In this article I will show you how to obtain victim's credentials without cracking any hashes. There are a couple of ways to perform this task (for example dumping the SAM file and cracking the NTLM hashes), but here I will explain how to do it using PowerShell and a bit of social engineering. We are going to create a fake login popup.

Hey readers! This tutorial will be the entry point for the introduction of buffer overflows. Something like requesting user input is a very common place for vulnerabilities to pop up and we will definitely have fun while trying to make programs crash. But for now, let's start with how we can get input from a user.

With the purchase of my new Apple Watch, the days of striving to be a James Bond-like spy have never been closer to fruition. Granted, talking to your wrist in public can look pretty pretentious, and I may very rarely do it, but let's get real—you look like 007!

Why I split it into two articles: I love images and I'm sure lots of us do. I decided to put in a lot of images as examples rather than have paragraph upon paragraph of boring text. Also, I don't think any of us like overly long articles; but if you think it's better to have it all in one article, let me know

I learned the hard way that boxed dyes just don't work well for me. A few months ago, I tried one that had a pretty name like "soft violet black." Sounds nice, right? What I ended up with was brown hair and hot pink roots. Trust me, it wasn't cute.

Want to secure your home? There are plenty of ways to go about it. You can make your doorbell send you a text if someone rings it while you're not home, or build a motion-triggered security camera. Even better, you can beat potential crooks at their own game by installing a door they can't even find.

For his thesis at Design Academy Eindhoven, artist/designer Tuomas Markunpoika Tolvanen created this incredible chair using tubular steel cut into thin rings. How did he get them to stay that way? He burned them. His project is called Engineering Temporality, and the inspiration came from his grandmother whose Alzheimer's disease is deteriorating her health and memories. Once he cut the rings, he laid them over an existing chair, only partially covering it. The fire acted as a varnish, creati...

Making cookies is one of the best things in life, especially around the holidays. There is nothing better than getting together with friends and family and bonding by baking cookies.

If you prefer glow sticks over candles during a power outage, then this how-to is for you! Although glow sticks are used as temporary light sources, there are other applications for them. Divers use them for night diving, fisherman use them to catch swordfish, and the military uses them for light markers, along with infrared versions used in conjunction with night vision devices. But with all these handy uses for glow sticks, the most popular is — recreational use, like dancing at raves, some...

Titlibo Nihaan shows us how to make Bo Kho(Vietnamese Beef Stew,in this video. The ingredients for this are,500 grams of beef,3 chopped shallots,1 small onion, thinly sliced,soy sauce,nuoc mam sauce,a bunch of fresh basil,2 red chillies,3 cloves of garlic,1 tablespoon lemon grass,1 tablespoon of turmeric powder,1 tablespoon of curry powder 1 tablespoon of brown sugar,4 star anise and a beef stock cube.In a small pan dry roast the star anise for 5 minutes.When cooled,gring them in a coffee gri...

To make a lotus out of a single sheet of paper, use a colored, square paper sheet with a different center color (optional). With the colored side facing outwards, fold the sheet diagonally in half creating a center crease. Open up and repeat the step with the other corner to obtain a center point. Carefully fold the 4 corners towards the center point to form a smaller square. Repeat the same procedure with this square. Flip over and repeat the same procedure over again. The next step is optio...

Karen Solomon shows how to make bacon. You need 2 1/2 to 3 pounds of pork belly with no skin or bone. Rinse the belly with water and pat really dry. Mix ingredients for cure which includes 1/2 cup sugar, 1 tablespoon blackstrap molasses, 1 teaspoon freshly ground pepper, 2 tablespoons kosher salt and 1 teaspoon curing salt. Curing salt may be obtained at local butcher shop or online at Sausage Maker. Curing salt helps preserve the color of the bacon and ensures no spoilage. Mix ingredients un...

Aluminum nitrate nonahydrate is a crystalline hydrate - a salt of aluminum and nitric acid - Al(NO3)3·9H2O. It's used for a variety of things such as antiperspirants, corrosion inhibitors, and petroleum refining, or… glow-in-the-dark powder. Watch this science video tutorial from Nurd Rage on how to make aluminum nitrate nonahydrate with Dr. Lithium.

