Your Apple Watch is a fantastic tool that can help you perform daily tasks on your iPhone. Notifications get filtered through it, you can respond to messages on it, and you can even use Apple Pay to purchase goods and services. Your Apple Watch is also a valuable asset when it comes to finding your lost iPhone, too.

Thanks to the popularity of casual gaming on smartphones, handheld gaming consoles like Sony's PlayStation Vita have been on the decline. But if you own a new PlayStation 4, the Vita is a nice thing to have, since you can easily connect it to your PS4 for Remote Play.

Ever wish you could see in the dark? Well, you can't but this how-to will show you a way to build a device to help you out. You will need light polarizors, a flashlight, and a digital camera. Make an infrared night vision device, just follow along with the steps in this video tutorial. Now you can see at night!

Today's the big day for all Apple fans to start updating their devices to the new iOS 5, which has many improved features compared to its iOS 4 predecessor.

You will need a jailbroken iPhone to make this work (won't work for iPod Touches, sorry). When you get the MyWi app from Cydia, you can turn your iPhone into a mobile hotspot using the 3G network. You can even set up your new hotspot to have a password and protect it. This connection will be a little slow, and is dependent on your reception as well. But now you can take an Internet connection with you wherever you and your iPhone go!

Since it's introduction, iPhone has become the standard for design and ease of use, redefining what's possible on a mobile phone. And now with iPhone 3G, this revolutionary device gets even better, offering even more advanced capabilities. iPhone 3G works with fast 3G cellular and wi-fi networks around the world to keep you connected wherever you go. With its integrated GPS technology iPhone 3G makes it even easier to find where you are and where you're going. iPhone 2.0 software includes sup...

This video will show you how to subnet using CIDR notation. If you're curious about how to determine networks, subnet masks, broadcast addresses and what makes a host range valid. A great video for anyone currently studying computer networking technology.

This video will teach you how to hack a WEP wifi network on a Mac. You'll need to follow the link, grab the prog and follow the steps. It's not too hard, so give it a try. Remember, stealing is illegal!

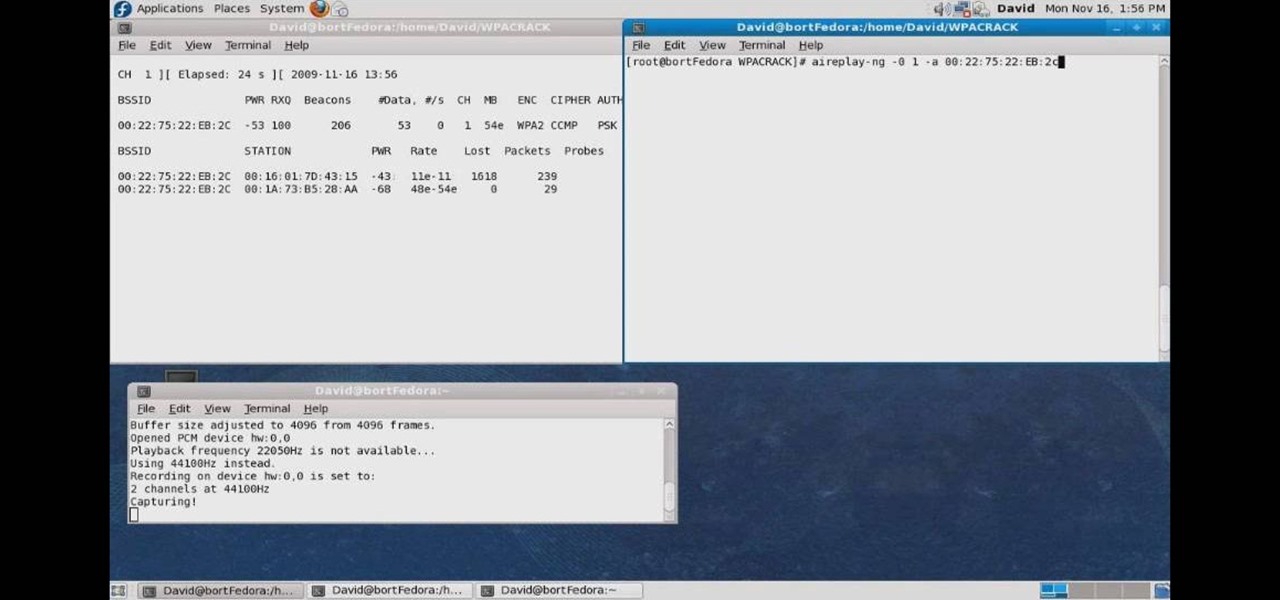
In this how to video, you will learn how to crack a WPA encrypted wireless network. To do this, you will need the Air Crack package for Linux. First, disable the wireless adapter and enable monitor mode. Next, identify the channel in the wireless network and Mac address. Once you have this, you can listen to the traffic coming to and from this point. Wait for the handshake or disconnect something in order to force it to reconnect. From here, you are ready to perform the attack. With any encry...

