In this video tutorial, viewers learn how to perform hanging knee ups. This exercise targets the abdominal muscles. Users will need to use a smith rack for this exercise. Begin by hanging on the top of the smith rack. Users should have a bar behind the rack that will support the back area. While hanging, users will point the chin down and bring the knees up. Then raise the chin up and bring knees down. Continue performing this movement in a series of sets and repetitions. This video will bene...

This video shows a quick way to lift your sagging jowls with face exercises. This video targets the platysma and sternomastoid muscles at the front of

Are you the one scraping sticky marshmallowed yams and congealed gravy off the dishes every Thanksgiving? Shame someone else into doing it this year. Avoid doing the Thanksgiving dishes.

Check out this video tutorial to learn more about the Phishing Filter on Internet Explorer 7. Web browsers such as Microsoft's Internet Explorer 7 have become an important part of the computing experience for business and home users around the world. With the popularity of web browsers for accessing information, running programs, and even accessing corporate resources, the browser has become a target for viruses, malware, and phishing schemes that present real dangers to Internet users. Inter...

Limber up your back with exercises and stretches for your workout routine in this fitness video. Take action: to find an ideal position use a pole or handle, hold for 15 to 30 seconds while holding the pole lower to target lower back, and change grips. Tom Clifford, the instructor in this how-to video, has a degree in physical education, fitness and health from Eastern Michigan University, where he ran track and cross-country. Tom has worked as a personal trainer for two years. He also has a ...

Get those shoulders ready to exercise. Learn how to do exercises and stretches for your workout routine in this fitness video. Take action: always stretch slowly, using a stretching device, rotate shoulder down to target deltoids, cross arm over chest and pull on elbow, holding for 15 to 30 seconds, and then rotate arms to loosen shoulders. Tom Clifford, the instructor of this how-to video, has a degree in physical education, fitness and health from Eastern Michigan University, where he ran t...

Increase the flexibility of your shoulders. Exercises and stretches for your workout routine in this fitness video. Take action: use stretching device, hold stretch for 15 to 30 seconds, then lean farther from hand to increase the stretch, and rotate shoulder to target deltoids. Tom Clifford, the instructor of this how-to video, has a degree in physical education, fitness and health from Eastern Michigan University, where he ran track and cross-country. Tom has worked as a personal trainer fo...

Shape up your lower back and glutes. Learn how to do exercises and stretches for your workout routine in this fitness video. Take action: position feet 5 feet apart, bend over, exhale and lean to right, exhale and lean around to left, and focus on stretching the target muscles. Tom Clifford, the instructor in this how-to video, has a degree in physical education, fitness and health from Eastern Michigan University, where he ran track and cross-country. Tom has worked as a personal trainer for...

Triceps curls target the muscles at the back of the arm, building muscle mass and toning. Learn how to do triceps curl exercises in this strength training video. Take action: extend arm above head & elbow at 45 degrees, move slowly, lower weight and extend up, fix your upper arm in place, and lift to 7/8 of full extension. Tom Clifford, the instructor of this how-to video, has a degree in physical education, fitness and health from Eastern Michigan University, where he ran track and cross-cou...

Squats are a weight training exercise that involves lowering the body and raising it again, targeting the legs and core. Learn how to do squat exercises in this strength training video. Take action: keep back straight & flexed, keep knees over heels, stick butt out to maintain safe posture, and look forward. Tom Clifford, the instructor in this how-to video, has a degree in physical education, fitness and health from Eastern Michigan University, where he ran track and cross-country. Tom has w...

The calf muscles at the back of the lower leg are important to target when strength and weight training for speed and agility. Learn how to do calf muscle exercises in this strength training video. Take action: use platform or stairwell, stretch calves before flexing muscles, follow full range of motion to increase intensity, try using one leg for more resistance, and keep feet together or wide apart. Tom Clifford, the instructor in this how-to video, has a degree in physical education, fitne...

The large quadriceps muscles on the front of the thigh are important to target when strength and weight training to build overall muscle mass. Learn how to do quadriceps exercises in this strength training video. Take action: squats and lunges strengthen quadriceps, keep back straight, keep knees above heels in squats and lunges, and never lean forward during a lunge. Tom Clifford, the instructor in this how-to video, has a degree in physical education, fitness and health from Eastern Michiga...

Triceps extensions for seniors target the triceps muscles of the upper arm to build muscle mass and tone. Learn how to do triceps extension exercises for seniors in this strength training video. Take action: use sturdy chair, keep back straight and abs tight, use light weight, lift elbow and hold in place, lower the weight, extend 7/8 of full potential, and contract triceps. Tom Clifford, the instructor in this how-to video, has a degree in physical education, fitness and health from Eastern ...

