In this video series, watch as professional violinist Jason Salmon teaches you how to play scales on a violin in G minor. Improve your music theory and violin playing technique with the help of these instructional videos.

In this tutorial video, learn how to get started using the Akai MPC 4000 drum machine. Our expert music producer will give you a tour of the basic interface for the MPC, and then show you how to load, chop, and slice samples, layer a beat, use the sequencer, and create a basic hip-hop beat of your own.

In these jazz piano lessons on video, pianist Ryan Larson teaches us not only how to improve our freestyle technique, but also how to read and write music—since you are only able to improvise with what you know.

In this instructional video series, our expert will show you the basics of Afro-Cuban dance by teaching basic steps, giving pointers on special moves and techniques as well as history on the origins of Afro-Cuban dance and the music and musical instruments that accompany it.

In this instructional online video dance lesson, our dance instructors will show you how to do some of the most basic and impressive moves associated with Disco and 70's music culture.

Aerobic exercise routines can take many forms. Aerobic dancing is an exercise program that combines elements of dance with traditional aerobic steps and techniques, strength training, and stretching, all set to upbeat music.

In these advanced guitar lessons on video, learn how to develop your skills even further. Our expert will show you how to play guitar in the seven modes, or interval frameworks, of diatonic music (in the key of A).

In this video series of music lessons, learn how to play the Baroque lute from professional musician Foti Lycourdis. Foti will teach you about the history of the lute and what exactly is a Baroque lute.

Our expert, Hope Wells, shows you some basic ideas for teaching music to children. Using a piano, Hope teaches basic beats, reading notes, and staffs.

In this video series of music lessons, learn how to play the trombone from trombone expert JD Keating. JD will teach you about the parts of the trombone such as the slide and the positions of the slide.

In these Halloween costume videos, learn how to dress up like the man who sold the world a new identity every ten years or so. Whatever music, fashion, or art decade you decide to portray Bowie in, things should all be hunky dory.

In this series of kitsch avante garde instructional music and space sounds videos, our theremin expert explains the basic principles of this bizarre instrument. He also tells you how to operate the controls and even demonstrates how to coax a song out of it. Join Brain Wilson, John Spencer and any number of science fiction soundtrack composers on the evergrowing bandwagon of theremin disciples.

This video clip series will cover everything you will need to know about getting started improvising on the Native American flute. Not only will our very experienced expert show you some important improvising techniques such as vibrato and bending notes but you will also learn about the importance of using nature as an inspirational tool to help you create better music. Take these tips and start having fun with your new talent!

Play dobro slide acoustic guitar. Ed Dowling, author of Understanding Open Tunings has been playing guitar in open tunings for 39 years. He builds his own guitars and has released five albums of slide and bluegrass music.

In these music lessons on video with Bill Macpherson, learn what equipment you need to sound like a blues guitar hero. Get tips on what amplifiers to play through, and what electric guitars work best for that smooth, warm signature blues guitar tone. Find out what amp settings work well for drive and reverb, and learn what an effects pedal might offer you for a grittier, more distorted sound. Watch these videos and learn how to continue one of the richest living musical traditions we have today.

Make instruments out of household items. Annie Brunson has a degree in Music and Theater from Bretton Hall and has taught piano, oboe, and middle school band. Here she shows us craft projects on making percussion instruments.

In this tutorial video, learn how to get started using the Akai MPC 2000XL drum machine. Our expert music producer, Amir Tauheed, will give you a tour of the basic interface for the MPC, and then show you how to load, chop, and slice samples, layer a beat, use the sequencer, and create a basic hip-hop beat of your own.

Hashes are commonly used to store sensitive information like credentials to avoid storing them in plaintext. With tools like Hashcat, it's possible to crack these hashes, but only if we know the algorithm used to generate the hash. Using a tool called hash-identifier, we can easily fingerprint any hashes to discover the right Hashcat mode to use to retrieve a password.

