If you want to pull a small trailer with the Chevy Aveo, you are going to need some wiring for the trailer lights. This video will demonstrate how easy it is to connect a modulite circuit protected wiring harness. Now, even though you don't have a truck, you can run to the hardware store to pick up supplies and it will be safe, convenient, and legal.

Learn how to plant tulip bulbs correctly and protect them from critters. A garden expert gives detailed instructions.

Learn how to develop good pass blocking to protect your quarterback when playing football.
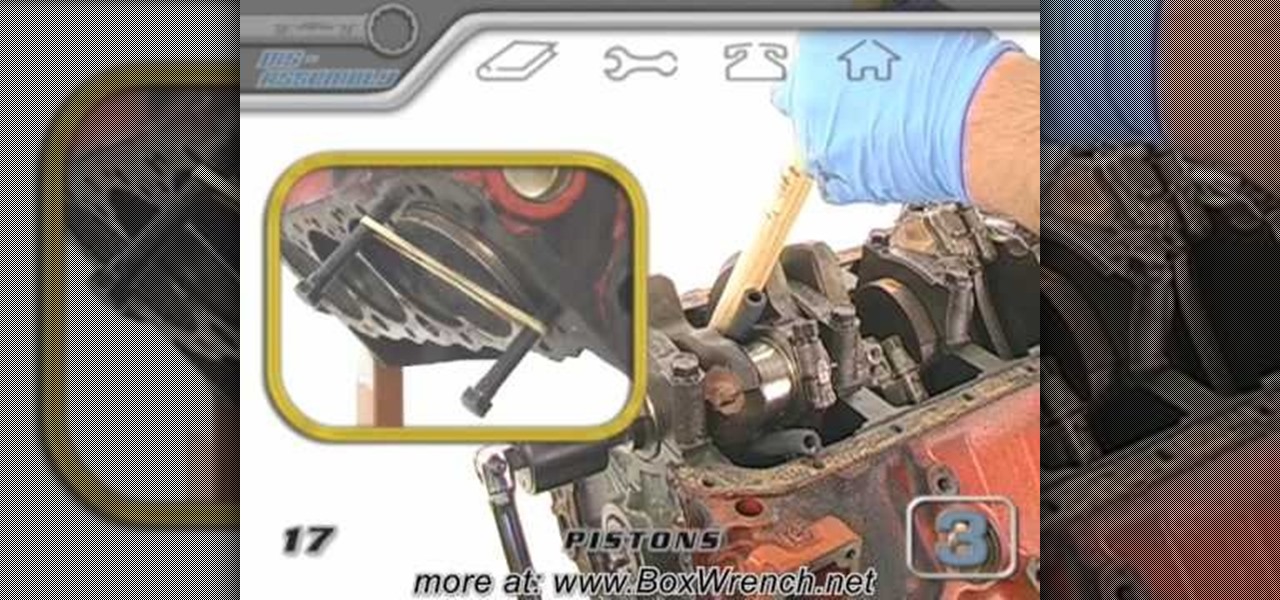
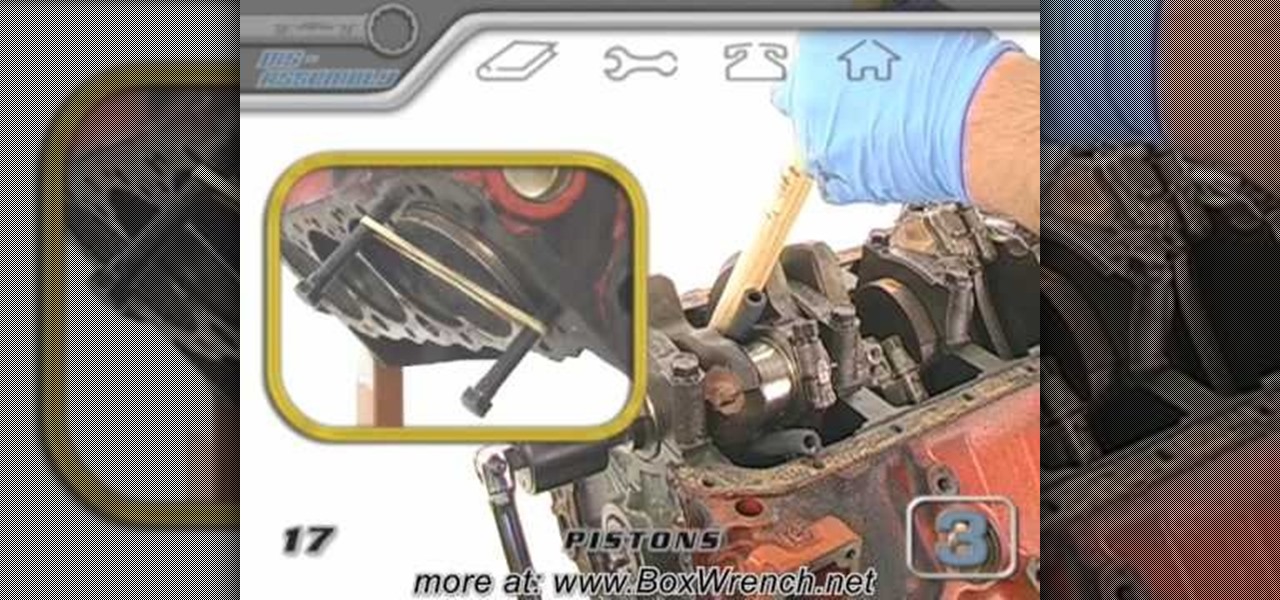
When you're ready to remove the pistons, start with the rod caps. You'll also get to see the crankshaft, rod bearings and journals for the first time and inspect them for damage as they come out. Great tips on protecting the cylinder bore while removing the pistons and connecting rods.

