In case you haven't figured out already, our government is always on the move to figure out new ways to extend their control. The CISPA, for one, is one of the best examples, along with "re-education" programs, and racial divide (Trayvon). What I've noticed in the past few months is that their new "ideas" are coming out at an increasingly alarming rate.

Solar panels are an amazing invention. Catching energy from the Sun before it even enters Earth's food chain, photovoltaics are like an all-natural nuclear power plant. Unfortunately, the constituted parts of a solar panel are rare, valuable, and subject to the coercive forces of market competition.
Hey guys, remember the 'booms' in Clintonville, IN? Well, they were back the previous night. And they were louder than before. What's going on? The mayor and police would love to dismiss it as geological activity, but results show otherwise:

If Null Byte had a large Batman-like spotlight calling for help, we would definitely be using it right now. However, we don't, so this is my digital equivalent. Information security is a huge field, far too much for one man to cover adequately, so I need your help!

We're officially seeking Null Byters on a weekly basis who are willing to take the time to educate the community. Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (IF up to par, of course). There is no need to be intimidated if you fear you lack the writing skills. I will edit your drafts if necessary and get them looking top-notch! You can write tutorials on any skill level, and about anything you feel like sharing that...

We're officially seeking Null Byters on a weekly basis who are willing to take the time to educate the community. Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (IF up to par, of course). There is no need to be intimidated if you fear you lack the writing skills. I will edit your drafts if necessary and get them looking top-notch! You can write tutorials on any skill level, and about anything you feel like sharing that...

Happy Monday to all of you out there, thankfully the Consumer Electronics Show is now behind us. It feels quite possible that a cold was caught by yours truly simply by reading the numerous reports of germs being spread from booth to booth on the show floor. I'll do my best to soldier on, in the meantime if you haven't already, you can experience the convention vicariously by reading my 'Best of CES' post here.

Our first look will be at scavenger hunt beginners. The youngsters. The ones some people say shouldn't even be doing a scavenger hunt (and maybe they're right). If you dare to put on a treasure hunt for people who can't tie their shoe, here is what you need to know.

Last week, we discussed whether Google should require you to use your real name for Google+ profiles. Google is working on eliminating fake profiles, and in the process, they've booted some real people, including actor +William Shatner. If you find out that your Google+ account has been suspended, you can appeal the suspension and get your profile reinstated.

Google+ is the most exciting new social network to come around this decade, and the only product with a chance of challenging the monopolies we know as Facebook and Twitter. As an Internet addict, I've joined every major social network there is - from Friendster (who?) to MySpace (so ugly) to LinkedIn (yawn) to Twitter (irritating) and Facebook (annoying to manage). Competition is delicious, especially between well-financed monopolies. Google+ really seems to have identified an Achille's heel...
Student group hopes to keep bikes on campus By Conrad wilton · Daily Trojan

Does that (hopefully somewhat correct) tune ring any bells? Here's a reminder: Once upon a time there were two Italian plumbers named Mario and Luigi. Mario and his sidekick resided in the Mushroom Kingdom, a monarchy ruled by the beautiful Princess Peach. Mario's mission: stop the villain Bowser from his numerous attempts to kidnap the lovely princess.

After 3,000 man hours and $100 grand spent, 49-year-old Randy Grubb of rural Oregon turned this old junker long-haul truck...

Today's WSJ takes a tour of Russian billionaire Andrey Melnichenko's 394-foot insanely luxe yacht, coined "A".

... Describing the style of John Bonham's drumming instantly conjurs up visions of the thunderous power he created. His contributions to rock music were revolutionary, and his talent unmatched and irreplaceable. You can only imagine Jimmy Page's reaction to first seeing him in 1968, ending his search for a new drummer to form a new band, the New Yardbirds (later renamed Led Zeppelin.)

LEGO technic builder Sariel presents a mighty impressive weekend project: a motorized LEGO hand that emulates actual human movement. This feat of plastic engineering runs on a combination of electric motors and pneumatic valves.

This extended period at home due to COVID-19 is the perfect time to try out new apps in the Play Store. But instead of buying premium versions, Google Play Pass will give you unlimited access to paid apps and games for about five bucks. And there's an even better deal now to help with coronavirus.