This is chemistry at its best! Europium is the chemical element (Eu) which was named after Europe. Dysprosium (Dy) is a rare earth element of a metallic silver luster. Watch this science video tutorial from Nurd Rage on how to make europium and dysprosium nitrate salts with Dr. Lithium.

Farkle hacks, cheats, glitches. How to hack Farkle. Watch this video tutorial to learn how to play Farkle and Farkle Pro on Facebook. Learn about scoring and gameplay in Farkle. What's you highest score?

Watch this science video tutorial from Nurd Rage on how to get lithium metal from an Energizer battery. They show you how to get Lithium Metal from an Energizer Ultimate Lithium battery.

A light meter can prove to be an invaluable tool on any film set, allowing you to quickly and efficiently set lights and know the correct exposure values of those lights. Light meters were initially designed for still photographers and cinematographers can easily calibrate them to a given film stock speed for shooting film. But what about today’s digital cinematographer? I’m glad you asked. In this video tutorial you'll see how you can use a light meter to quickly and efficiently light a scen...

XSS Shell is a cross-site scripting backdoor into the victim's browser which enables an attacker to issue commands and receive responses. During a normal XSS attack an attacker only has one chance to control a victim's browser; however, the XSS Shell keeps the connection between the attacker and the victim open to allow the attacker to continuously manipulate the victim's browser. XSS Shell works by setting up an XSS Channel, an AJAX application embedded into the victim's browser, that can ob...

Trust is one of the most important aspects in a relationship. You can work on some trust building exercises and activities to strengthen your current relationships. Plus some of these activities are just fun.

PDF is a Portable Document Format, which is a popular format to represent documents and pass it over the internet. You can merge different PDF documents to obtain a single document. You can do this on your Mac, using the preview option. Preview does a lot more than the name suggests. You can actually merge PDF's and also rearrange pages inside the documents. There are some changes in the functionality in preview feature between the leopard and snow leopard versions. To use this first you will...

This video is provided by "Betty Sell" from AAA travels. In this video she tells about the international travel and also about the important documents to be carried while carrying out an international travel, that is the international driving permit, commonly called as an IDP. It's very important to carry an IDP while traveling overseas because an IDP acts as an important recognizable form of photo identification which helps us to communicate with foreign authorities. To get more information ...

Smash glow? What the heck is that? That's exactly what you'll find out… watch this science video tutorial from Nurd Rage on how to make smash-glow crystals (triboluminescent crystals) with Dr. Lithium.

Pixel Perfect is the "perfect" show to help you with your Photoshop skills. Be amazed and learn as master digital artist Bert Monroy takes a stylus and a digital pad and treats it as Monet and Picasso do with oil and canvas. Learn the tips and tricks you need to whip those digital pictures into shape with Adobe Photoshop and Illustrator. In this episode, Ben shows you how to apply light sources to 3D models in Photoshop.

There are many password-cracking tools out there, but one of the mainstays has always been John the Ripper. It's a powerful piece of software that can be configured and used in many different ways. Metasploit actually contains a little-known module version of JTR that can be used to quickly crack weak passwords, so let's explore it in an attempt to save precious time and effort.

The art of privilege escalation is a skill that any competent hacker should possess. It's an entire field unto itself, and while it's good to know how to perform the techniques involved manually, it's often more efficient to have a script automate the process. LinEnum is one such script that can be incredibly useful for privilege escalation on Linux systems.

A simple security flaw can allow an attacker to gain a strong foothold with little effort on their part. When a web application permits remotely hosted files to be loaded without any validation, a whole can of worms is opened up, with consequences ranging from simple website defacement to full-on code execution. For this reason, RFI can be a promising path to obtaining a shell.

Hello again, readers! In our previous crypter tutorial, we looked at how we could obfuscate our malware (or any program) by using a simple one-byte XOR key. In this quick tutorial, we will be looking at how a simple little tweak can create a better means of obfuscation. Let's get right into it!

In this article, we will build a parallel password cracker using the techniques explained in the previous part. As SHA-512 is the digest function that Kali (and most modern Linux distributions) use to store our passwords, we will make a SHA-512 password cracker.

