
How To: Make a Lego Man Halloween Costume Based on Any Lego Movie Character
Who doesn't love The Lego Movie? With a theme song that shouts the film's awesomeness, becoming one of its brick-bodied, eternally happy characters is everyone's dream.


Who doesn't love The Lego Movie? With a theme song that shouts the film's awesomeness, becoming one of its brick-bodied, eternally happy characters is everyone's dream.

Welcome back, my hacker novitiates! Every so often, a MAJOR vulnerability appears that makes millions of systems vulnerable to attack. The most recent, named Shellshock, basically leaves every Mac OS X, Linux, and UNIX system on the planet vulnerable. As nearly two-thirds of all web servers on planet Earth run one of these operating systems (primarily Linux), that's a whole lot of systems out there waiting to be harvested.

Welcome back, my amateur hackers! Many of you here are new to hacking. If so, I strongly recommend that each of you set up a "laboratory" to practice your hacks. Just like any discipline, you need to practice, practice, and practice some more before you take it out to the real world.

HTC is one of the few OEMs that make it easy to unlock the bootloader on their devices. And while they do warn you that doing so voids your warranty, they don't tell you that it also prevents you from collecting promotions that come with their devices.

It's been a minute since Michael Bay released his tragedy of a remake of Teenage Mutant Ninja Turtles. As a huge fan of the cartoon and the movies from the '90s, I have made it a point to not watch the latest this franchise has to offer—I'm certainly not in the business of ruining my childhood. But the awfulness of the remake aside, the TMNT resurgence means I'm celebrating the comeback of everybody's favorite teenage reptiles. Thankfully, Todd's Kitchen has a tutorial for mutant ooze that's ...

Security is a priority for many when they first set up their mobile devices. Nobody wants to have a stranger or nosey friend go through their phone and discover risqué photos or embarrassing text messages. These days, the closet is gone—everyone keeps their skeletons in their phones.

Welcome back, my novice hackers! In a recent tutorial, I showed you how to use shikata_ga_nai to change the signature of a payload to evade detection by security devices (firewalls, IDS, etc.) and AV software.

Welcome back, my rookie hackers! Most often, the professional hacker is seeking protected information from the target system or network. This might be credit card numbers, personally identifiable information, or intellectual property (formulas, plans, blueprints, designs, etc.). Most of my Null Byte guides have been focused on getting into the system, but this only begs the question—"what do I do when I get there?"
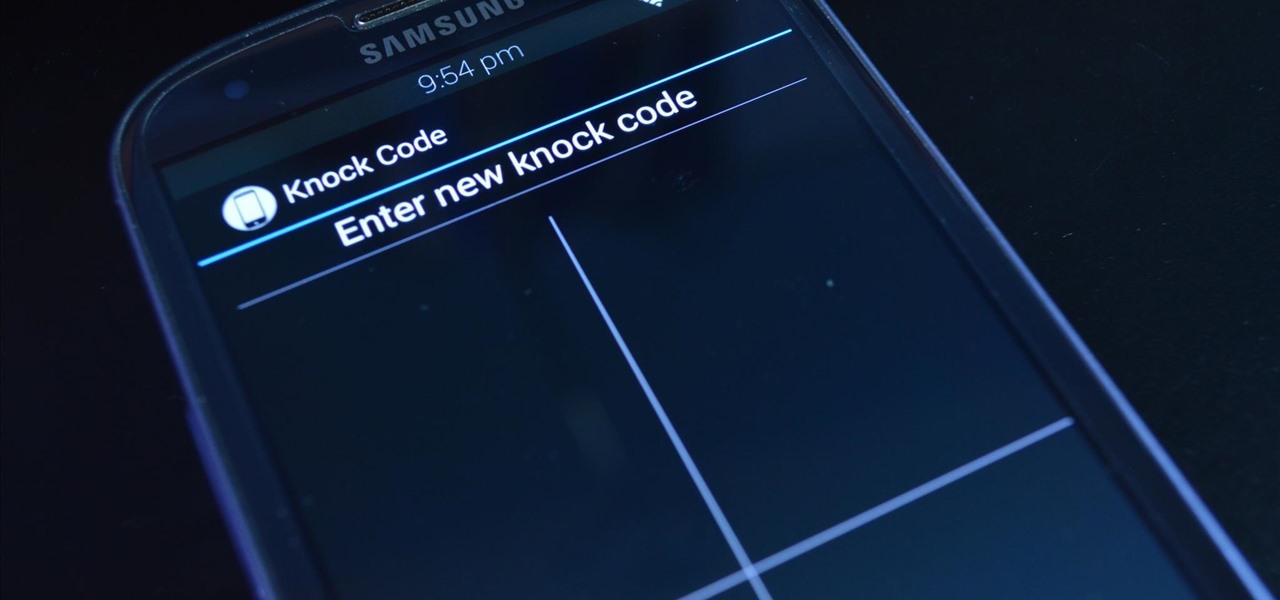
LG's arsenal of screen-off and screen-on tap gestures recently expanded into lock screen territory. Dubbed "Knock Code", this feature allows owners of various LG phones, like the G2 and upcoming G3 to unlock their phone with a series of taps on the screen. The most impressive part is that the screen doesn't even need to be on!

