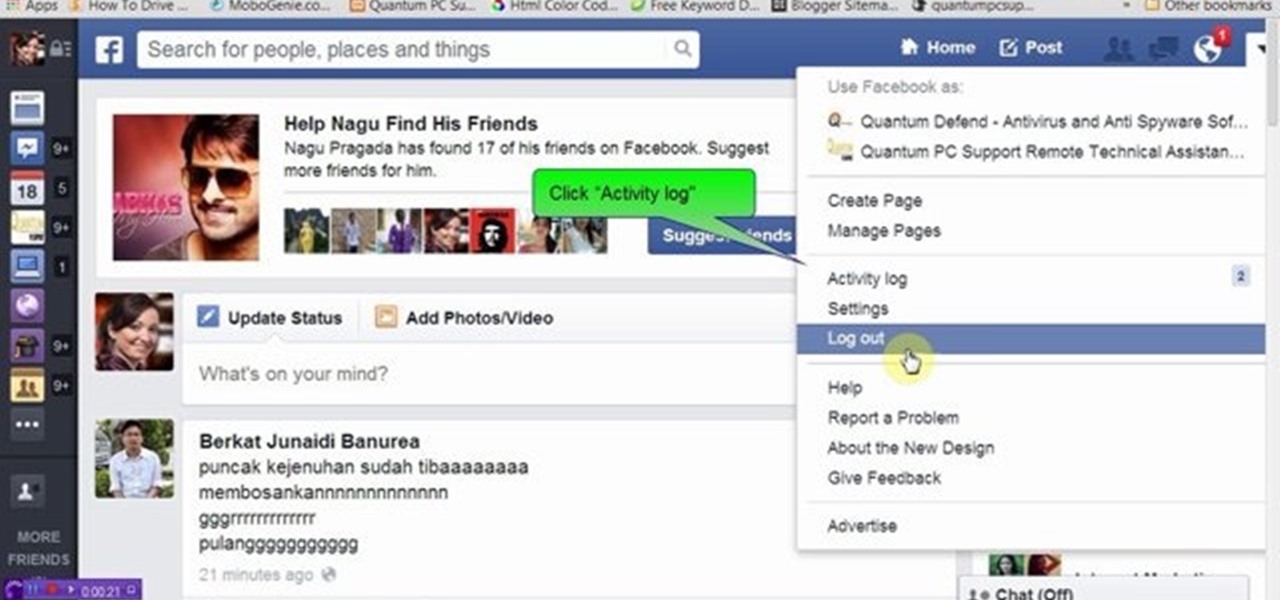
We know that Facebook is a very useful social media site. Facebook keeps your search history in its database. This video will show you how to view or delete history in your Facebook account. Follow the video and try it yourself.
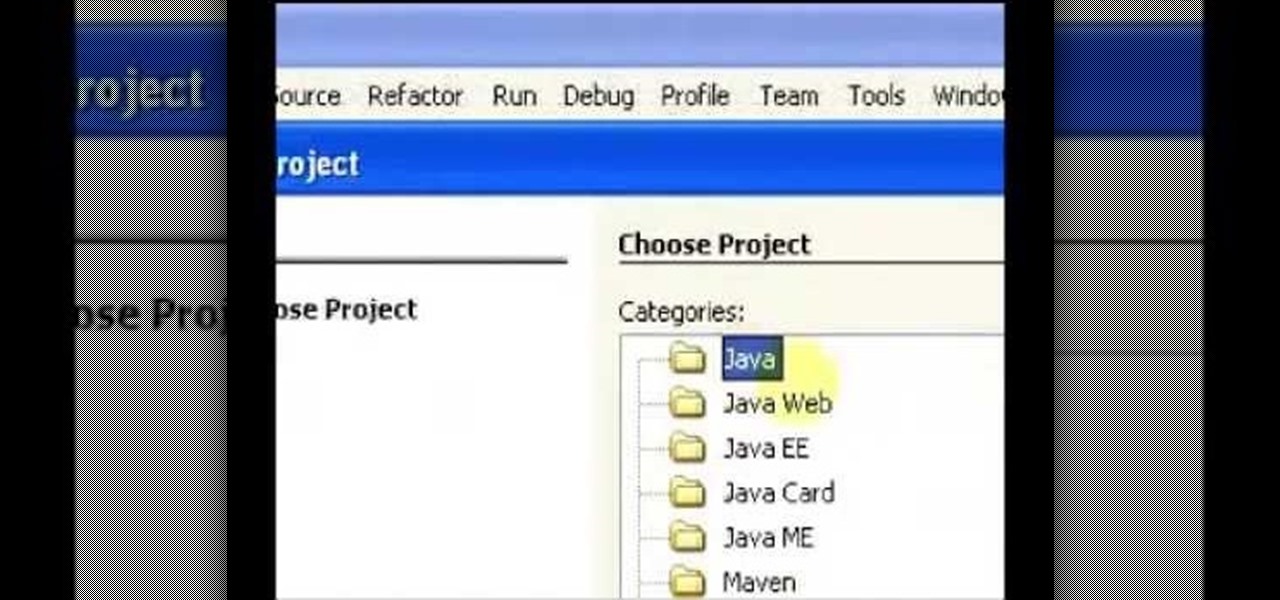
I have made a video to show how we can add an applet into web application. It is shown in two parts. The applet can communicate with database too.

