Daemon Tools Lite is a program that helps you install a virtual drive, thereby loading an .iso image into the drive to be used at all times with ease. Download DAEMON Tools Lite by searching on the google. After you download, install the program successfully. This may take some time as the virtual drive needs to be installed. Once installed a small icon appears on the bottom right corner of the screen on the task bar. Right click on the icon and go to ‘virtual CD/DVD ROM’. Select a drive ...

In this tutorial we learn how to take off artificial nails at home. You will need: acetone, foil (in strips), finger file, nail clippers, buffer and cotton ball. First, tear your cotton ball into two pieces and completely soak it in the acetone. Now, apply the cotton ball over the nail and wrap the foil completely around the nail. Do this on each nail for around 1-2 hours. After this, remove the nail with nail clippers, if it's tough to remove, put the foil back on and let sit for longer. Now...

How to format a USB thumb drive to NTFS in Windows XP Go to my computer, click to the USB flash drive properties, in that click on Hardware, click on SanDisk Cruzer USB device, and then to its properties, then click to policies, in that click on the optimize for performance button, click ok. Again click ok on the properties icon.

In this how-to video, you will learn how to free up disk space on your Windows Vista computer. First, go to my computer and right click the drive that you want to free up space on. Next, click on properties. Click disk cleanup on the new window. Select which files you want to delete by checking the appropriate boxes. Once this is done, click okay. You can also select clean up in the other tab to free even more space. The first section will allow you to remove programs you do not need, while t...

In this tutorial, learn how to install superstar fonts like those used for Hannah Montana and High School Musical in Windows XP.

To insert a picture on your wiki page you first need to find the picure you want. Hit the edit button and click the image of the tree. Browse your computer to find the picture you want, click open, and then scroll down and click "upload" If your file does not upload, it may be becuase it is to large, or becuase it has strange character in the name. Try renaming the file or re-sizing it. Hit insert and resize image if neccisary. You can right click and go to image properties to change many thi...

In this video, we learn how to delete hidden driver viruses. First, scan your computer with anti-virus and try to delete the virus that is harming your computer. If you have done this and your anti-virus can't delete it, download HijackThis from Trend Secure. Go through the download stages and install the new software. Now, open up HijackThis on your desktop. Once it's opened, open up the "misc tools" section. After this, click on "delete a file on reboot". Now, write the virus location name ...

First you need the pre-downloaded game you want to burn. It will be in a ".XBE" file.You must have "Quix" downloaded off the internet. If you do a search for it via Google it will come up and you need to go through the download process.This will change it into a "ISO" that you can burn.Then go to Google and you need to find an "ISO" that fits your computer.Then you must run the "ISO" file through the "Quix" system that you downloaded. Now insert your Blank disc and burn the "ISO" onto the dis...

This video tutorial from dproxisback presents how to download and install Handbrake DVD ripping tool.To avoid installation problems, carefully choose application version for each type of computer and operating system.Open your internet browser and visit http://handbrake.fr/?article=download web page.Choose correct version for your type of operating system (MacOS, Linux, Windows).Download and install the application. Run Handbrake once it's installed.Click File-Select Source. Browse for your f...

Is your Outlook inbox starting to seem overwhelming? No problem! In just a few minutes you can corral that growing pile of e-mail by using the 'archive' feature. Have a look at this video and learn how to use this handy option and clean up the mess in your inbox.

Need some extra space on your computer? Grab those folders and zip 'em! Watch this tutorial and learn how to consolidate your folders into a single zip file, saving you space and keeping you organized.

If you're serious about keeping your diary for your eyes only then you might have to take some drastic steps. There are some very clever ways to distract from, encrypt, hide, or disguise a diary if you're willing to put in the work.

Have you ever wondered how to open a .ISO file without the need for the disk? Well with Daemon Tools, and this tutorial, you can learn just that. What you will end up doing is creating a virtual drive on your computer, and mounting the .ISO image onto that virtual drive. It's as simple as loading up the program, right clicking on the icon in your task bar tray, clicking on the empty drive, and mounting any .ISO image you like! In no time you'll be playing your favorite game, or program withou...

Follow along as we are shown how to make a movie in Windows Movie Maker. -To begin, open up Windows Movie Maker, if you do not have this you can download it at http://www.microsoft.com

Linuxjournalonline teaches you how to use GRUB to dual-boot Linux and another operating system. You need to go to etc/default/grub and edit that file. Here you can configure the time it needs to start booting a system and what OS to boot. You need to be root to edit this configuration file. Don't forget to run update-grub to force an update of grub.cfg. And this is the end of the short process needed to configure Grub 2 for Linux.

