Arguably Chromecast's biggest feature since its launch, screen mirroring functionality started rolling out to select devices earlier this week, and in a word, it's awesome.
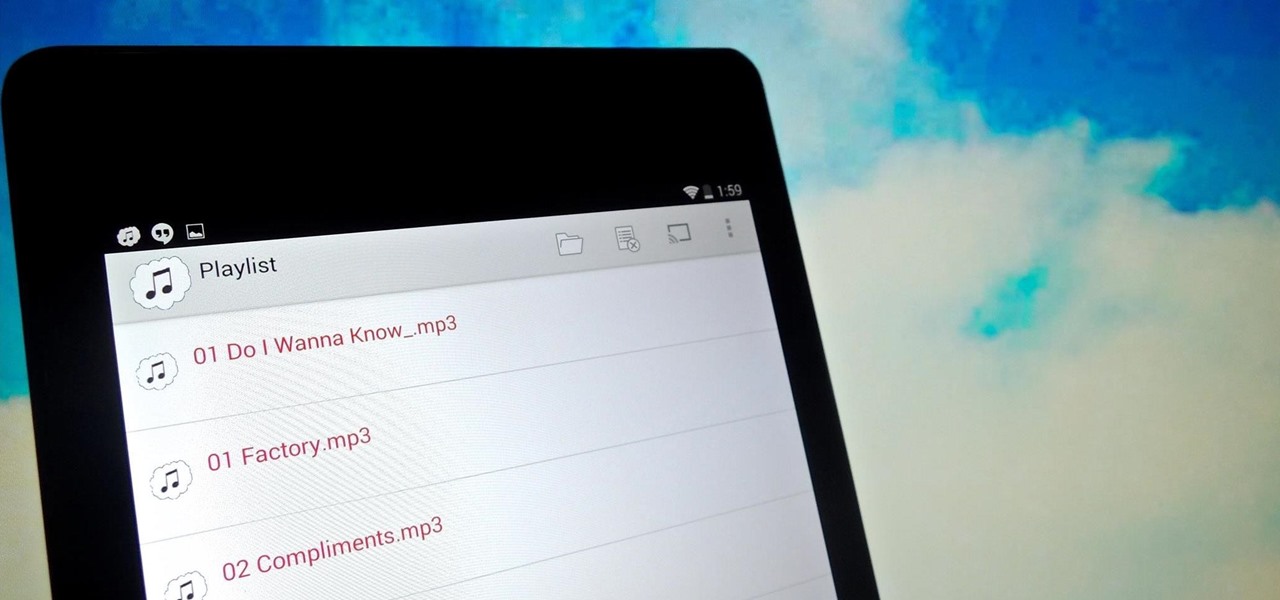
There is no SD card support on the Nexus 7, so managing internal storage can be tricky. There are ways to free up space, but the biggest space hog on my tablet is music, and that's not something I'm willing to delete just yet.

In February of this year, the Higher Court of Berlin ruled that Facebook must follow strict German data protection laws, which Facebook's terms of services and privacy policies circumvent.
When browsing the web, you may not be quite as anonymous as you think, especially if you are using public WiFi. The easiest way to stay as anonymous and safe as you are going to get, is to use a VPN (there are a number of great free ones). In this tutorial, we will show you how to set up a VPN on Android, and how this protects you.
In a era where cyber security is becoming increasingly important, Comcast has decided to use its customers' routers to provide hotspot access to the public. A new program, outlined by Dwight Silverman over on the Houston Chronicle website, seeks to provide Xfinity customers with city-wide Wi-Fi hotspots by using, well...other customers' wireless routers.

Netflix releases monthly reports on major ISPs relating to how well their service works on each provider. The purpose is to educate the public on their choice of service provider, but since many of us hardly have any choice at all when is comes to an ISP, it backhandedly works to shame them (if they're even capable of feeling shame under all those millions of dollars).

