I may be a bit weird, but I enjoy listening to music at night as I fall asleep. Sure, you could create a playlist of songs so that it stopped after all the songs finished playing, but I have a rather extensive database of music and I enjoy listening to them randomly. Also, I like to ensure it terminates after a specific amount of time (I don't want it playing all night). Or sometimes I use it when I am cooking so that when the music stops, I know I need to check on my food, etc.

I have owned quite the plethora of electronics in my life. A commonality between most of these devices' screens is frozen or dead pixels. This is probably the most annoying thing about buying new hardware—your LCD, or worse, LED display has one or more pixels that continues to stay lit. Most of the time, this will appear in the form of a brightly colored pixel that never changes, or a pixel that never displays the right color. Once you notice it's there, you just can't stop staring at it. It ...

The smell of hot curry pouring from room is inevitable. The mixture of spices filled up my nostril as I sat. The lighting of the room might not be pleasant but it is the way in which the restaurant owner set up his restaurant to stop excessive lighting, which is done with a huge decorative curtain. My attention was set on the glamorous uplifting Indian pop music, playing from the large high-definition televisions.

There are many ways to jailbreak the iPhone, found all over the internet. This method explains how to jailbreak the iPhone or iPod touch using Quickfreedom 2.0 BETA on a machine running Windows Vista.

If you've ever gotten super glue stuck to your fingers, you know what a pain it can be to get it off again! Don't worry - there's a simple household item you probably already stock that can take care of your super glue super mess!

If you need some help rigging a soft plastic fishing bait, this quick video can help. Use tandem rigging to get it done. The tandem rigging is liked when short strikes become an issue. As baits get increasingly longer, the second hook becomes increasingly important. Particularly recommend is tandem rigging on longer baits, such as 14” and 18” models.

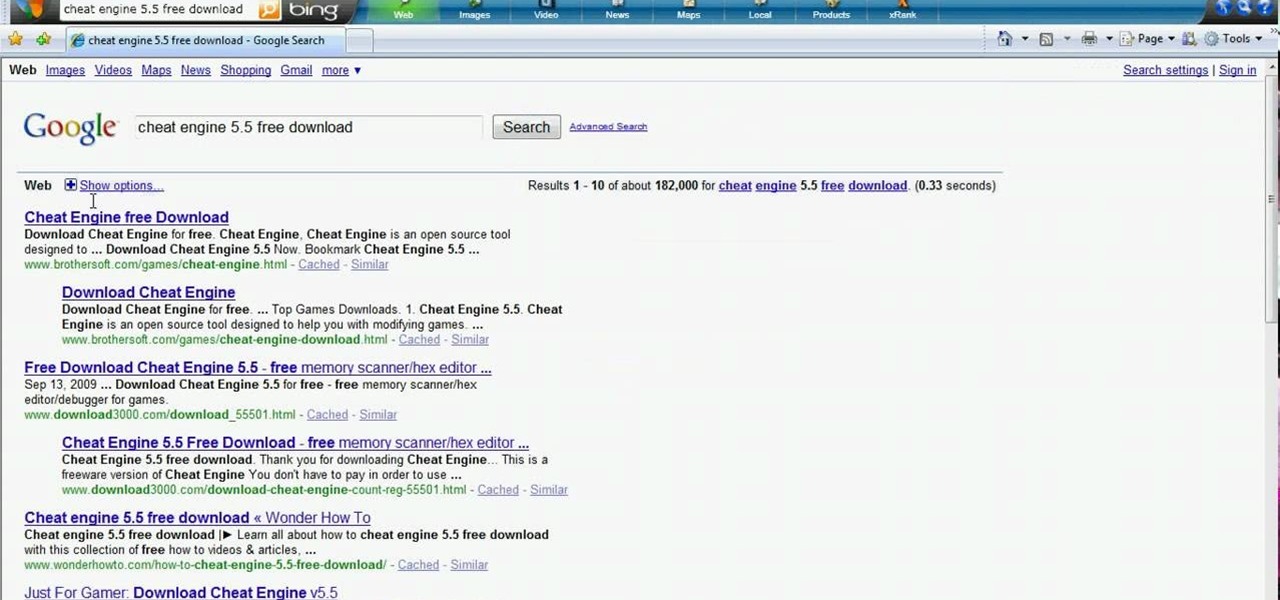
Hacking flash games is the new coolest thing these days... now hackers can be anywhere, ever expanding, all thanks to a little cheating program called Cheat Engine. Check out this video tutorial to learn how to download and install Cheat Engine to hack flash games.