Once you unlock your bootloader and root, you're left with one more hurdle to overcome, and that's getting S-Off.
these techniques are little warm ups i love to use on a daily bases. it depends how my voice is feeling. singing is my passion. and if it yours, you found the right gal :)

Here are instructions to make origami bat. You will need 383 black, 47 brown, 3 white and 2 red triangles. In the video below you'll see a map.
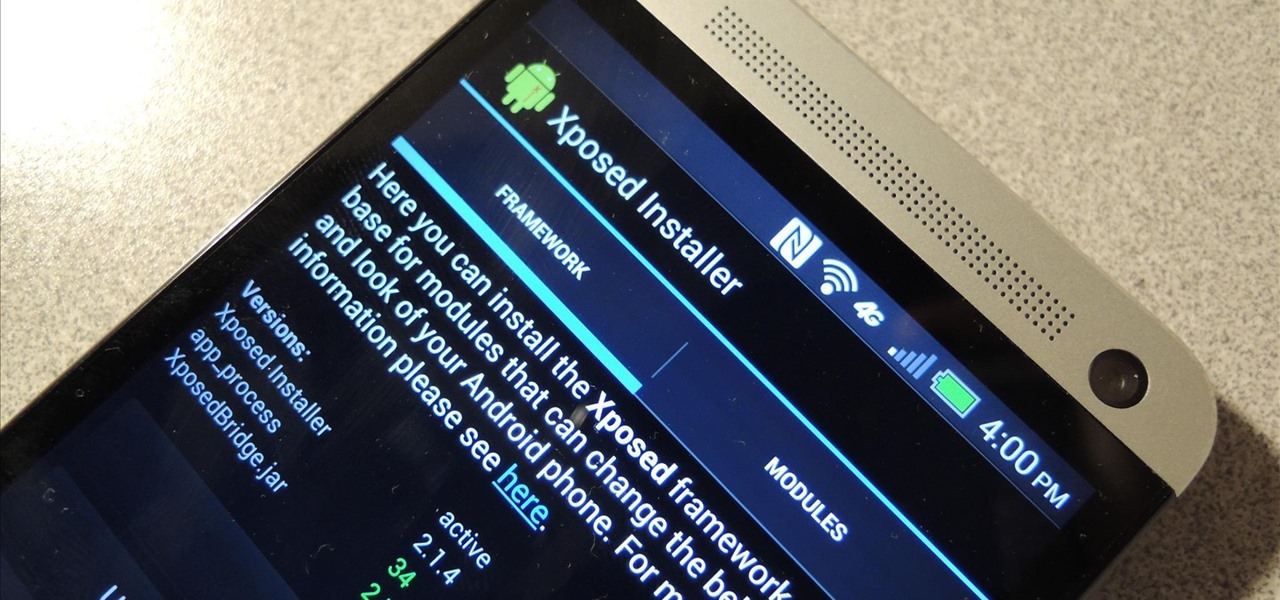
Update: The installation process for Xposed Installer is now dead simple—check out our updated guide!