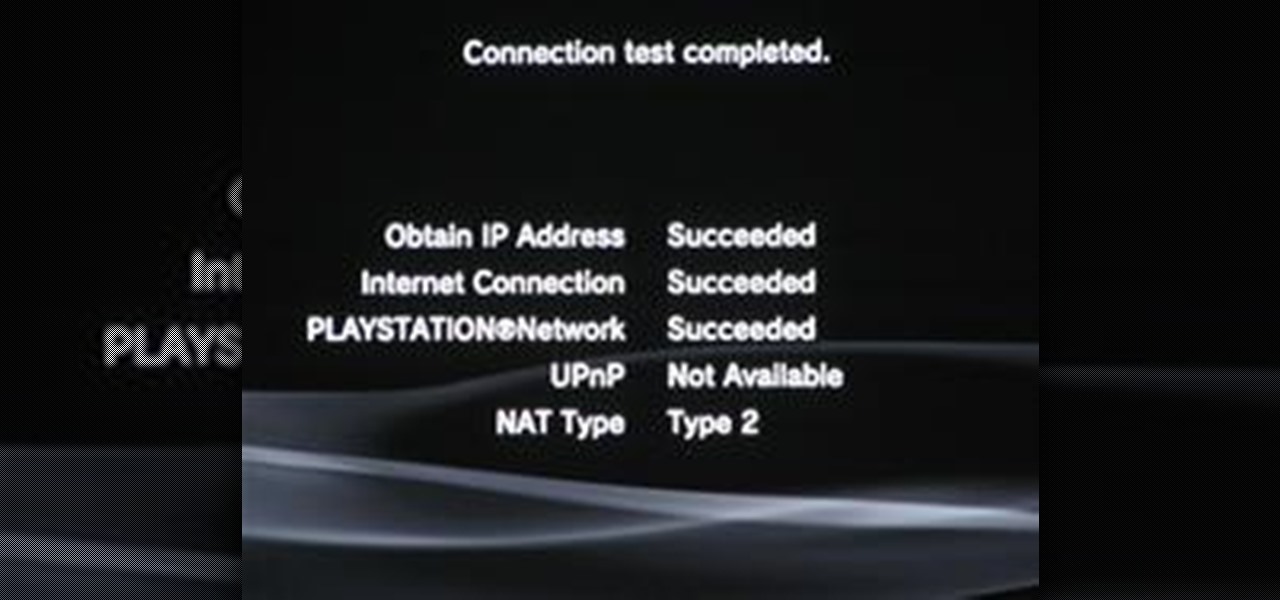
Despite the recent problems with the 1.04 update for PlayStation 3 gamers, Call of Duty: Black Ops remains a juggernaut for Activision in the gaming community, and its sales alone prove it.

At first, the Black Ops 1.04 patch seemed like a godsend. It was supposed to fix the horde of issues plaguing Call of Duty: Black Ops on the PlayStation 3.

Welcome to Compute & Conquer! This article may seem a little basic. We all have an idea of what a computer is but the fundamentals are necessary. Without knowing how something works, how can we determine a problem and find a solution when something goes awry? Way too often, I find myself helping someone with a very "easy to fix" problem on their computer. A problem which could have either been avoided or fixed had they had the basic knowledge of how to use a computer. Even worse, I've seen to...

Are you a big astronomy enthusiast? Do you have some amazing astrophotography pictures you'd like to share? If so, become a contributor over here at Astronomy World! We are looking for new moderators, along with contributors, to post pictures and videos, write tutorials and astronomy-related news articles, and even share updates on how your observing went!

Medicine, like the internet, is serious business. So when the text that appears on the labels of our medicine bottles makes about as much sense as an epileptic in a rave club, we can't help but take pause. Follow us on a journey of prescriptions and misdescriptions!

Last Friday's mission was to accomplish solving HackThisSite, Realistic 5, the fifth and last in my series of realistic hacking simulation missions. This time, telemarketers are invading people's privacy, and it was up to us to stop them! The job was to get root on the site and delete the contact database in order to return the right of privacy to its victims.

SSH is amazing, and we praise its existence on Null Byte for many reasons. Notably, it allows us to reroute our traffic through encrypted ports on our local host to be sent to its destination when on the go. You can even control your home computers remotely over a secure and encrypted connection. This is handy for a multitude of reasons.

