The NSA's massive internet spying efforts will continue. In President Obama's latest press conference, he went public to (in so many words) say that the NSA's spying efforts will continue uninterrupted. This, coming just weeks after the Amash Amendment which would have defunded the program, was narrowly defeated in the House (you can check if your congressmen voted against it here).
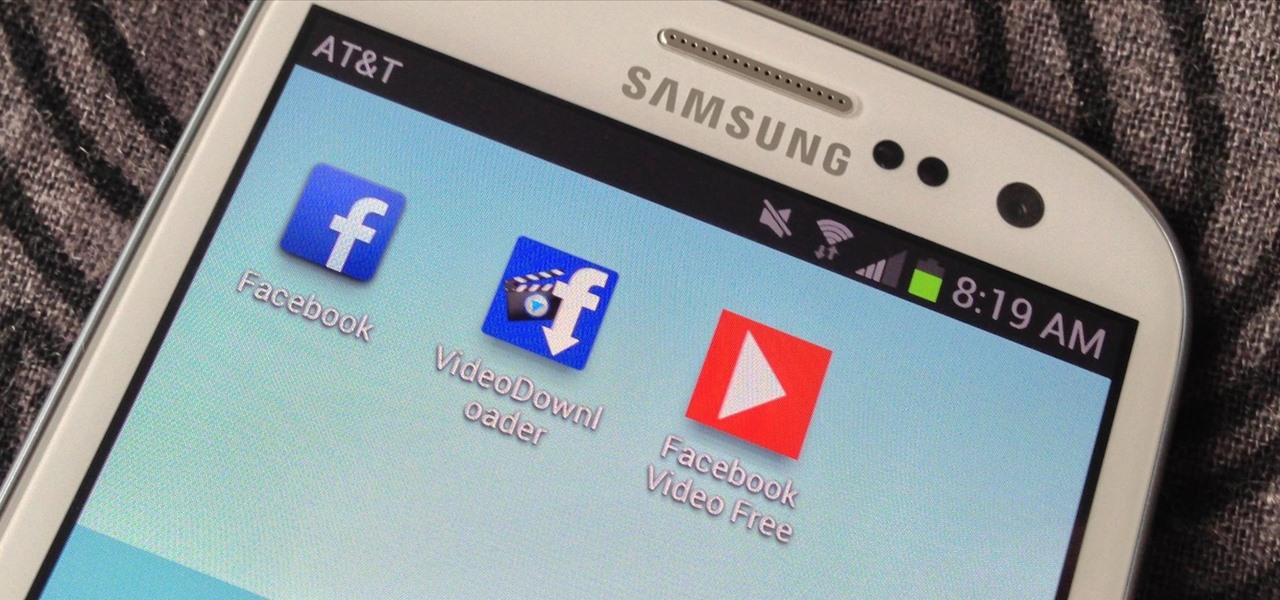
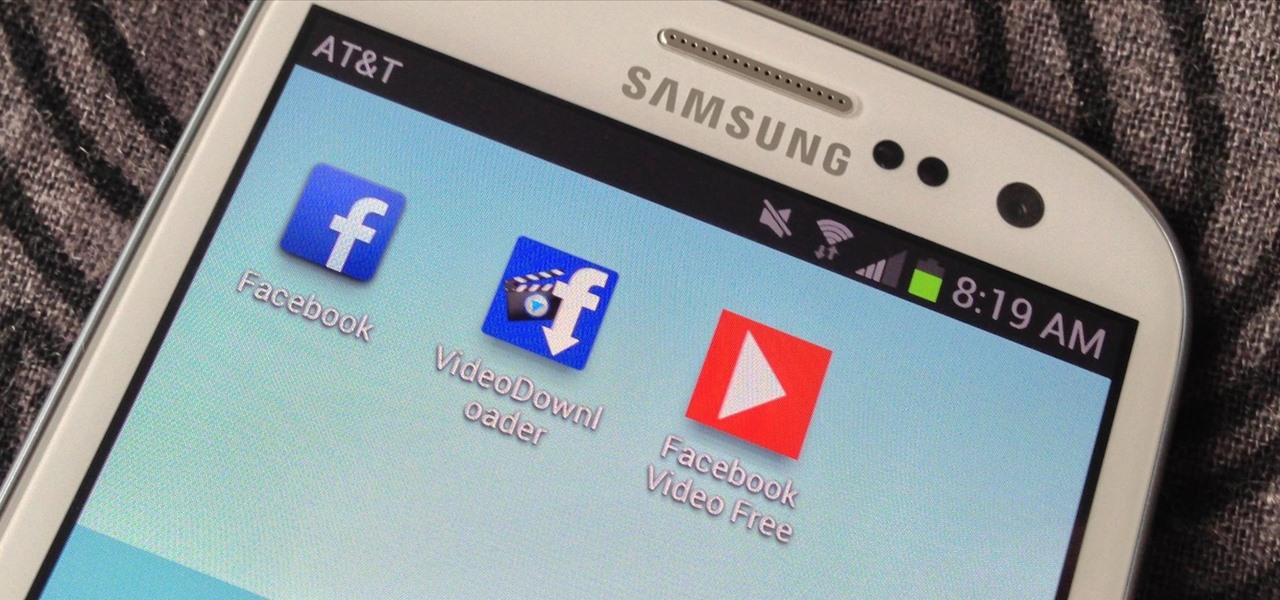
One thing that gets overlooked on Facebook is the amount of videos you can watch, and I'm not just talking about videos uploaded directly by Facebook users—I mean everything ever shared—YouTube, Vine, Instagram, Vimeo, etc.