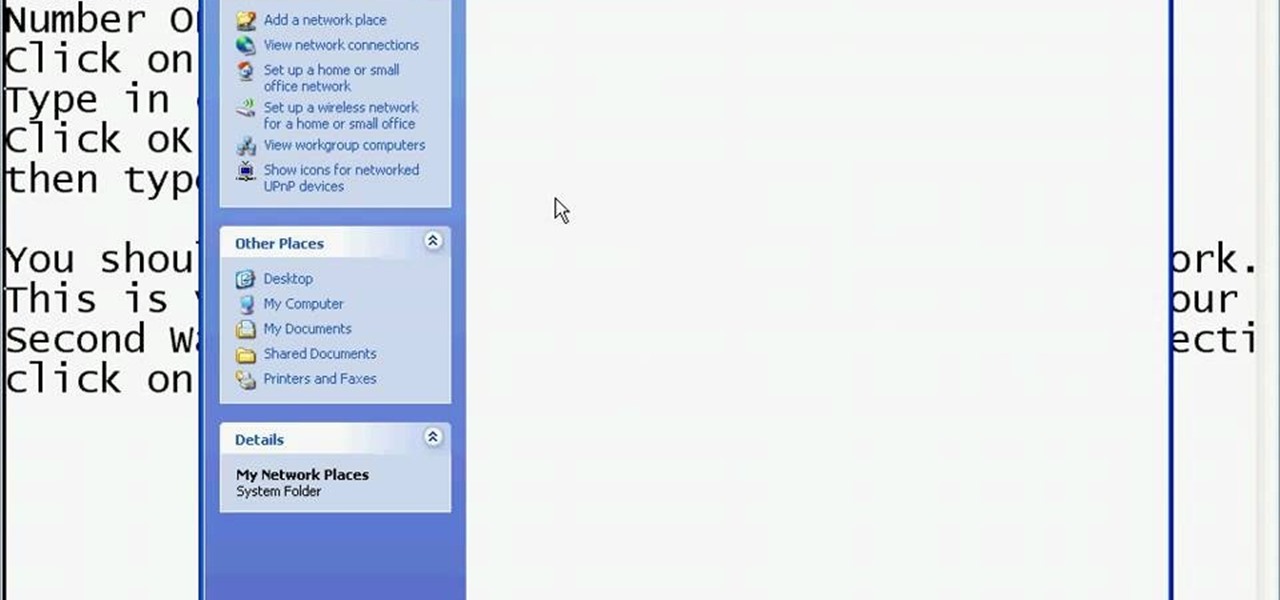
This video shows you the method to find if someone else is using your Internet connection. There are two methods for this. The first method involves opening the start menu and click on 'Run'. Type cmd in the text box which opens as a result of clicking on 'Run'. Type NET VIEW at the command prompt. This will show all people using your network. The second method involves going to Start menu. Go to Connect to and Show all connections. Click on My network places. Click on 'View workgroup compute...

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to map networks with Spiceworks.

