The National Aeronautics and Space Administration (NASA), provides this educational video on how Isaac Newton's three laws of motion apply to aerospace and the climb and descent of an aircraft. The powerhouse of space exploration is one place you should learn these concepts from.

Understand the concepts of drag force and how Newton's laws of motion apply to an aircraft's take off with help from NASA -- the National Aeronautics and Space Administration. The juggernaut of space exploration lays everything out on the table for you. Learn from the best, learn from the pros, learn from NASA.

Learn Newton's laws of motion from the utmost authority on aeronautics -- NASA aka National Aeronautics and Space Administration. See how Newton's laws apply to aircrafts from the powerhouse of space exploration. They talk about thrust force as applied to aviation.

The powerhouse of space exploration, NASA (National Aeronautics and Space Administration), sheds light on Newton's laws of motion as pertaining to drag force on aircrafts. This is a great source for any aeronautics major. The infamous government agency breaks drag down for you.

Join NASA (National Aeronautics and Space Administration) as they give the basics on the concepts of weight and balance as applied to aerospace. There's no better place to learn about aviation theory than NASA, the United States government's most infamous agency--the powerhouse of space exploration.

Learn everything you need to know about Newton's third law of motion from none other than NASA. The National Aeronautics and Space Administration is the United States government's most infamous agency and powerhouse of space exploration. Why wouldn't you want to learn Newton's laws of motion from them?

The second law of motion. Force equals mass times acceleration. F=MA. Learn the facts about Newton's second law of motion from the National Aeronautics and Space Administration, otherwise known as NASA. The United States government's most infamous agencyand the powerhouse of space exploration explains motion theory.

Demystify Newton's first law of motion with none other than NASA -- the National Aeronautics and Space Administration. The United States government's most infamous agency and powerhouse of space exploration teaches you the law of inertia… Newton's first law of motion.

In this video tutorial, viewers learn how to change the lock pattern on an Android phone. The lock pattern allows minimum security on the phone to prevent other people from tampering with your mobile files. Begin by going into the Settings and click on Location & security. Under Screen unlock pattern, select Change unlock pattern. In order to change the unlock pattern, users will have to type in the current unlock pattern. Now type in the new unlock pattern and press Continue. Then retype the...

The Nessus vulnerability scanner, is the world-leader in active scanners, featuring high speed discovery, configuration auditing, asset profiling, sensitive data discovery and vulnerability analysis of your security posture. Nessus scanners can be distributed throughout an entire enterprise, inside DMZs, and across physically separate networks. In this network security video tutorial, you'll learn how to hack a network using Nessus 3.

Watch this video tutorial, and learn how to turn an ordinary inexpensive webcam into a hidden home security system, viewable anywhere in the world from your cell phone! With a cute and cuddly teddy bear and a cheap webcam, you can make the perfect homemade security camera, or just a camera to spy on your sister and her friends during sleepovers. Follow along with the steps in this how-to video and learn how to set up this spy system. Note: this video is NOT recommended for people who are perv...

By DevonLocks.Com - Security pins can be a pain. This video shows you how to bypass them. See our other video on how to spot them.

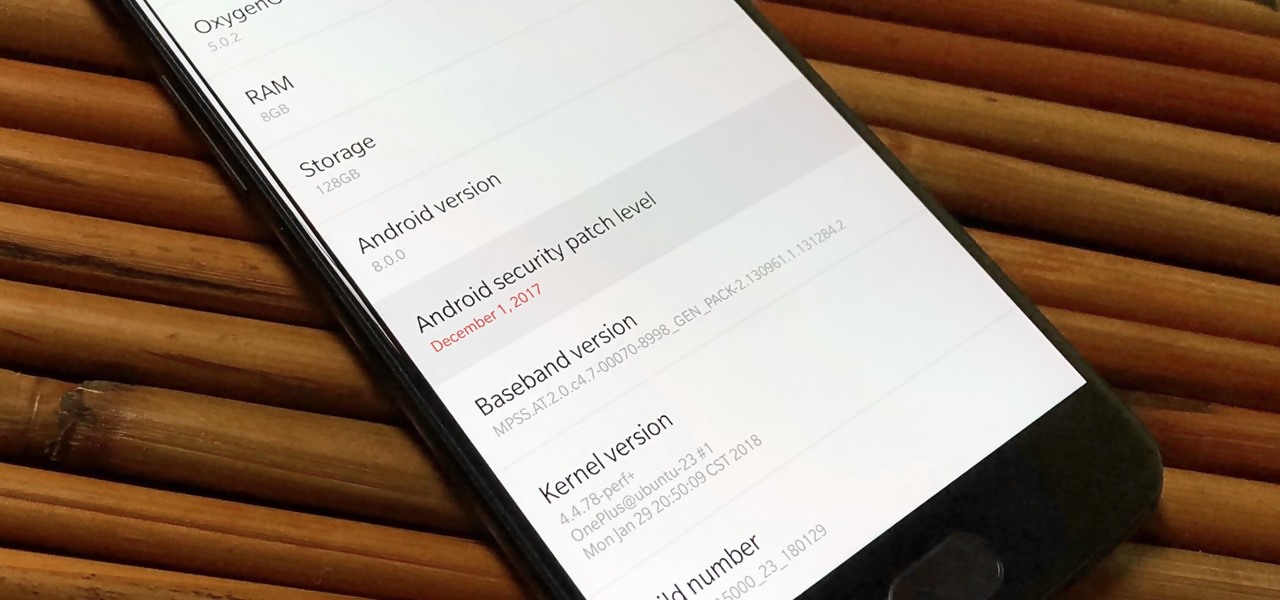
If you own the Galaxy S8, S8+, or Note 5, be on the lookout for a new security update. These Samsung devices are the latest to receive the December security update to patch issues from both Samsung and Android.

