Want music now? Not keen on downloading software or suspicious files to get it? This is a handy media trick from Tinkernut on how to torrent audio files without downloads. Stream music torrents without having to download any torrent software using Bitlet.org .

You may have lost your files but you needn't loose hope, too. In this episode of Lab Rats TV, Andy and Sean show you how to recover your deleted data (and your marriage!) using oranges. For detailed instructions on recovering your own lost data, take a look at this tech how-to.

This Windows XP video tutorial offers an explanation of how to use a little-utilized and known trick that gives you the power to rename multiple files both quickly and with ease. For more, or to get started batch renaming files yourself, take a look!

The tarbuck knot is a non-jamming knot, great for when the rope will be bearing a heavy load, and shocked with sudden weight. Form the loop around the winch then make a serises of turns around the standing part in a clockwise direction. Bring the running end down to the base of the runs and make another clockwise turn finishing off with a figure eight through the exiting strand from the top turn. Watch this video knot-tying tutorial and learn how to tie a tarbuck knot.

This fitness how to video discusses a few standing poses that might work for tight hamstrings and hips. Ask any non-yogi office worker to sit down on the floor and cross his legs, and 9 out of 10 times, his knees will be way off the floor and his back will be hunched up like Quasimodo. If your hips are really tight, your average yoga class will only help you make small gains. In order to double or even triple your progress, keep going to class, but take ten minutes each day and practice the p...
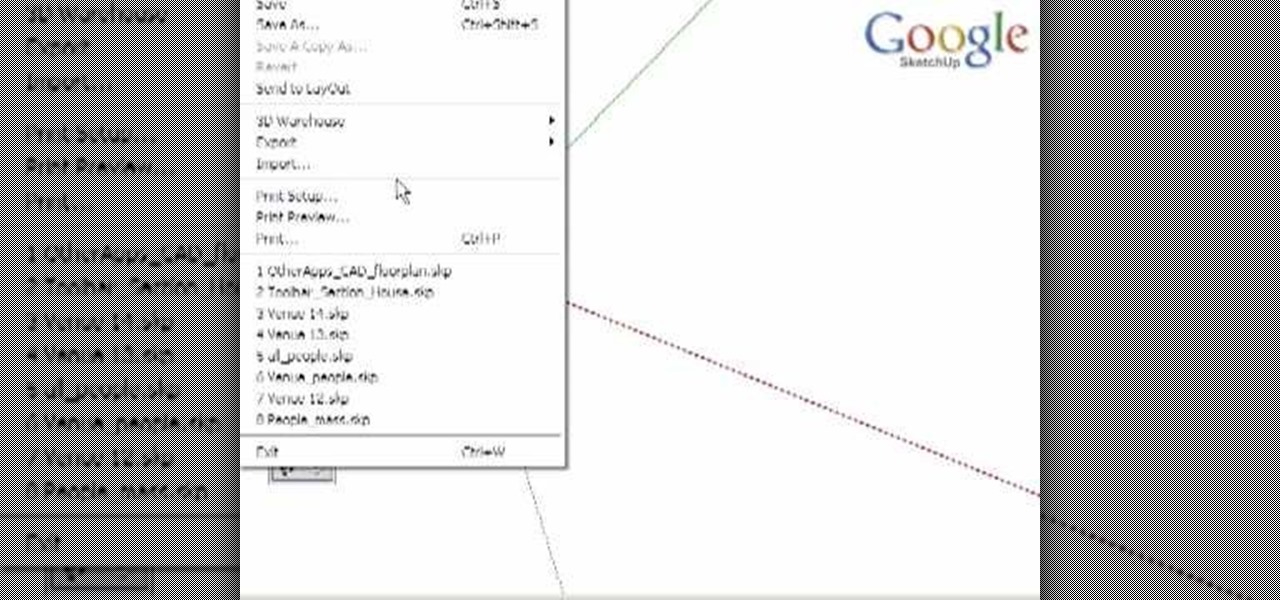
There are varied approaches to using SketchUp with CAD files. This video series presents one method we suggest as it is quick and creates a good clean SketchUp model.