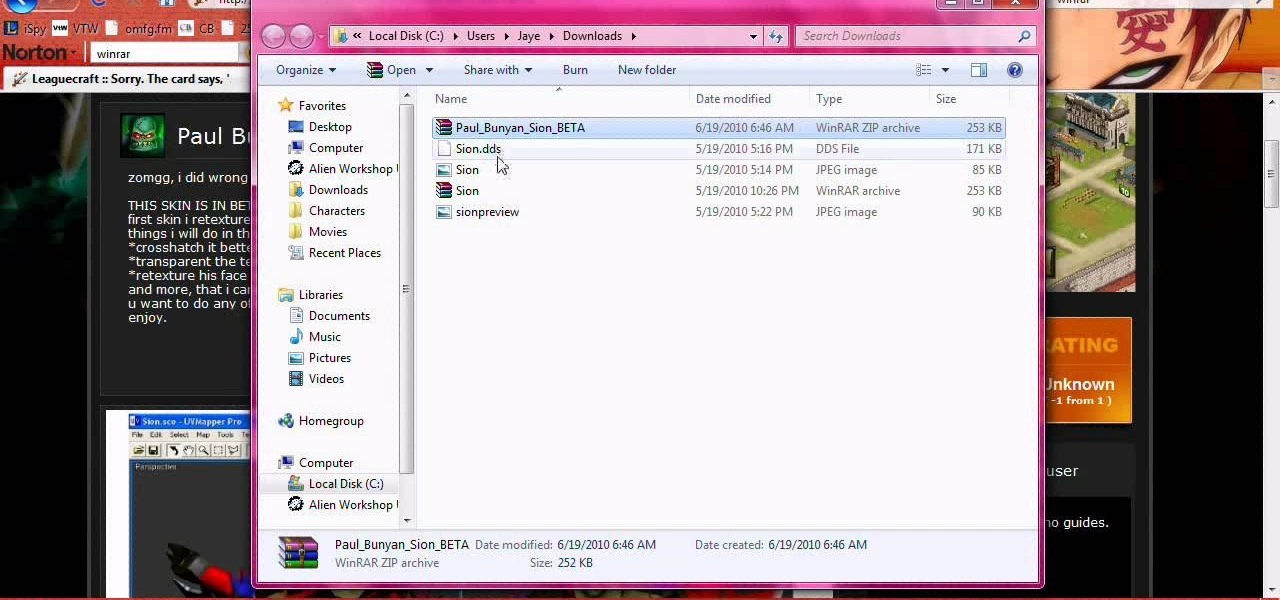
Personalize your League of Legends champions by altering their skins! This method will only change their appearance for you. This shows you how to obtain custom skins and apply them to your favorite champion (or one you just want to change around).

System of equations is nothing but a system which contains more than one linear equations. This system of equations can be solved to arrive at the solution of the system. A simple system of the linear equations can be a pair of equations. To solve this kind of system you can employ the substitution method. So take the two equation of the system. Solve for the value of y in the first equation in terms of x. Now take this value of y and substitute in the second equation y value. Now the second ...

This video shows us how to use a cuttlebug and make a congratulations card. Here are the following steps:

In this video the author shows how to do similarity transformations. He says that similarity transformations are used to draw the similar images at a different location and the k value is most important while doing this kind of transformation. He says that a negative k value tells that the copy of the shape will end at the opposite side of the origin to the original shape. He says that a positive k value tells that the copy will lie on the same side of the origin. Next thing about the k value...

Does dentistry sound of interest to you? If you don’t mind spending the day in other peoples’ mouths, dentistry might just be the career for you. In this video, learn what steps need to be taken to break into the field of dentistry.

This video tutorial shows you how to sow the seeds of the Begonia Semperflorens. 1. Obtain an already grown flower pot.

Check out this L4D2 walkthrough for some tips on Campaign 5: The Parish - Park. Stock up on items and exit via the door right next to the one you entered. Clear out any zombies and work your way up the large staircase into the park. Be prepared to deal with a likely Crescendo event in the plaza here. Pick a one of the staircases to climb up and enter the park. The restrooms near the entrance of the park usually contain a throwable item or two. For more info, watch the whole gameplay.

This last campaign is the hardest one. In the first part of campaign five, try not to drown and watch this L4D2 walkthrough for some tips on Campaign 5: The Parish - Waterfront. You are dropped off on the waterfront and told to make your way to the bridge. Pick up weapons and medpacks and head up the staircase. Go through the gate and clear a path to the Waterfront Market directly in front of you. There should be an open door for you to walk into. You may encounter a SWAT zombie at this point...

