
News: Meta Sues Former Employee Over Trade Secrets
Meta Company filed suit today against a former employee and his startup DreamWorld USA, Inc. for the misappropriation of trade secrets and confidential information.


Meta Company filed suit today against a former employee and his startup DreamWorld USA, Inc. for the misappropriation of trade secrets and confidential information.
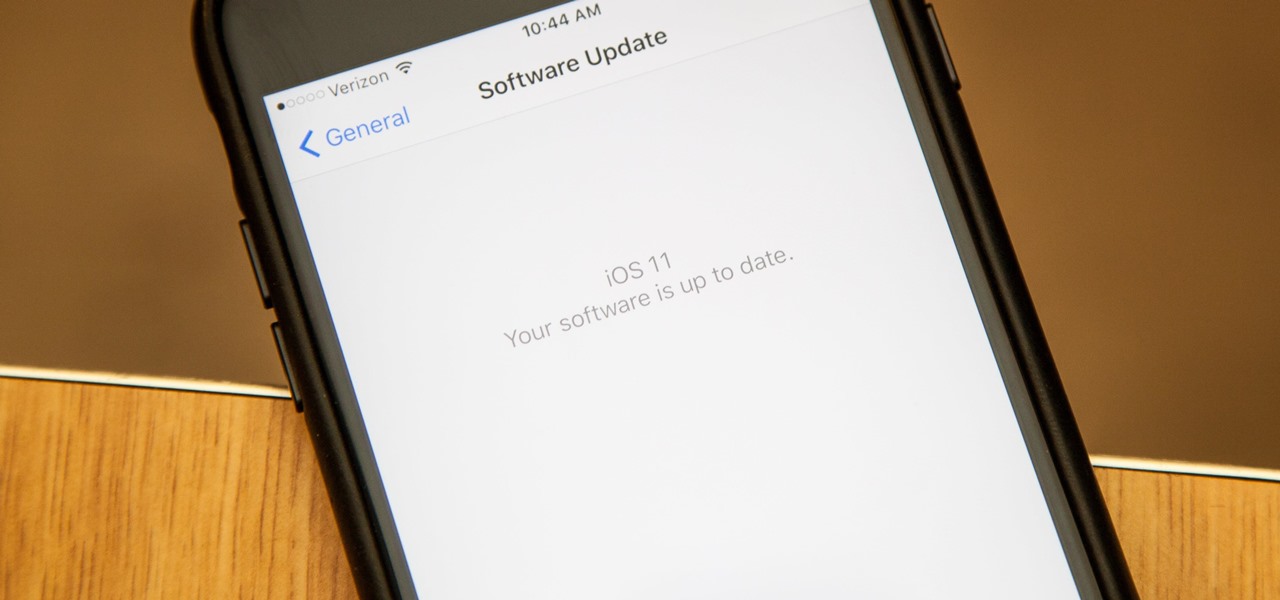
Apple introduced their new mobile operating system for iPad, iPhone, and iPod touch at WWDC on June 5, 2017, and there are a lot of great new features to try out. While the official version of iOS 11 was released to the public on Sept. 19, you can still sign up either as a developer or with the iOS Beta Program to get new versions of iOS 11 before anyone else does.