Cast iron skillets are the original non-stick "Teflon" coating. An iron skillet seasoned properly will keep food from sticking, and its is great for browning and easy to care for. And good cast iron cookware will last a life time. Cast iron skillets have been handed down from generation to generation. Rita's favorite cast iron skillet was handed down from her mother and is at least 100 years old.

Want to send a 100MB file via e-mail? How about 1GB? This how-to video can help you do it, and it will cost you nothing. Watch this helpful internet tutorial video to learn how to email large files for free.

This tutorial video will show you how to make an adorable greeting card that has a hole in the middle for storing files. this greeting card it great for any occasion and means so much more because it's hand made.

Watch this software tutorial video to learn how to quickly unzip archived files using the program WinZip. WinZip makes unzipping and unarchiving archived files quick and easy, and this how-to video provides helpful tips on how to use the program.

Using Windows Media Player, you can share files among a group of computers and easily access files regardless of where the media is stored. See how to share files in Media Player.

Working in Photoshop and not sure how to save your files? What ARE all those extensions and what exactly are the differences. Well, this video breaks it down so you'll know just how to save your precious work.

File collaboration is one of the best integration features between Office 2003/Office 2007 and SharePoint. These task panes allow you to access and modify content in a SharePoint site from within Office without having to navigate to the site using your browser. The feature is available in the following Office 2003 and Office 2007 applications: Word, Excel, Microsoft Project, OneNote, PowerPoint, and Visio.

Is your hard drive filled to the brim but your not sure which files or file is hogging up all the space? Well check out jDisk for a visual representation of those space hogs.

How does Lightroom handle the process of going between itself and Photoshop? Where are the PSD files and what do we do with them? Check out this video and learn more about psds files and working with them in Lightroom.

Your gynecologist has recommended that you undergo surgery to remove vaginal fibroids. But what does that actually mean?

Watch this video to learn an easy way to FTP (file transfer protocol) files using the Safari browser.

I show you a great way to take your beautiful .avi files and turn them into much smaller files that are great quality as well. And you don't have to buy extra software to do it!

Learn how to record audio from video files (even Flash .flv files or Youtube videos) using the Windows sound recorder. All of the software used in this tutorial comes bundled with Windows.

Are you tired of having a bunch of files on your computer that you cannot get rid of? Find out how to use Windows notepad to remove unwanted files from your pc.

Have you ever seen a DOCX file, and don't know how to open it? Or you have a DOCX file, and want to convert it? Watch Chris' video to find out more about DOCX now.

You have an assignment due, whether it's homework for school or a project for work, but you've only got a few hours left. There's no way you're going to finish in time and do a good job, and you don't want to turn in anything incomplete or half-assed. While it may seem you're out of luck, there's a simple way to buy yourself more time.

You may be familiar with image-based or audio-based steganography, the art of hiding messages or code inside of pictures, but that's not the only way to conceal secret communications. With zero-width characters, we can use text-based steganography to stash hidden information inside of plain text, and we can even figure out who's leaking documents online.