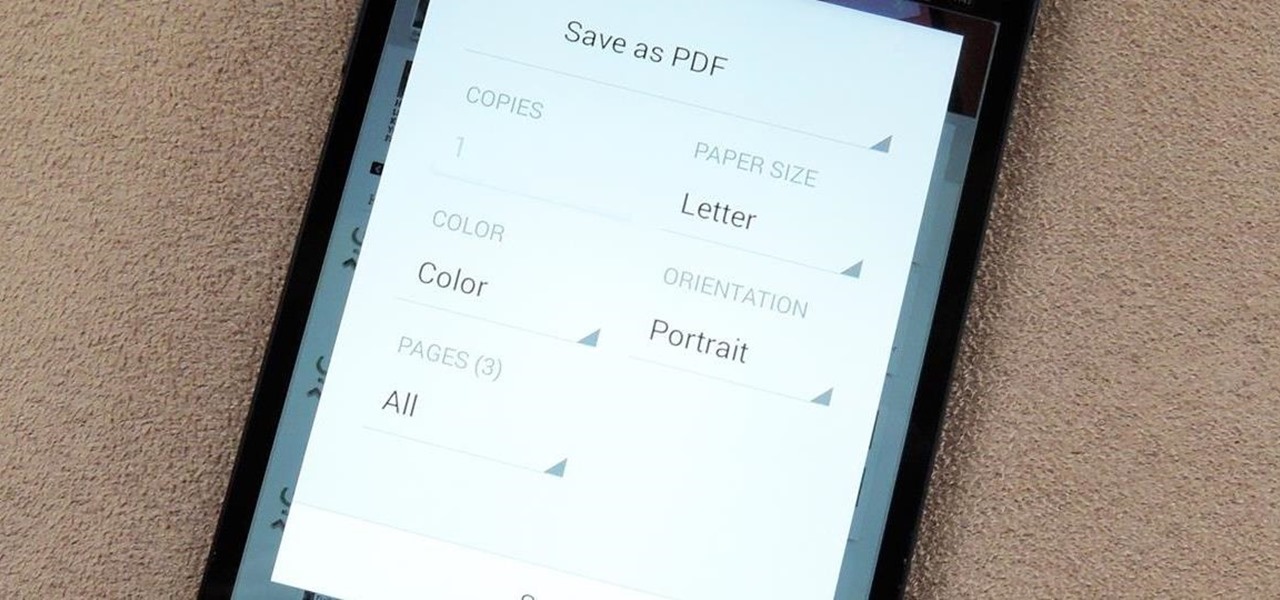
You may not always be connected to the internet, but if you're anything like me, your thirst for web content is insatiable. Whether you're on an airplane or stuck in an area with no reception, having some offline content stored on your Nexus can definitely save the day.

Log in to your LinkedIn profile, and you'll immediately be prompted to check out who's peeked at your profile. With one click, you can discover how many recruiters, companies, and random people have viewed your online resume.

"Millions of us have smartphones with the power to speed up research that will benefit billions of people around the world." - Professor Francois Grey

Unless you've been living under a rock with no internet connection, it's safe to say that you've heard of the Heartbleed flaw that allows practically anyone with the right knowledge to steal your personal information, such as passwords, credit card numbers, and e-mail addresses using OpenSSL.

It appears that the next iteration of KitKat, Android 4.4.3, is fast approaching. If the past is any indication, today's update to the Nexus 5 software changelog on Sprint's website tells us a new version of Android will begin rolling out within 24 hours. Sprint has broken the news of a forthcoming Android release twice in the past. With 4.4.1 and 4.4.2, a mini-changelog was posted on the Sprint website about a day before Google began pushing updates to its Nexus devices.

If you lend someone your phone, even if it's just for a second, there's a chance they can enter an app and see something you'd rather they didn't. Whether it's a personal email or a private photo, there are plenty of reasons why you'd want to keep snoops out of certain apps.