Nine times out of ten, when you pick up your Samsung Galaxy Note 2, you already know what app you're going to be using. If you only have Swipe to unlock enabled, finding that app is as easy as swiping and locating the app on your Home screen or in the app drawer.
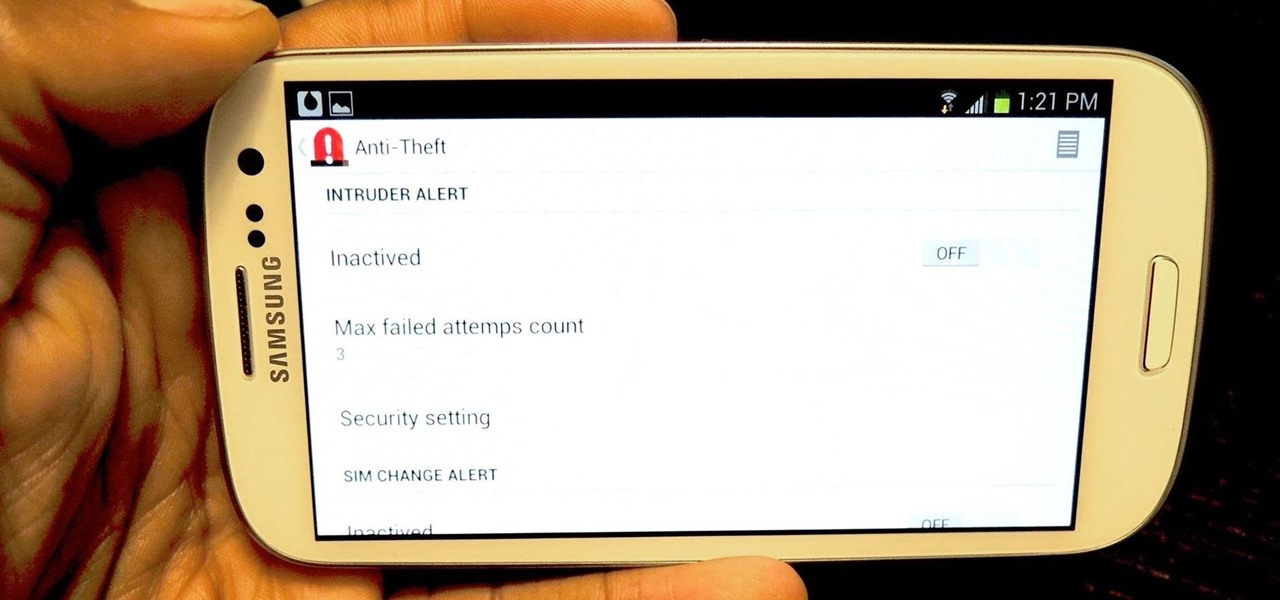
I love surprises. Surprise parties, surprise visits, surprise Patrick... But there are times when a surprise is the last thing you want, like reaching into your pocket to find that your Samsung Galaxy S3 is not where it should be.

Welcome back, my nascent Hackers! In my last blog, we looked at a passive way to gather information necessary for a hack. The advantage of using passive recon is that it's totally undetectable, meaning that the target never knows you're scouting them and you leave no tracks. The disadvantage, of course, is that it's limited to only some websites and not entirely reliable.

Welcome back, my hacker novitiates! Many of you have written me that you're having difficulty installing and running Metasploit on a variety of platforms. No matter if you're using Mac, Linux, or Windows, I strongly recommend you install BackTrack as your secondary OS, a virtaulization system, or on an external drive. This particular Linux distribution has many hacking and security tools integrated—including Metasploit.