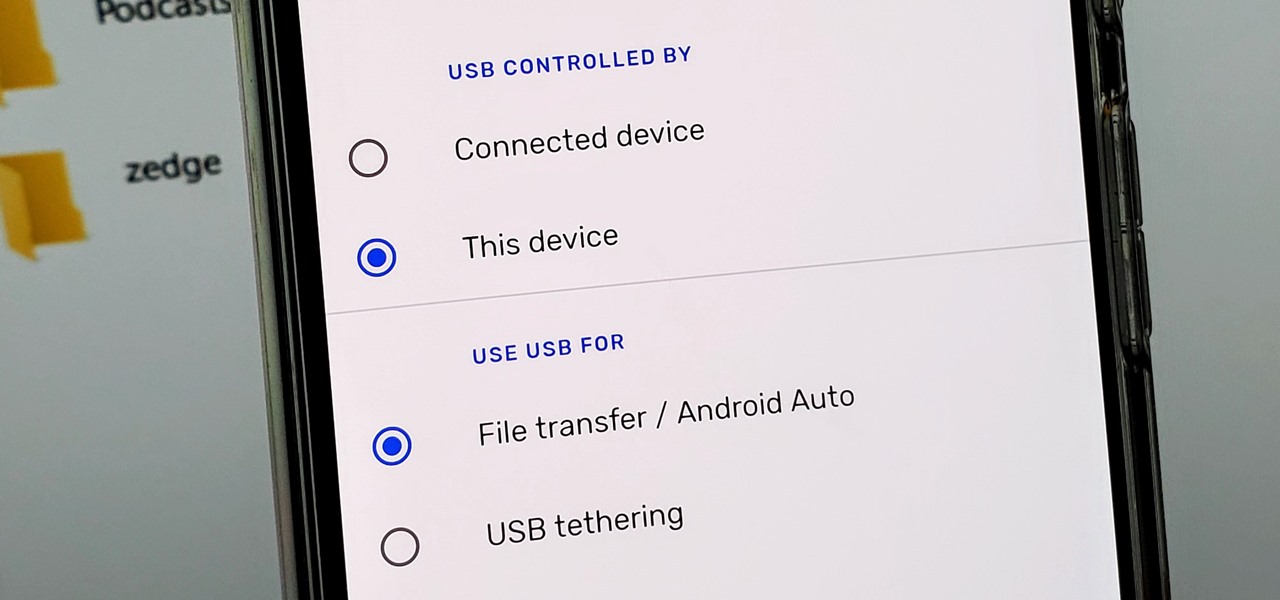
Back in the earlier days of Android, you were able to connect your phone to a computer, and it would mount automatically. This meant once the USB connection was made, your internal storage would pop up on the computer and you could go about your business. But recent versions of Android changed that to help increase security.

Your phone is loaded with contacts you've collected over the years. They're an asset, and you should use your library of connections outside the confines of your mobile device. Luckily, your Pixel uses a standardized medium to store contacts that can be used by the likes of LinkedIn, Outlook, Hubspot, iCloud, and more.

The Files app was first introduced to the iPhone with the release of iOS 11. In the two years since its unveiling, we've enjoyed a more desktop-class experience since there's finally a decent file manager for mobile devices. That said, there was always one major issue with the Files app, an issue iOS 13 solves for good.

Who's ready to let future Facebook augmented reality smartglasses read their brain? Well, ready or not, the tech giant is making progress in the area of brain control interfaces (BCI) by funding research.

Firewall solutions for macOS aren't impervious to attacks. By taking advantage of web browser dependencies already whitelisted by the firewall, an attacker can exfiltrate data or remotely control a MacBook, iMac, Mac mini, or another computer running macOS (previously known as Mac OS X).

It's easier than you might think to hack into Wi-Fi routers using just one unrooted Android phone. This method doesn't require brute-forcing the password, a Windows OS for converting PowerShell scripts into EXE format, a reliable VPS for intercepting hacked Wi-Fi passwords, or Metasploit for post-exploitation tricks.

Directory traversal, or path traversal, is an HTTP attack which allows attackers to access restricted directories by using the ../ characters to backtrack into files or directories outside the root folder. If a web app is vulnerable to this, an attacker can potentially access restricted files that contain info about all registered users on the system, their permissions, and encrypted passwords.

There once was a time in the Android rooting scene where we couldn't rely on using a custom recovery for all of our modding needs. Manual file flashing was very popular in the early days of Android before custom recoveries started taking over. With the rise of TWRP, it seemed like there was almost no need for manual file flashers; however, they appear to be making a welcomed return in a big way.

The newest version of macOS has arrived. While everyone's mind is being blown by Mojave's groundbreaking new Dark Mode, we'll be taking advantage of its insecure file permissions to establish a persistent backdoor with a self-destructing payload that leaves little evidence for forensics.

It's important to know who you're dealing with after hacking your target's MacBook. Getting remote access is simple, but covertly gathering information about the user and their system can be a challenge.

With all the web applications out on the internet today, and especially the ones built and configured by novices, it's easy to find vulnerabilities. Some are more perilous than others, but the consequences of even the slightest breach can be tremendous in the hands of a skilled hacker. Directory traversal is a relatively simple attack but can be used to expose sensitive information on a server.