Marketing and healthcare, two of the leading industries in the adoption of augmented reality, continue to demonstrate applications for the technology in their businesses. Meanwhile, improvements to augmented reality devices are just around the corner with new developments from two display makers.
The driverless competition is heating up as Detroit automakers attempt to woo tech talent away from some of Silicon Valley's biggest players.
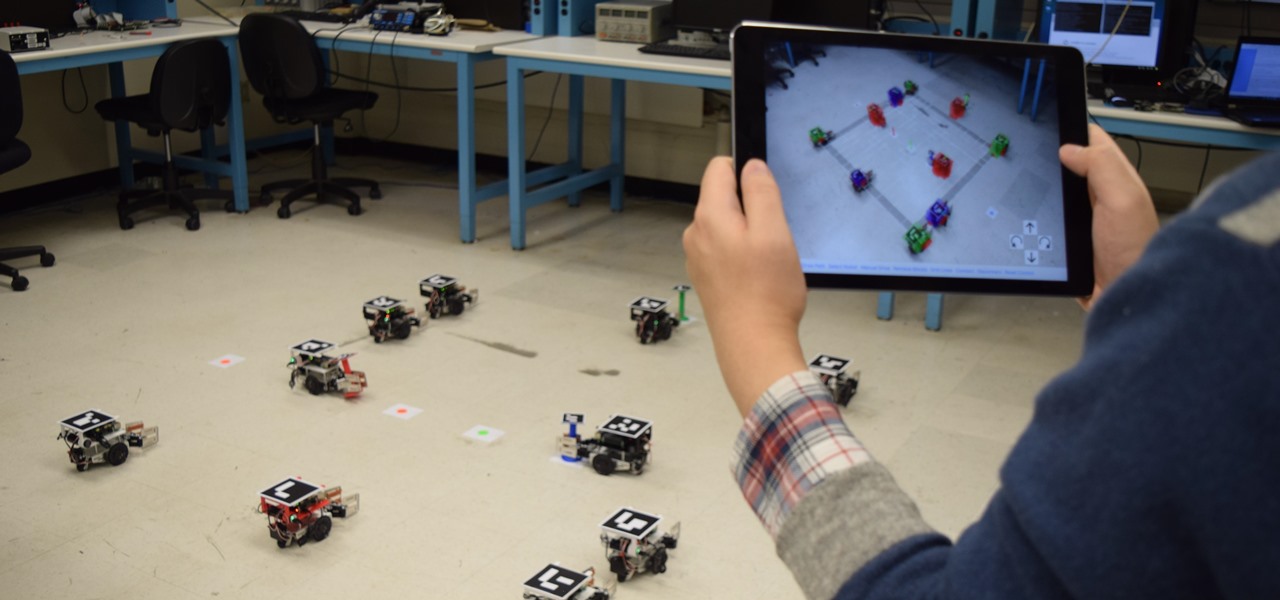
Have you ever wanted to control a swarm of robots? Well, now you can! Robotics researchers at New York University (NYU) have created an app which controls 'bots from your smartphone, using augmented reality. This AR app would certainly come in handy when you want to make a coffee from the comfort of your couch, but let's not get ahead of ourselves!

The Disney Research Lab is using projector-based illumination to paint actors' faces during live performances. You know what that means? Disney just took Halloween to a whole new level.

Onshore, or on a boat, have you ever wondered what swims below in the dark water? Using standard equipment and a new process, marine scientists can now get a good look at what is swimming by—just by analyzing the water.

Obstetric tetanus in an unvaccinated Amish woman after a home birth has emphasized the need for preventative healthcare.

Rabbits have been a persistent problem in Australia for over 150 years. Now the Peel Harvey Catchment Council (PHCC) and Peel-Harvey Biosecurity Group have released a strain of the rabbit haemorrhagic disease virus (RHDV), called RHDV1 K5, to reduce the number of pests in the Murray region of New South Wales.
Google's own devices have always been the first to get new Android features — but unlike the Nexus series, last year's Pixel phones have a handful of exclusive tweaks that were never intended to trickle down to other devices once the newer Android version rolled out to them. These Pixel exclusives included the Pixel launcher and a unique set of on-screen navigation buttons.

For anyone who has spent an entire afternoon attempting to assemble a set of IKEA chairs, these wooden masterpieces probably seem pretty appealing.

Fish are delicate, flaky, and can be damn tricky to cook; more often than not, you end up with a hard, dry block of flesh that makes your taste buds sad. And the best ways to cook fish that you know of—c'mon, who doesn't love a fried fish—take way too much effort for you to bother with on a weeknight. Or maybe you're looking for a healthier way to enjoy fish that doesn't require batter or frying at all.

Consider the radish. This root vegetable is so sadly misunderstood sometimes, and that makes us sad because we adore its spicy flavor and crunchy texture. We're always on the lookout for unique food items that can be turned into a dish of wow and wonder with just a few simple steps, and radishes truly fit the bill.

I fry foods a lot. A LOT. We're talking wings by the dozen here. As a result, I go through a ton of frying oil. Now, frying oil isn't the most expensive ingredient out there, but it adds up when you fry regularly. Of course, I always reuse my oil, but straining it can be a huge mess and it gets to a certain point where enough is enough. It's time to start fresh.

Hash browns are a breakfast staple and for good reason: they're simple, salty, and crispy, and so delicious that you can easily down several servings of them in one sitting. Basically, they're the French fries of breakfast.

Today's pollution, hectic lifestyle, inadequate sleep and no time for pampering can leave your skin lackluster resulting in drying skin and making dry skin drier ultimately causing the early appearance of wrinkles and aging. A good fruit facial helps relax your skin from deep inside and the proper messaging gives it a rosy glow by increasing blood circulation imparting your face with a luminous glow. These are even better because they are natural and chemical free unlike the artificial facial...