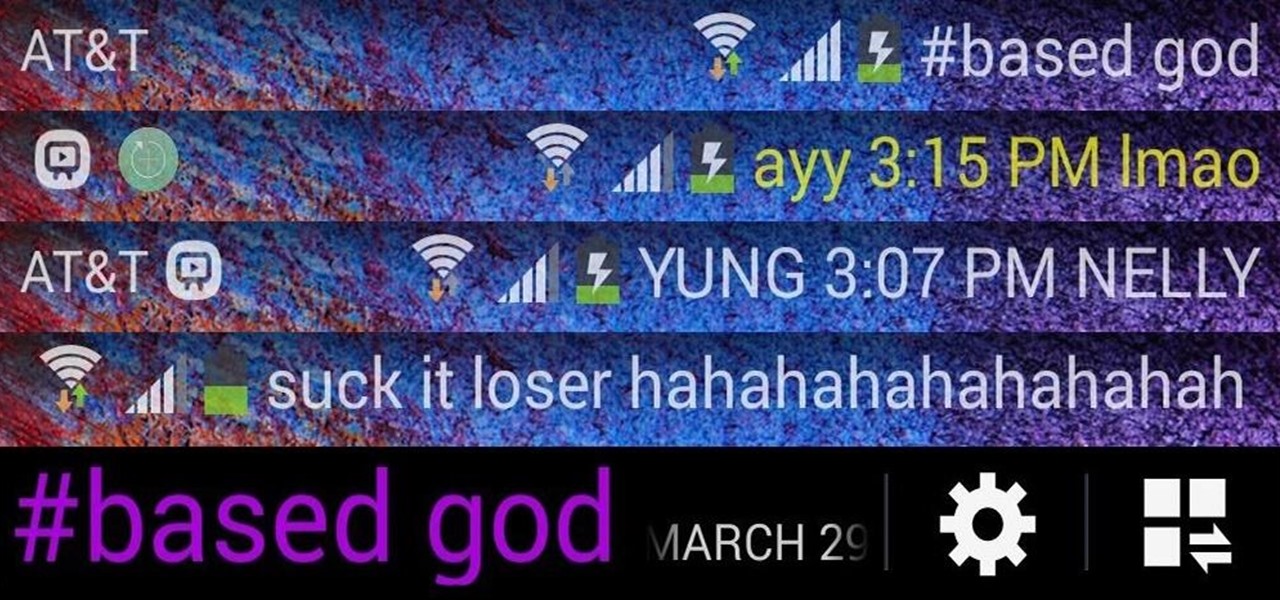
I love my status bar. Not only does it tell what time it is and how much battery juice is left, but it gives me cellular connection info, text alerts, and app update notifications. However, one thing is does not give me is customization. Since you're looking at it all the damn time, why not personalize it?

Google Glass is all about transforming the world around us with little to zero interaction from the wearer. Much of this is done using augmented reality—a live view of physical, real-world environments that are augmented by computer-generated input in the form of graphics, sights, and sounds.

Imagine that Tinder fornicated with Facebook and had a baby. The product of that union would be the hideous, yet overwhelmingly interesting SocialRadar, an app dedicated to stalkers and stalkees.

If you've never played Cards Against Humanity, it's time to get initiated. Originally funded through Kickstarter, the free to download card game is basically an obscene version of Apples to Apples.

The newest version of Android, 4.4.2 KitKat, is making its way onto AT&T Samsung Galaxy S4s right now. Itching to try out the latest that Google has to offer? Keep an eye on your status bar for a notification letting you know that a system update is ready.

Last week, Apple issued an iOS 7.0.6 update that fixed a serious security vulnerability that could allow hackers to steal passwords, read emails, and get info from other SSL-encrypted communications.

Pretty soon, every restaurant and store you walk into will know exactly what you're doing. Retail analytics companies like Euclid, ShopperTrak, RetailNext, and Prism Skylabs have penetrated hundreds of food shops and retail stores across the country, installing sensors that track and log customers' moves while they dine and shop.

Welcome back, my budding hackers! In my continuing effort to build your basic Linux skills for hacking, I want to show you how to build a secure "tunnel" to MySQL.

The @DesignGears guys have been busy today, leaking an unofficial KitKat build (Android version 4.4.2) for the AT&T Samsung Galaxy Note 3. The latest is a peek into what the international variants are beginning to see, although this build is far from official. Still, if you want to give it a shot, I'll show you how to install it, but make sure to check out the details below the how-to to see what you can expect, good or bad.

Ever since its introduction back in iOS 6, AirPlay has been helping us iOS and Mac users stream content over to an Apple TV or third-party speaker system. It's an incredibly useful feature. However, it's also severely limiting. The few compatible products out there are extremely expensive, making wireless streaming a not-so-easy task.