All kinds of people pretend to be someone they're not on the internet, including scammers, people attempting to wind others up, hackers and web predators. Almost all of these people will leave bases uncovered and they're all easy to expose when you understand how to. Here are my favorite ways of finding out when somebody is lying quickly. Image Search

CONTEST ENDED: WINNERS ANNOUNCED This contest has ended and winners have been announced. To see who won, check out our quick winners post. Thanks to everyone for submitting their ideas!

In this article, I'll be explaining the basics of how microcontrollers work, physically and virtually. First off, microcontrollers are no simple thing, so don't be discouraged if you find it mind-boggling! The world of microcontrollers is fascinating, engaging, and an awesome hobby; it never gets boring. I'll be focusing more on I/O and analog based microcontrollers, such as those running Arduino, and using Atmel chips as examples (these are most commonly available, and easy to program).

In my first installment in this series on professional hacking tools, we downloaded and installed Metasploit, the exploitation framework. Now, we will begin to explore the Metasploit Framework and initiate a tried and true hack.

Despite the controversy over Scrabble Trickster across the word world, Mattel's modern take on the classic crossword board game is out in stores— but not in the United States. It's only available in and around the UK, but you can snag your copy just in time for Christmas from Amazon UK. You can also visit the official Scrabble Trickster website. I imagine this is going to be a hot item in the United Kingdom this holiday season, but as for me— it's the one Scrabble game I refuse to add to my c...

One sure fire way to add excitement to a summer day when you think it's just too scorching to go outside is by having a water balloon fight. This is a great way to stave off boredom and you'll be sure to feel like a kid again while getting some fun exercise.

You love your bike and it was stolen. Although, this is not a good scenario, you still may be able to retrieve it. Sketch the serial number or means of identification into the bike and then when it is stolen you can really get the word out to all the places that it might turn up.

This week, Apple unveiled its own version of Google Lens in the form of Live Text. In response, Google just hit back with a new feature for its visual search tool called Places, a new search category that can recognize landmarks and return information on them within the camera view, which Apple touted as a capability of Live Text during its WWDC keynote.

