
SPLOIT: Building Android Applications for Hackers : Part 1 : Introduction to Android.
Greetings my fellow aspiring hackers,


Greetings my fellow aspiring hackers,

Amazon is slowly trying to gain as much influence in the tech world as it has in the consumer market, and with the Amazon Fire HD 7, they have their eyes set on taking on the "budget tablet" space.

Recently, I've been experimenting with BeEF (Browser Exploitation Framework), and to say the least, I'm hooked. When using BeEF, you must "hook" the victims browser. This means that you must run the script provided by BeEF, which is titled "hook.js", in the victims browser. Once you've done that, you can run commands against the victims browser and cause all kinds of mayhem. Among these commands, there is an option to use the victims webcam. This is what we'll be doing here today, so, let's g...

Hello all! In this tutorial, I'd like to show you one way of getting root on OS X. Check out this GitHub page for a recent privilege escalation exploit that was recently discovered. I've tested it and it works on both OS X 10.9 Mavericks and OS X 10.10 Yosemite, but appears to have been patched with OS X 10.11 El Capitan. If you check out the file main.m you can see where most of the magic is happening. This source code can very easily be changed to make it do more than just the system("/bin/...

Hello all, this is my first submission to null byte! I noticed something a little strange, particularly that whenever Meterpreter is discussed, it is virtually always in the context of Windows. Granted, the Windows Meterpreter is more powerful than the version that can run on OS X (it has several more commands/options), but I think it is still worth noting how to do it. I've even seen some people mistakenly say that Meterpreter can only be run on Windows, which is not true. Meterpreter can ea...

In this day and age, maintaining your privacy is a perpetual battle, and doing so with an internet-connected device like your smartphone is even more of a struggle. Every website you visit, every app you install, every message you send, and every call you make is a potential vulnerability that could expose you to prying eyes.

Mobile payment systems have been around for almost 5 years now, starting with Google Wallet. But when Apple got into the game last year with their new Apple Pay service, things really started to take off. Around this time, Samsung responded by acquiring an up-and-coming mobile payments company that owned the rights to an incredibly innovative technology called Magnetic Secure Transmission (MST).

It seems like whenever someone sees my phone, they ask me two questions right off the bat; "What phone is that?" and "How did you get your Android to look like that?"

Developing GUI apps in python is really cool. I ask those who understand the language to help convert some of the command-line or console programs or apps ( I mean programs that are useful to a hacker ) to GUI. I know GUI makes us lazy and not wanna learn but we should all know its fast. Today's tutorial is on p2p chat app I developed last week and decided to share it with the community since its kinda cool.

Welcome back, my greenhorn hackers! As hackers, we often take for granted that nearly all of our hacking tools and operating system are free and open source. I think it's important to examine a bit of background on how we arrived at this intriguing juncture in the history of computer software. After all, we pay for nearly all of our other software (Microsoft, Adobe, etc.) and nearly everything else we use in life, so how is it that Linux and all our hacking tools are free?

When you think of an online music service nowadays, Spotify is probably near the first that come to mind, and for good reason. Being able to create, share, and take all of your playlists anywhere, across all of your devices, is something that I couldn't live without. Unfortunately, nothing this good is free, and with Spotify Premium, users of their free service are left with very limited features when streaming on their mobile devices.