Welcome back, my hacker apprentices! I recently began a new series on digital forensics to show aspiring hackers what the forensic investigator can do and see while investigating a cyber attack. This is the second installment in that series and will focus upon network forensics. In other words, what can a network forensic investigator learn about the attacker during an investigation and how.

This last weekend, Apple released the second beta of iOS 7.1 for iPad, iPhone, and iPod touch, and I've got a firsthand look of what's to come in iOS 7.1—the first major update since iOS 7 was released.

No matter how much of a gamer you are, typing with your PS4 controller is a bitch. Let's just be real. Having to move left, then right, then down, for every single letter can make writing a message very time consuming; so much so that I usually avoid messaging altogether.

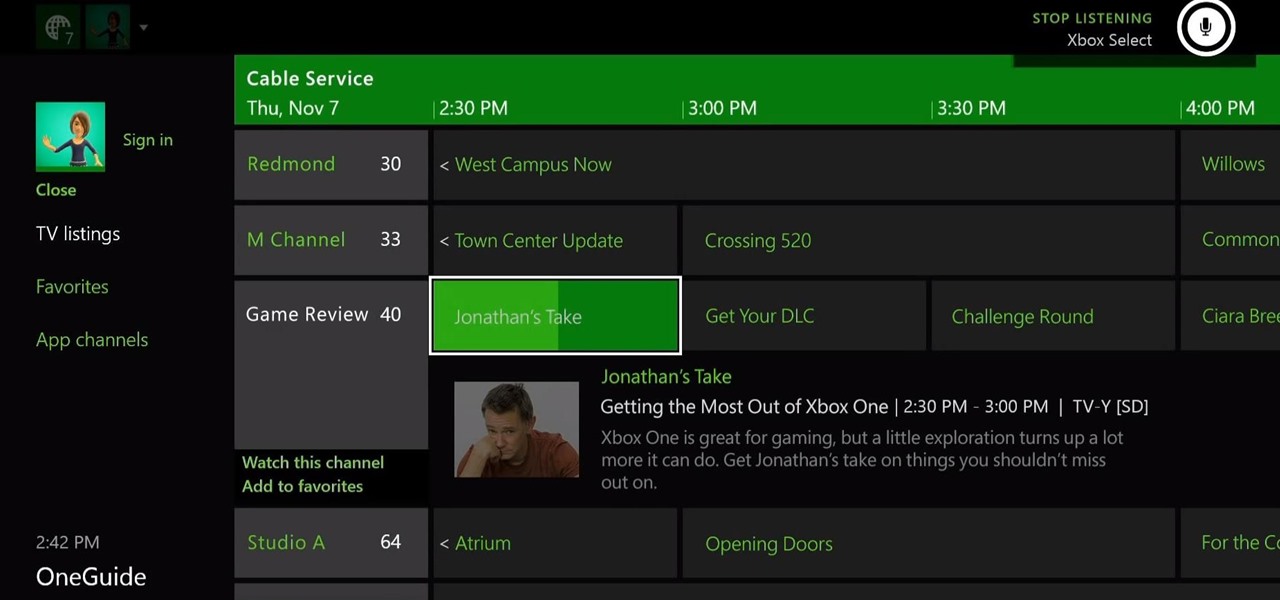
The Xbox One is the quintessential jack of all trades. It can be your browser, music player, gaming system, and cable box, but in order to benefit from all of these goodies, you're going to have to set it all up.

The infamous Red Ring of Death plagued the Xbox 360 for years, leading people like me over to the PlayStation 3 console. Now it looks like Sony and its new PlayStation 4 are running into the same problems as Microsoft did.

It seems nowadays the word "easy" has taken on an alternate meaning. When I see "easy," I expect a quick and painless process, but when it comes to flashing or installing a custom ROM, easy means anything but.

If you are willing to teach online, you might have thought of making online courses. But if you found it too hard, you can start with micro-courses, that can be created in 10 to 30 minutes. Step 1: Define 5-7 Main Points That You Will Cover in Separate Lessons.