First things first: You can't actually recover a Joomla administrator password. That's because Joomla uses a one-way MD5 hash that prevents you from doing so. However, it is possible to reset your password.

There are many password-cracking tools out there, but one of the mainstays has always been John the Ripper. It's a powerful piece of software that can be configured and used in many different ways. Metasploit actually contains a little-known module version of JTR that can be used to quickly crack weak passwords, so let's explore it in an attempt to save precious time and effort.

No operating system is stricken with as many vulnerabilities as Windows, and it's often a race to release the latest patches to fix things. From an attacker's point of view, knowing which patches are present on a Windows machine can make or break successful exploitation. Today, we will be covering three methods of patch enumeration, using Metasploit, WMIC, and Windows Exploit Suggester.
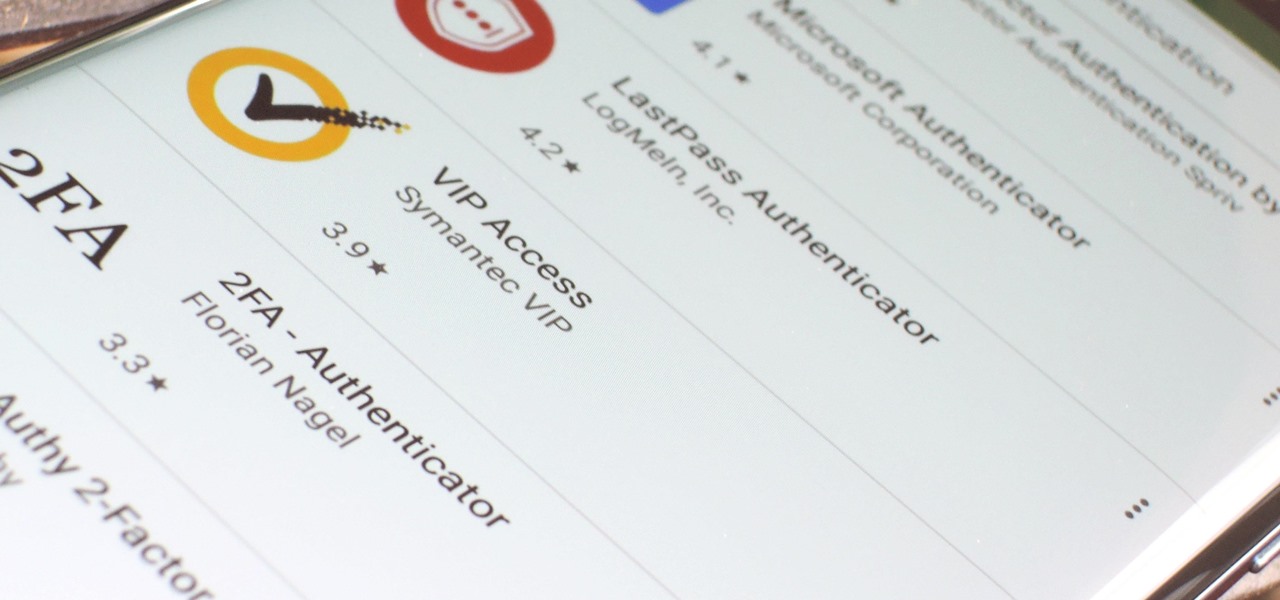
If you want the best two-factor authentication app out there, our pick is Authy. A close second is LastPass Authenticator. If neither of those is to your liking, try Duo Mobile or Microsoft Authenticator. But if you're fine with missing out on great features, then and only then should you look at using Google Authenticator.