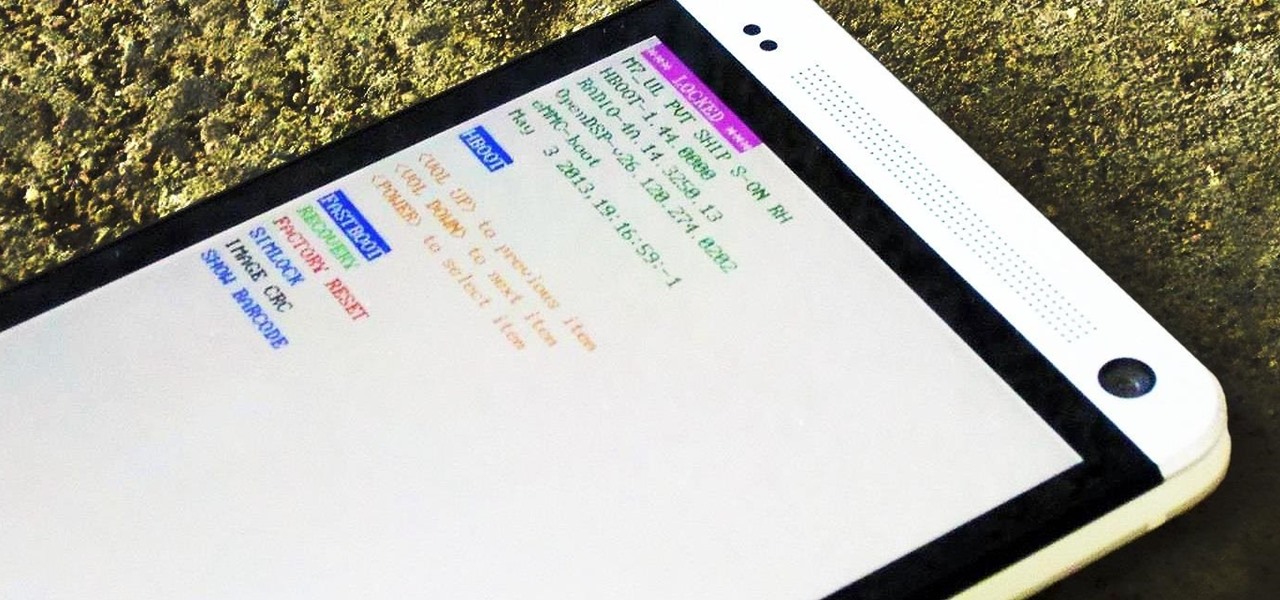
Straight out of the box, the Nexus 5 is an awesome device, but even it can be faster with better battery life. Luckily, one of the things that makes it so awesome is that there are tons of developers creating mods for it, since it runs stock Android by default. When it comes to gaining speed and better battery life, flashing a custom kernel is the way to go.

Welcome back, my tenderfoot hackers! I have written many tutorials on hacking using Metasploit, including leaving no evidence behind and exploring the inner architecture. Also, there are my Metasploit cheat sheets for commands and hacking scripts.

The release of the Nexus 5 marked the debut of the Google Now Launcher. Even with an integrated Google Now page on your home screen, the most talked-about feature was actually the always-listening functionality.

Google recently updated the camera software for the Nexus 5, and in doing so, made the app available to all devices running Android KitKat. This means that not only do we get a nice new camera interface on our phones, but we also get the benefit of an expanded development community.

Probably one of the most sought after features of the LG G2 is its "Knock Knock" capabilities. Rather than dealing with that pesky power button, you simply double-tap portions of the screen to either sleep or wake your device.

When Google introduced their new launcher alongside the Nexus 5, one of the most innovative features was the "always listening" voice search, meaning that at any time you were on your home screen, triggering a Google search was as simple as saying "Okay, Google."
If you're reading this, chances are you're a softModder, someone who doesn't let anything stand in his or her way from ultimate customization.

A bouquet of roses is a lovely thought but will quickly wilt and die. Give your loved one a bouquet of roses that will last for years to come and it will only cost you the price of a pencil and paper. They’re quick and easy to sketch.

Treasure may be buried as close as your own backyard. If you have some time to kill, try the art of treasure hunting. You’ll be sure to discover lots of interesting thing after learning how to use a metal detector to look for treasure.

It takes more than a kicky costume to become a professional wrestler. Start young to build up your basic wrestling skills and athleticism. To turn pro you’re going to need some acting flare, love for performing and a little luck.

Summer is almost here and you’re looking forward to that exotic vacation but you are going to need a passport and photos to go in it. There are a few simple ways to get a photo for your application. Find the method that is best for you and get traveling.

Bennett's fracture takes place at the base of the thumb. It typically occurs when an individual falls on an outstretch hand. The force is directed this way; the fracture occurs here. Learn how to diagnose and treat a Bennett's fracture in this medical how-to video.

A dislocated shoulder involves movement of the ball of the humerus away from the ball and socket joint. Ninety-five percent of the time, it will come out anteriorly when an individual's arm is forcefully pushed backwards and rotated in such a way that the ligaments in the front of their shoulder tear and the ball will pop out the front of the shoulder. This is a very common injury seen in contact sports. Learn how to diagnose and treat a dislocated shoulder in this medical how-to video.