I recently had my iPhone stolen at public park and did everything I could to locate it, but with Find My iPhone disabled (I know, what an idiot) and no exact address to give to the police, I had about a .00000001 percent chance of getting it back.

The Samsung Galaxy S4 has already received a ton of hype, as it follows one of the most successful Android phones ever—the Galaxy S3. While the phone isn't set to be available for a least another month, it does boast some pretty awesome features.

Who doesn't love a good prank? Taking advantage of unwilling and gullible bystanders is an obvious recipe for success—and some hilarious amusement.
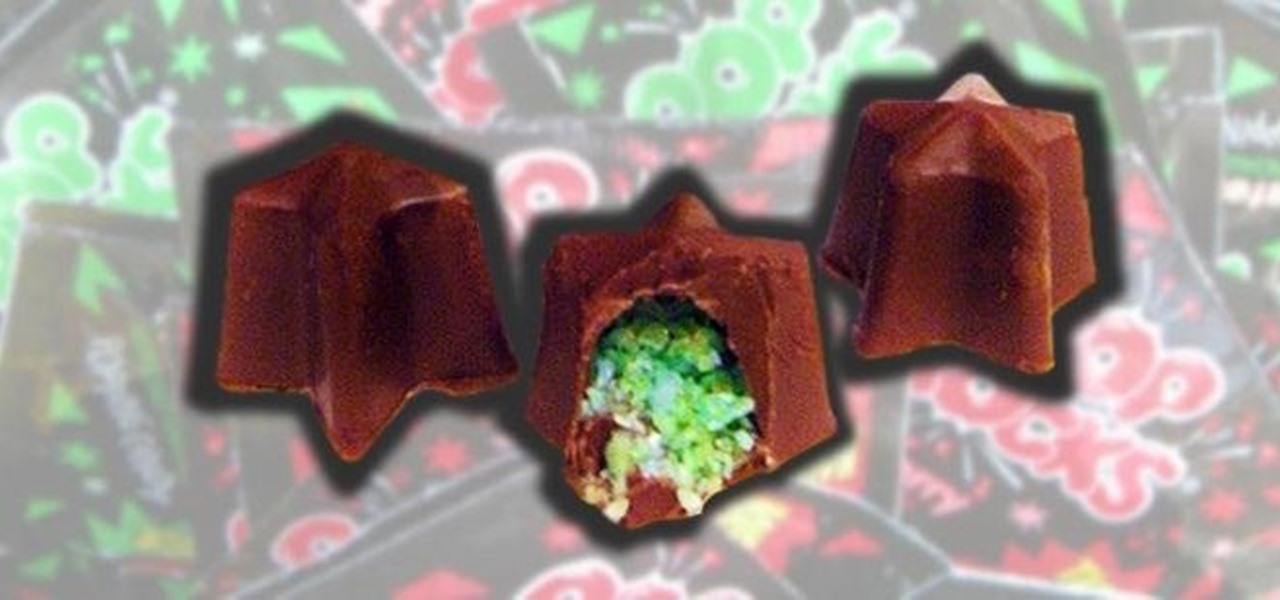
If there's anything I've ascertained from all my candy-eating, it's that Pop Rocks are singularly the most awesome candy ever. The carbon dioxide gas that's mixed with the hard sugar forms a load of tiny, 600-psi bubbles, which vigorously release when they melt in your mouth.

Everybody loves burritos. E-V-E-R-Y-B-O-D-Y.

As a multitasker, I've embraced the hustle and bustle that has filled my life. I'm constantly doing several things at a time, while looking for shortcuts to finish all of these things quicker than before. I brush my teeth with my cell phone in hand and drive to work with breakfast in mouth—I spare no time. Well, now there's an application for the Mac users among us that can help take some of the stress out of doing a thousand things at once.