GitHub is an extremely popular site that allows developers to store source code and interact with other users about their projects. Anyone can download public, open-source files on GitHub manually or with Git, and anyone can fork off someone's project to expand or improve it into its own project. It's a really great site for programmers, developers, and even inspiring hackers.
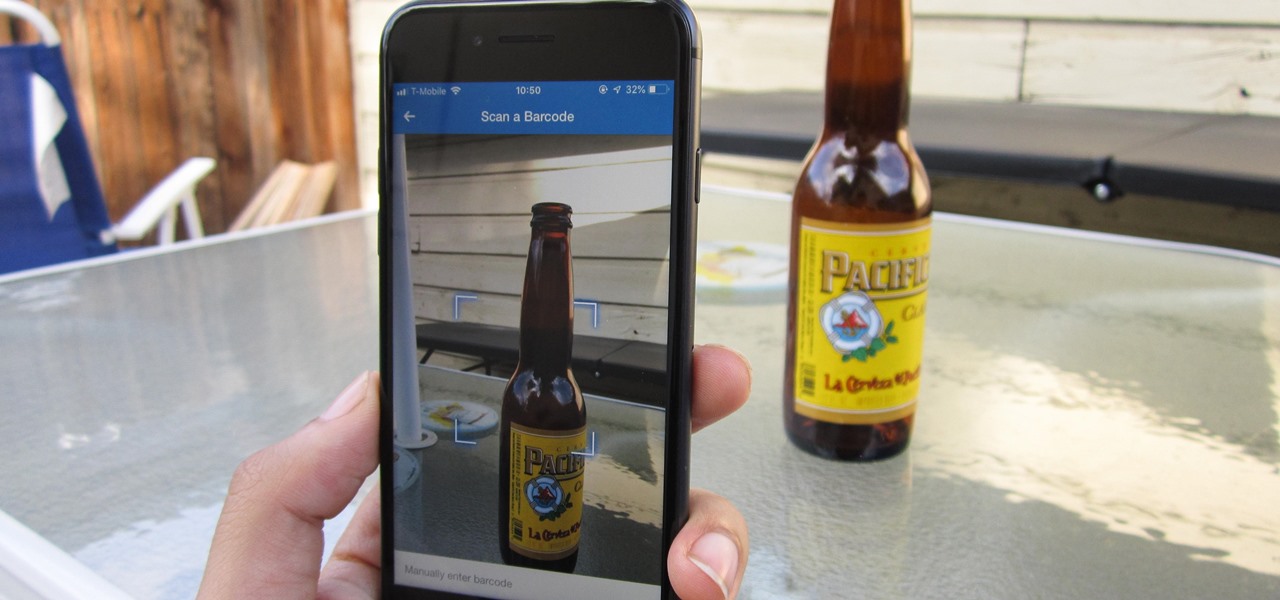
In MyFitnessPal, you can search through a food database to add your meal into the app's diary and track your calories. Unfortunately, the sheer size of the database can make it hard to find exactly what you have just consumed, which is why MFP includes a barcode feature to make the process of adding food much smoother.

Well-regarded men from the history of the United States tend to grace the country's currency, but what if equally deserving women were honored in the same fashion?

It is often said that the best hackers remain unknown, and the greatest attacks are left undiscovered, but it's hard for an up-and-coming penetration tester or white hat to learn anything unless one of those factors is actually known or discovered. But the end goal here in our SQL injection lessons is to make that statement as true as possible for us when performing our hacks.

Google just unveiled it's biggest search product in recent memory, except this time the search giant is looking to take over the world of virtual objects.

Hello friends! This tutorial will teach you how to build a local pentesting lab on your Linux machine which will enable you to easily install common web applications so you can practice locating and exploiting their known vulnerabilities (or discover new ones!). In particular, this is an excellent way to learn how to hack Wordpress, Joomla, and Dupral plus many more!
For every contact photo you add, Android keeps two copies. The first is stored at a 720p resolution, and this is used for high-definition imagery when you're looking at a full-sized contact card. But the second image is only 96 pixels by 96 pixels, and this is used for all thumbnails throughout the operating system.
Yellow buses are beginning to trickle into traffic. Retailers are pushing pens, pencils, and notebooks. Grumbling Facebook statuses run rampant through your feed. Surely you recognize the signs—school is starting. For some, it already has.