As many of you know, I have been running a couple of series here on Null Byte about digital forensics called Digital Forensics for the Aspiring Hacker and Digital Forensics Using Kali. Although many readers have seemed to enjoy these series, just as many seem to be pondering, "Why should I study digital forensics?"

In this video, we learn how to remove Security Tool the simple way. Most ways will not remove this from your computer, but this way will. To start, you will need to restart your computer. After this, press ctrl+alt+del the moment Windows shows up. Then, go to the Task Manager and look through the programs that are open. When your security tool opens, press the same buttons to get the mouse free. Then close the security tool from the Task Manager. Now, go to your desktop and press on the icon ...

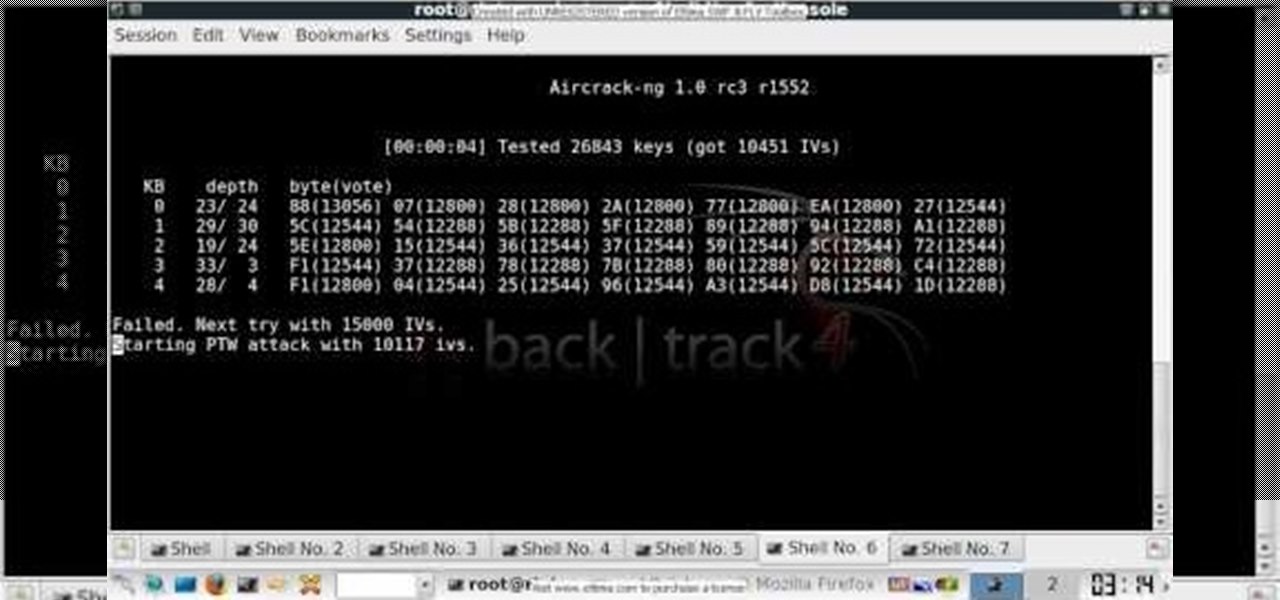
In this clip, you'll learn how to use the BackTrack Linux distro and the Aircrack-ng WiFi security app to hack a WEP network. The process is simple. For more information, including step-by-step instructions, and to get started testing the security of your own WiFi networks, watch this hacker's how-to.