Isolate shoulder muscles with specific weightlifting exercises. Learn tips and techniques for working out the chest, back, shoulders, and arms in this weightlifting video. Take action: targeting anterior & lateral deltoids, bring dumbbells to side with feet shoulder-width apart. Lance is certified personal trainer through American Fitness Association of America. He graduated from UNC with a biology degree and currently works for a gym. He specializes in weight training, circuit training, endu...

Penetration-testing frameworks can be incredibly useful since they often streamline certain processes and save time by having a lot of tools available in one place. Of course, the most popular pentesting framework is undoubtedly Metasploit, but there are many others out there that cater to particular needs. For auditing web applications and servers, Tishna comes in handy.

While much of the world is currently in some form of quarantine due to the COVID-19 pandemic, augmented reality (AR) gives us all the opportunity to see virtual content while stuck in our homes.

Password cracking is a specialty of some hackers, and it's often thought that raw computing power trumps everything else. That is true in some cases, but sometimes it's more about the wordlist. Making a custom, targeted wordlist can cut down cracking time considerably, and Wordlister can help with that.

All Kohl's wants for Christmas is Snapchat augmented reality. In conjunction with a holiday pop-up hosted in New York City from Nov. 7 through Nov. 10, Snapchat ran a sponsored portal lens available to targeted Snapchat users in the AR carousel. The experience gave users the ability to virtually transport themselves to the pop-up.

Businesses leave paper trails for nearly every activity they do, making it easy for a hacker or researcher to dig up everything from business licenses to a CEO's signature if they know where to look. To do this, we'll dig into the databases of government organizations and private companies to learn everything we can about businesses and the people behind them.

If the name Leroy Jenkins elicits a reaction from you, then you are old enough to remember the iconic title World of Warcraft from its heydey (whether or not you actually played the massively multiplayer online role-playing game).

Automating port scanners, directory crawlers, and reconnaissance tools can be complicated for beginners just getting started with Kali Linux. Sparta solves this problem with an easy-to-use graphical interface designed to simplify a penetration tester's tasks.

A hacker with privileged access to a Windows 10 computer can configure it to act as a web proxy, which allows the attacker to target devices and services on the network through the compromised computer. The probes and attacks appear to originate from the Windows 10 computer, making it difficult to detect the attacker's actual location.

A lot of people still trust their web browsers to remember every online account password for them. If you're one of those users, you need to adopt a more secure way of managing passwords, because browser-stored passwords are hacker gold mines. With a USB Rubber Ducky and physical access to your computer, they can have a screenshot of all your credentials in their inbox in less than 60 seconds.

Information gathering is one of the most important steps in pentesting or hacking, and it can often be more rewarding to run things on the target itself as opposed to just running scripts against it remotely. With an SQL injection, a hacker can compromise a server and, ultimately, upload and run the "unix-privesc-check" script locally in order to further identify possible attack vectors.

The ability to stay organized and be resourceful with data gathered from recon is one of the things that separates the true hackers from the script kiddies. Metasploit contains a built-in database that allows for efficient storage of information and the ability to utilize that information to better understand the target, which ultimately leads to more successful exploitation.

Let's face it, iPhones are expensive. With the latest iPhone XS Max reaching as high as $1,449, our wallets could all use a little support. That's where Black Friday comes in, supplying us with deals and discounts on iPhones of all kinds. If you're looking for a new iPhone this holiday season without having to break the bank, you've come to the right place.

One of the first steps in reconnaissance is determining the open ports on a system. Nmap is widely considered the undisputed king of port scanning, but certain situations call for different tools. Metasploit makes it easy to conduct port scanning from directly inside the framework, and we'll show you three types of port scans: TCP, SYN, and XMAS.

With just one line of Ruby code embedded into a fake PDF, a hacker can remotely control any Mac computer from anywhere in the world. Creating the command is the easy part, but getting the target to open the code is where a hacker will need to get creative.

With the rise of website encryption (TLS), sniffing passwords from network activity has become difficult. However, it's still possible to quietly exfiltrate a target's network traffic in real time to extract passwords and sensitive information. Pertaining to macOS, there are two methods for retrieving traffic from a backdoored Mac.

Using Hydra, Ncrack, and other brute-forcing tools to crack passwords for the first time can be frustrating and confusing. To ease into the process, let's discuss automating and optimizing brute-force attacks for potentially vulnerable services such as SMTP, SSH, IMAP, and FTP discovered by Nmap, a popular network scanning utility.

With an ordinary birthday card, we can introduce a physical device which contains malicious files into someone's home and deceive them into inserting the device into a computer.

Now that we have our payload hosted on our VPS, as well as Metasploit installed, we can begin developing the webpage which will trick our "John Smith" target into opening our malicious file. Once he has, we can take over his computer.