The best way to keep rats out is by making it difficult and unappealing for them to come inside. Keep your house clean and free of anything that a rat might want to eat. Rats can fit through very small opening so go on the defensive and keep rats where they belong.

When smartphones were first getting popular, apps were much more limited in scope. Because of that, it was easier to find better programs to do what was needed. Now, in the App Store alone, there are nearly two million apps for you to choose from. When you're just looking for an app that will work well for the task at hand, two million is a lot to sort through.

The Apple Watch is rapidly becoming a standalone device that you can use without an iPhone or internet connection, and Deezer and Spotify have just helped make that even more true by adding support for offline playback on the watch.

Throughout Thursday's virtual Snap Partner Summit, Snapchat's parent company made a profound statement: If you use Snapchat, you're a creator.

Apple released the newest update for iPhone, iOS 14.5.1, today, Monday, May 3. The update (build number 18E212) is the first since iOS 14.5, which Apple made available one week earlier on Monday, April 26.

If you do a lot of typing every day — writing reports, essays, emails, and whatnot — we can guarantee your day would be improved by taking less time to do it. Thankfully, we've found a super-smart AI-powered tool that will do just that, and right now, you can get an amazing 52% off a Lightkey Pro Text Prediction Software: Lifetime Subscription for the sale price of just $79.99 (regular price $169).

These days, the only thing your eyes view more than your phone's home screen is the backside of your eyelids. So it goes without saying that whatever picture you have as your background gets old pretty fast.

Most iPhones are more than capable of shooting crispy, high-quality video, perfect for any TikTok account to use. But if you're serious about the platform, especially in the long-run, you don't want just any iPhone. Instead, you'll want to pick up an iPhone 12 Pro or 12 Pro Max.

You may be wondering what exactly makes the Pixel 4a's camera so great. Compared to its predecessor, it has the same Sony IMX363 sensor and no additional hardware. Well, beyond stellar image processing, it also has several great new features that Google has added since they released the Pixel 3a last year.

With bans looming or already happening across the world, TikTok still remains one of the most popular, entertaining, and addicting apps you can download right now. The problem is, browsing TikTok can be a bit painful at night since everything outside of the video feed uses a bright white theme. Thankfully, dark mode for TikTok is here, but there's a catch.

Lossless quality isn't for everyone. If you can't distinguish between lossless audio and other formats, you probably but don't need it. But if you're a musician who's sharing ideas with bandmates or a journalist interviewing people for a video, you might want the best possible quality, which is what lossless offers. And you might not know it, but the Voice Memos app on your iPhone supports it.

AirPods are not only a great way to listen to music on your iPhone, but you can also use them as a headset for phone calls, videoconference, Siri, voice memos, audio messages, and more. While each 'Pod has a built-in microphone, they aren't used simultaneously, and your AirPods will automatically choose which to use. If you want to only use the mic from one 'Pod or the other, there's a way to do that.

Since its original release as a spreadsheet program called Multiplan in 1982, Microsoft Excel has become the world's premier business software. If you think that it's only good for spreadsheets, you haven't been paying enough attention.