You may have caught our prior list of excellent egg hacks. Well, we've rounded up 10 more awesome tips and tricks to perfect your egg game. Check 'em out below.

Knives are among the most important utensils in any kitchen; it's hard to even conceive of cooking a decent meal without them. However, many different foods can be prepped without a knife, and some are actually better off without one. If you don't believe me, then check out these 10 creative methods for chopping, peeling, mincing, and slicing knifeless.
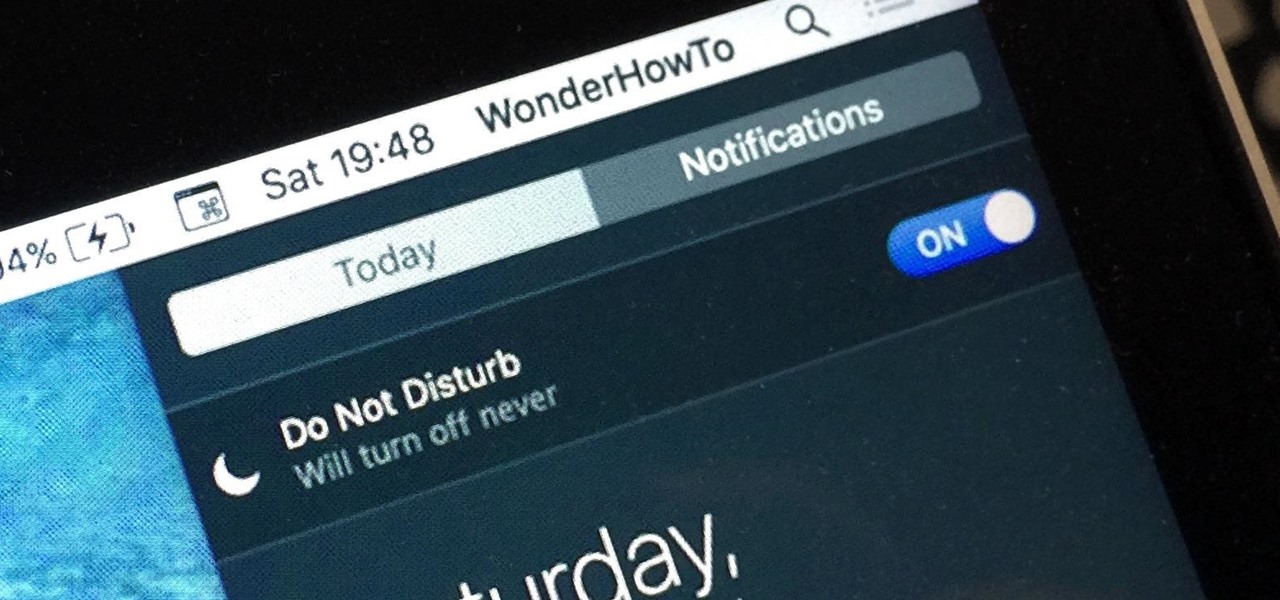
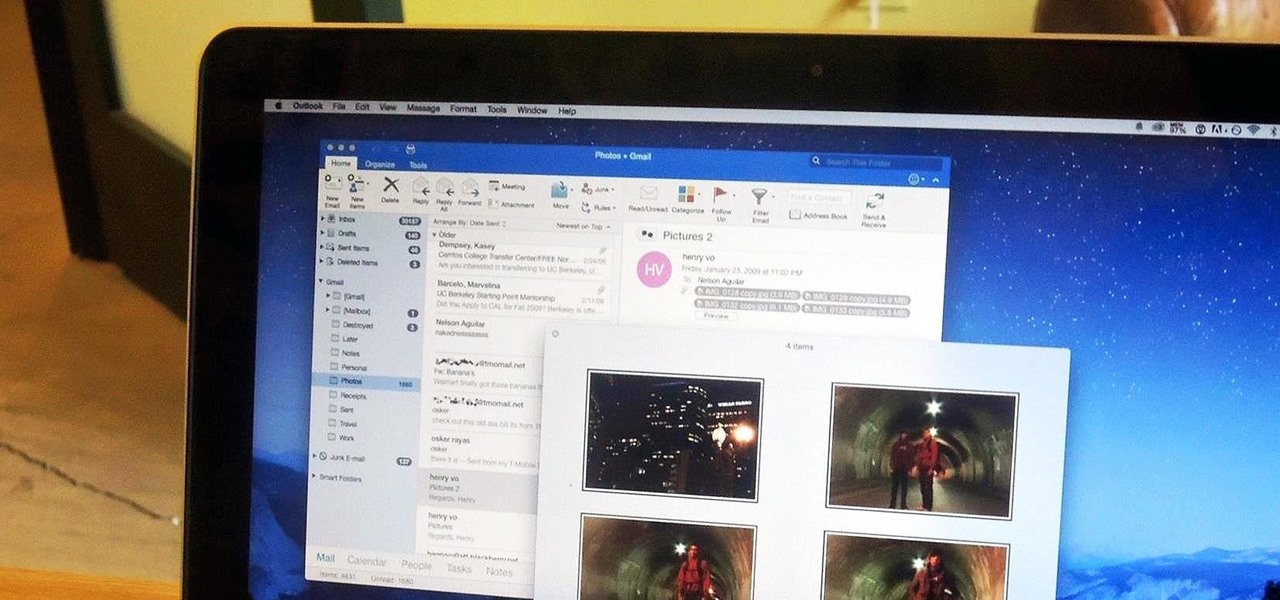
