Many of us in the Steampunk community have pets that we love and cherish, myself included, and we want those pets to share our joy of Steampunk. In reality, they couldn't care less, but for some reason we still love to dress them up. Their reactions usually range from bemused acceptance to temper tantrums, but the awwwws we get from onlookers usually makes it worthwhile.

If you want to start the party out right, you have to impress the crowd with your awesome bartending skills. While lighting cocktails on fire is a nice way to warm up the crowd, it's been done by thousands of bartenders across the globe. Plus, if you're not careful, you could end up like this guy:
Are you scared that the RIAA is about to track you down for illegally downloading songs. Well, here is a method of obtaining many songs absolutely free that is virtually untrackable

Say whatever you want, but Steampunk is primarily a maker culture. Consider that Steampunk has existed since the 1960s and yet more or less languished in obscurity until approximately 2005, which is when it made the leap to costuming. That costuming was what provided the leap to the tangible, despite the fact that Steampunk art had also existed for years.
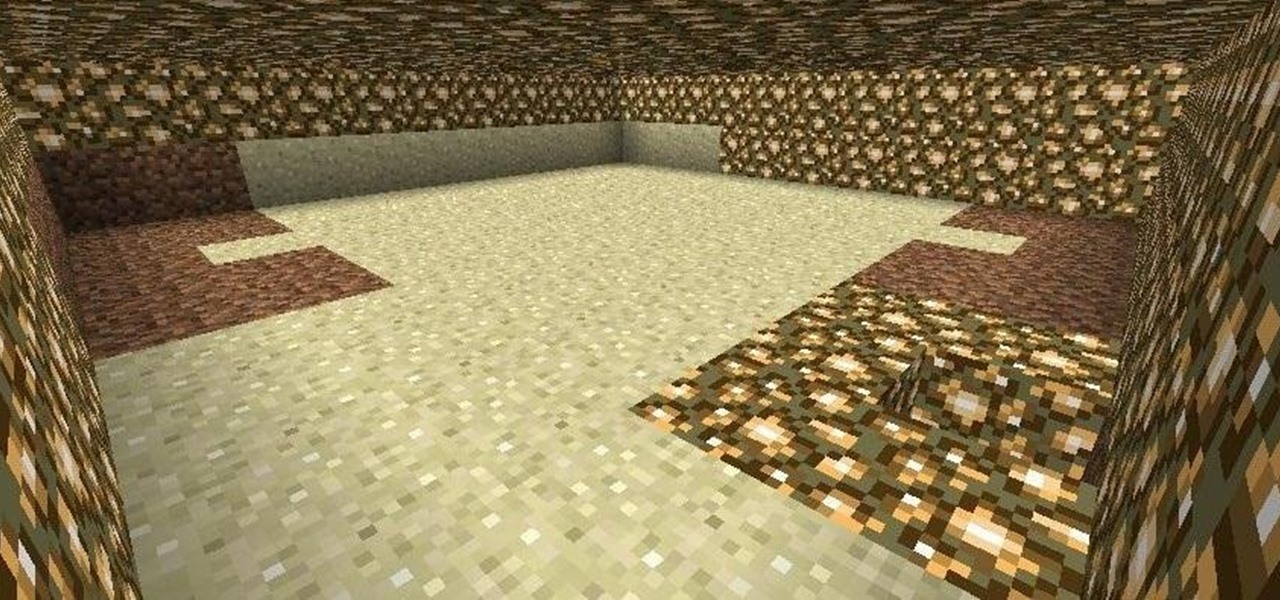
There are a number of different techniques for building underwater in Minecraft. The easiest is to fill a room with wood or leaves, then set them on fire. It'll burn down, leaving a pocket of air for you.

The final chapter of Christopher Nolan's Batman trilogy is here, The Dark Knight Rises, and if you're anything like me, it made you want to immediately don a cowl of your own and run around punching criminals. Don't forget though, one of the most awesome aspects of Batman is his never-ending supply of crazy gadgets. Unfortunately for most of us, we don't have a billion dollars, nor Morgan Freeman, so we'll just have to make do with some good old-fashioned DIY tricks. Read on for a rundown of ...

There are lots of people who want to stay anonymous online, and lots of reasons they want to do this. Staying anonymous on the internet isn't easy, and it's probably possible to trace almost anyone with enough time and resources. A lot of people think that they're completely secure with just one method of cover. For example, a lot of people thought anyone using the Tor network was nearly untraceable, but then things like this often cast doubt on just how secure these networks are. Unless you ...

Spices are a necessary ingredient in any kitchen. It doesn't matter how good of chef you are—without proper spices, your food will always fall flat.

Have you ever felt like you wanted to totally annihilate someone in Minecraft with a machine gun? Yeah, me, too. Thankfully, you can!

In this article, I'll be explaining the basics of how microcontrollers work, physically and virtually. First off, microcontrollers are no simple thing, so don't be discouraged if you find it mind-boggling! The world of microcontrollers is fascinating, engaging, and an awesome hobby; it never gets boring. I'll be focusing more on I/O and analog based microcontrollers, such as those running Arduino, and using Atmel chips as examples (these are most commonly available, and easy to program).