So you've learned all of the dance moves to Gangnam Style and made your very own papercraft version of PSY that dances whenever you want him to. Now it's time to take your obsession a step further—by making yourself the star of the Gangnam Style music video. JibJab, the custom e-card site, has created a free tool that lets you use any photo to replace PSY's face with yours (or whoever you choose), then share the video with your friends.

Keyless entry remotes are great, but they don't always work how you want them to. One of the most common complaints is that they just don't reach far enough, and there's nothing more annoying when you can't remember where you parked. After all, what's the point of having "remote" entry if you have to be right next to the car for it to work?

You can carve a pumpkin that smokes, has an LED display, or even one with the President's face on it, but if you want your jack-o'-lantern to really stand out—make it sing the Ghostbusters theme.

One of the biggest time-consuming nuisances for any barbecue is prepping corn on the cob. If you've got a lot of mouths to feed, shucking corn is just downright painful, thanks to all of those silk strings that hide in the crevices of the kernel rows.

Outdoor lighting is an important part of your landscape. It's serves multiple purposes, but wouldn't you want to make sure you're getting the right lights, for both daytime and nighttime use? Lowe's has the answers to help you plan and install outdoor lighting in your yard.

Quickly turn a profit during a combat mission by ratting - killing NPC enemies who spawn in asteroid belts. The difficulty of rats depends on how secure your system is - the lower security, the harder the rats are to kill. This tutorial shows you the best way, as a new player, to earn money by ratting.

In order to set up a secure wireless router, you will need to use the security that is available with your wireless routing. You will need to change the default ID names and password on your computer. Try to make sure that your passwords are difficult. Also, turn on the encryption: e.g. WEP.