When Apple wanted to bring their Notification Center to Mac OS X, I loved the idea. But after using it since its integration in Mountain Lion, it's been more annoying and distracting than anything. More and more apps incorporate notifications, so I'm constantly getting sound alerts and banners in the top right corner that I don't want.
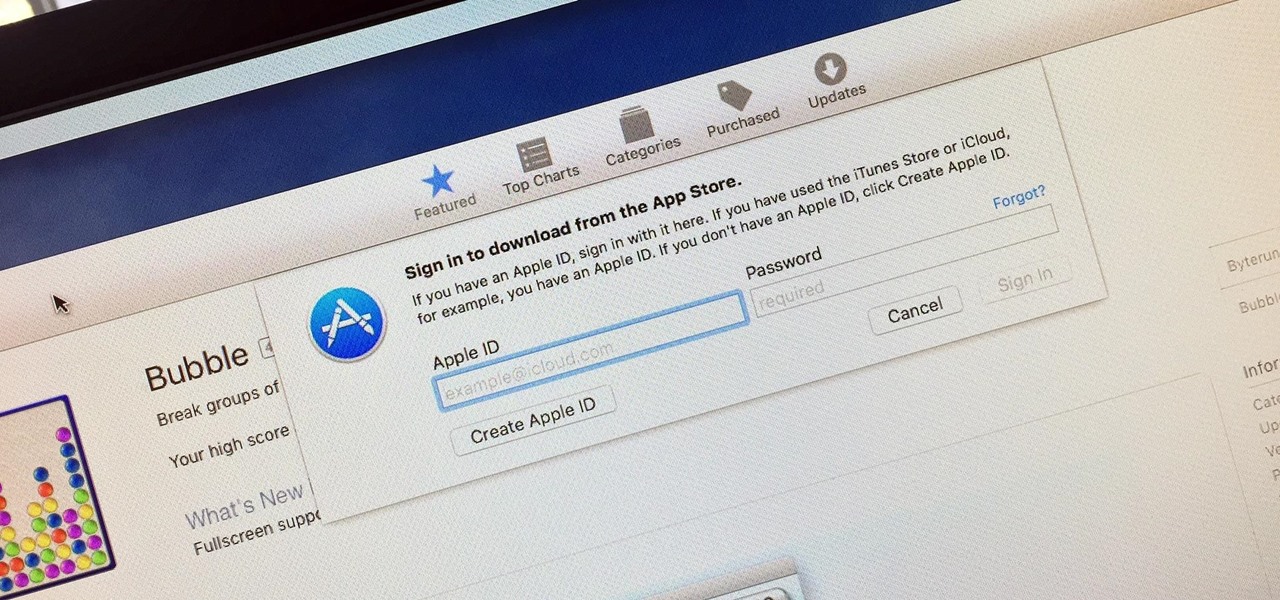
Whether you want to edit photos, compress files, play games, or DJ your next party, there's a free Mac app that can help you out. But things can get annoying real fast if you download a lot of free apps from the Mac App Store, since you have to type in your Apple ID password each time.