The high limit thermostat can be found in gas and electric dryers and serves as a safety feature that helps to prevent the dryer from becoming too hot when it’s running. The thermostat is designed to shut off power to the dryer’s heater when the dryer vent is blocked or clogged. The high limit thermostat on your dryer is something that does need to be replaced from time to time. Fortunately, it is a job that you can do on your own with basic tools.

Welcome back, my budding hackers! Previous to this tutorial, we've focused mostly on hacking the target system. If we're successful in owning the target system, we'll then want to make certain that the system administrator doesn't know we were there, and that he or she cannot track us.

While the PlayStation 3 is an awesome gaming console and the iPhone is an awesome smartphone, Apple and Sony have made two devices (that could be perfect for each other) nearly incompatible. Truth be told, this is more Apple's fault than Sony's, but we'll get into that later.

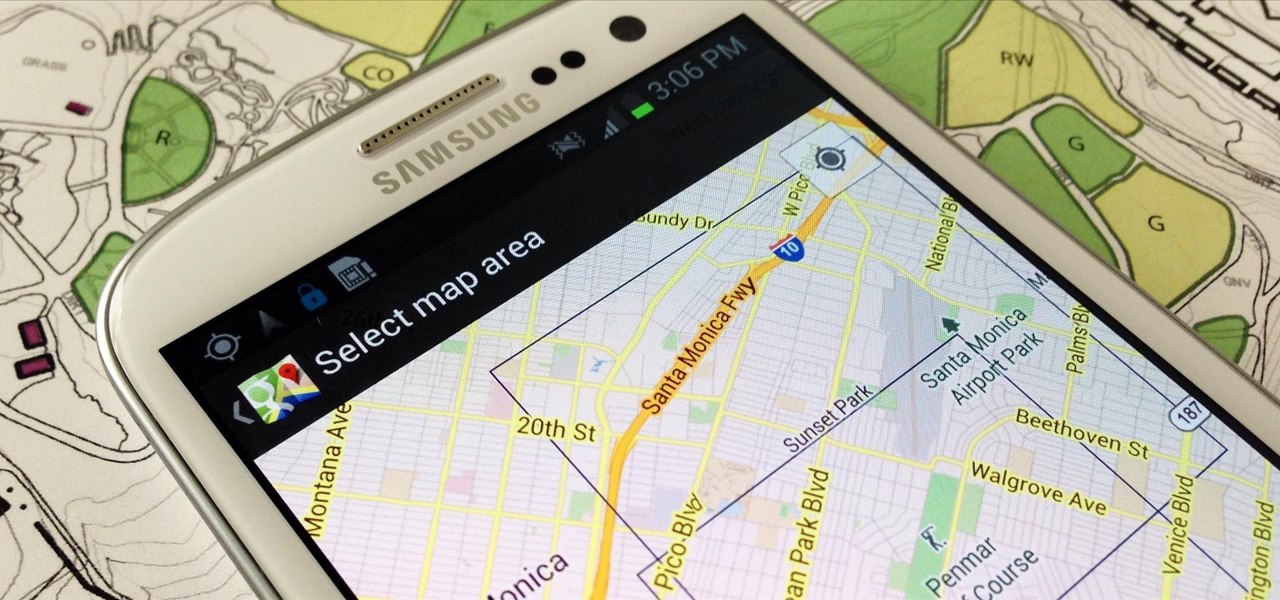
When you have to take four different freeways to go twelve miles, Google Maps becomes a very close and dear friend—especially in Los Angeles. Without my trusty Samsung Galaxy S3, I seriously don't know if I could make it back home half of the time. Of course, you'd probably get better directions using a Garmin, TomTom, or other GPS device, but when you already have a smartphone like the GS3, dedicated GPS units become nothing more than a luxury item.

A deck of cards may be a magician's best way to demonstrate his or her's sleight of hand, but for the prankster, it's the perfect way to deliver a shocking 300 volts of electricity! And that's exactly what I'm going to show you how to do today. Stuart Edge used it in his "Electric Shock Kissing Prank" to show the ladies how a man can really put the sparks in a kiss.

