Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to map networks with Spiceworks.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to packet sniff networks with the fundamentals.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to break down IP and TCP header with Wireshark.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to turn any Windows application into a service.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to organize your desktop with Microsoft Scalable Fabrics.

Beat the Level 2-3 Boss in Resident Evil 5 via this walkthrough and gameplay. Resident Evil 5 (RE 5) is the sequel to 2005's Resident Evil 4. This game guide shows you BSAA emblem locations, treasures, and includes strategies for all 6 missions and boss fights.

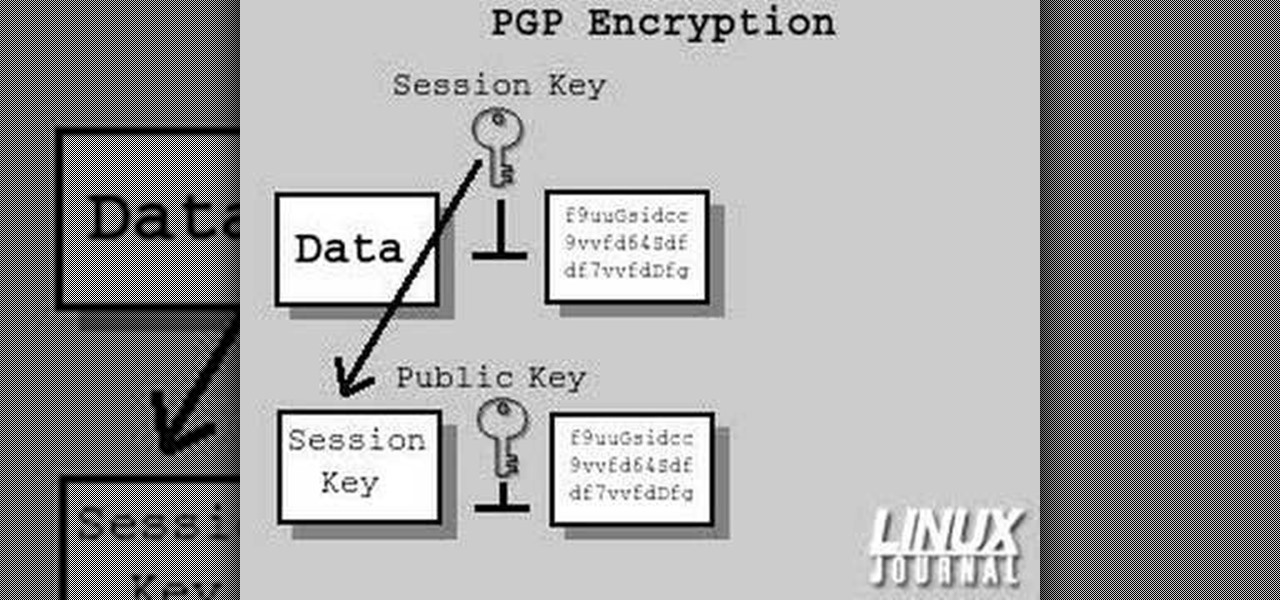
In today's time of rampant information crimes, including identity theft, security is more important to the average computer user than ever. This tutorial from Linux Journal Online shows how you can use GnuPG to secure and verify data on your Linux box. (This video was created using only free and open source software tools: TightVNC, pyvnc2swf, ardour2, audacity, jackd, LAME, kolourpaint, cinelerra-cv, mjpegtools, and ffmpeg.)

Check out this video tutorial to see how to construct an alarm system, that's based on the principle of motion detectors, which work by touch. It's very useful to catch unpleasant visitors red-handed. So make sure your chocolate bar never gets snagged again, catch the bandits with a motion detector alarm! Or just keep you kids away from the birthday present closet where peeping is not allowed.

This is a tutorial that shows you how to view and control your computer screen from your iPhone/iPod Touch. But this method is for people who have a jailbroken iPhone/iPod Touch. This works on Edge and Wifi. If you are having problems connecting try going to control panel then security center then turn your firewall off. Also try turning off anything like virus protection.

See how to make an X10 wireless security camera into a nice helmet cam on the cheap in this three-part video. All it takes is an X10 camera, ten bucks in parts, and two hours of your time.

In this episode, Brandon Jackson shows how to merge two images with the Photoshop gradient tool to create a banner montage. Doug Grammar joins D.Lee Beard again, this time to explain spyware, adware, and keylogging. They explain what these threats to your privacy & computer speed are as well as how to prevent and get rid of them. Speaking of security, Jason Rybicki shows one way to tell if your privacy is being compromised on a Mac using a free widget.

Learn to draw the mighty bird of prey, the eagle. Eagles tend to frequent national symbols like the "Coat of Arms", for countries like Egypt, Mexico, Germany, Austria, Russia and Armenia. It's more famous as The Great Seal of the United States. So, eagles seem to be one of the most influential birds in the world, so why wouldn't you want to learn how to draw it? This how-to illustrates the step-by-step details to drawing an eagle, "Águila" is the Spanish translation of eagle.

Team USA's Stefanie Nation on setting up properly in the stance. Pick up some bowling tips and tricks to improve your game, whether you are a beginner or a competitive bowler in a bowling league. Learn how to use the proper bowling stance with this bowling video.

Team USA's Lynda Barnes on importance of lane courtesy. Pick up some bowling tips and tricks to improve your game, whether you are a beginner or a competitive bowler in a bowling league. Learn how to practice proper lane courtesy with this bowling video.

Basics on proper way to pick up a bowling ball. Pick up some bowling tips and tricks to improve your game, whether you are a beginner or a competitive bowler in a bowling league. Learn how to properly pick up a bowling ball with this bowling video.