This video helps you to protect your computer against viruses and spyware often contracted when using peer to peer (p2p) networks like limewire, kazaa and emule.

To save energy, protect your garden, and keep warm during the winter follow these simple tips to winterize your home.

Reviews of products used to protect your home, family, and other pets. Also, we'll have a look at the legal side of pet damage in a rental property and how to prevent it.

Protect the kids from playground falls and mulch the plants at the same time! Landscape designer Michael Glassman spins his wheels finding inventive ways to use recycled rubber tires in the backyard.

This may sound like a terrible thing to show you how to do, but the Neistat Brothers are simply victims of bicycle theft who got fed up. They use their own bikes to show you how to steal a bike in NYC (in broad daylight) so hopefully you can learn from them, how to better protect your ride.

Protecting a new or young tree by staking it enables it to grow the strong root system it needs to secure itself in the ground. We will showyou how to stake a tree.

Microsoft Office files can be password-protected in order to prevent tampering and ensure data integrity. But password-protected documents from earlier versions of Office are susceptible to having their hashes extracted with a simple program called office2john. Those extracted hashes can then be cracked using John the Ripper and Hashcat.

When Google introduced the Pixel 3 on October 9th, one of new additions they briefly mentioned was the Titan M security chip. While they did talk about how it will improve overall security, they didn't expand on the number of changes it brings to the Pixel 3's security. Well, they finally shared more, and it's a pretty big deal.

Not all threats to our privacy come from hackers thousands of miles away. Often, we just want to keep our data safe from those around us, who may snoop in our phones or demand we reveal our secrets. That's where BlackBerry Locker comes in.

When BlackBerry made the move to Android OS, they were aware of the limitations it presented. Unlike with BB10, they didn't create the operating system and would have to deal with the vulnerabilities already included. As a result, they added numerous security enhancements, and at the heart of this is DTEK.

We know Android 9.0 will have the formal designation of Pie, following Google's age-old tradition of naming their OS after items you'd normally find on a dessert menu. And thanks to a slew of new features that centers around your overall security, P could also stand for Privacy.

It's no secret that you can protect notes on your iPhone with a password, but one thing that most people don't know is that you can actually set unique passwords for each note instead of a blanket password for all of them. It's not obvious at all in the Notes app, but it's easy to do once you've got the hang of it.

When it comes to your security, you want the best of the best. Why settle for mediocre service with something as valuable as your protection? Malware continues to make its way onto the Play Store, leaving millions of devices vulnerable. You need an app that will shield your devices from both the latest malware threats and threats nearby. And when it comes to antivirus apps, there is only one choice.

before I move on to more exciting areas in this series, I want to also point out some things to protect your information & how to not get DoXed.

Back in 2010, iOS developer Daniel Amitay developed a camera security app for iPhones that used an unlock screen almost identical to that of the iPhone.

The Fish Contamination Education Collaborative (FCEC) has made this video to reach the public about fish preparation safety, to make su. It's important to prepare fish in a certain way, because some species of fish have contaminants that pose health risks. Those contaminants are stored in the fatty portion of the fish, so by cleaning and cooking the fish in a certain way, you can reduce your exposure to those toxins.

Kipkay's ingenuity is enough to amaze us all, especially all of you indie filmmakers. These five tips for aspiring filmmakers will help you keep your sanity and avoid frustrating times. Have you ever got stuck in the rain while shooting? Have your recorder tapes ever gotten disorganized? Is your camera's display getting scratched up more than you want? Kipkay answers all of these questions with his five ingenious video tips.

New techniques may improve a swimming pool workout from Masters coach Nancy Kirkpatrick Reno. Before sticking a toe in the water, consider this advice: * Swim in a pool that's at least 20 to 25 yards long; those pools can usually be found at high schools and some gyms. A 50-meter Olympic-size pool is best, but not everyone has access to that. "If you're going to become a lap swimmer," Kirkpatrick-Reno says, "you can't go any shorter or you'll be constantly turning." An outdoor pool is prefera...