You don't want anybody to have access to your cell phone. Nobody. Well, instead of the standard unlock mechanism, the one anybody can unlock your cell phone with, the Motorola DROID, and Android enable mobile device, allows you to create your own unlock pattern, secret to anyone else, which wakes it from sleep mode. Best Buy has answers. The Best Buy Mobile team explains how simple it is to set up a secure lock on a Motorola DROID cell phone.
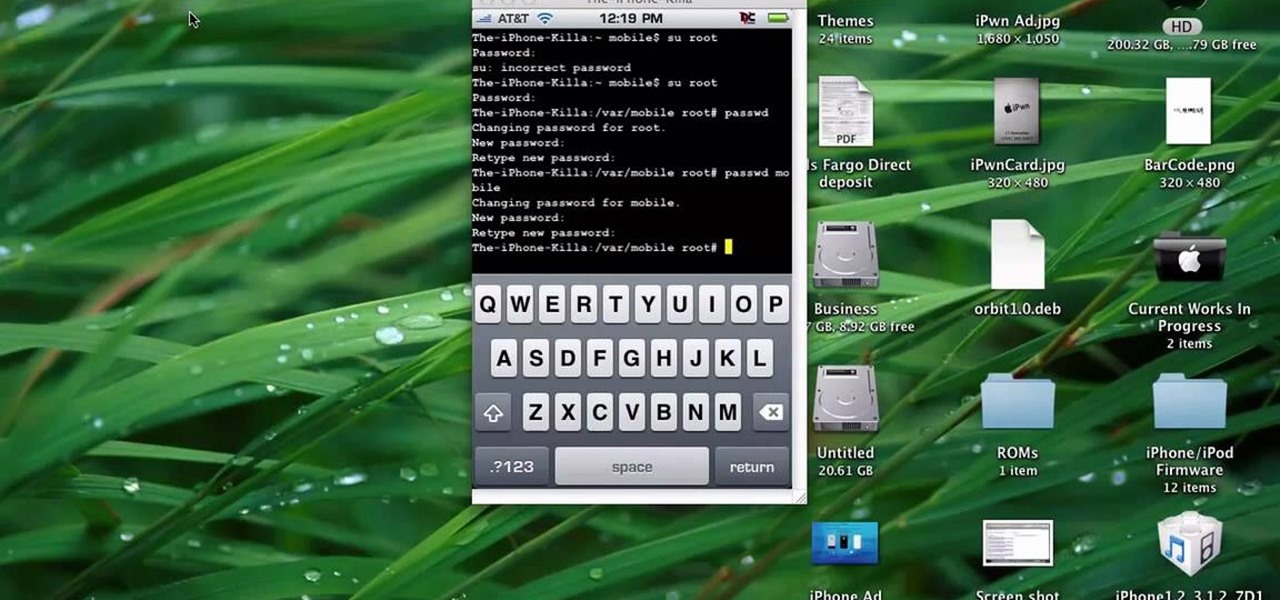
This quick tutorial runs you through a fast and easy way to make your iPhone or iPod Touch more secure. However the best security is abstinence. Just don't run the programs that leave your devices vulnerable unless you need them.
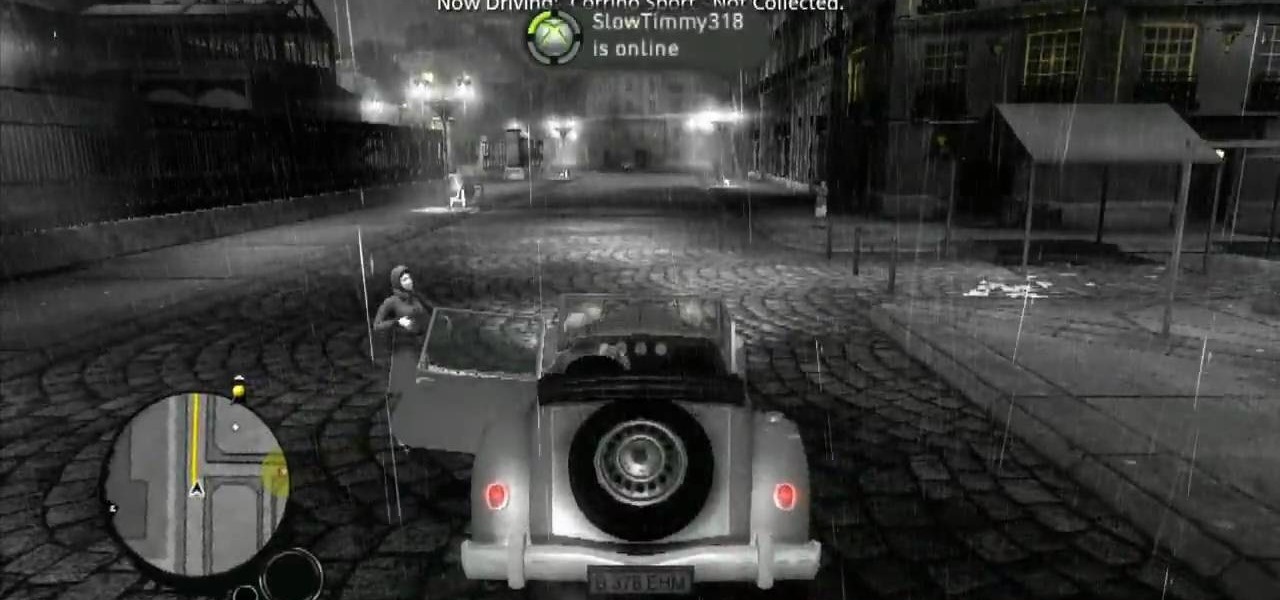
Make your way through The Saboteur for the Xbox 360. In the eighth mission in Act 1: Doppelganger, the ambassador will rendezvous with a German official near the Place des Vosges. Security will be tight around the ground level, but you should be able to find a vantage point among the rooftops. For more info, watch the whole gameplay.

So you want to party with celebrities. Whatever you do, don’t cry. You won’t just look silly—you’ll look unstable. Follow these steps to get you one step closer to hanging with the stars.
New to Windows? No problem... here's a beginner's video tutorial that will teach you how to prevent cut, paste, copy, and delete on Windows files.