During our last adventure into the realm of format string exploitation, we learned how we can manipulate format specifiers to rewrite a program's memory with an arbitrary value. While that's all well and good, arbitrary values are boring. We want to gain full control over the values we write, and today we are going to learn how to do just that.

Earlier this year, rumors began to swirl regarding Apple's upcoming iPhone SE 2. They predicted an A10 processor and a glass back for wireless charging, all at a price point at least $150 cheaper than the iPhone 7. While it wasn't poised to turn heads like the iPhone X, it would have been a reasonable upgrade for many users looking for a more budget-oriented Apple device.

Format strings are a handy way for programmers to whip up a string from several variables. They are designed to save the programmer time and allow their code to look much cleaner. Unbeknownst to some programmers, format strings can also be used by an attacker to compromise their entire program. In this guide, we are going to look at just how we can use a format string to exploit a running program.

During a penetration test, one of the most important aspects of engaging a target is information gathering. The more information you have coming into an attack, the more likely the attack is to succeed. In this article, I'll be looking at SpiderFoot, a modular cross-platform OSINT (open-source intelligence) gathering tool.

The augmented reality feature in Pokémon GO is one of the key components that draw people in to the popular Android and iPhone game. Indeed, there's nothing quite like the sight of a Pokémon standing around in an otherwise uninteresting parking lot.

Devastating and deadly, land mines are a persistent threat in many areas of the world. Funding to clear regions of land mines has been decreasing, but new research may offer a less dangerous method of locating hidden, underground explosives by using glowing bacteria.

The Shadow Brokers, a hacker group known for its dump of NSA hacking tools in 2016, has just leaked their remaining set of data which implies that the NSA compromised SWIFT, the global provider of secure financial services, to spy on banks in the Middle East.

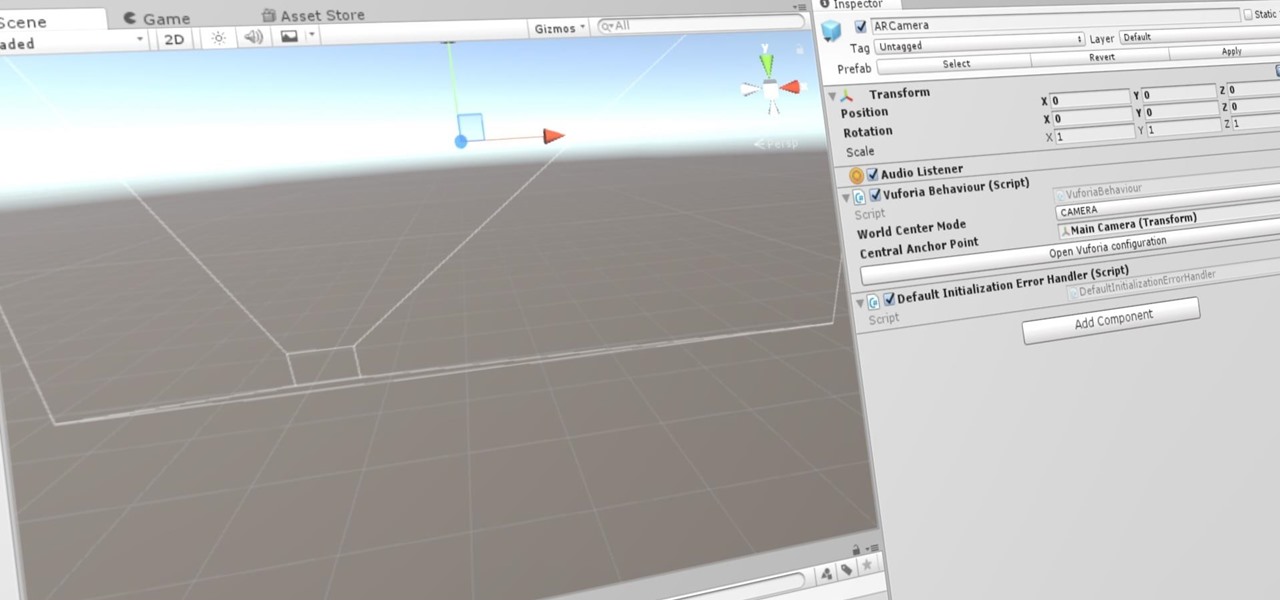
Now that we've set up Vuforia in Unity, we can work on the more exciting aspects of making physical objects come to life on the HoloLens. In this guide, we will choose an image (something that you physically have in your home), build our ImageTarget database, and then set up our Unity camera to be able to recognize the chosen image so that it can overlay the 3D holographic effect on top of it.