Computer forensics expert Steve Burgess gives a highly informative tutorial on how to recover deleted emails in Outlook and Eudora. The most critical factor affecting the recoverability of deleted web-based emails, according to Steve, is whether the PST file, which stores all the emails, has been compressed after the mail was deleted. If this hasn't been done it is possible to hack into this file and recover the deleted email. Text-based emails, like those one creates on programs like Eudora,...

This how-to video shows you how to download music from MySpace in good quality. This method is one hundred percent free and legal as long as you don't share the files with anybody other than yourself. The video shows viewers everything from accessing the artists music page of which you would like to download songs from, to clicking the get files button and getting your music. If you use this method of downloading music you will bypass paying a dollar per song and still keep things legal.

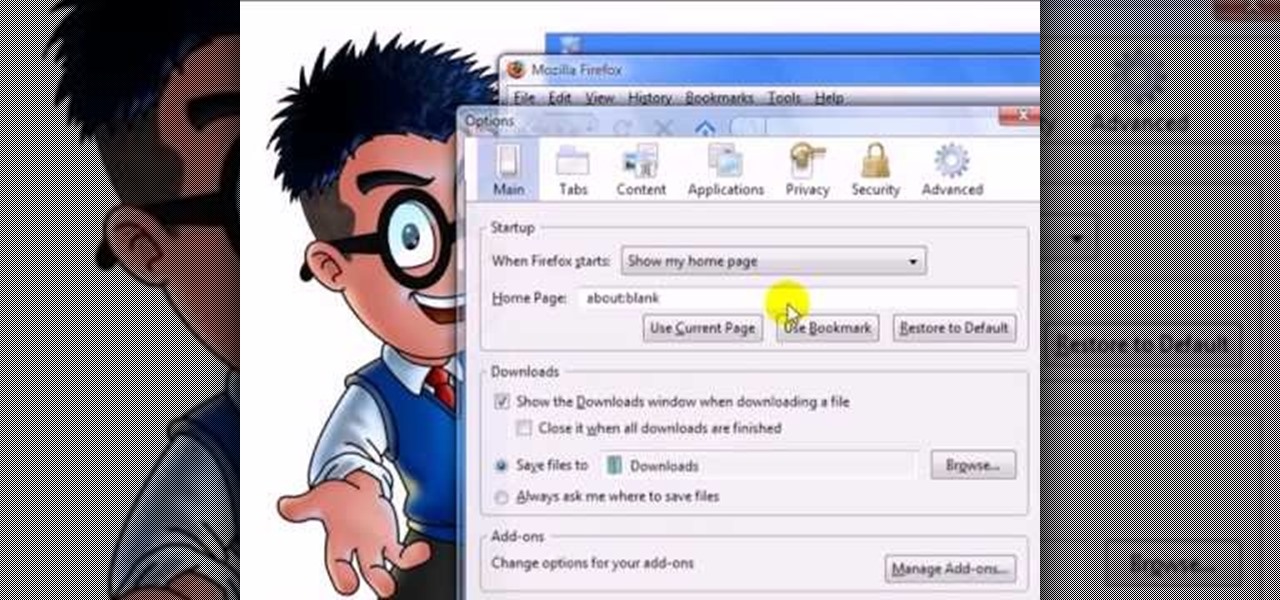
With this useful video, you will learn some tips and tricks about how to delete your web browser history, passwords, cookies, also cache form data and temporary internet files.

Can't wait until you get home to get onto MySpace? This video gives step by step instructions on how to try and unblock MySpace while you are at school or on a server that does not allow access to the site. This video does not have narration, but has written instructions on how to get around blocked sites with out using a proxy server. However, you have to have access to the system 32 files for this tutorial to work, and accessing these files does go against a lot of network policies.

It's no secret that Apple's Notes app supports attachments such as photos, videos, and web links, as well as other file types like PDFs, word documents, spreadsheets, locations on a map, and audio tracks. While images, videos, and document scans are simple to add on an iPhone or iPad, other file types aren't as easy — at least until you know how.