This is my first article on here, it's based off of a project that I'm working on at school which is on three ways to bypass windows user password's. If all goes as planned and you all would like I'll work on part two and part three and post them as soon as I can. I do have to give credit to Puppy Monkey Baby and The Defalt, both of whom are my classmates at college and have helped me with writing this article.

One of the best qualities about fresh bread (such as sourdough) is a thick, crispy crust—which is easy to create in a commercial oven, but can be tricky for home cooks to replicate. Luckily, the the trick to baking a professional-style crust is a simple one—just bake your loaf with steam using one of these three methods to achieve the perfect, crispy crust.

You gotta love Android—not only can you replace your default home screen entirely, but there are tons of options that provide alternative methods for launching apps with ease. We've covered some of these options in the past, including an app called Bar Launcher that lets you launch apps from your notification tray—but that one's starting to look a little dated these days.

So you dropped your smartphone and the screen cracked. Again. Just the thought of sending it out for repair or buying a new phone is driving you mad.

There are a million (okay, slight exaggeration) ways to peel an egg, and countless numbers of tips, tricks, and hacks that are supposed to make that deviled egg appetizer you agreed to make for the party an absolute snap. More often than not, though, experiences vary... and pock-marked, greyish-yolked boiled eggs find their way into your collection whether you like it or not.

As a kid, my mother would always bring the noodles onto the table in a colander, then bring the pot of sauce she cooked separately. So I grew up with the idea that pasta and sauce were two separate entities that you combined table-side, and continued to eat pasta that way well into my adulthood when cooking at home. It was only much later that I realized the error of my ways... that pasta could taste so much better than I had previously imagined.

I mentioned in 2015 I wanted to start a 'DoXing' series, and since I havent seen this on Null Byte, I am now going to introduce this to the community.

Hello again, and welcome back to another tutorial on functions, this time, covering recursion. What Is Recursion?

Hello readers, in this tutorial, we will be discussing how to perform file operations such as reading and writing.

School internet filters serve a valid purpose—they keep students from wandering off into the deep corners of the web while still allowing at least some internet access. But a lot of these restrictions are completely ridiculous, to the point where some school districts block access to the educational material in National Geographic or forbid searching terms like "China," "Iran," or "Russia"—because, you know, breasts and commies.

3D Touch on the iPhone 6S and 6S Plus is a pretty cool feature, and will only get better as more developers begin to roll its functionality into their apps.

This is my first ever how-to so I apologize in advance for any grammar mistakes or spelling errors. Introduction
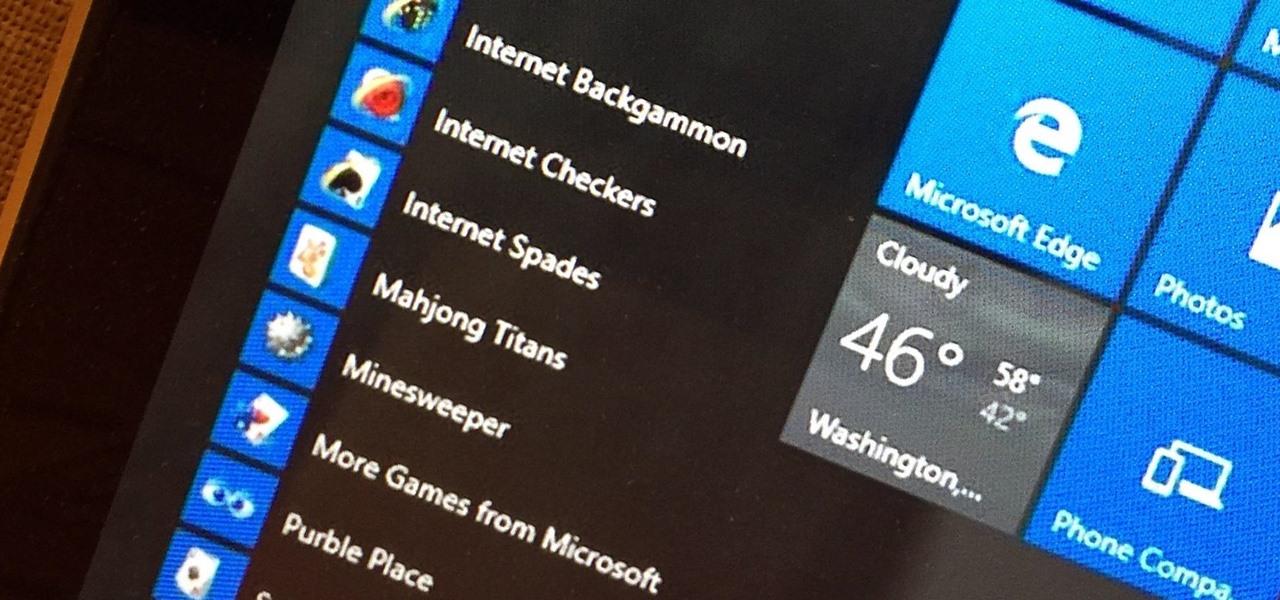
Microsoft's Windows 10 has proven to be a solid release by Microsoft, with faster adoption rates than its predecessor builds. The seamless integration of cloud services and tweaks both major and minor make using Windows easier than ever now. And it's almost enough to forget you ever used Windows Vista... almost.