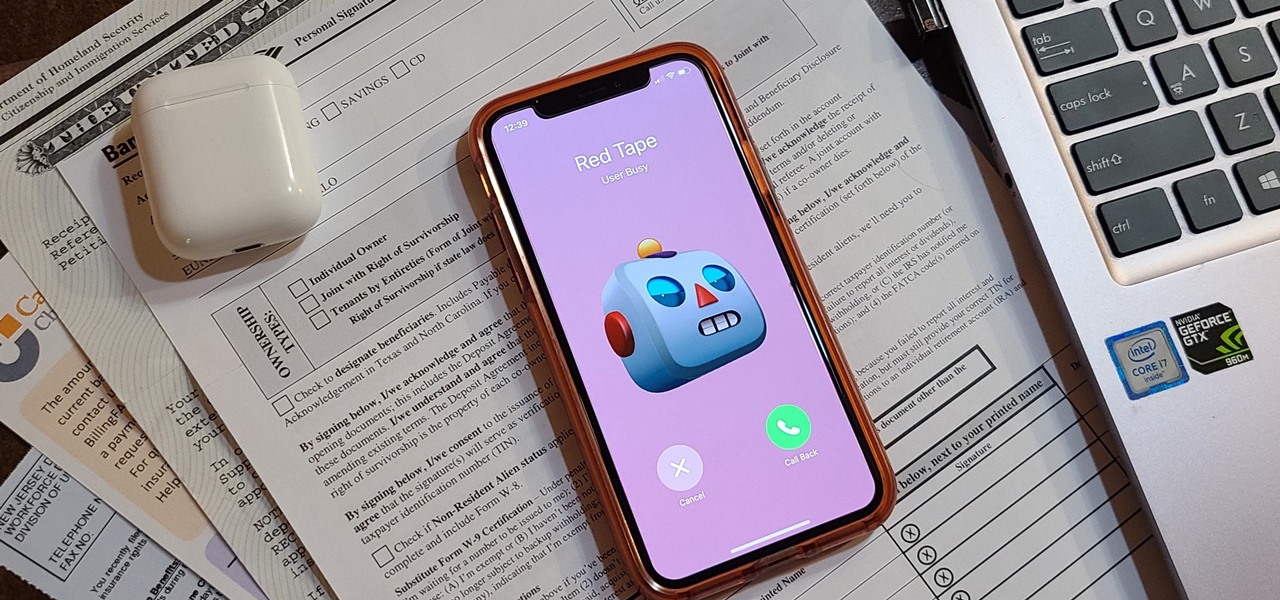
Even under normal circumstances, it's almost impossible to speak to a representative for a government agency or company in just one try. Many systems will put you on hold for long periods or ask to call you back when someone is available, but there are still some out there that just give you the busy signal over and over again. In those cases, there's a jailbreak tweak that can help.

With more digital content than ever, the search feature on smart TVs is essential. But typing is such a terrible experience when you're forced to use voice dictation or peck around with the remote control. Thankfully, there's a better way.

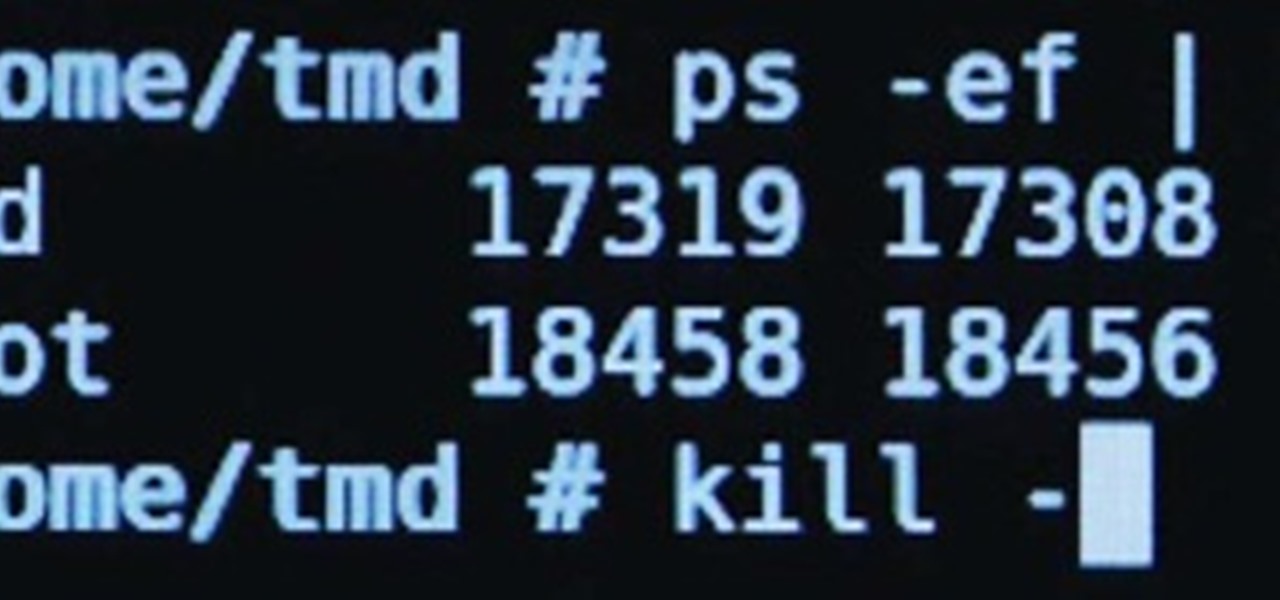
File permissions can get tricky on Linux and can be a valuable avenue of attack during privilege escalation if things aren't configured correctly. SUID binaries can often be an easy path to root, but sifting through all of the defaults can be a massive waste of time. Luckily, there's a simple script that can sort things out for us.