Passwords on Windows are stored as hashes, and sometimes they can be tough to crack. In certain situations, though, we can get around that by using the hash as is, with no need to know the plaintext password. It's especially interesting if we can manage to get the hash of an administrative user since we can then authenticate with higher privileges by performing an attack known as pass the hash.

For those with small hands, smartphones have gotten out of control as of late. Nearly every flagship phone is over six inches in length, so many are forced to use phones that are too big for them and hope they don't fall. Well, thanks to one developer, using these phones can be a lot easier.

KeePassX, 1Password, and LastPass are effective against keyloggers, phishing, and database breaches, but passwords managers rely on the operating system's clipboard to securely move credentials from the password vault to the web browser. It's within these few seconds that an attacker can dump the clipboard contents and exfiltrate passwords.

Apple's scheduled to show off the first look of iOS 13 at WWDC 2019 on June 3, but what will the new operating system hold for iPhone? Rumors suggest that many features initially planned for iOS 12 will show up in iOS 13, codenamed "Yukon," and dark mode will be the big ticket item this year.

Gathering information on an online target can be a time-consuming activity, especially if you only need specific pieces of information about a target with a lot of subdomains. We can use a web crawler designed for OSINT called Photon to do the heavy lifting, sifting through URLs on our behalf to retrieve information of value to a hacker.

When it comes to rooting and modding any Android device, ADB and Fastboot commands will quickly become your two new best friends once you realize the power they have. From unlocking your bootloader to flashing any file you could ever want — if you're serious about the modding and customization game, you'll want to become acquainted with these commands as soon as possible.

To borrow from the canon of Game of Thrones, what is dead may never die. And while the Meta Company that we knew this time last year is no more, the patent infringement lawsuit filed against the company lives on.

When someone sends you a funny video, image, tweet, what have you, often the first thing you want to do is share it with someone else. Instead of copying the link and jumping over to another chat to do so, WhatsApp makes it easy to share content right from the thread you received it in, via the forward feature.

During Huawei's P30 smartphone launch event on Tuesday, the China-based company unveiled a surprise addition to its line-up: smartglasses.

Microsoft Office files can be password-protected in order to prevent tampering and ensure data integrity. But password-protected documents from earlier versions of Office are susceptible to having their hashes extracted with a simple program called office2john. Those extracted hashes can then be cracked using John the Ripper and Hashcat.

Android 9.0 Pie moved the status bar clock from the right corner to the left to accommodate phones with notches, but there's one major downside for Samsung users: since no Galaxy phones have a notch, all this did was take away space for the notification icons that would otherwise start from the left corner.

The tactic of brute-forcing a login, i.e., trying many passwords very quickly until the correct one is discovered, can be easy for services like SSH or Telnet. For something like a website login page, we must identify different elements of the page first. Thanks to a Python tool for brute-forcing websites called Hatch, this process has been simplified to the point that even a beginner can try it.

Stories are everywhere in social media today, but that wasn't always the case. In 2013, Snapchat introduced the world to these temporary windows into our daily lives. Since then, stories have infiltrated other popular apps. However, to stand out, you can't solely rely on the app where the story will be posted. Instead, you need a suite of apps that can turn your story into something special.

On the surface, Instagram is pretty intuitive, so you might think that you already know everything there is to know about using it on your iPhone or Android phone. But this photo and video-sharing app is constantly adding new features, some of which don't make the press releases. Even if you're an Instagram guru, chances are you've missed one of these hidden goodies.

Publicly, things have been pretty quiet over at Meta, the augmented reality headset and software startup based in Silicon Valley. But that doesn't mean that the company doesn't have a few strong opinions about the state of AR in 2018.