In this tutorial, we learn how to use salty hashes to keep passwords secure. A hash is stored in a database that is hashed with an algorithm, so not everyone can see exactly what your password is. When you type your password into a website, it doesn't actually register as words, it registers as a hash. This keeps your passwords secure so not everyone can see them. Salting is when you use random pits and attaching them to your regular hashes so not every password is the same. The salt is what ...
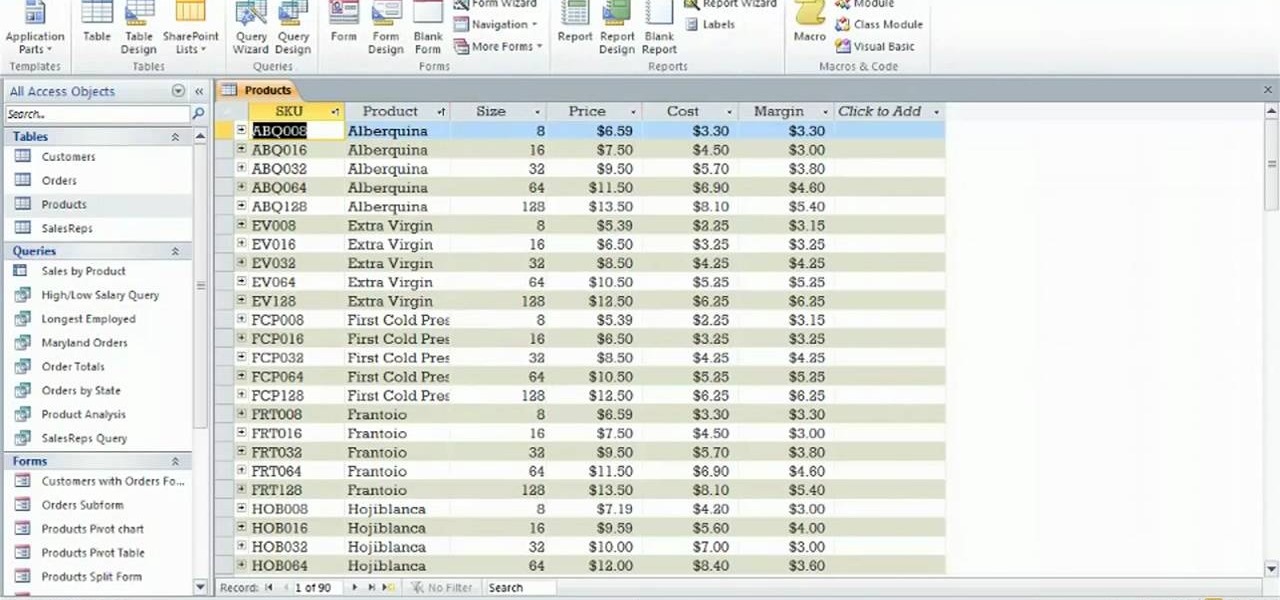
Before you can work in MS Access 2010, you'll need to learn how to work with it. See how to navigate the Ribbon interface when working in Microsoft Access 2010 with this guide. Whether you're new to Microsoft's popular database management application or a seasoned MS Office professional just looking to better acquaint yourself with the Access 2010 workflow, you're sure to be well served by this video tutorial. For more information, and to get started using the Backstage view in your own Acces...

Foundstone Hacme Shipping is a web-based shipping application developed by Foundstone to demonstrate common web application hacking techniques such as SQL Injection, Cross Site Scripting and Escalation of Privileges as well as Authentication and Authorization flaws and how they are manifested in the code. Written in ColdFusion MX 7 using the Model-Glue framework and a MySQL database, the application emulates the on-line services provided by major shipping companies. This video will get you st...

How to Use Your Mac as a Server: Turn your Mac Mini into a server! Yes, that's right, with a little know-how and a little spunk, you can turn an inexpensive Mac Mini computer into a server to provide services over you network. You won't even need the Mac OS X Server, just the Mac OS X Client, so there is no extra software to buy, just the Mac Mini and it's operating system.

A Membership Provider allows a web application to store and retrieve membership data for a user, and the standard ASP.NET Membership Provider uses pre-defined SQL Server tables. In this video tutorial, Chris Pels shows how to create a custom membership provider that uses custom SQL Server tables separate from the pre-defined tables used by the standard provider. The principles covered in the video will apply to creating custom membership providers using other databases such as Access or Oracl...