Working with Oracle, odds are you may, on occasion, need to build an Oracle database from MySQL. Happily, this DreamCoder tutorial will walk you, step by step, through the process. To learn how to build an Oracle database from MySQL data, take a look!

If you're new to DreamCoder for MySQL, one of the first things you may want to know how to accomplish is to connect to a remote MySQL database securely via SSH tunneling. Happily, this tutorial will walk you, step by step, through the process. To learn how to establish a secure connection between a given MySQL database and the DreamCoder for MySQL, take a look!

Pyrit is one of the most powerful WPA/WPA2 cracking tools in a hacker's arsenal, with the ability to benchmark a computer's CPU speeds, analyze capture files for crackable handshakes, and even tap into GPU password-cracking power. To demonstrate how quickly it can hack a WPA/WPA2 password, we'll use it to play a Wi-Fi hacking CTF game anyone can practice for less than $10.

If you thought the selfie would only ever be used to bombard your feed on Instagram, you were wrong. Dead wrong. JetBlue is looking to take those selfies and use them to check you in for your next flight.

Snapchat is attempting to take over the world via augmented reality technology. Well, it's more of a virtual makeover than a takeover, but still ...

T-Mobile just unveiled two new services—Scam ID and Scam Block—which specifically target those pestering robo-calls that reach out to 2.4 million Americans every month.
Hello guys I am ROMEO 64 (sounds weird I guess but who cares. :D).. Alright....Ever wondered what happens when you login to your Facebook account?

Welcome Back !! TheGeeks. SQL Injection (SQLI) Part-1

Though you can use the Social Engineering Toolkit to clone websites, this way is much more customisable.

If I were to lose access to the entire internet for the rest of my life, one of the websites I would miss the most would have to be Wikipedia. Wikipedia has ended countless arguments, informed me of how old and single some of my favorite actresses are, and helped me brush up on thousands of historical topics.

If you're new to DreamCoder for Oracle, one of the first things you may want to know how to do is to monitor a remote Oracle database. Happily, this tutorial will walk you, step by step, through the process. To learn how to monitor a given Oracle database remotely via DreamCoder for Oracle, take a look!

If you're new to DreamCoder for Oracle, one of the very first features you should acquaint yourself with is the export data process, which will permit you to backup your Oracle databases with ease. For step by step instructions, consult this how-to.

There are nearly 100,000 unique onion service addresses online with over two million people using Tor every single day. Join me as I explore a small fraction of what the Tor network has to offer.

Leaked databases get passed around the internet and no one seems to notice. We've become desensitized to the data breaches that occur on a daily basis because it happens so frequently. Join me as I illustrate why reusing passwords across multiple websites is a truly awful practice — and compromise hundreds of social media accounts in the process.

Welcome back, my tenderfoot hackers! As hackers, we often are required to get past antivirus (AV) software or other security measures. To do so effectively, we need to have some understanding of how AV software works. In this tutorial, we will take a cursory view of how AV software works so that you can better strategize on how to evade detection by it.

Many of my aspiring hackers have written to me asking the same thing. "What skills do I need to be a good hacker?"

If you're new to DreamCoder for PostgreSQL, one of the very first features you should acquaint yourself with is the export data process, which will permit you to backup your PostgreSQL databases with ease. For step by step instructions, consult this how-to.

If you're new to DreamCoder for MySQL, one of the first things you may want to know how to accomplish is how to import data to a remote MySQL database. Happily, this tutorial will walk you, step by step, through the process. Take a look!

This MS Office software tutorial gives tips and tricks on integration between Access and Outlook. Access is Microsoft's database software and Outlook is the email software. So if you need to work with your database and email at the same time, check out this tutorial on integrating Access 2007 with Outlook 2007.

Mario hacks, cheats, glitches. How to play and hack the flash game Mario Games. Watch this video tutorial to learn how to hack Mario Games with Cheat Engine 5.5 (09/30/09). Download Cheat Engine.

Ever wanted to find out who stole the cookie from the cookie jar? Take a page from crime scene investigators and get the proof you need.

While we haven't covered Amazon Web Services, or AWS, on Null Byte before, Amazon's cloud computing platform is ripe for attack by hackers, pentesters, and cybersecurity researchers. It's also an excellent cloud hosting service to build or use vulnerable-by-design AWS setups and frameworks.

Businesses leave paper trails for nearly every activity they do, making it easy for a hacker or researcher to dig up everything from business licenses to a CEO's signature if they know where to look. To do this, we'll dig into the databases of government organizations and private companies to learn everything we can about businesses and the people behind them.