No matter how many camera improvements a phone adds, you're always better off using manual mode. Known as "Pro Mode" on the Galaxy S20, this feature can remove Samsung's pre- and post-processing from photos, putting you in total control.

Choosing which programming language to learn next can be a truly daunting task. That's the case regardless of whether you're a Null Byter just beginning a career in development and cybersecurity or you're a seasoned ethical hacking and penetration tester with years of extensive coding experience under your belt. On that note, we recommend Python for anyone who hasn't mastered it yet.

The 2020 iPhone SE had been through the rumor mill for a long time, but Apple finally unveiled the second-generation iPhone SE on Wednesday, April 15. While it doesn't sport the 4-inch design of the original SE, it combines a small form-factor with modern specs. The big question, of course, is when and how you can get your hands on one.

It's finally here. After years of rumors and speculation, Apple unveiled the new iPhone SE on April 15. While it doesn't have a 4-inch display like the original SE, it's the smallest new iPhone you can buy today, with the chipset of the iPhone 11, 11 Pro, and 11 Pro Max. So, when can you get your hands on it?

With the Wigle WiFi app running on an Android phone, a hacker can discover and map any nearby network, including those created by printers and other insecure devices. The default tools to analyze the resulting data can fall short of what a hacker needs, but by importing wardriving data into Jupyter Notebook, we can map all Wi-Fi devices we encounter and slice through the data with ease.

For those not used to it, working from home can be a difficult transition. Everything around you can be a distraction, and distance from your boss and coworkers means less pressure and incentive to get things done. So it's not surprising to see a major drop in productivity during a period of self-quarantine, but your phone can help you stay on track instead of sidetracking you.

SSH, or the secure shell, is a way of controlling a computer remotely from a command-line interface. While the information exchanged in the SSH session is encrypted, it's easy to spy on an SSH session if you have access to the computer that's being logged in to. Using a tool called SSHPry, we can spy on and inject commands into the SSH sessions of any other user logged in to on the same machine.

It's not hard to let the new SARS-CoV-2 strain of coronavirus put pressure on our minds. Fear of catching COVID-19 is never far from the topic of conversation. But it doesn't have to be that way. If you're struggling with anxiety, stress, depression, or any negative emotions due to the virus's effect on our lives right now, you might find some solace in meditation.

With every new Galaxy flagship release comes the age-old dilemma: do I choose great hardware or great software? For years, Samsung has given users the best components available on any smartphone. The problem is the software is an acquired taste. But there is something you can do about it.

Smartphones are more like computers than actual telephones. Unfortunately, thieves, hackers, and other bad actors know this and are always looking to make money off your personal data. Thankfully, your Galaxy S20, S20+, or S20 Ultra has tools to combat these threats — as long as you know where to look.

Using a strong password is critical to the security of your online accounts. However, according to Dashlane, US users hold an average of 130 different accounts. Memorizing strong passwords for that many accounts is impractical. Fortunately, password managers solve the problem.

As fun as Twitter is, it can also quickly turn scary. Anonymous, aggressive, and troll accounts can attack you for your tweets and stalk your every move. While you could make your profile private and block users, there are lesser-known privacy and security features that you can switch to improve your safety online.

As long as you're on the internet, you can be hacked. With an estimated 2.65 billion social media users, these apps are prime targets for hackers.

Whether you're trying to become an influencer or just want to share better photos and videos, the best camera to start with is your smartphone. It is likely the only camera you always have on you and it's probably capable of excellent pictures and video capture. But with a little help, it could definitely be better.

Hashes are commonly used to store sensitive information like credentials to avoid storing them in plaintext. With tools like Hashcat, it's possible to crack these hashes, but only if we know the algorithm used to generate the hash. Using a tool called hash-identifier, we can easily fingerprint any hashes to discover the right Hashcat mode to use to retrieve a password.

Web application firewalls are one of the strongest defenses a web app has, but they can be vulnerable if the firewall version used is known to an attacker. Understanding which firewall a target is using can be the first step to a hacker discovering how to get past it — and what defenses are in place on a target. And the tools Wafw00f and Nmap make fingerprinting firewalls easy.

Apple hasn't refreshed its text tones on iPhones since iOS 7. That's six years of the same sounds. And while text tones like Bamboo and Hello have undoubtedly aged like fine wine, that's still too long to live with the same old sounds day after day. Let's take matters into our own hands — let's make our own text tones, right in Music on macOS 10.15 Catalina.