Bokeh (which translates to "blur" in Japanese) is a photography technique referring to the blurred areas of a photograph. Basic bokeh photographs often have one point of focus, while the background falls away into a dreamy, blurred haze.

Learn the recommended cleaning techniques for your Lynx Grill. The Lynx grill has many innovative features and understanding how to use each grill feature can make you more proficient user of the grill.

In this video tutorial, viewers learn how to lose belly fat without having to do crunches. The exercises provided in this video are: push-ups, squats and dumbbell squat raises. These exercise don't just work on the abdominal muscles. It is recommended to do each exercise until failure. These exercises use the abdominal muscles as stabilizers. The key to losing fat is to push yourself hard to do the exercise. Abdominal muscles are not designed to flex. Crunches do not help lose belly fat. This...

In this video tutorial, viewers learn how to pick the lock of a garage door. It is not recommended for users to learn this technique to use to open other people's garage doors to break in someone's home or steal their possessions. The tools needed for this technique are a L-key and a diamond pick. Put the L-key at the bottom of the lock hold and fiddle around with the diamond pick on the top part of the hole. Do this until your able to rotate the lock. This video will benefit those viewers wh...

This video shows the process of removing scratches from an iPod. The video demonstrates the best way to remove scratches not only from the metal but from the front viewing screen also. One starts with the recommended Weiman Metal Polish and 100% cotton cloth. To achieve best results and a scratch free finish, the video also gives tips like shaking the polish before use. Your iPod as well as any other similar piece of equipment will look scratch free and as good as new by following these simpl...

Thanks to the PlayStation 3 and Xbox 360, video games are constantly evolving to higher degrees of sophistication, with complex graphics, lifelike resemblances and storylines that create exciting experiences that relieve the tediousness of our everyday lives.

Whether you miss the good old days of Telnet or you want to know what hacking was like when security was nothing but an afterthought, Telehack is the game for you. The text-based hacking game is a simulation of a stylized combination of ARPANET and Usenet, circa 1985 to 1990, with a full multi-user universe and player interactions, including 26,600 hosts.

If you want to get started sniffing Wi-Fi networks, you usually need to start with a wireless network adapter. But thanks to a Wi-Fi sniffing library written in Arduino and the ultra-cheap ESP8266 chip, you might not need one. For less than $10 in electronics, you can build a tiny Arduino Wi-Fi sniffer that saves Wireshark-compatible PCAP files and fits anywhere.

There's actually more to the dialer screen on your OnePlus than meets the eye. Besides its obvious purpose of calling people, there's a vast array of secret codes that you can input to troubleshoot your device, in addition to revealing important information, making anonymous phone calls, and so much more.

The war on dehydration is a commercially burgeoning marketplace. An increasingly sophisticated consumer population hoping to conquer everything from 26-mile marathons to vodka shots is deconstructing every functional remedy in the fight to quell the effects of severe dehydration.

It's easy to have your password stolen. Important people like executives, government workers, journalists, and activists face sophisticated phishing attacks to compromise their online accounts, often targeting Google account credentials. To reduce this risk, Google created the Advanced Protection Program, which uses U2F security keys to control account access and make stolen passwords worthless.

Hackers can be notoriously difficult to buy gifts for, so we've curated a list of the top 20 most popular items Null Byte readers are buying during their ethical-hacking studies. Whether you're buying a gift for a friend or have been dying to share this list with someone shopping for you, we've got you covered with our 2017 selection of hacker holiday gifts — just in time for Christmas.

The holidays are stressful. Between traveling, family, and dinner, Thanksgiving weekend can feel like weeks. Many families have traditions that make the days long, but some of us would rather curl up somewhere and watch our favorite shows. But all is not lost — our phones do so much for us now that they can help make the long stressful weekend much more bearable.

Hi, everyone! Recently, I've been working on a pretty interesting and foolish project I had in mind, and here I'm bringing to all of you my findings. This guide's main aim is to document the process of building an Android kernel, specifically a CyanogenMod kernel and ROM, and modifying the kernel configuration to add special features, in this case, wireless adapter Alfa AWUS036H support, one of the most famous among Null Byters.

Mr. Trailer gives instructions on how to play a fun game called Farkle. Players will need five dice. He recommends casino dice which come in a pack of five. First roll the dice to see who goes first. The objective is to get ones, fives, triples, or straights. You have to get 650 to get on the board. Keep score on paper to keep track. Once you get on the board you can "stay" or roll again. Triples are 100 x the number. For example three 6's would be 600, a 1 would be 100, etc. Mr. Trailer has ...

No need to go on living one more day with a dirty couch. It's a good idea to thuroughly clearn your couch to remove any seen or unseen dirt. Include a good couch cleaning on your next chore wheel and see if you notice the difference.

They say cheaters never prosper, but how will your know for sure if you don't give it a try? By a little repositioning of the blindfold and some spacial awareness you can be the master at this classic party game.

If your cray fish or crawfish has tiny tiny worms crawling over the shell, watch this how-to video to fix the problem.