And just when you thought it was safe in town, you come back and find out it's like you were never there. Zombies everywhere. Watch this L4D2 walkthrough to play Campaign 4: Hard Rain - Return to Town. Gather any equipment and head out of the safehouse. The suburban neighborhood you travelled through last time is now flooded. You will want to spend as little time as possible wading through water. Try to look for rooftops or makeshift walkways to maximize your maneuverability. After dropping d...

Learn your way around the saccharine and bloody land of the sugar mill in L4D2. See the whole gameplay for Campaign 4: Hard Rain - Sugarmill. Stock up on weapons and head down the stairs to open the door of the safehouse. Clear out any zombies on the street and go across through the open window into the sugar mill. Once in the building, head to the left. There should be an open door leading back outside. For more info, watch the whole gameplay.

Make your way through the deadly plantation in L4D2. See the gameplay for Campaign 3: Swamp Fever - Plantation. Gear up and go outside of the safehouse. It will be light out. Mop up any zombies here and head straight ahead, bearing to the left. You will climb a small hill and see an opening in the fence. Check the sundries building on your left for items. Make your way through the rows of houses here towards the red two-story house at the end. Don't go inside the house, turn left right before...

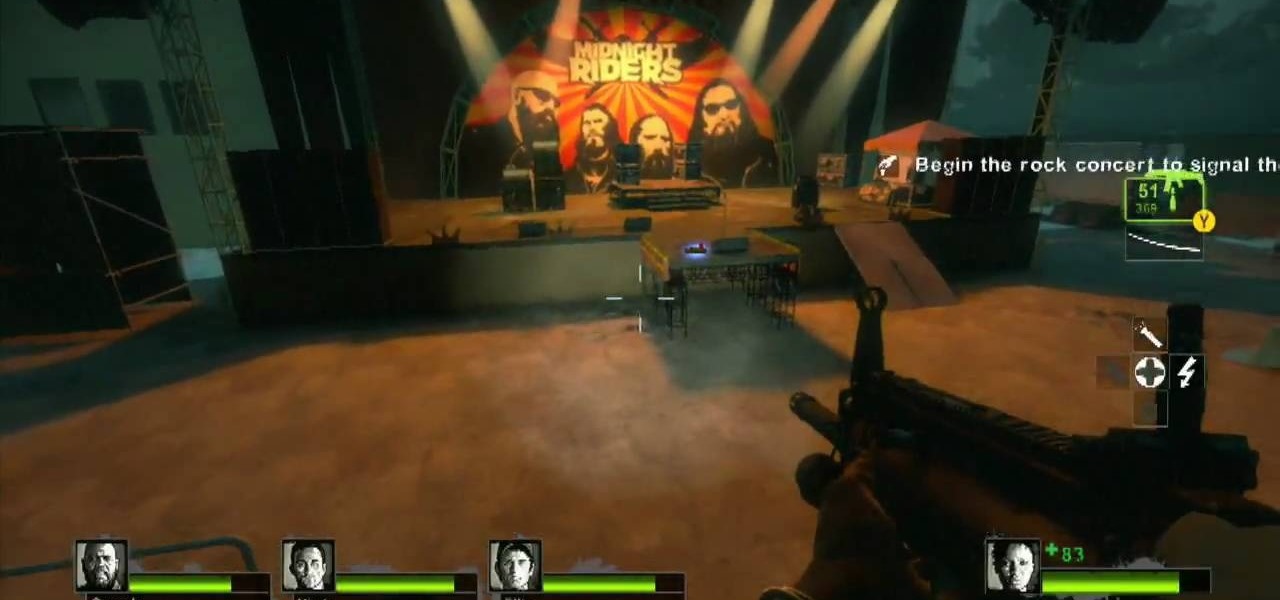
Don't let L4D2 get the best of you. Take control by checking out this video on Campaign 2: Dark Carnival - Concert. Grab your guns and go out the door. There is really only one path to follow, so move right around the venue until you reach the stage. Feel free to use up your ammo as there will be a refill when you reach the end. There are bathrooms to your right and left, but it isn't worth your time to search them. Clear out any zombies in the stage area. You must then flip the switch on the...