Learn how to use the Backtrack Linux distro and the Aircrack-ng WiFi security app to crack a WEP key. The process is simple. For more information, including step-by-step instructions, and to get started testing the security of your own WiFi networks, watch this hacker's how-to.

In this clip, you'll learn how to use the Backtrack Linux distro and the Aircrack-ng WiFi security app to crack a 64-bit WEP key. The process is simple. For more information, including step-by-step instructions, and to get started testing the security of your own WiFi networks, watch this hacker's how-to.

In this clip, you'll learn how to use the Backtrack 3 Linux distro and Aircrack-ng WiFi security app to crack the password to a WEP-protected wireless network. The process is simple. For more information, including step-by-step instructions, and to get started testing the security of your own WiFi networks, watch this hacker's how-to.

In this clip, you'll learn how to use the Backtrack Linux distro and the Aircrack-ng WiFi security app to crack a WEP key. The process is simple. For more information, including step-by-step instructions, and to get started testing the security of your own WiFi networks, watch this hacker's how-to.

Wish there were a way to turn your webcam into a bonafide security camera? Well, there is! And it's easy! So easy, in fact, that this home-computing how-to from the folks at TekZilla can present a complete overview of the process in just over two minutes. For more information, including step-by-step instructions, take a look.

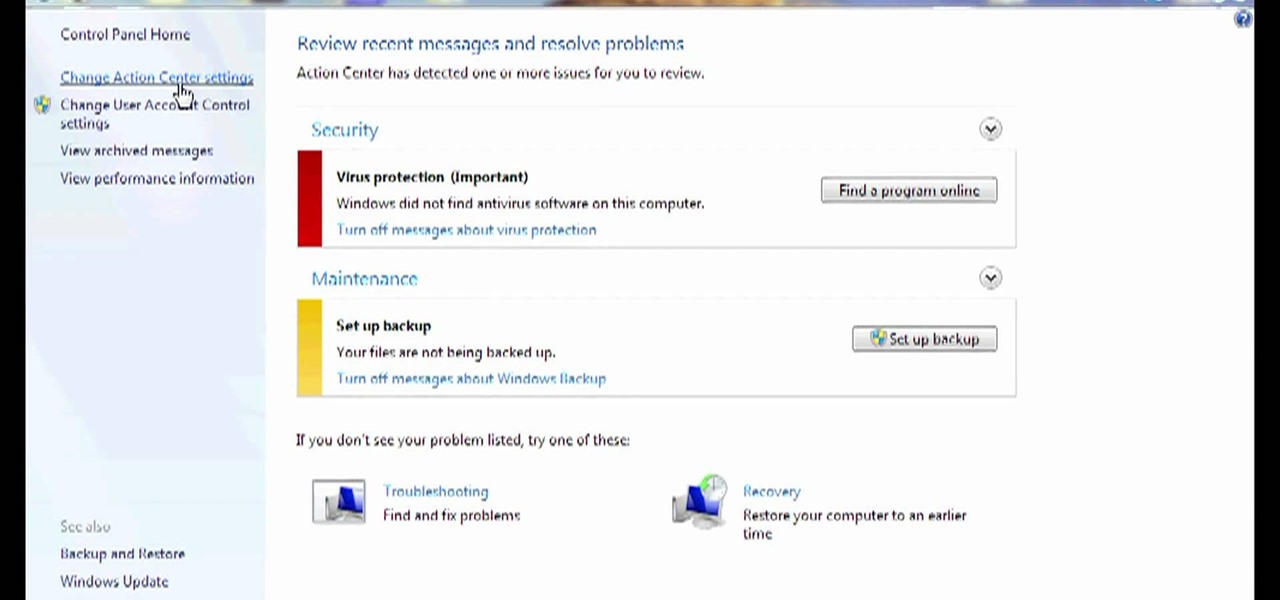
Need some help figuring out how to disable potentially annoying popup security notifications in Microsoft Windows 7? This video tutorial will show you how it's done! It's easy! So easy, in fact, that this home-computing how-to can present a complete overview of the process in just over a minute's time. For more information, including detailed, step-by-step instructions, watch this Win 7 user's guide.

In this Microsoft Windows 7 users guide, you'll learn how to take advantage of the operating system's new Applocker security feature. It's easy! So easy, in fact, that this home-computing how-to can present a complete, step-by-step overview of the process in about a minute and a half. For more information, including complete, step-by-step instructions, take a look.

