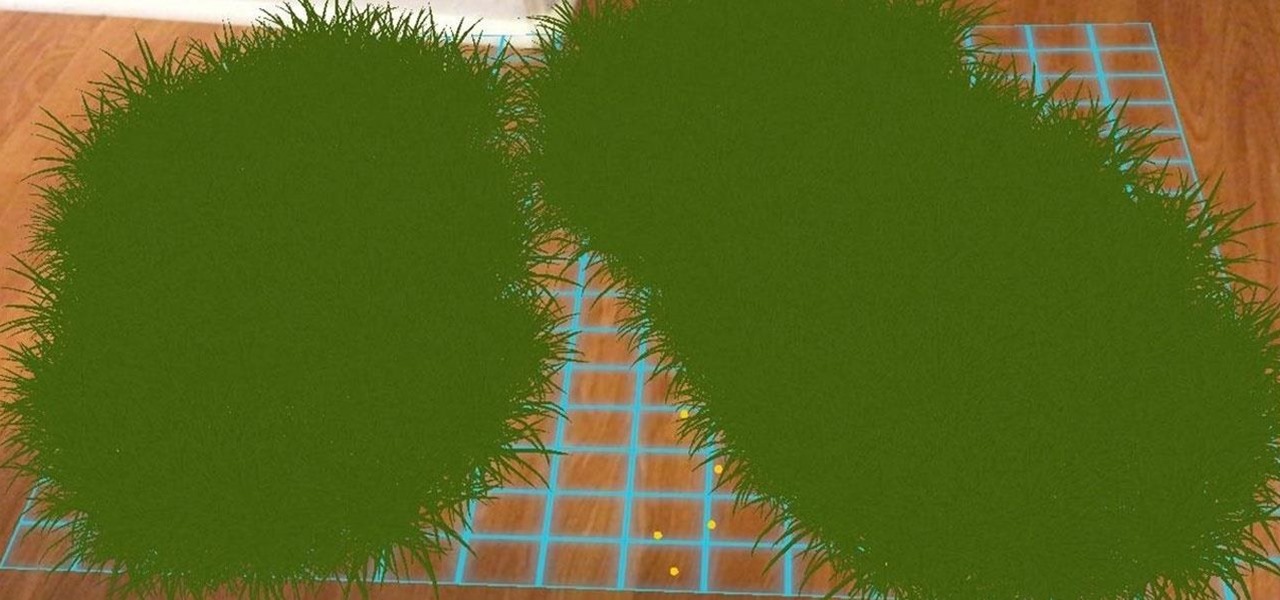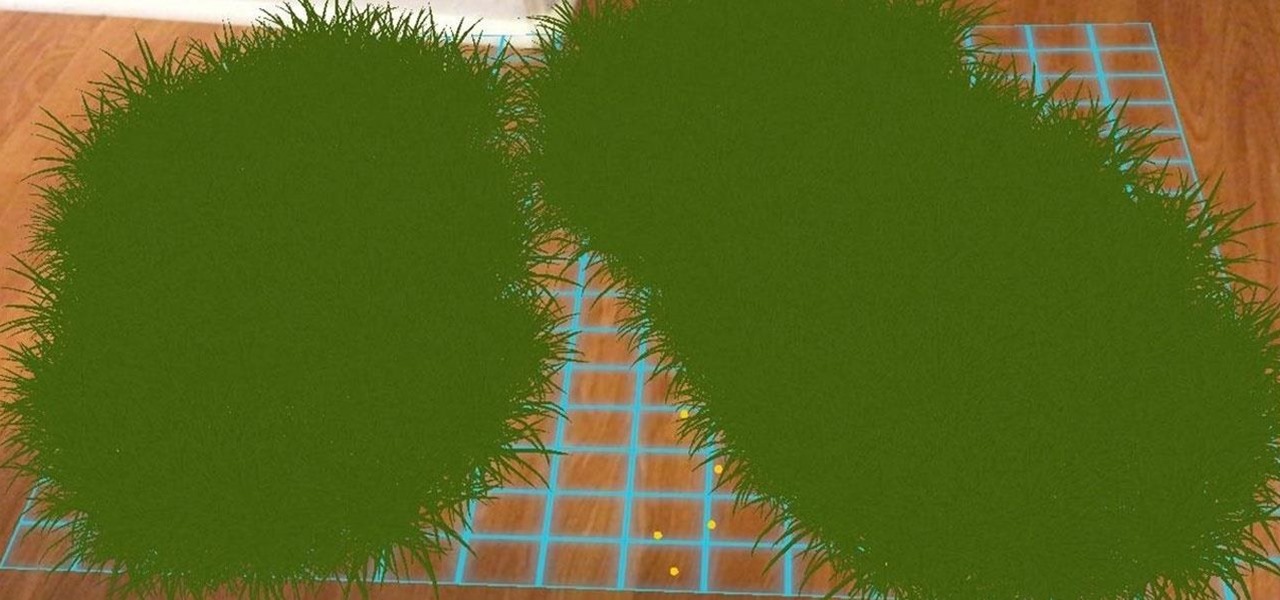
Ever notice how some augmented reality apps can pin specific 3D objects on the ground? Many AR games and apps can accurately plant various 3D characters and objects on the ground in such a way that, when we look down upon them, the objects appear to be entirely pinned to the ground in the real world. If we move our smartphone around and come back to those spots, they're still there.