Most of us have never put much thought into this, but the question needs to be asked — what exactly happens to all of our online accounts when we die? No, the internet won't just know and delete accounts for you, so you need to plan for life's one guarantee. Because without a plan, things become a lot harder to sort out.

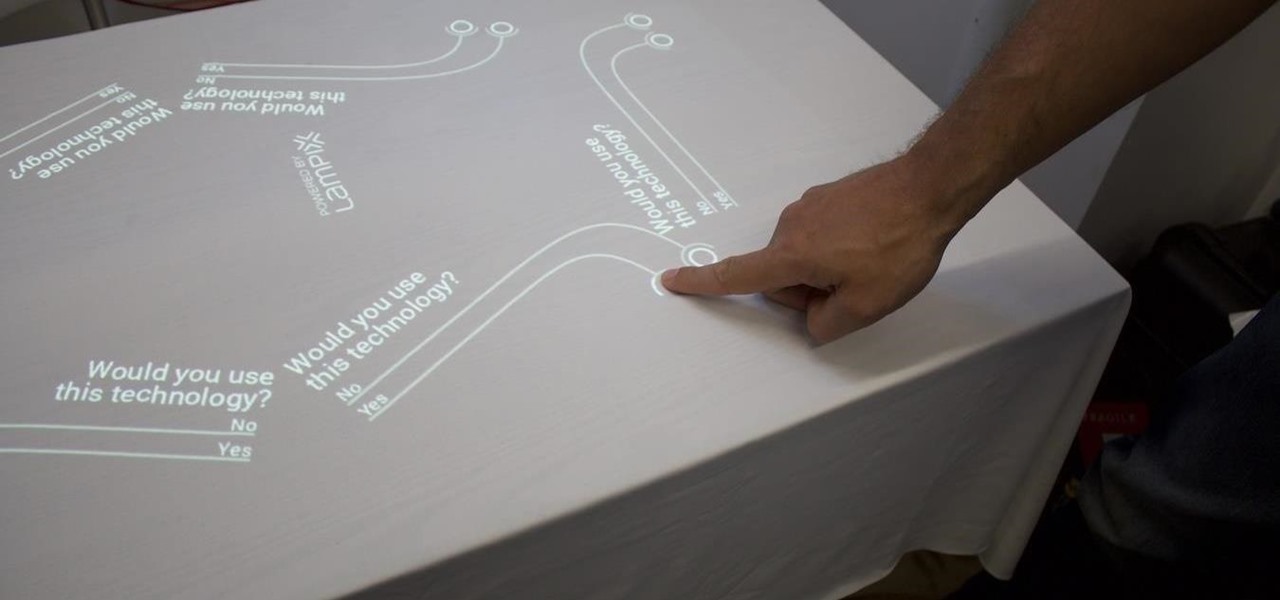
Over the past week, companies took a variety of approaches to investing in augmented reality. Lampix is backing its own effort to build an ecosystem for augmented reality platforms. Nokia and Xiaomi are teaming up on numerous fronts, potentially including augmented reality.

Greetings all. I'm back with another informational review of the diversity of utilities for use in the sphere of hacking at your disposal. Today we are going to cover the insides of CUPP (Common User Passwords Profiler) in its entirety. The tool is very basic in nature, as there is little to no configuration needed to get cracking (worst pun ever). So let's get started, shall we?

Welcome back, my greenhorn hackers! Digital forensics and hacking are complementary disciplines. The better you are at digital forensics, the better hacker you are, and the better hacker you are, the better you are digital forensics. Unfortunately, few people in either profession cross these discipline lines.

Welcome back, my greenhorn hackers! In my continuing effort to demonstrate to you how to hack the ubiquitous Windows 7, we will going after that notoriously vulnerable Adobe Flash that is on nearly every client Windows system (you are not likely to find it on servers).

Welcome back, my aspiring hackers! As mentioned several times in previous Linux tutorials, nearly everything in Linux is a file, and very often they are text files. For instance, all of the configuration files in Linux are text files. To reconfigure an application in Linux, we simply need to open the configuration file, change the text file, re-save, and then restart the application and our reconfiguration is applied.

SQLite is a small C library that implements a self-contained, embeddable, zero-configuration SQL database engine. SQLite implements a large subset of SQL-92 and stores a complete database in a single disk file. The library footprint is less than 250 KB making is suitable for use in embedded devices and applications where memory space is scarce.

Learn how to access the PS3 secret recovery menu by following this tutorial. You will need a PS3, PS3 remote, and a USB charger cable. Hold the power button on your system. Listen for three beeps (as you keep your finger on the power button). The third beep will turn your system off. Repeat this process, but this time, you will hear only two beeps (one beep followed by a quick double beep). Turn your TV on and it will tell you to connect your controller to the PSP. Connect your USB cable to t...