Welcome back, my nascent Hackers! In my last blog, we looked at a passive way to gather information necessary for a hack. The advantage of using passive recon is that it's totally undetectable, meaning that the target never knows you're scouting them and you leave no tracks. The disadvantage, of course, is that it's limited to only some websites and not entirely reliable.

I've had the thankless duty of choosing the music for far too many get-togethers, and no matter how good you think your music taste is, or how many new tracks you have on your iPhone or iPod, you will never—ever—satisfy everyone.

Samsung just concluded their live unveiling of the Samsung Galaxy S4! A more in-depth look can be found here.

Welcome back , my fledgling hackers! Lately, I've been focusing more on client-side hacks. While web servers, database servers, and file servers have garnered increased protection, the client-side remains extremely vulnerable, and there is much to teach. This time, we'll look at inserting a listener (rootkit) inside a PDF file, exploiting a vulnerability in Adobe's Reader.

The PlayStation 3 is a sweet gaming system, and even though Blu-ray discs didn't really live up to all the hype and there is still no HBO GO app available, I love my PS3. One of the coolest things about it is that you can customize it to look however you want. One of the most common ways to do this is by changing the wallpaper, but most people use their computers to transfer wallpaper images over.

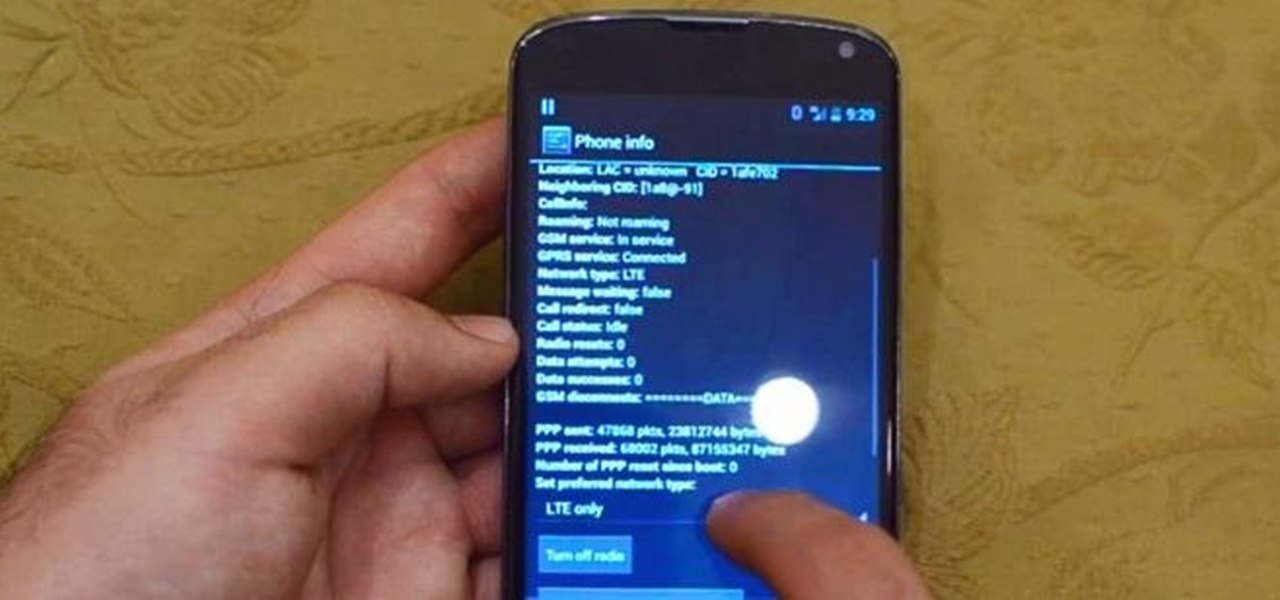
When the specs for Google's Nexus 4 came out, most critics were more than thrilled. A very fast processor, lots of RAM, a big display with very high resolution, and an 8MP camera made it the media darling of the smartphone world. It climbed the ranks of the best smartphones available, but couldn't quite reach to the top due to one reason—no 4G LTE. Samsung's Galaxy S III and Apple's iPhone 5 both come with 4G LTE, so why couldn't the LG Nexus 4? While there are many reasons, Google was stated...