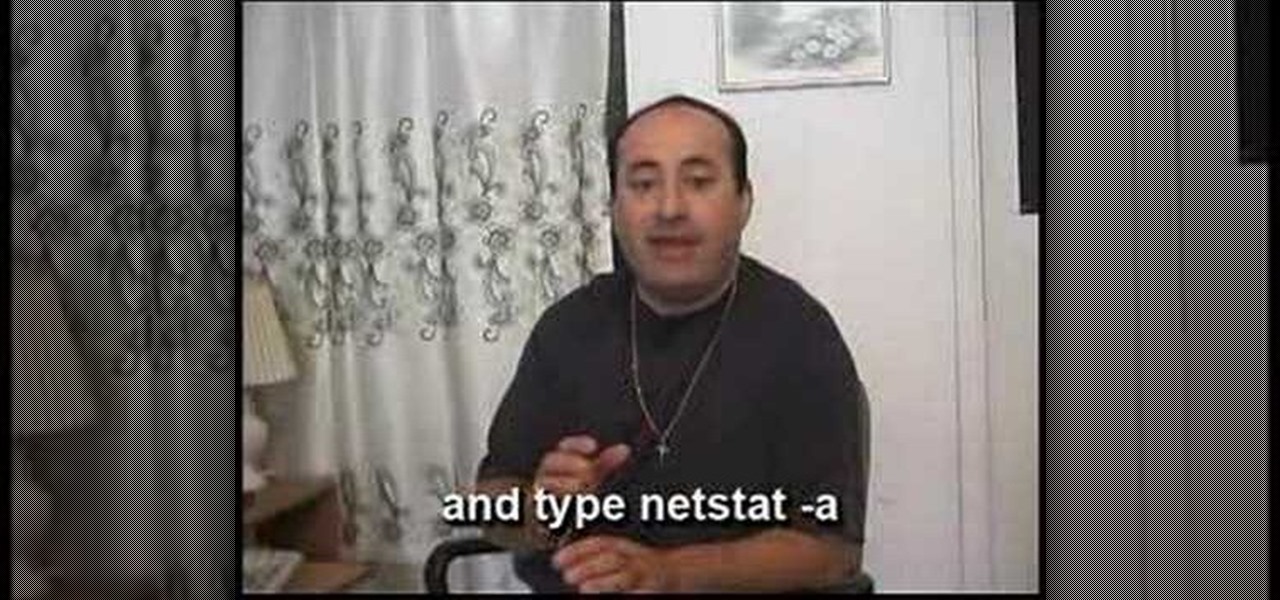
Want to see whether your PC is being accessed by hackers? Netstat (network statistics) is a command-line tool that displays network connections (both incoming and outgoing), routing tables, and a number of network interface statistics. It is available on Unix, Unix-like, and Windows NT-based operating systems. This video tutorial presents a basic introduction to working with the netstat tool. Determine whether you've been hacked with this how-to.

Nmap ("Network Mapper") is a free and open source (license) utility for network exploration or security auditing. Many systems and network administrators also find it useful for tasks such as network inventory, managing service upgrade schedules, and monitoring host or service uptime. Nmap uses raw IP packets in novel ways to determine what hosts are available on the network, what services (application name and version) those hosts are offering, what operating systems (and OS versions) they a...

Anyone can set up their own wireless network. All you need is a little know-how. You will need a computer with wireless capability, a high-speed modem, a wireless router, and a broadband internet connection. Don't get tied to the wall; a wireless connection will allow you to move the computer freely around your home and still get an internet connection. Watch this video tutorial and learn how to hook up a wireless network at home.

Tekzilla shows you how to troubleshoot network woes with ping and traceroute.

The team at Magic Leap just got a millennial-style boost with the announcement that financial news network Cheddar is coming to the Magic Leap One.

Another massive piece of the mysterious augmented reality puzzle known as Magic Leap fell into place on Wednesday as AT&T announced that it will be the exclusive launch carrier for the device.

The conversation of which operating system is most secure, macOS vs. Windows, is an ongoing debate. Most will say macOS is more secure, but I'd like to weigh in by showing how to backdoor a MacBook in less than two minutes and maintain a persistent shell using tools already built into macOS.

Samsung's 2016 line of smartphones has a new update, at least for the devices on AT&T. The update brings the Galaxy S7 to version G930AUCS4BQL1 and the Galaxy S7 Edge to version G935AUCS4BQL1. Here's what's on the table.

With Virtual Network Computing, you don't need to carry a spare keyboard, mouse, or monitor to use your headless computer's full graphical user interface (GUI). Instead, you can connect remotely to it through any available computer or smartphone.