Hello, budding augmented reality developers! My name is Ambuj, and I'll be introducing all of you Next Reality readers to the world ARKit, as I'm developing an ARKit 101 series on using ARKit to create augmented reality apps for iPad and iPhone. My background is in software engineering, and I've been working on iOS apps for the past three years.

Its official: On May 8, T-Mobile finally released the Android Oreo update for the LG V30 and V30+. Now, every major US wireless carrier has pushed the update. For me, this update is a big deal. Not only does Android Oreo bring some new tools and features, but LG has also included a few additions as well.

While there are at least five cool things coming in iOS 11.4, they may not be enough to get you to install the iOS 11.4 beta on your iPhone. Since its initial beta release at the start of April, there have been plenty of known issues and user-reported bugs to deal with. While bugs are to be expected with a beta, you may want to read these before installing this one on your iPhone.

Google Calendar is a cornerstone of the Google Suite, perhaps second only to Gmail itself. Whereas email is constantly plagued by phishing attacks, as of yet, the calendar is a relatively untapped social engineering attack vector. But it's relatively easy for an attacker to inject a meeting or event into a target's Google Calendar and use it to exploit them.

One feature in iOS you're likely underutilizing is 3D Touch, a highly useful, unique tool for iPhones ever since it first appeared on the iPhone 6S. Apple's pressure-sensitive interactivity gives iOS an extra layer of functionality, which can be clearly seen across the entirety of your device. From the lock screen to the home screen to the apps in between, there are plenty of ways to use 3D Touch.

TouchWiz might not be the Android skin of choice for hardcore aficionados, but the Galaxy's OS still has a ton of great features up its sleeve that help provide one of the most enjoyable smartphone experiences out there. Many of these are relatively hidden and overlooked features that you may not be aware of.

One of Android's biggest strengths is its flexibility. There's usually more than one way to perform the same task, which makes it easy to find an alternate method that works better for you. Android also has some hidden features that newer users might not be aware of, so we made this list to highlight lesser-known tips and tricks.

The war on dehydration is a commercially burgeoning marketplace. An increasingly sophisticated consumer population hoping to conquer everything from 26-mile marathons to vodka shots is deconstructing every functional remedy in the fight to quell the effects of severe dehydration.

They're finally here — Samsung has officially revealed the Galaxy S9 and S9+, which run Android Oreo out of the box. Since we've spent plenty of time with the Oreo beta for the Galaxy S8, we already know about some of the best new software features coming to the Galaxy S9. Like previous updates, Samsung has enhanced its software with a fresh look and brand new functionality.

An attacker with shell access to a Linux server can manipulate, or perhaps even ruin, anything they have access to. While many more subtle attacks could provide significant value to a hacker, most attacks also leave traces. These traces, of course, can also be manipulated and avoided through methods such as shell scripting.