Today's cheerleading incorporates difficult stunts and gymnastics into the routines. ESPN even now broadcasts the National High School Cheerleading Competition nationally! Madonna, Paula Abdul, Sandra Bullock and even Ronald Reagan were all cheerleaders! So if you or your children want to crack next year's squad, learn from our expert Shyra Fernandez. Shyra will show you the correct way to perform various advanced jumps and stunts that will get you on your way to being a "crack" cheerleader.

In this online video series, learn judo techniques from 12 time U.S. National Masters Champion Sensei John T. Anderson, as he demonstrates moves such as the compression arm lock, forearm lock, Hadaka Jin rear stranglehold, breakfalling, Juji Gatame cross lock, Kate Te Jume stranglehold, Kisa Katame, straight arm lock, Tai Otosha body throw, passing guard, Ko Uchi Gari major inside reap, leg throw, arm entwining, and Uke Otoshi hand drop.

Valentino Moutafov studied at the National Sports Academy in Sofia, Bulgaria. He has 20+ years teaching & coaching experience, and has competed in mixed pair & men's pair acrobatics.

Sibylle Walters founded Flairs Gymnastics in 1990. She is a former German National Gymnastics Champion.

Richard has been an avid pool player for the past 25 years and has played in competitive team and singles events since 1993. He has finished in the top ten percentile in both BCA national and VNEA international tournaments.

We've all attempted to fold a paper airplane before, right? One we hoped would sail majestically through the air for a good while but just ended up nose-diving into the grass. Paper planes, an invention likely as old as paper, are models of engineering; and they must account for the same dynamics as real planes, from drag force to stability to weight. So what is the perfect design?

Learning to code is difficult, particularly if you're doing it alone. While coding may be among the most valued job skills in many markets, the education is sometimes inaccessible.

Hey, you, still stuck at home? Cheer up, today is the first day of spring. Yes, really. And since you're probably locked in on TV, we're guessing you need a break from some of the less than sunshiney news reports rolling in. Well, no worries, because there's actually some good news to report.

We may or may not see Apple's long-awaited take on AR smartglasses this year, but the company is more than getting its practice swings in with its current wearables business, which hit record revenue in 2019 according to financial results released this week.

While consumer-grade smartglasses are the holy grail for tech companies, smartglasses maker Vuzix knows where its bread is buttered, and that's in the enterprise segment.
Drone mishaps, such as the collision that scratched a military helicopter in New York, are becoming something of an everyday hazard.
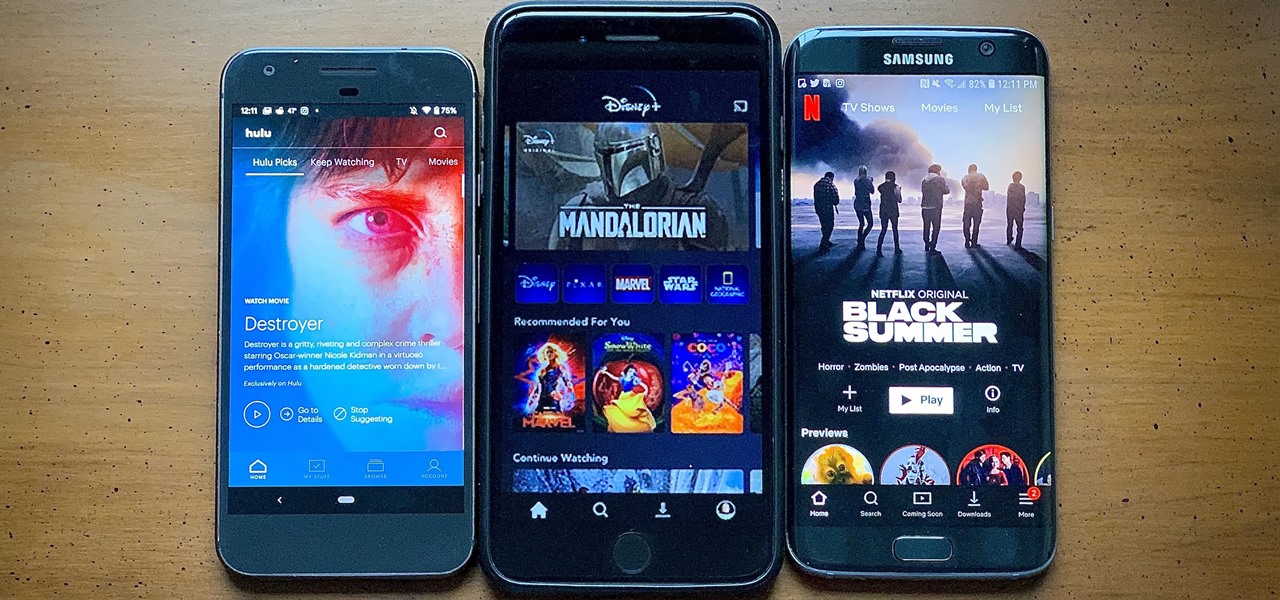
After much anticipation, Disney finally revealed its plans for its exclusive streaming service. Disney+ launches Nov. 12, and with it, all of the Disney content you know and love. But do you really need another streaming app in your life? We asked the same thing, so we broke down what we know about Disney+ and compared it to the current competition.