Some of us woke up at the KRACK of dawn to begin reading about the latest serious vulnerability that impacts the vast majority of users on Wi-Fi. If you weren't one of those early readers, I'm talking about the Key Reinstallation Attack, which affects nearly all Wi-Fi devices.

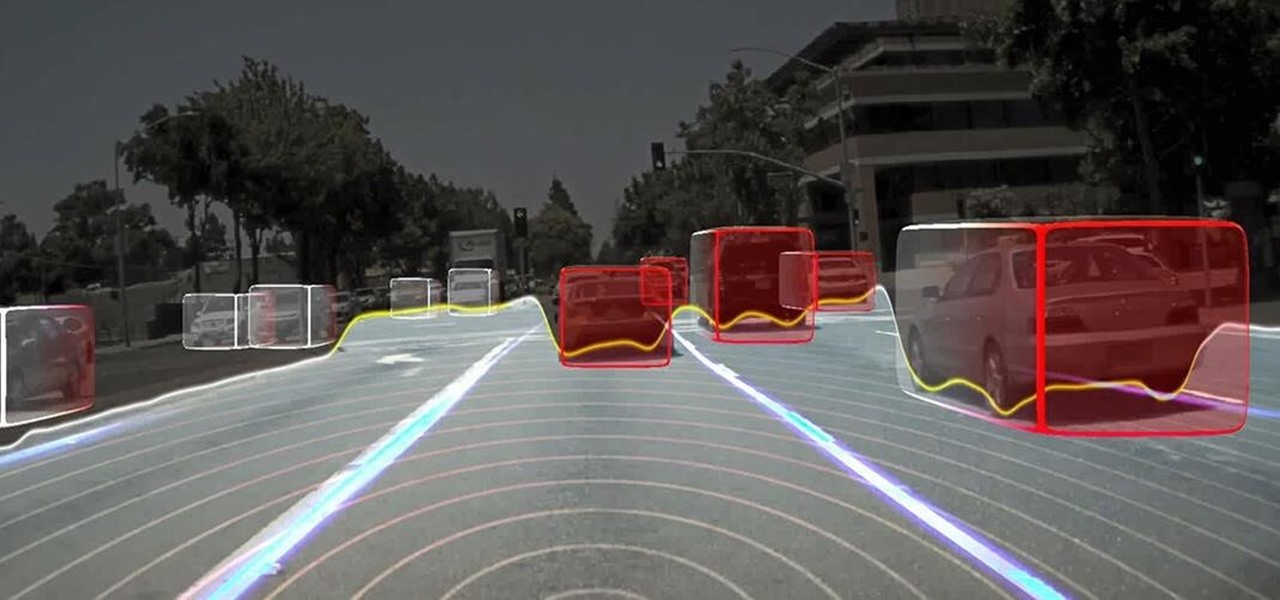
Long before Nvidia figured out how to embed neural networks in its graphics processor units (GPUs) for driverless vehicles, it and other chipmakers were already making the same kinds of devices for 3D games and other apps.