One of the best things about Android is the ability to customize your phone to your liking. From changing the layout of icons to finding the perfect wallpaper to reflect your current mood, there's a wide range of tools to make your phone yours.

Andre was enjoying the carefree life of a 12-year-old with his friends, riding his bike and playing sports, like all kids that age. Schoolwork wasn't hard for him, and his grades showed that.

PowerShell Empire is a post-exploitation framework for computers and servers running Microsoft Windows, Windows Server operating systems, or both. In these tutorials, we will be exploring everything from how to install Powershell Empire to how to snoop around a target's computer without the antivirus software knowing about it. If we are lucky, we might even be able to obtain domain administrator credentials and own the whole network.

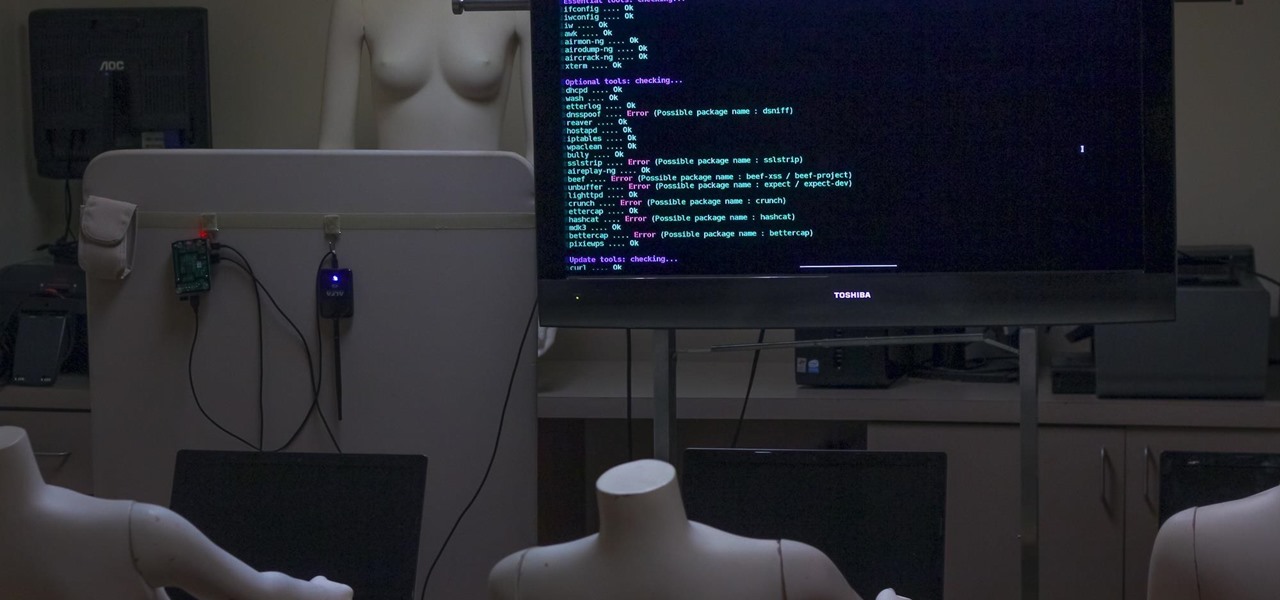
Airgeddon is a multi-Bash network auditor capable of Wi-Fi jamming. This capability lets you target and disconnect devices from a wireless network, all without joining it. It runs on Kali, and we'll cover installing, configuring, and using its jamming functionalities on a small, inexpensive Raspberry Pi. When done correctly, it will deny service to a wireless network for up to several blocks.

Brand loyalty is one of the main factors behind our decision to choose a particular mobile device, but it doesn't have to be the entire equation. Educated consumers know that certain devices simply fit their budget and usage better than others, which means you can't always let a logo dictate what kind of phone or tablet you buy.

It always looks different when it's not about you. The Internet is our world's Alterego. Those many bits don't really make sense unless we want them to be valuable, to mean something.