If you've recently built a Wi-Fi spy camera out of an ESP32-CAM, you can use it for a variety of things. A baby monitor at night, a security camera for catching package thieves, a hidden video streamer to catch someone going somewhere they shouldn't be — you could use it for pretty much anything. Best of all, this inexpensive camera module can perform facial detection and facial recognition!

Wireless headphones are convenient, comfortable, and more common than ever before. With the massive proliferation of wireless earbuds, it's hard to identify which ones are good and which ones just want to look like they're worth the price. Avanca T1 Bluetooth Wireless Earbuds are high-quality wireless earbuds with excellent functionality and a low price of $29.95 now that they're 50% off.

The gold standard in any business is reaching the front page of Google. You need to get your brand in front of audiences. While it can seem daunting, it's not impossible when you master SEO best practices.

These days, you can FaceTime with family and friends whether you're at home connected to Wi-Fi or on-the-go with mobile data. You may have noticed, however, that your iPhone will sometimes drop Wi-Fi and rely on cellular instead — whether you're placing or receiving a FaceTime call. While that's not an expected result, there is a workaround to get your FaceTime calls back on track.

For the average consumer, augmented reality is a fun way of dressing up photos and videos for social media. However, AR is also gaining momentum as a medium for storytelling, particularly in sharing powerful messages.

File permissions can get tricky on Linux and can be a valuable avenue of attack during privilege escalation if things aren't configured correctly. SUID binaries can often be an easy path to root, but sifting through all of the defaults can be a massive waste of time. Luckily, there's a simple script that can sort things out for us.

SSH, or the secure shell, is a way of controlling a computer remotely from a command-line interface. While the information exchanged in the SSH session is encrypted, it's easy to spy on an SSH session if you have access to the computer that's being logged in to. Using a tool called SSHPry, we can spy on and inject commands into the SSH sessions of any other user logged in to on the same machine.

The first headset running on the Qualcomm Snapdragon XR2 chipset from an original equipment manufacturer is official.

What's the latest dance trend sweeping TikTok? The Shuffle Dance. If you just watch people doing the Shuffle Dance, especially the really good ones, you might think it's a bit complicated. In reality, it's really not that hard. It's just a handful of steps.

It's time to make some more room at the augmented reality cosmetics counter. This week, social media giant Pinterest unveiled "Try On," a virtual make-up visualization tool running on its Lens visual search tool.

Lego has shipped several apps and products that add an augmented reality dimension to their playsets. But it has taken a reality TV show from Fox to allow brick fans to build with virtual bricks in augmented reality.

Some of the leading big tech companies are still working in the lab on actual products, but at least some of their leadership did have some thoughts to share on the future direction of the technology this week.

One of Android's biggest strengths relative to iOS is how simple it is to sideload apps that aren't on the official app store. Rather than having to sign IPA files or tell your phone you trust a developer every two weeks, you can just enable a setting and be done with it.

It's been said time and time again: reconnaissance is perhaps the most critical phase of an attack. It's especially important when preparing an attack against a database since one wrong move can destroy every last bit of data, which usually isn't the desired outcome. Metasploit contains a variety of modules that can be used to enumerate MySQL databases, making it easy to gather valuable information.

While some of us thought Apple might pass on a new beta update in favor of an official release, it appears iOS 13.3.1 is here to stay in beta testing. This time, it didn't take four weeks to get here. The third public beta for 13.3.1 is now available, eight days after the release of public beta 2.

Brute-forcing is an easy way of discovering weak login credentials and is often one of the first steps when a hacker finds network services running on a network they gain access to. For beginners and experienced hackers alike, it's useful to have access to the right tools to discover, classify, and then launch customized brute-force attacks against a target. BruteDum does it all from a single framework.

While Elon Musk is in Los Angeles showing off the future of personal transport via the Cybertruck, another, unaffiliated group is taking one of his most popular ideas to market, with augmented reality as a key part of the plan.