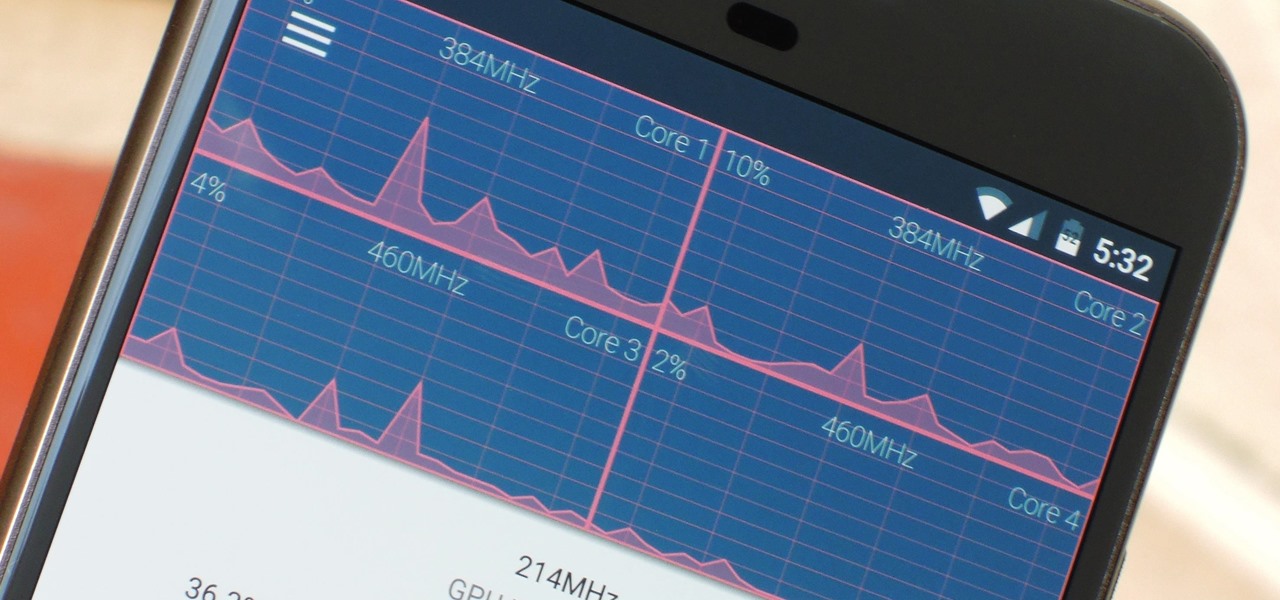
The Google Chrome browser does mostly everything well and integrates nicely with other Google services, but it's not exactly renowned for speed. With a rooted device and the aid of an app called Kernel Adiutor, however, you can make Chrome as nimble as some of the fastest browsers on the market.

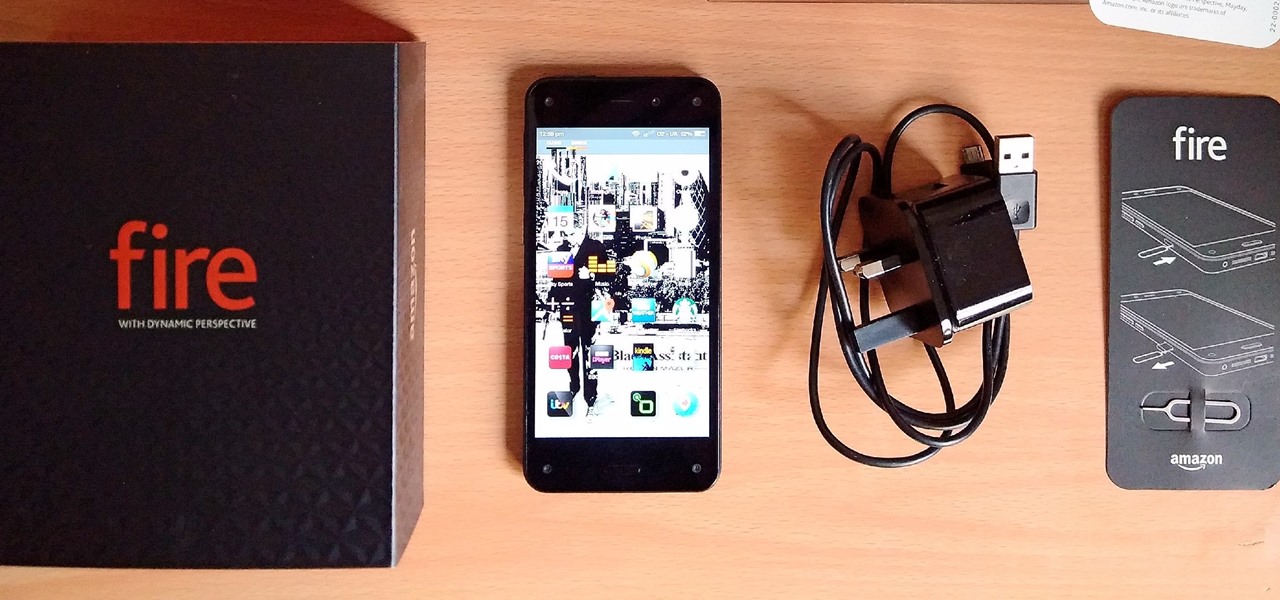
Amazon's first venture into the wireless phone market was a crash and burn moment — and that's us being kind. Their FirePhone went down in flames almost instantly, no pun intended.

The Pixel and Pixel XL come with an awesome data-saving feature called Wi-Fi Assistant that automatically connects to open internet hotspots, then creates a secure VPN on your device to keep your data safe.