Cassidy Schaub demonstrates two handed delivery (back). Pick up some bowling tips and tricks to improve your game, whether you are a beginner or a competitive bowler in a bowling league. Learn the form for two-handed delivery with this bowling video. These bowling tutorials are brought to you by USBC, United Stated Bowling Congress. Search USBC on WonderHowTo for more bowling tutorials. From the USBC website: "USBC is the national governing body for bowling as recognized by the United States ...

Cassidy Schaub demonstrates two handed delivery (front). Pick up some bowling tips and tricks to improve your game, whether you are a beginner or a competitive bowler in a bowling league. Learn the form for two-handed delivery with this bowling video.

In this scientific video tutorial, undergraduate students in a forensic chemistry lab demonstrate a forensic DNA test to catch a criminal. Learn how to perform a forensic DNA test! Just like in CSI.

In this scientific video tutorial, undergraduate students in a forensic chemistry lab demonstrate how to perform gunshot residue analysis (GSR). Learn how to perform gun shot residue analysis (GSR)! Just like in CSI.

In this scientific video tutorial, undergraduate students in a forensic chemistry lab demonstrate how to use a comparison microscope for bullet and bullet casing comparisons, and color developments tests for impression marking enhancement (such as for filed-off serial numbers). Learn how to perform ballistics comparisons! Just like in CSI.

In this scientific video tutorial, undergraduate students in a forensic chemistry lab demonstrate how to develop fingerprints using a variety of methods: Cyanoacrylate (superglue) fuming, dusting, and iodine fuming. Learn how to dust for fingerprints, just like on CSI.

Wish you could flip in order to spice up that cheer you've been working on? Learn how to do both a front and back hand spring in this video tutorial.

Mastering your pike will add flare to any cheer. Learn how to do cheerleading pike jumps in this video tutorial.

Changing your leg position can create a beautiful variation to an already existing cheer. Learn some cheerleading leg variations in this video tutorial.

Knowing how to properly set up your mounts for cheerleading will help you execute your stunts safer and better. Learn how to do some stunt mounts in this video tutorial.

One of the most important things to do before practicing your cheerleading is to stretch properly. Learn some simple tips on stretching in this video tutorial.

Using stunts will ensure your cheers are visible to the crowd. Learn some shoulder height cheerleading stunts in this video tutorial.

While SSH is a powerful tool for controlling a computer remotely, not all applications can be run over the command line. Some apps (like Firefox) and hacking tools (like Airgeddon) require opening multiple X windows to function, which can be accomplished by taking advantage of built-in graphical X forwarding for SSH.

One of the best things about Android is the ability to customize every aspect of your device to make it your own. However, unless you have prior knowledge or experience with every single setting available to you, you might have missed a few critical features without even knowing it. Some settings are easy to find, while others might be tucked away in another menu of their own.

Your social security number, credit card information, and medical history can fall into the wrong hands if you're not careful about how and where you share your data online. If you really care about your data, there are tools and techniques you can utilize to protect yourself from cyberstalkers, advertisers, and hackers in a time when digital lives are a high commodity.

Smartphones are like high tech buckets that collect our personal information through constant use. This has some obvious benefits, like getting a more personalized experience with our devices. On the other hand, this data is a tempting target for bad actors looking to make a buck at the expense of your privacy.

In a world increasingly regulated by computers, bugs are like real-life cheat codes. They give you the power to break the rules and do good or bad without ever leaving your seat. And government agencies around the world are discovering and stockpiling unreported bugs as cyberweapons to use against anybody they see fit.

While maggots living in human eyeballs isn't necessarily a problem in the states, it could happen to you one day if a fly decides your warm eyeball is a suitable place for its larvae. If this rare event should happen, before you start gouging your eyeball out, remember this trick from National Geographic explorer and engineer Albert Lin and everything will be okay.

Seldom in recent history has a cyber security event caused so much media stir (maybe because it happened to a media company?) and international relations upheaval. Cyber security breaches seem to take place daily of major corporations, but the Sony hack seems to have captured the American imagination and, for that matter, the whole world's attention.

Elaine Lemm demonstrates how to make the traditional British dish, yorkshire pudding. This video recipe goes through all the necessary steps for preparing yorkshire pudding.

In this tutorial, we learn how to sign up and set up a Twitter account. Twitter is a social networking site where you have 140 characters to tell your friends how you are feeling, what you are doing, or talk to them! You can follow people and other people can follow you. You can choose who follows you, which will create and strengthen online relationships. You can even get business referrals from this! Just by getting yourself out there, this is a great tool. To sign up, you will simply go to...

In this tutorial, we learn how to remove pop up screens when Avira Antivirus updates. First, locate the installation folder for Avira, this should be in your computer programs. After this, locate the file "avnotify.exe". Next, right click this and go to the preferences option. Now, go to security, then edit, then click on the system option. Click "deny" on all the boxes in the bottom section, then save these. Now, the next time your Avira updates, you will not get a pop up box that tells you ...

Tired of your PC pestering you to check this or fix that? Are you sick of all those pop-up balloons? Well, Windows 7 now has a feature called Action Center, and it lets you decide which alerts you see and which ones you don’t. See it in action!

This video tutorial is in the Computers & Programming category where you will learn how to secure your wireless internet connection. If you don't secure your wireless internet connection you are allowing others to enter in to your network. Open the set up CD and first change the network name from the default name to anything that you like. For this go to step 3 of 'naming your network', type in your network name and click 'next'. Then you enable security on the network by choosing 'WPA2'. Nex...

You have an online store ready to go… almost. You still have to deal with getting the perfect shopping cart to go along with your e-store. Matt Winn from Volusion walks you through what to consider when choosing a shopping cart software for your online store. From what type of software exists in the market, to the required features, to security levels (PCI certification), to the type of support you may need.