While "Baby Yoda" from The Mandalorian threatens to overshadow it, Star Wars: The Rise of Skywalker arrives in theaters next week, which means it's time for Disney and Lucasfilm to ramp up its promotional strategy.

Edison Mail's big Assistant update means more features and functions for you in a convenient, efficient package. One of the most significant changes to come with the 1.17.0 (iOS) and 1.12.0 (Android) updates is calendar functionality for all connected email accounts. Other apps, like Spark, have had this for some time, but we're excited that Edison has finally jumped aboard the bandwagon, too.

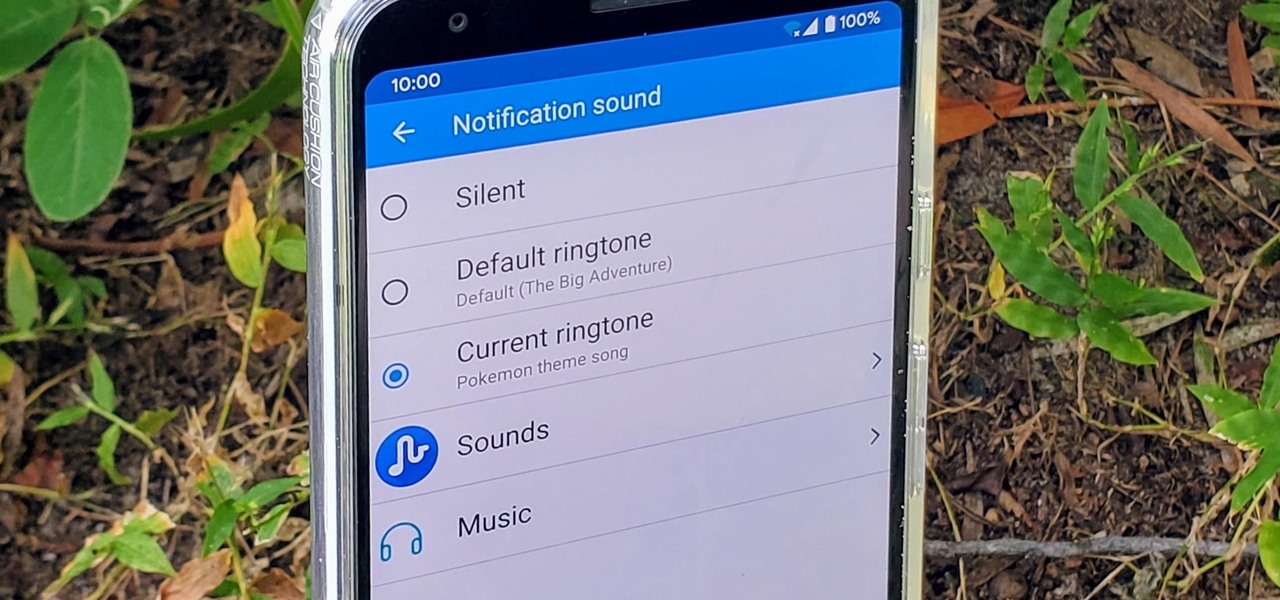
Have you ever walked around in public and heard the same handful of default ringtones over and over again? How do these people know who's calling without looking first? It's tough to tell when they all sound the same, but there is something crafty you can do to help with that. Using a different ringtone for certain contacts will allow you to differentiate between them instantly.

Apple's upcoming update for iOS 13 adds a host of fun new features, piggy-backing on the changes both iOS 13.1 and iOS 13 brought to the table. When you update, expect new emojis, Deep Fusion on 2019 iPhone cameras, among so much else. Want in on the action? Apple just released the fourth public beta for iOS 13.2 today, Wednesday, Oct. 23.

The biggest feature in the iOS 13 update is a new system-wide Dark Mode. It's a simple switch that you enable to turn system menus and Apple apps dark, but it can also darken third-party apps if their developers elect to support it. Trouble is, most haven't yet, so half of your apps likely still have a blinding white background.