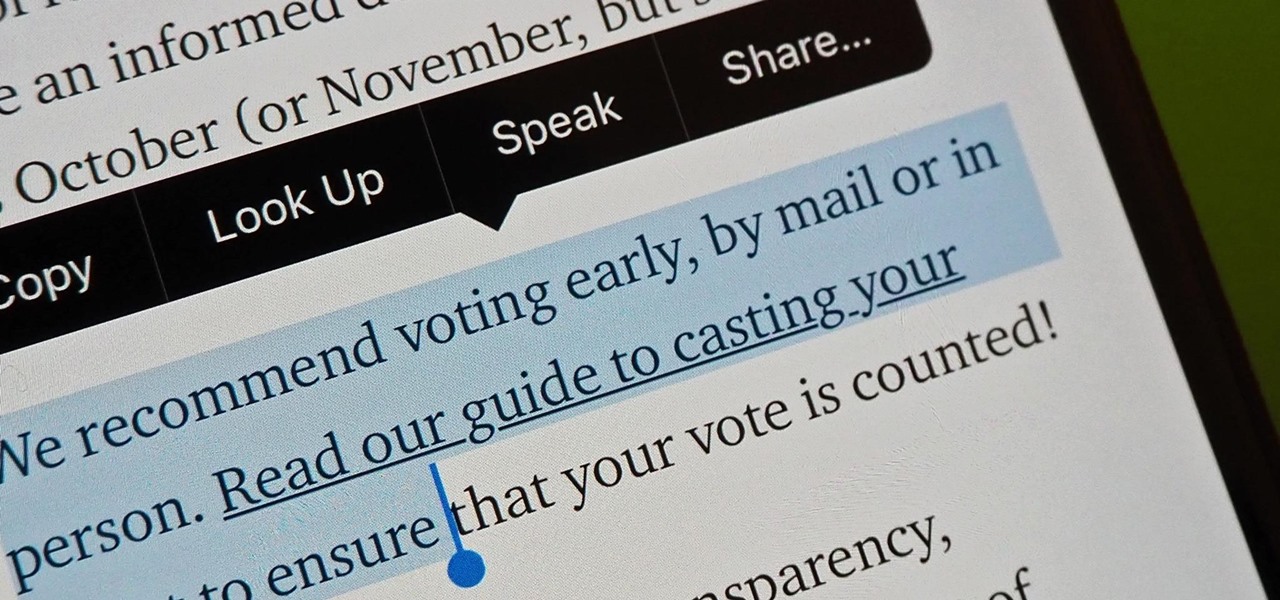
Highlight text, tap "Copy," open the app to paste the text into, long-press or double-tap where you want it, and hit "Paste." That's probably what you do when you need to copy text from one location to paste into another on your iPhone. It's a tried-and-true method, but there's a hidden trick for saving and sharing text on iOS that cuts down on that lengthy copy-paste process.

Samsung uses their own SamsungOne font for their Galaxy lineup. But if you're coming from an iPhone or another Android device, you might not love it. With the help of this mod, however, you're sure to find a font that's right for you.

As a native of Alabama, Apple CEO Tim Cook has a special place in his heart for the state. He also empathizes with the struggles that African-Americans have historically faced in the state, particularly during the 1950s and '60s civil rights era.

If left unattended, a hacker with a USB Rubber Ducky and physical access to the computer can infiltrate even the most secure computer. Such attacks often go undetected without the use of a tool like USBRip, which can provide you with assurance that your device hasn't been compromised.

Samba can be configured to allow any user with write access the ability to create a link to the root filesystem. Once an attacker has this level of access, it's only a matter of time before the system gets owned. Although this configuration isn't that common in the wild, it does happen, and Metasploit has a module to easily exploit this security flaw.

Did Google CEO Sundar Pichai kill Google Glass for non-enterprise users? That's the obvious first question following news that non-enterprise Glass users will no longer have access to Google's core apps after February 2020.

Windows 10 passwords stored as NTLM hashes can be dumped and exfiltrated to an attacker's system in seconds. The hashes can be very easily brute-forced and cracked to reveal the passwords in plaintext using a combination of tools, including Mimikatz, ProcDump, John the Ripper, and Hashcat.

Have you ever heard someone else's iPhone ringing and thought it was yours? Of course you did. iPhone ringtones are iconic, but not varied. If you're using one of the more popular iOS sounds, you'll likely encounter it in the wild multiple times. Why bother, when you can create your own custom ringtones right on your Mac.

Lenovo has done a great job preventing leaks of their new Moto RAZR. We've seen a few images here and there, but for the most part, we knew very little about the long-rumored phone. But with the announcement date just around the corner, an FCC filing has given us a look at the new RAZR from almost every angle.

While MacOS computers have been spared from some of the most famous malware attacks, there is no shortage of malicious programs written for them. To keep your computer safe from some of the most common types of malware, we'll check out two free tools. These tools can automatically detect ransomware encrypting your files and watch for unauthorized access to your microphone and camera.

Microsoft.com is one of the most extensive domains on the internet with thousands of registered subdomains. Windows 10 will ping these subdomains hundreds of times an hour, making it challenging to firewall and monitor all of the requests made by the operating system. An attacker can use these subdomains to serve payloads to evade network firewalls.