DBAs, developers and designers are often tasked with building and managing databases. Especially when the database has been developed by someone else, you have little to no insight into the database structure. Join Quest Software to learn more about Toad Data Modeler and its features that provide:

The next libSSH or OpenSSH exploit may be just around the corner. Keep your SSH service out of Shodan's database before hackers find new ways to bypass the password protecting the server.

If you need to scan a large number of domains for a specific web app vulnerability, Dorkbot may be the tool for you. Dorkbot uses search engines to locate dorks and then scan potentially vulnerable apps with a scanner module.

After numerous scandals like the Equifax data breach and the 2016 US election, cybersecurity has become a significant issue for Americans. Unfortunately, anytime we use our devices, we're open to a cyber attack — especially when we browse the web. However, there are ways that we can make it harder for hackers and data miners.

So it's 2017 and there are no flying cars and teleportation devices around, but there might be holographic smartphones sometime soon. As cool as that sounds, should we trust a holographic smartphone from a company that has never made smartphones before?

Welcome back, my novice hackers! In a recent tutorial, I showed how the SNMP protocol can be a gold mine of information for reconnaissance on a potential target. If you haven't already, I strongly suggest that you read it before progressing here, as little of this will make much sense without that background.

Researching genealogy takes a little enterprise and the skills of a master sleuth.. Watch this video to learn how to research your genealogy and family tree.

Just days after the launch of Google Poly, the marketplace for 3D virtual objects that developers can use for augmented and virtual reality apps, SketchFab, the current leader in the space, is firing back with a major enhancement to its platform.

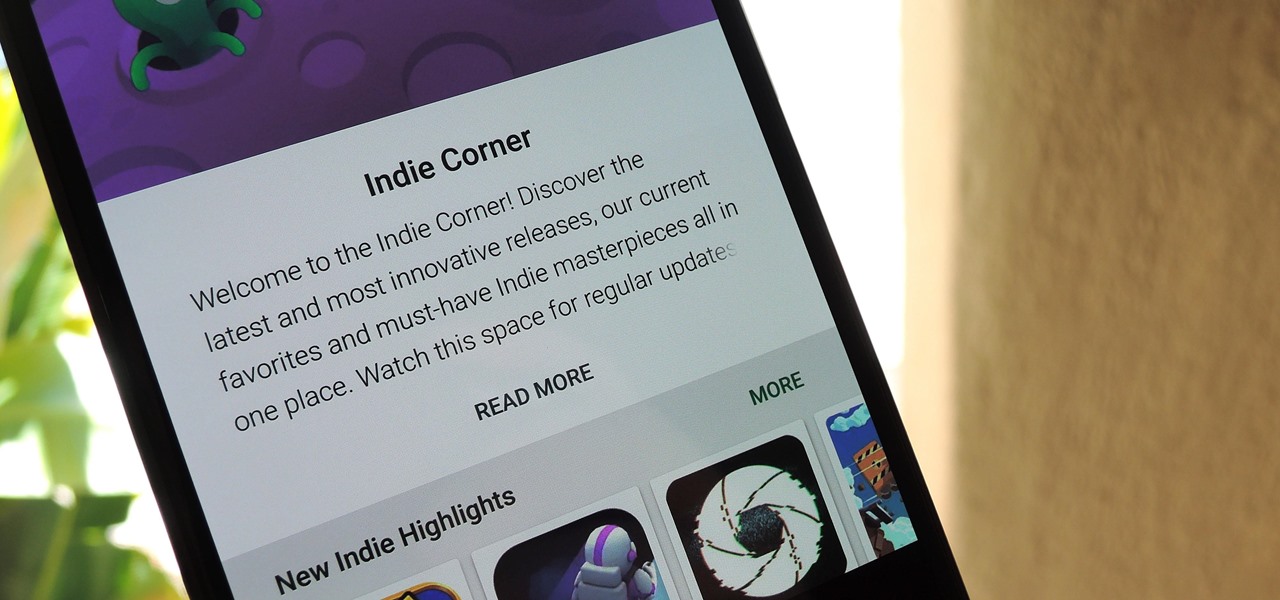
Mobile gaming is a huge industry that raked in more than $91 billion in revenue in 2016, and of course, all of the major players get most of the glory. But smaller, independent game developers make some of the most fun and unique games out there — it's just harder to find their stuff because they don't have the promotional budget of studios like Rovio and Gameloft.