With the macOS stager created and the attacker's system hosting the Empire listener, the malicious AppleScript can be designed and disguised to appear as a legitimate PDF using a few Unicode and icon manipulation tricks.

An attacker with shell access to a Linux server can manipulate, or perhaps even ruin, anything they have access to. While many more subtle attacks could provide significant value to a hacker, most attacks also leave traces. These traces, of course, can also be manipulated and avoided through methods such as shell scripting.

Despite concerns with SafetyNet, Google actually cares about root. Every phone they sell has an unlockable bootloader, so you can toggle a setting and send a Fastboot command, then start flashing custom firmware right away. The Pixel 2 and Pixel 2 XL continue this tradition, and now they have an official root method.

Steganography is the art of hiding information in plain sight, and in this tutorial, I'll show you how to use Steghide — a very simple command line tool to do just that. In addition, I'll go over a bit of conceptual background to help you understand what's going on behind the scenes. This is a tool that's simple, configurable, and only takes a few seconds to hide information in many file types.

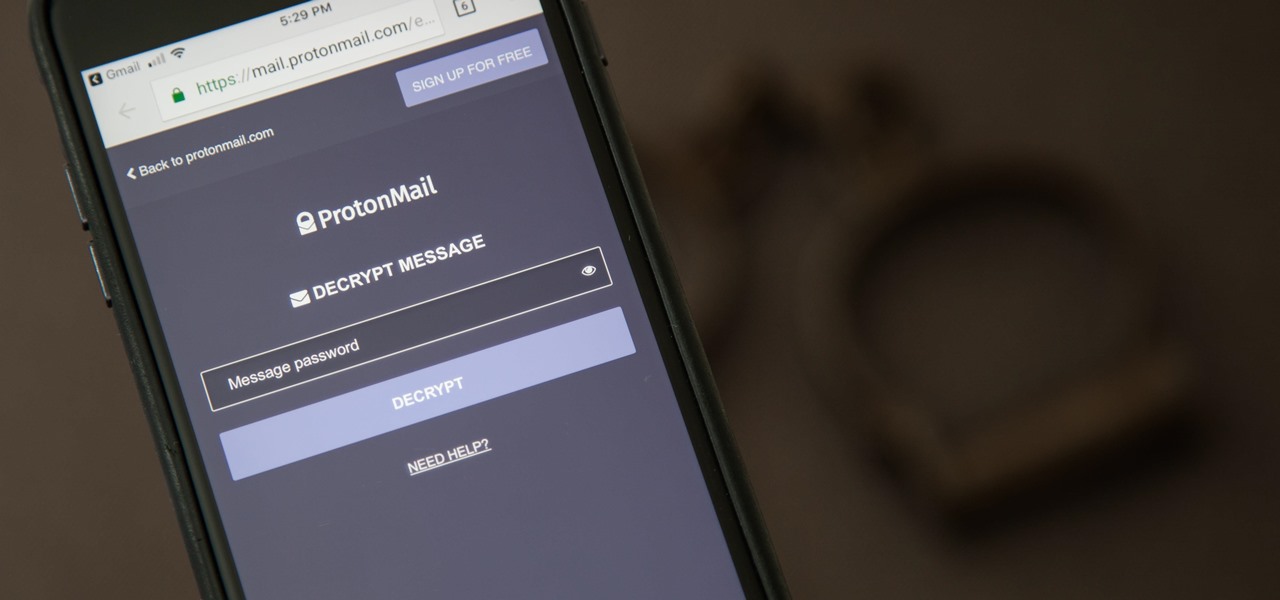
It can be hard to get all of your friends, family, coworkers, and acquaintances to jump on board with the more-secure email system ProtonMail, but that doesn't mean you can't still send them encrypted emails. Best of all, they won't even have to install any other apps or extensions to read or reply to the messages.

Cell phones have advanced rapidly since their inception. However, one frustrating aspect of our handheld computers is that we sometimes expect more than they can handle. We want smartphones to do all our PCs can do, but in many cases, that just isn't possible; especially when that comes to viewing and sending certain file types. WhatsApp is taking steps to bridge that gap now, by allowing users to send whatever kind of file they want, with one or two restrictions ...