KeePassX, 1Password, and LastPass are effective against keyloggers, phishing, and database breaches, but passwords managers rely on the operating system's clipboard to securely move credentials from the password vault to the web browser. It's within these few seconds that an attacker can dump the clipboard contents and exfiltrate passwords.

The next libSSH or OpenSSH exploit may be just around the corner. Keep your SSH service out of Shodan's database before hackers find new ways to bypass the password protecting the server.

With the number of web applications out there today, it comes as no surprise that there are just as many vulnerabilities waiting for hackers to discover. Finding those vulnerabilities can be a difficult task, but there are plenty of tools available to make the process easier. While it won't help find any zero-days, web scanners such as Uniscan will detect common vulnerabilities.

Augmented reality startup Nreal was a hit at this month's CES event, with some even calling the device a worthy challenger to the Magic Leap One.

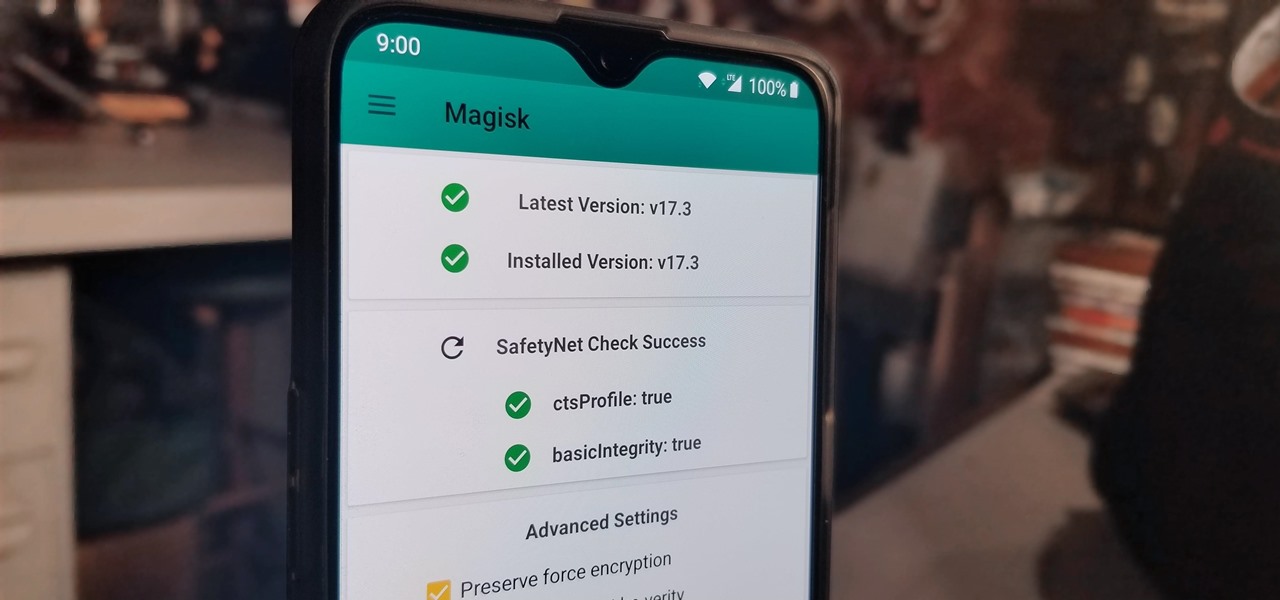
With the recent launch of the OnePlus 6T, the company continues to impress us with some of the best phones when it comes to the rooting and modding. OnePlus has made it easy enough to get up and running with the rooting process as fast as possible. The OnePlus devices follow the same core principles Google uses for their Pixels, which is excellent news for both the user and the development side of things.

In a previous tutorial, we were able to place the Mona Lisa on vertical surfaces such as walls, books, and monitors using ARKit 1.5. By combining the power of Scene Kit and Sprite Kit (Apple's 2D graphics engine), we can play a video on a flat surface in ARKit.

The ability to execute system commands via a vulnerable web application makes command injection a fruitful attack vector for any hacker. But while this type of vulnerability is highly prized, it can often take quite a bit of time to probe through an entire application to find these flaws. Luckily, there is a useful tool called Commix that can automate this process for us.

A powered-off MacBook can be compromised in less than three minutes. With just a few commands, it's possible for a hacker to extract a target's password hash and crack it without their knowledge.

Although the Essential PH-1 got off to a rocky start, thanks to steady updates, it has slowly become one of the best Android phones to come out in recent years. For $499, the Essential Phone is a cheaper Pixel, receiving updates almost as soon as the Pixel lineup does. What's more, you get a phone with an easily unlockable bootloader, which is the first step to rooting.