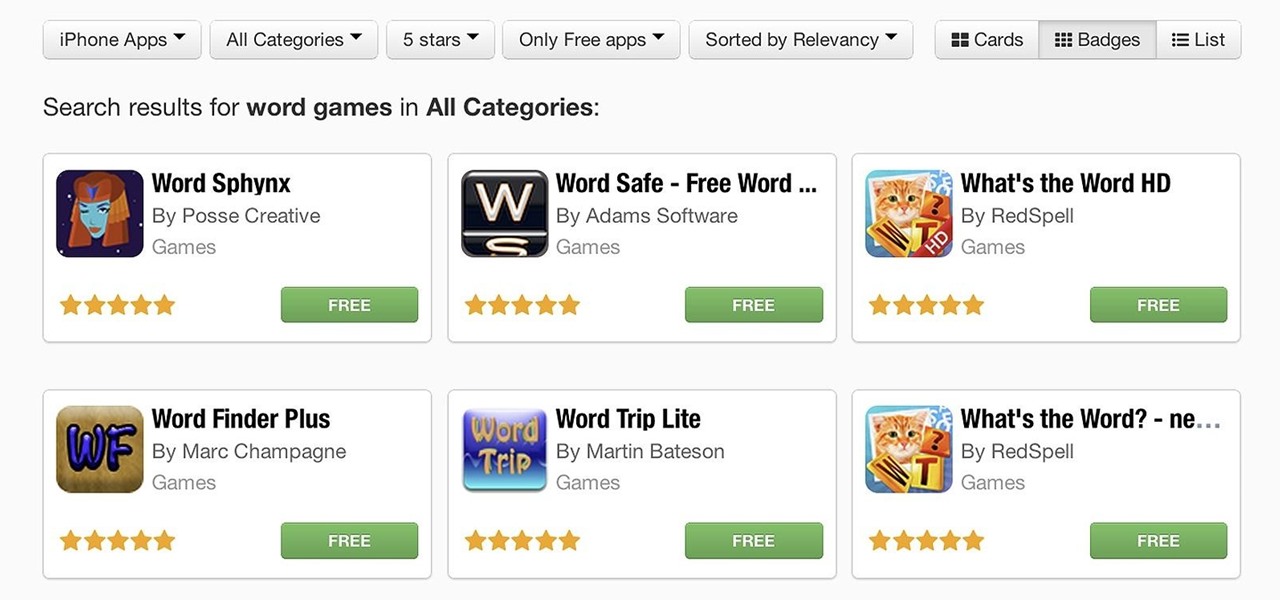
If you have an iOS device, chances are you've spent a decent amount of time in the App Store—without at least a few apps, smartphones are pretty boring. There's an app to do just about anything you could ask for, but the problem is finding them. Searching the App Store sucks.
Most people have tons of gadgets laying around the house these days, and they all need to be charged. Let the Wood Whisperer take you through the process of building a gadget station for all your favorite electronics. From laptops to cell phones, this gadget station will hold them all. Be sure to watch the entire 12-part tutorial from beginning to end for the whole experience.
When stories are told about people in need, the ones with happy endings include the details of someone that produced an action that caused the people in need to be better off than before. Do we have to wait for the identification of a need? Could we on purpose just plan to present products and services that cause our customers and client to see an improvement in their circumstances just because of the business interchange with an owner manager of purpose? The fair exchange of products or serv...

We've shared a capture-the-flag game for grabbing handshakes and cracking passwords for Wi-Fi, and there are some upcoming CTF games we plan on sharing for other Wi-Fi hacks and even a dead-drop game. While security-minded activities and war games are excellent ways to improve your hacking skills, coding a real video game is also an excellent exercise for improving your programming abilities.

Recovery mode and download mode are useful for modding and they can come in handy in a pinch. Booting into recovery mode to do a factory reset or wipe cache fan save your Galaxy S20 from a soft brick, and entering download mode lets you install firmware with utilities like Odin and Smart Switch.

There's definitely some malware-ridden apps on the Play Store. When it comes to the third-party apps you've connected to your Google Fit account, some have a crazy amount of permissions they have no business accessing. For example, you probably don't want a heart monitor app having access to your personal location data.

While Elon Musk is in Los Angeles showing off the future of personal transport via the Cybertruck, another, unaffiliated group is taking one of his most popular ideas to market, with augmented reality as a key part of the plan.