Last Friday's mission was to accomplish solving HackThisSite, realistic 4. The fourth in a series of realistic simulation missions was designed to be exactly like a situation you may encounter in the real world. This time, we are told "Fischer's Animal Products is a company that slaughters animals and turns their skin into overpriced products which are then sold to rich bastards! Help animal rights activists increase political awareness by hacking their mailing list."

Do you need proxy access, but cannot have it for some reason? The most common perpetrator behind the issue is the network you're trying to access the pages from. Some networks will block websites, then go as far as filtering out all of the web queries for terms like "proxy" because it can get around their filter. Quick web proxies can be used for tons of other things, though.

You might be sitting there thinking that I'm crazy, but the truth is you're only partially right. You can get free text messaging for life, all for a cheap, one-time fee. But, how can that be possible? An exploit in AT&T's prepaid GoPhones is the culprit behind this sweet, oh-so rare opportunity for exploitation. The exploit grants a lifetime of free texting, assuming that the company stays afloat from now until the end of time.

Last Friday's mission was to accomplish solving HackThisSite, realistic 3. The third mission in a series of realistic simulation missions was designed to be exactly like situations you may encounter in the real world, requesting we help a friend restore a defaced website about posting peaceful poetry.

I have to say, the Xbox 360 controller is the best controller ever created. When I first held it back in 2005, I swore that the dudes working at Microsoft came over and took a molding of my hands because of how great it felt. The thing felt like it was born there.

The biggest struggle with flashing DVD drives on Xbox 360s has been the price tag of the probe to extract keys on some drives. The probe and kit is required to extract the DVD key, which is needed to perform a drive repair, flash, or backup of any kind. Who wants to pay big bucks for the "pro" kit and then get added to a huge waiting list behind a million other people looking to buy the same product? We can hack the same thing together at home!

Last Friday's mission was to accomplish solving HackThisSite, basic mission 10. This mission teaches us how to use JavaScript to manipulate cookies on poorly coded cookie-based authorization.

Here we are at week three of Edit on a Dime, the community for free and inexpensive apps for video, audio and image editing.

Friday's mission was to accomplish solving HackThisSite, basic mission 7, which required us to learn some basic Unix commands. If you have any prior experience using Unix commands, this should be a breeze for you if you sit and think for a second.

A little about myself and astronomy: I created this world because I love astronomy. I really, really, love astronomy. When I was ten, I went to a restaurant and saw a huge wall mural of the Andromeda Galaxy. At my house, we had a tiny refractor telescope. I knew this wasn't enough, so I bought (with help) an 8 inch Dobsonian reflector. I looked up one time to try to find something to look at and saw something fuzzy- the Orion Nebula. This is when I really got into using my telescope. I still ...

Hey all, I've introduced myself in the forum, but for newcomers, I'm former admin of Giveaway Tuesdays, and current moderator of Phone Snap!

First, we'd like to congratulate Marek Antozi, the winner of our very last Giveaway Tuesdays! Photo Challenge. Thankful for Dialogue is a concept most family members can relate to—the occasional stressful Thanksgiving bickering and inevitable resolution is not uncommon, after all. ;)

Hello, my fellow cell phonographers! In today’s day and age, cell phone photography is growing rapidly with the advancement of smartphones and the constant stream of new multi-featured camera phone and photo editing apps.

As many of you may have noticed, nearly every Google product (i.e. Gmail, Google search, etc.) has gone through a bit of a makeover since the release of Google+. Big blocky buttons and enormous font sizes are apparently the thing of the future, and with a cool JavaScript hack, you can have a goofy YouTube, too! Now, I'm actually just being a bit facetious, the new YouTube is really the only thing that I like out of all of Google's recent redesigns. It looks pretty sleek.

Welcome to Part 3 in my series on protecting your computer from prying eyes (Part 1, Part 2). In today's segment, we will be going over drive encryption using the TrueCrypt program on Windows OS. Drive encryption is a technique that masks your data with a cryptographic function. The encryption header stores the password that you have entered for the archive, which allows the data to be reversed and read from. Encrypted data is safe from anyone who wants to read it, other than people with the ...

Encryped traffic and tunneling is a must when away from home to keep you and your information safe. SSH tunnels can be slow, and are heavily encrypted. VPNs are an all port solution, and proxies are just not what we need in most cases. Then, there is Tor.