Hello all! In this tutorial, I'd like to show you one way of getting root on OS X. Check out this GitHub page for a recent privilege escalation exploit that was recently discovered. I've tested it and it works on both OS X 10.9 Mavericks and OS X 10.10 Yosemite, but appears to have been patched with OS X 10.11 El Capitan. If you check out the file main.m you can see where most of the magic is happening. This source code can very easily be changed to make it do more than just the system("/bin/...

Windows 10 is officially here, and frankly, there's a ton of new features in Microsoft's latest operating system. From the return of the Start menu to the new Edge browser, Windows 10 can take some getting used to.
Hello and welcome to my article. I have made this article for anyone who wants to become a hacker, and wants to know how to get started.

Did you know Kali 1.0.8? You probably did, and you probably know about the EFI boot option that has been added.

What if the code you are trying to reverse engineer is obfuscated or somehow corrupted? What if no way is left? Here comes what I like to call (wrongly and ironically) the "brute force of reverse engineering".

Since its introduction on the iPhone 5S, Touch ID has made unlocking Home button iPhones quick and secure. The second-generation iPhone SE brought back the beloved feature in 2020 but didn't take any steps to improve on the technology. So if you're rocking Touch ID and having trouble getting it to read your fingerprints, there are some things you can do to fix it.

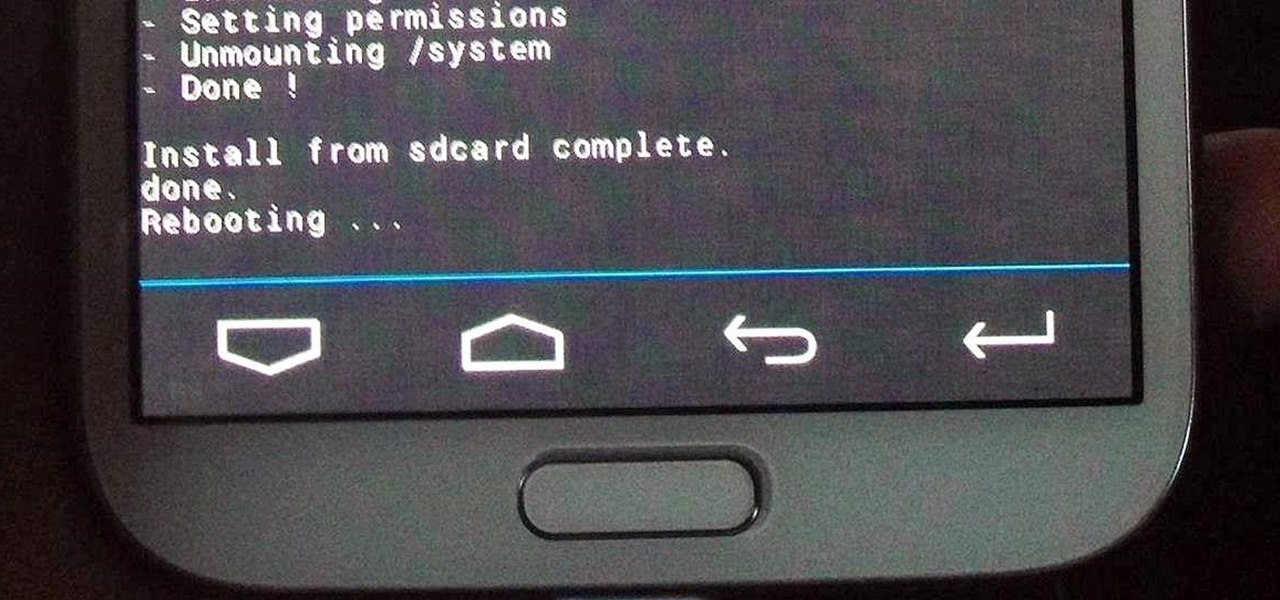
Just like the recently rediscovered Star Wars ruins in the Tunisian desert, there are tons of hidden treasures in your Samsung Galaxy Note 2 just waiting to be unearthed.
Nobel-prize winning economist Paul Krugman and Republican presidential candidate Ron Paul talk about inflation, monetary policy and the role of the Federal Reserve. They speak on Bloomberg Television’s “Street Smart.”