In this how-to video you'll learn all the tricks and tips to getting yourself through airport security quickly and easily, even if you have electronic gadgets. Some companies produce travel gear that the TSA will let pass through without having to remove your laptop or electronics. Timesaver! Watch this video and you'll soon be cruising through the "Expert Traveller" line.

It seems that almost every multiplayer map in Gears of War 2 has a secret glitch-based way of getting underneath it. This video is a tutorial on how to do just one of these glitches. It will show you how to get under the Security multiplayer map using a barrier breaker glitch.

In this tutorial, learn how to disable the annoying UAC or User Account Control on your Windows Vista computer. This clip will show you how to do this without compromising your security.

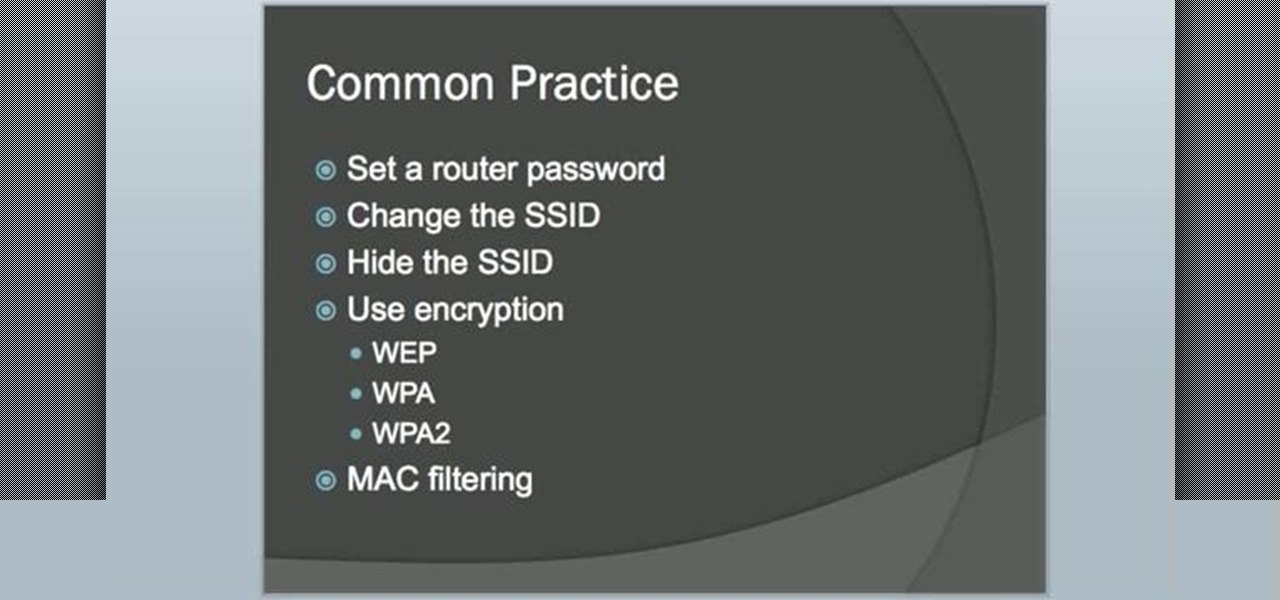
In this video tutorial, viewers learn how to secure a home wireless network. There are 3 types of security protocols for connecting devices. The 3 types of security protocols are: OPEN, WEP and WPA. Users should use passwords that are secure but no so obscure that they are unusable. The password should not be dictionary words. They should be mixed with casing and contain the user's phone number. Go to your router's website and log into the website. Find the setting for wireless security and e...