Check out this 2 part walkthrough of RE 5 Chapter 2-3 Savanna. This Resident Evil 5 Walkthrough is being played on Veterans Difficulty in Co-Op mode with Chris Redfield being played by Reule and Sheva Alomar being played by RavenVanHelsing.

Resident Evil 5 (RE 5) is the sequel to 2005's Resident Evil 4. This game guide shows you BSAA emblem locations, treasures, and includes strategies for all 6 missions and boss fights.
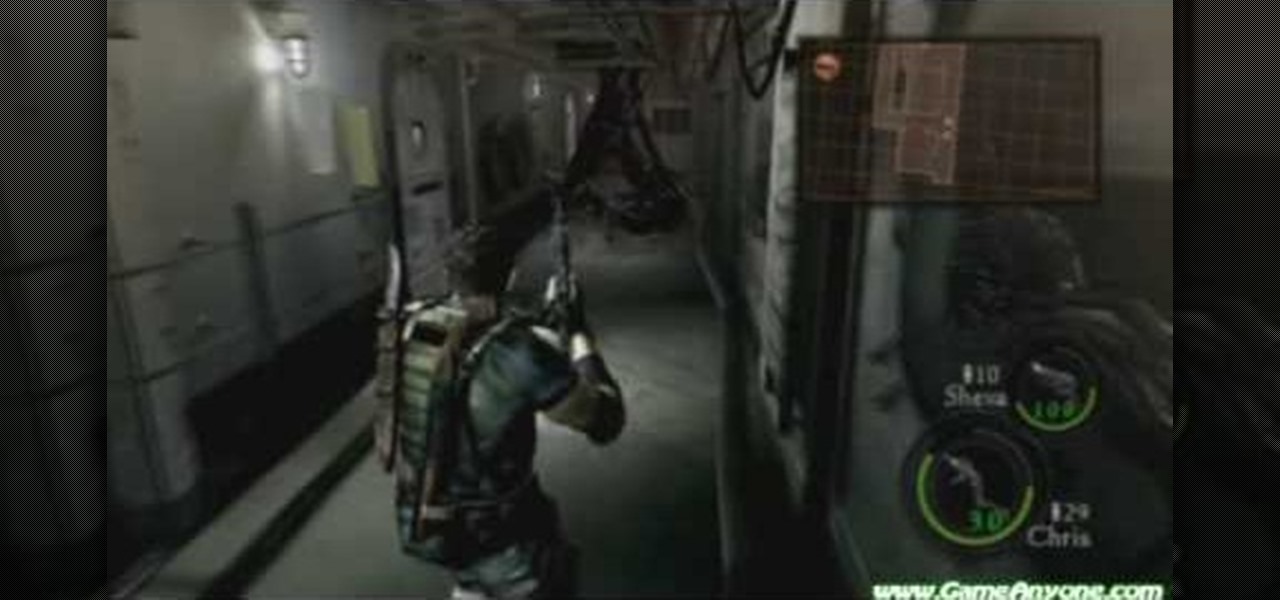
Check out this walkthrough of Residential Evil 5, Chapter 6-2: Main Deck. Resident Evil 5 (RE 5) is the sequel to 2005's Resident Evil 4. This game guide shows you BSAA emblem locations, treasures, and includes strategies for all 6 missions and boss fights.

Last weekend, some unlucky Gmail users inadvertently had their email accounts wiped out. Actually, it was 0.02 percent of all Gmail users—or roughly 40,000 of the 200 million who use the email service, due to an "unexpected bug" which affected copies of the data. Gmail does make backup files of everything, so eventually everyone will reclaim their email history. In fact, as of yesterday, Google has successfully restored all information from their backup tapes and has started returning everyon...

Breaking into a low-security lock is easy (and thus, why it's the subject of a googolplex number of Youtube tutorials made by mischievous prepubescent boys). But add a combination number to a lock and your lock-picking life gets much harder.