Welcome back my networking geeks. In this part we are going to keep discussing about IP Addressing and I hope after you finish reading it you will become an IP wizzard.
Greetings null-bytians. Say you have been able to penetrate your neighbour's AP, and of course you had spoofed your MAC address. Now you go on and test to see with excitement if the password really works and the MAC is still spoofed. You login successfully and you browse the web forgetting to check what your current MAC is. Well, if you may do an ifconfig command, you will see that your permanent MAC is being used. Oh!! and guess what, ... your real MAC has been logged. Even though there is t...

When I tried to set up an eviltwin for a MitM-constelation in kali 2.0, I couldn't provide internet to the victim. The origin was the brctl bridging. I have read many tutorials but all of them where explained in backtrack and older versions of kali. So i was searching for a solution without using brctl and this solution will be explained now. This will just work on unencrypted wireless-environments.

These days, that pocket-sized computer we call a smartphone is home to your entire digital life. But with the onset of mobile payments and online banking, the line between your virtual world and the physical realm is becoming increasingly blurred.

T-Mobile's "Uncarrier" initiative has done wonders for my wallet and my data usage. Before I had to deal with being throttled down to 2G speeds after passing my data limit, but thanks to their unlimited data plans, I'm free to use as much LTE data as I possibly can. The only downside is, when sharing data through a mobile hotspot (tethering), T-Mobile imposes a 5 GB limit (which was recently upped to 7 GB for some).

Most smartphone games are clichéd and mundane, but every now and then a mobile game will appear with a new concept or idea that sets it apart from all the rest. While other developers continue to regurgitate the same old "winning" formulas, developer Sebastian Goszyla is changing how we play.

At last month's I/O event, Google demonstrated a set of cool new features that were said to be coming to the Chromecast soon. While we may not be able to set custom backgrounds or cast content without being on the same WiFi network just yet, the biggest feature of them all has started rolling out to devices today: Screen mirroring.

Samsung is helping photographers in getting more utility out of their cameras with their new Samsung Smart Camera App. With it, your device becomes a powerful viewfinder for your Samsung camera, allowing you to not only frame shots, but control multiple aspects of the camera, right through your phone.

Newer smartphones are more power hungry than ever before, and the Samsung Galaxy Note 2 has a mighty appetite for amps that only Jenny Craig could possibly curb. On average, your Note 2 (or other Android device) lasts for what, a day, maybe two days before dying. Mine barely lasts 8 hours! This is thanks to all of the apps running in the background of your phone, even when you're not using them, eating through all of your CPU, leaving nothing but crumbs.

UPDATE (February 26, 2014) Yesterday, the U.S. House of Representatives passed H.R. 1123 with a 295-114 vote decision. The ruling repeals the 2012 Library of Congress (LOC) decision that limited the ability to legally "unlock" your smartphone (see below).

It doesn't really matter what kind of cell phone you have—battery life is one of the most important features for any electronic device. We've written tons of articles on how to get better battery life from your Android, iPhone, Kindle, and more, but we've never really covered Windows Phones before—until now. The Nokia Lumia 920 and other devices running Windows Phone 8 suffer from battery problems just like any other mobile device. So, if you've got one in your hands that can't seem to make i...

As a multitasker, I've embraced the hustle and bustle that has filled my life. I'm constantly doing several things at a time, while looking for shortcuts to finish all of these things quicker than before. I brush my teeth with my cell phone in hand and drive to work with breakfast in mouth—I spare no time. Well, now there's an application for the Mac users among us that can help take some of the stress out of doing a thousand things at once.

Sharing screens is a great way to showcase projects, photos, or videos without having to download and upload those files on the other devices. This is made easy with AllSharePlus. You can download the AllSharePlay application for your Samsung Galaxy S III or Tab 2 right here. If you would like to download it for sharing on your laptop, you can visit the Samsung website. For now, the desktop app is only compatible with Windows XP or Windows 7 and the devices shown above. Nevertheless, it is gr...

Several people have been reporting Wi-Fi problems after updating to iOS 6 on both iPads and iPhones. The connection might work sometimes, but it usually cuts out or takes forever to connect to anything, only to time out shortly after.