It is important to have healthy teeth not only for your appearance but for your overall health as well. You can keep your teeth white by avoiding foods that stain your teeth and having a good cleaning routine including fluoride

Awakening the female energy that resides in the base of your spine is not a process that can be done in an afternoon but is something you work towards though lots of work in kundalini yoga and work toward an enlightened state of being.

It might seem like an inconvenience but it is important to take the time to find out what has caused your oil light to come one in your car. You may just be low on oil or you may have a more serious problem but ignoring the warning will only lead to further damage.

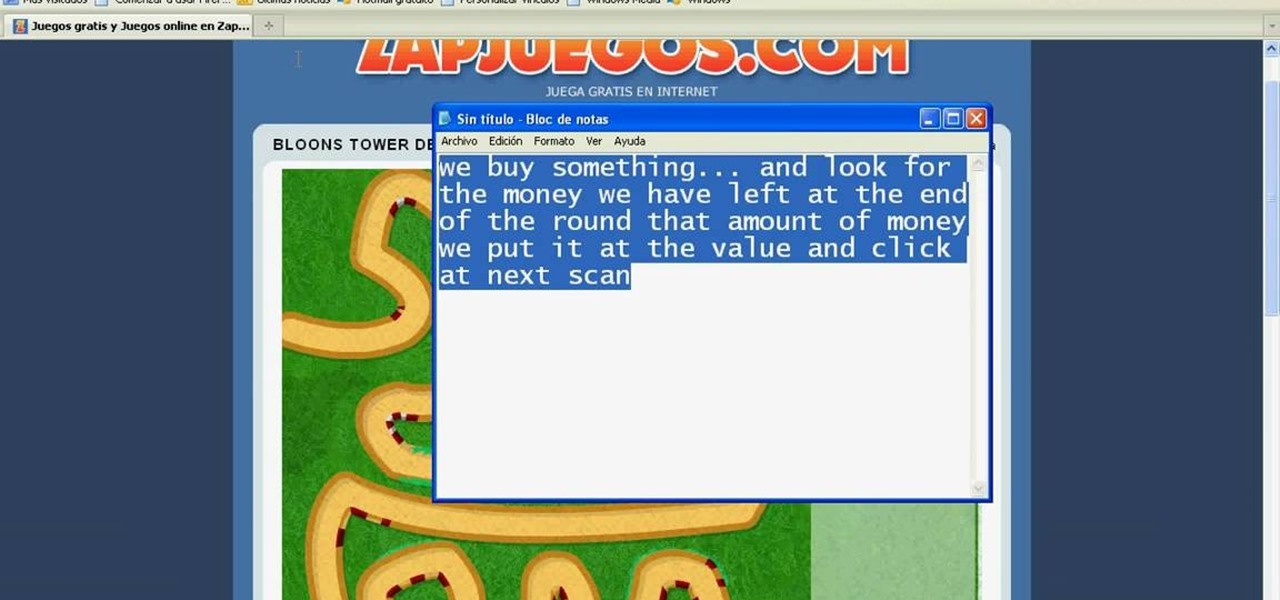
Hacking money in BTD3 is the key to success. And how do you plan to hack Bloons Tower Defense 3 money? With Cheat Engine, of course.

This session is tailor-made for advanced Studio users aiming to achieve ultimate quality surface creation.

Have you ever had a great meal at your local restaurant and wondered how to make it yourself? Or perhaps you've found yourself stumped at what to make for dinner based on the random provisions in your kitchen? Now, you can discover solutions to these food-based problems via Snapchat's computer vision wizardry.

No matter the field you work in, tech dominates every industry in 2020, and that means that you can always increase your earning potential by adding valuable coding skills to your arsenal. Coding can lead to dream software development career paths, lucrative freelance work, and it can be an impressive boost to your résumé. Now, you can learn these valuable skills at home with The Complete One Hour Coder Bundle, an offer at an unmissable 97% off its usual price, at just $34.99 (usually $1,200).

While sheltering at home orders are lifting, companies are still conducting most business online. Case in point, hackers have been having a field day over the last few months. Securing your identity has always been important, but never as much as it is at this moment.

The Pi-hole project is a popular DNS-level ad blocker, but it can be much more than that. Its DNS-level filtering can also be used as a firewall of sorts to prevent malicious websites from resolving, as well as to keep privacy-killing trackers such as Google Analytics from ever loading in the browser. Let's take a look at setting a Pi-hole up and customizing a blacklist to suit your needs.

When you don't have a steady cellular signal or immediate Wi-Fi access but need to communicate with others around you, you can set up an off-the-grid voice communications network using a Raspberry Pi and an Android app.

With protests springing up across America, there's a chance you may have your first interaction with law enforcement. Many demonstrators will have their phones in-hand to film the action, which, sadly, could prompt an officer to demand the device and any self-incriminating data it may contain. Before this happens, you should know there are tools at your disposal to protect your data in such situations.

After many years of rumors, the second-generation iPhone SE is here. At $399, it is the most inexpensive iPhone Apple has sold since the original iPhone SE came out. And while the new SE comes with Apple's typical five-watt power adapter, the smartphone supports fast charging — you just need to get a fast charger separately.