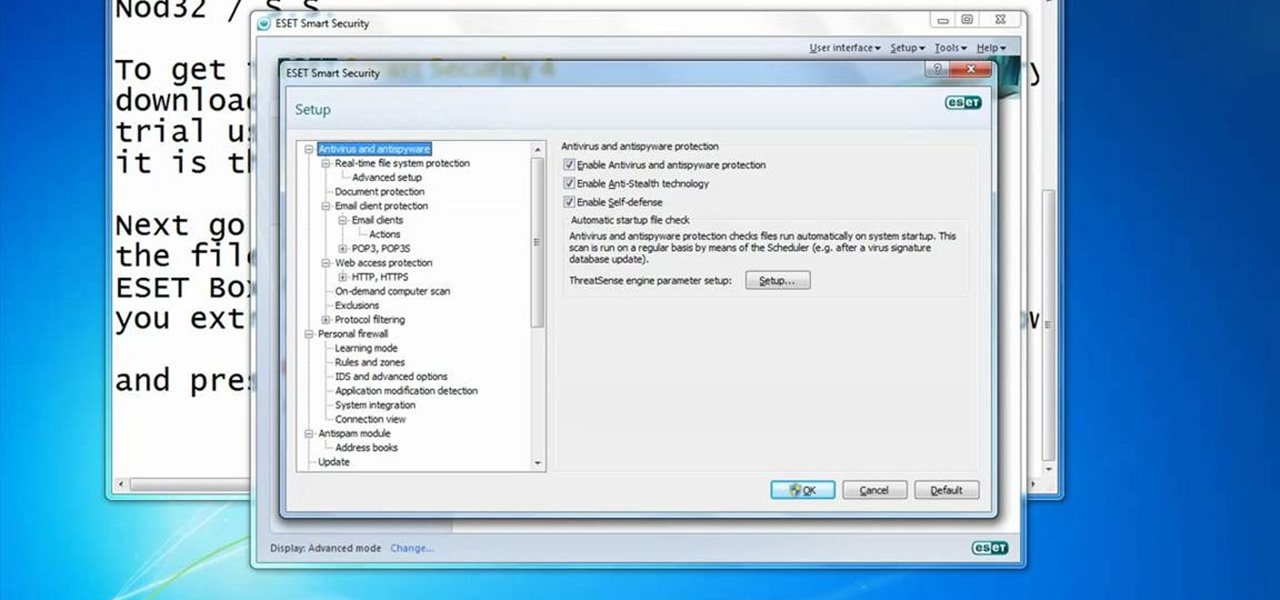
In this video you will learn how to Get ESET Nod32 or Smart Security forever. First make sure you have the trial for ESET Nod32or Smart Security. To do this go into the description of the video, download that file and put in the trial username and password. The downloaded file its called ESET Box4Ever.Before you extract the file open your ESET window and press F5.Uncheck self defense and restart computer. After you restarted the computer extract the files from ESET Box4Ever and run the file, ...

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to obscure your OS fingerprint.

Got a mystery to solve? Somebody’s been making off with your stuff, and you don’t have a clue who it is, do you? Here’s your chance to catch them in the act. In this how to video you will learn to make a DIY laser security system.

Learn how you can protect your home in a pretty radical and fun way by transforming two cheap household items into a stealth hi-tech, anti-burglar, security system! Literally to hot for any bad guy to handle!

In this video you will see how to access network security cameras through google search engine easily!

Samsung just began rolling out the Oreo Beta 2 to registered users of the Galaxy S8 and S8+. The update's changelog promises the inclusion of the October 2017 security patch. Unfortunately, after downloading the update, we've noticed this is not the case. Omission of the more recent security patch is notable in that it leaves devices vulnerable to several known exploits, such as KRACK.

Google released its "Android Security: 2016 Year in Review" report last month, and to no one's surprise, included its own flagship phones. However, one surprise on the list was the BlackBerry PRIV, which Google named one of the best Android devices for privacy.

A human rights activist from the United Arab Emirates recently stumbled upon three gaping security loopholes in iOS that work by enticing you to tap a link sent to your iPhone. Ahmed Mansoor received a text message from an unknown number roughly two weeks ago, but instead of following the link it included, he sent the message over to a security researcher at Citizen Lab.

In an article published in early-2015 by Peninsula Press, it was reported that the demand and the salaries for cyber security professionals are exploding! They cite that 209,000 cyber security jobs were unfilled last year, and that job postings have increased over 74% in the last 5 years. Job opening are expected to grow by another 53% over the next 3 years. You are definitely in the right field, my tenderfoot hackers! Some researchers are expecting information security jobs to continue to gr...

With all of the personal data that's stored on our smartphones, it's of vital importance that we have some sort of lock screen security enabled. One of the Galaxy S5's killer features is obviously the fingerprint scanner. It makes the process of dealing with a secure lock screen a bit easier than typing in a password or PIN.

As far as overall security updates are concerned, we all know that iOS reigns supreme over Android. But just how bad do Android devices fare against Apple in general? A recent report will have you second guessing some companies the next time you're in the market for a handset.

When it comes to your security, you want the best of the best. Why settle for mediocre service with something as valuable as your protection? Malware continues to make its way onto the Play Store, leaving millions of devices vulnerable. You need an app that will shield your devices from both the latest malware threats and threats nearby. And when it comes to antivirus apps, there is only one choice.

Samsung's 2016 line of smartphones has a new update, at least for the devices on AT&T. The update brings the Galaxy S7 to version G930AUCS4BQL1 and the Galaxy S7 Edge to version G935AUCS4BQL1. Here's what's on the table.