With Huawei's recent emergence as the second largest OEM in the world, the company was poised to finally make a big push into the US market. Instead, their efforts were derailed by an unlikely foe, the US government. As a result, American customers will miss out on the newly-released Huawei P20.

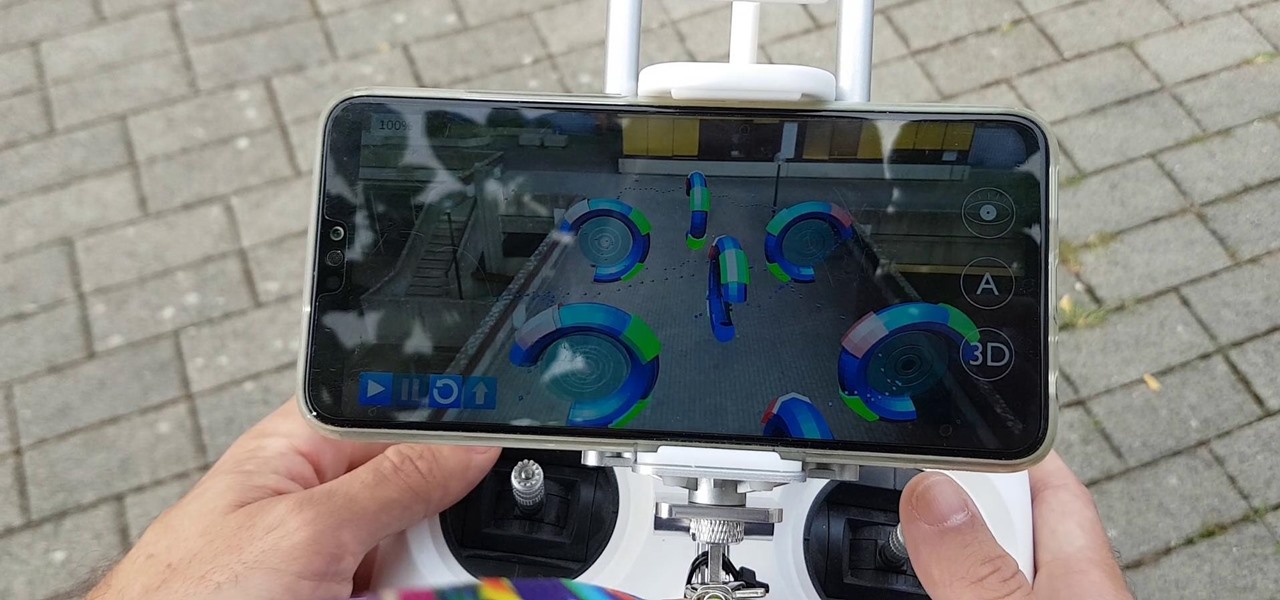
Augmented reality was recently named the "Mobile Disruptor of the Year" for 2017 by Mobile Marketer, but the technology is showing no signs of slowing down as we head into 2018. In fact, the technology appears to be gaining momentum.

ARKit is a marketer's dream. By providing tools for creating augmented reality experiences on mobile devices, AR apps can now be deployed easily alongside just about any campaign. As expected, we now have ARKit apps pushing wares ranging from automobiles to tequila.

When the climate changes, so do all the things that rely on the climate, including people, plants, and pathogens. A European study recently took a broad look at what kind of microorganisms are most likely to be affected as climate change heats, cools, dries, and wets the world around us.