Although early attempts at consumer smartglasses have employed trackpads and handheld or wearable controllers for user input, its the gesture control interfaces of the HoloLens 2 and the Magic Leap One that represent the future of smartglasses input.

In iOS 13, Apple is taking the Reminders app more seriously. With its long list of helpful new changes, the app finally stacks up to other task managers like Todoist or Wunderlist. One of the changes is small but mighty — the ability to add custom icons to lists. Doing so lets you personalize each collection of reminders to your liking and can help you identify lists with just a glance.

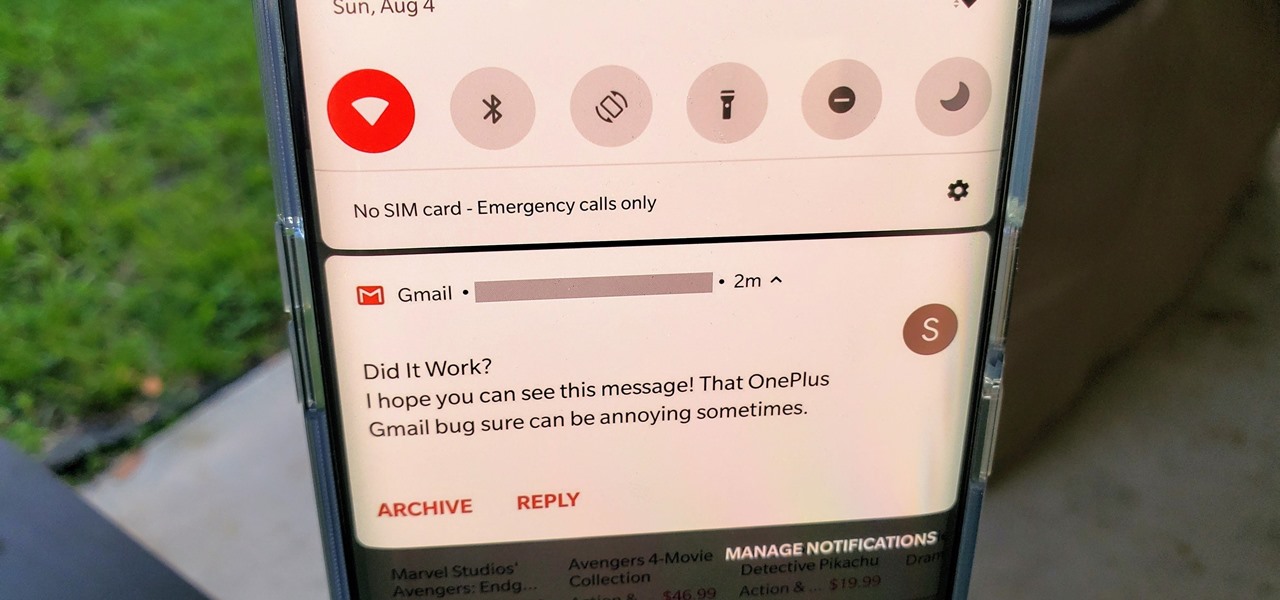
OxygenOS is often described as one of the best skins for Android on the market. It's fast, clean, and has a ton of useful features that appeal to just about everyone. However, it's also faced a significant issue for the longest time — overly aggressive battery optimizations that frequently kill background apps, including Gmail services.

The mystery surrounding Overture, an app that showed up in the Magic Leap World app store along with the latest Lumin software release, has been cleared up.

With Google taking on the sidewalks with augmented reality walking navigation for Google Maps, Apple has its sights set on the road.

Some investors play the short game, placing their bets on industries that show the quickest return on their investment, and, in the augmented reality space, that means the enterprise sector.

I'm here at the annual AWE event in Santa Clara, California, and the venue is just as packed, if not more so, than last year.

Because of its ability to place digital content into the real world, augmented reality lends itself well to artists and creatives.