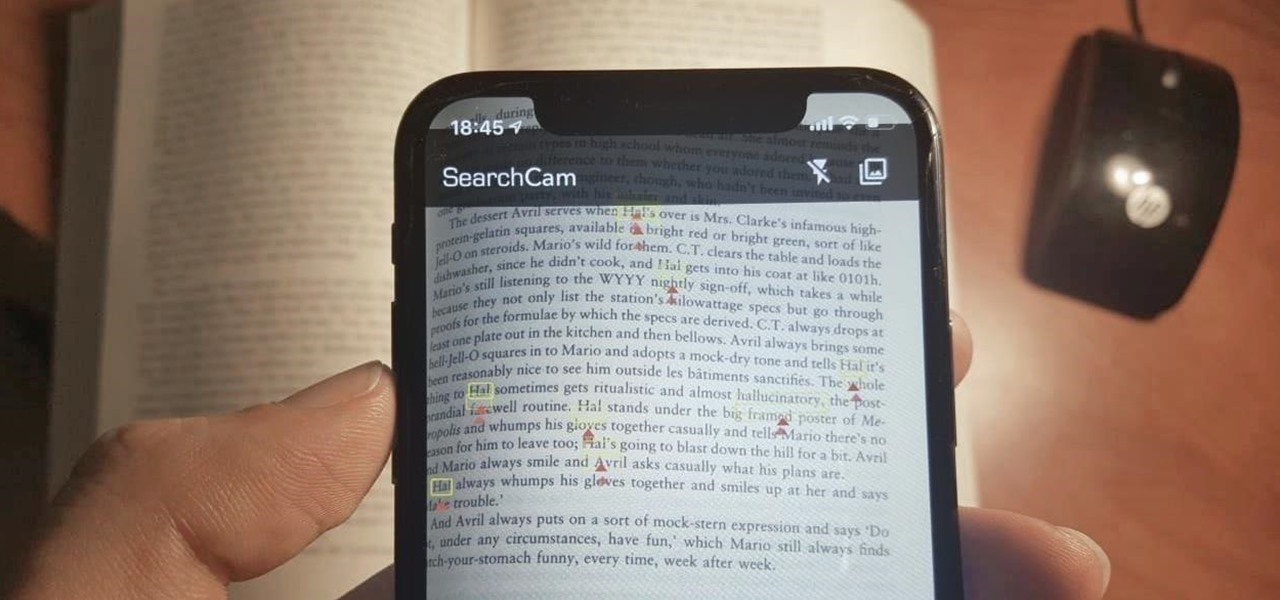
Safari has a convenient "Find" feature to search for specific words and phrases in a webpage, and Apple Books has a similar feature for e-books and PDFs. But those do nothing for you when searching text in the real world. Hardcover and paperback books are still very much a thing, as well as paper-based documents, and finding what you need is as simple as pointing your iPhone's camera at the page.

Cross-site scripting is one of the most common vulnerabilities found on the web today, with repercussions of this type of flaw ranging from harmless defacement to sensitive data exposure. Probing for XSS can be tedious and time-consuming for an attacker, but luckily there are tools available to make things a little easier, including Burp Suite, Wfuzz, and XSStrike.

Before you can dive into customizing your OnePlus 6T, you must take the initial step of unlocking the bootloader to gain the ability to install TWRP, Magisk, custom ROMs, and other mods.

The main draw for Google's Pixel series is the software. It rocks a clean version of stock Android instead of a heavy OEM skin like TouchWiz, it gets frequent prompt OS updates, the camera software is downright amazing, and it has perhaps the most fluid UI of any phone. But an understated advantage of the software is how dead-simple it is to modify with root-level tweaks.

The dream of Google Glass lives on via North's stylish and normal-looking smartglasses that bring text messages and navigation prompts into the user's field of view and Amazon Alexa integration for voice-activated assistance.

So, you rooted your Pixel 2 or 2 XL and everything seems to be working quite well. However, a month passes, and you get a notification to install the monthly security update. Like clockwork, Google has been pushing out OTA security patches every single month for a while, but there is a new problem for you at this point — as a rooted user, you are unable to apply the update correctly.

Your iPhone comes packed with a long list of excellent text tones to choose from. Bamboo anyone? Of course, for some of us, stock sounds from 2013 don't cut it anymore. We want customizability, something that's found more on Android than iOS. However, you can add your very own text tones to your iPhone right now, so long as you have a sound file in mind and a computer running iTunes.