Everyone starts their mornings differently, but one common thread amongst the masses tends to be the consumption of coffee, albeit in many different forms—instant, pre-ground, K-Cups, Nespresso, and so on. And I'm sure that we all have our own preferred methods, as well.

Boxed brownie mixes advertise their convenience compared to homemade brownies—with only a few ingredients, they promise a moist, chocolatey crumb. However, these "instant" mixes still require fresh ingredients and a baking time that matches that of homemade brownies. When you're craving a chocolate fix but you're coming up short on eggs, oil, and time, don't despair: you can still make brownies using a can of soda. Two Different Methods, One Soda Required

Android has a brand new mobile payments system, and it's rolling out to most devices as we speak. Android Pay, as it's called, will replace the existing Google Wallet app as an update, and it brings some awesome new functionality such as tokenization and the ability to tap-and-pay by simply unlocking your phone.

Onions add essential flavor to almost any dish, whether it's a sauce, main dish, or salad. They are one of the humblest "superfoods," full of vitamins and nutrients but generally inexpensive, which is why they're also one of the most widely eaten ingredients in the world.
After my hard drive crashed recently, I lost everything. Old college essays, half-written stories, short films, and most importantly, all of the photos that I had saved from the past five years... all gone.
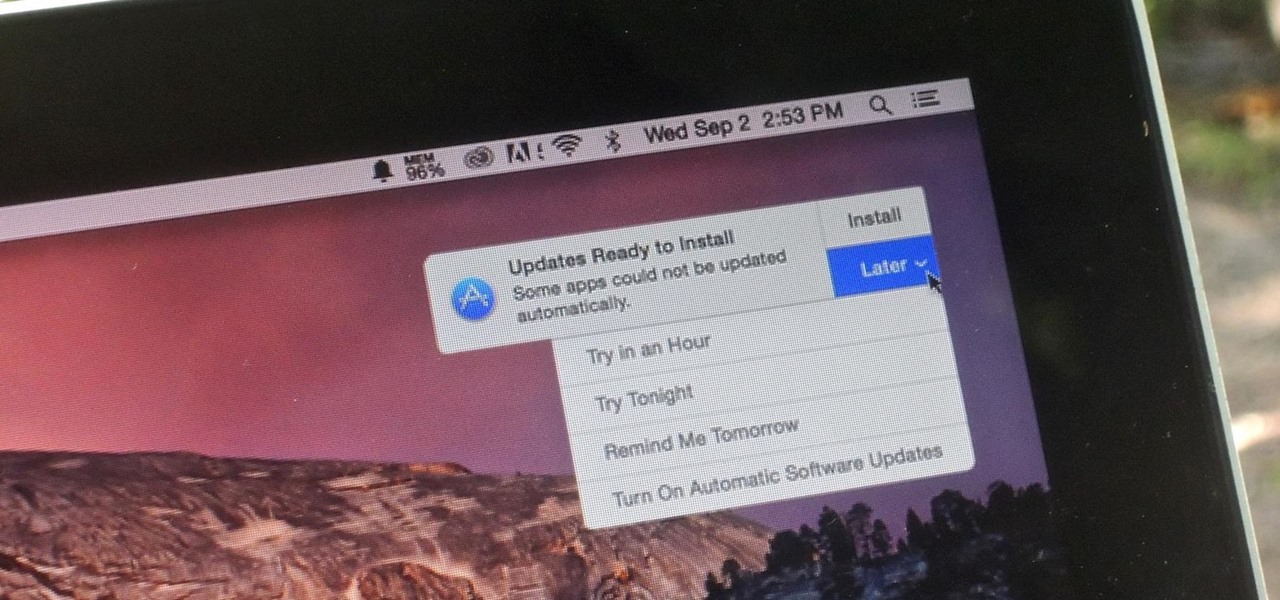
Software update notifications are meant to be a reminder to keep your operating system and apps up to date, but that doesn't mean that they never get annoying.

If you read my last tutorial on using SEToolkit, you probably know that SEToolkit is an effective way to make malicious actions look legitimate. But, that was only the beginning... the truth is, Metasploit and SEToolkit belong together, and help each other very well.