This week, Etsy How-Tuesday presents Kari aka ikyoto and Stella aka lookcloselypress of The {NewNew} York Team. Today we're going to learn how to screenprint our own snowflake gift wrap for the holidays. Kari and Stella remind us that recycling paper bags is a great source for materials for this kind of project.

They are after you from all over the globe. Looking for ways to exploit you. Ways to hurt you. Not political terrorists, but rather "info terrorists." Each month thousands of websites get hacked into and have hidden links inserted into the pages by people wanting their spam sites to rank highly in the search engines.

This video tutorial belongs to the software category which is going to show you how to convert a Word document to a password protected PDF file with NovaPDF. Go to NovaPDF and download the program and install it. It is a paid program. Select the word document that you want to convert and select print option. Under the name of the printer you will find novaPDF option. Select this and click 'preferences'. Now click on 'security' and select high level encryption. In the document permissions, sel...

If you're serious about keeping your diary for your eyes only then you might have to take some drastic steps. There are some very clever ways to distract from, encrypt, hide, or disguise a diary if you're willing to put in the work.

In this video tutorial, anyone who owns a Droid smartphone can learn how to better navigate their home screen. With this Droid phone tips, you'll be able to maximize your time and create shortcuts to your most used applications. The Droid's home screen in much like a computer's desktop; putting an icon on one of your Droid home screens allows you quick access to a program or app. There are numerous Android phones, but this video focuses on the "Droid" versions, but you may need to play around...

It's a timeless doggie no-no, and one that has been paradied in numerous dog scenes in movies: A plate of delicious fried, steaming food is left by the owner on the table. The owner then leaves for a brief moment. His dog, smelling the delicious goodness, seizes the moment and quickly jumps up, snatches a piece of chicken, and devours it under the table.

Pixel Perfect is the "perfect" show to help you with your Photoshop skills. Be amazed and learn as master digital artist Bert Monroy takes a stylus and a digital pad and treats it as Monet and Picasso do with oil and canvas. Learn the tips and tricks you need to whip those digital pictures into shape with Adobe Photoshop and Illustrator. In this episode, Ben shows you how to build an Egyptian Pharaoh's room in Photoshop.

Check out this strength trick from Revision3, Brian Brushwood and Scam School. We're back with another dirty trick, designed to teach you how to FAKE your way into (almost) duplicating the feats of the world's strongest men.

If you're concerned about someone accessing your OneDrive files, you may want to upgrade your protection by enabling fingerprint or Face ID unlocking. Your sensitive information deserves to be protected, and now you can do so easily. Worry no longer — if you need to let someone else use your phone, with a password-protected OneDrive, sneaky file grabbers will be out of luck.

Because of the way Google Play works, Android has a "bad app" problem. Google allows any developer to upload an app to the Play Store, regardless of if it works, how it looks, or whether or not it can harm users. Malware scanning happens primarily after apps are uploaded, and though Google has recently taken steps to safeguard users with its Play Protect program, you don't have to depend on them.

Ok, I have to admit, I drop my phone around 2–4 times a week. I'm horrible at protecting it and I've gone through my fair share of cracked phones. Most of the time, once the phone is cracked it's just easier to get an entirely new phone, rather than have to fight your phone provider for a fix.

Monday has been a big update day for Apple. Alongside the release of iOS 10.3, iWork has been updated across both iOS and macOS. The biggest change is the ability to unlock password-protected files with Touch ID, either on iPhone and iPad, or on the new MacBook Pro with Touch Bar.

Adding to the recent recent slew of bugs and issues within iOS 7, it now seems that emails sent with attachments are not encrypted, despite Apple's claims that they are.

Photobombing, the act of covert sabotage on a photographer and unsuspecting subject, can be a terror. This malicious and disingenuous art form has steadily grown since it first received significant coverage in 2009.

When you have a lot of equipment, dragging it everywhere with you can be a pain, especially when the weather's bad. Sure, you can put it in a camera bag, but a lot of them don't protect your stuff from water, and waterproof cases can get expensive.

Ipad is a revolutionary device from Apple with some amazing features. One of the major functions of Ipad is to serve as a E-book reader. Apple provides an application called Ibooks using which you can read ebooks on your device. You can also browse and purchase new ebooks using this applications. Launch Ibooks from your applications menu and it will take you to the collection of books that you already have on your device. Click the store button to visit the books store. From the store you can...

There's plenty of reasons why one would want to convert a webpage to a PDF document. And there's numerous ways on how one can convert that web page (HTML) into a PDF file. Check out this video tutorial on how to convert webpage HTML to PDF on Ubuntu Linux.

Check out this Scam School video on leanring the ultimate strength tricks. Bend frying pans and horseshoes with your bare hands! Watch Brian make you think he can use his bare hands to bend a horseshoe and to roll a frying pan!