Plantation Shutters Plantation Shutters give your home a clean and contemporary look that is both stylish and functional! This particular brand EuroVue by Bali are easy to install, even for the most novice do-it-yourselfers.
California grad student on no-fly list gets home after stranding An American student who discovered he was included on the government’s no-fly list and was barred from a U.S.-bound flight from Costa Rica was reunited with family and friends after he flew to Mexico and then walked across the U.S.-Mexico border Thursday evening.

This video demonstrates how to add a data table to an Excel 2007 chart. From the people who brought you the Dummies instructional book series, brings you the same non-intimidating guides in video form. Watch this video tutorial to learn how to add a data table to an Excel 2007 chart, For Dummies.

Metadata is data about data. Different file formats store extra data about themselves in different ways. This video will cover metadata that can be used during a forensic investigation, namely MS Word doc metadata and the metadata stored in a Jpeg's Exif data. Find metadata in Word docs and jpegs supporting Exif.

If you want your Lego Mindstorms NXT robot to function as accurately as possible youneed to understand how to get data from the viewing sensors via the NXT brick. Learn how to use the NXT brick and the NXT programming environment to view and change light, sound, or touch sensor data on a Lego Mindstorms Robot. View sensor data from a Lego Mindstorms NXT robot.

Data hubs allow you to create interactions among the different function blocks in the NXT programming environment. Using data hubs allows you to program your Lego Mindstorms NXT robot to perform complex tasks or output information based on these tasks. Program data hubs in the Lego Mindstorms NXT system.

At first, the Black Ops 1.04 patch seemed like a godsend. It was supposed to fix the horde of issues plaguing Call of Duty: Black Ops on the PlayStation 3.

Xeni visits the offices of the Electronic Frontier Foundation and speaks with Jake Appelbaum and Bill Paul, two of the authors of a security research paper that shows how your computer's memory can be tricked into revealing data you thought was safely encrypted, and out of the reach of others. Hack into encrypted computer data.

Oh Data, You so Awesome! We are going to use Node.JS to gather us some data. Given nodes plethora of well abstracted network abilities and it's deep evened nature, it will make quick work of plugging into various data sources and gathering / making good use of said data.
More and more websites implementing "like buttons" from Facebook, Google and Twitter. However, these buttons transmitting data to the operator of their network platforms already when the page loads – so completely without users approval.

By now, many of you may have heard about iPhone tracking and recording your location data, but is there anything else being extracted from cell phones without our knowledge? If you're a Michigan state resident, the answer is an alarming "maybe".

Most of us swipe on Tinder while on the go. With all the pictures, Tinder on Android and iOS uses a decent amount of data. If you know the pain of Tinder triggering overage fees, limit the data-hungry app. There's a little trick you can use to help keep your swiping up and your mobile bill down.

In this clip, you'll learn how to use the Entity Framework and RIA Services to migrate data from an SQL database to a Silverlight DataGrid (data grid). Whether you're new to Microsoft's popular web application framework or a seasoned web developer merely looking to improve your chops, you're sure to find benefit in this free MS Silverlight programming lesson. For more information, including a complete demonstration and detailed, step-by-step instructions, take a look. Move data from an SQL da...

Welcome to Part 3 in my series on protecting your computer from prying eyes (Part 1, Part 2). In today's segment, we will be going over drive encryption using the TrueCrypt program on Windows OS. Drive encryption is a technique that masks your data with a cryptographic function. The encryption header stores the password that you have entered for the archive, which allows the data to be reversed and read from. Encrypted data is safe from anyone who wants to read it, other than people with the ...

While we're waiting for Google to sort out the mess over suspended Google+ accounts, it's a good reminder that you have the option to download much of your Google+ data with Google Takeout. Google Takeout, created by an internal Google engineering team marketed as the Data Liberation Front, is a free service that provides a handy and easy way to download data from your Google+ stream, your contacts and circles, and other information in a zip file.