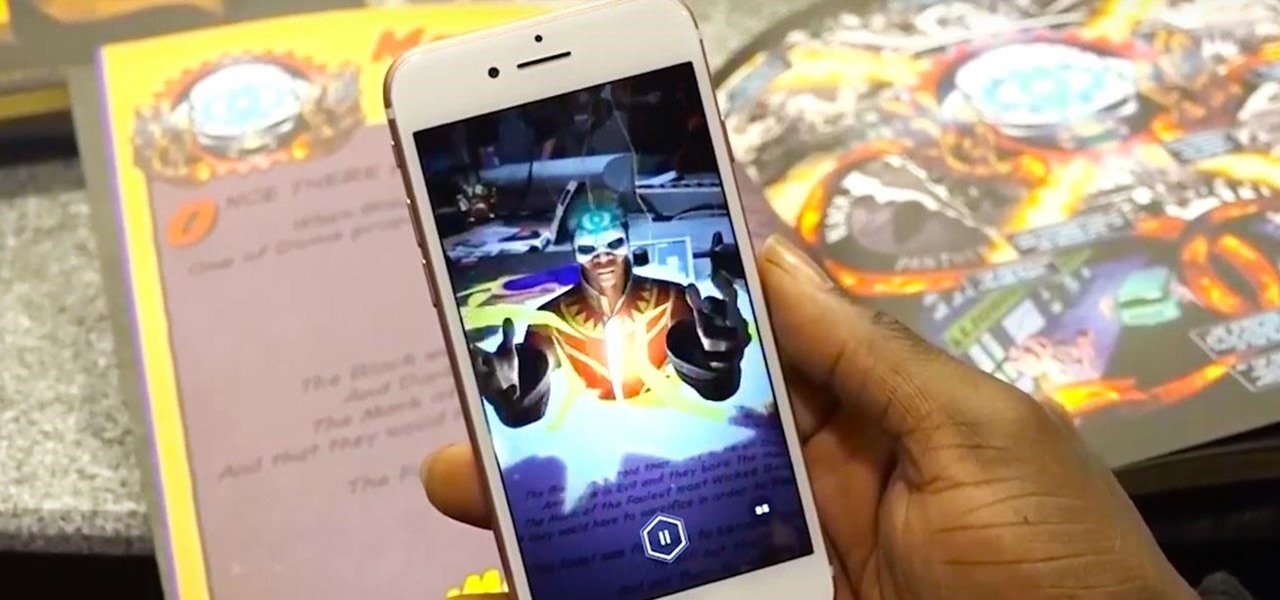
After three years and change, no one seems to be able to knock Pokémon GO off its augmented reality throne. Zombies, dinosaurs, and ghosts have all met defeat at the hands of the pocket monsters. Heck, not even the world's most popular wizard and Pokémon GO's developer can replicate the original's success.

Augmented reality enthusiasts who expected an AR hardware unveiling at Apple's annual iPhone launch event might not have to wait much longer.

Scanning pictures and uploading them to Google Photos is a great way to digitize your collection. With unlimited high-quality storage and text recognition capabilities, it's hard to pass up. And for your older family pictures, Google Photos will soon even colorize black and white images.

Augmented reality can be more than simply a way to enhance navigation, or superimpose virtual sunglasses onto your face. It can also be a platform for shining a light on important social issues.

Augmented reality as a storytelling medium can do some extraordinary things words and images alone can't convey -- such as transporting readers 400 years into the past.

As the tech world patiently waits for the advent of mainstream consumer smartglasses, Google is content to stick to the business world (for now).

The home bar, that tiny sliver of color at the bottom of the screen on Home button-less iPhone models, is helpful when first getting used to an iPhone X or newer's gestures. It helps you learn how to swipe up to unlock, go to the home screen, view the app switcher, and so on. But after a few weeks, it just becomes an annoying eyesore you can't get rid of — unless you have a jailbroken iPhone X.

The tradition of using cutting edge technology to prepare for missions in space, in this case, augmented reality, continues with a new team of international astronauts slated to board the International Space Station (ISS) later this year.

While these days it is better known for the cross-platform gaming sensation Fortnite, Epic Games also makes Unreal Engine, one of the top development environments for 3D content and, in turn, augmented reality and virtual reality experiences.

On Tuesday, Blue Vision Labs, one of three Google-backed companies working on AR Cloud platforms, announced its acquisition by ride-sharing company Lyft.

Facing mixed reviews for the Magic Leap One, Magic Leap has already returned to the lab to improve on the device's successor.

Better known among consumers for its virtual reality apps, Jaunt is now pivoting toward solutions for augmented reality developers.

In recent days, I've twice talked about brining the Magic Leap One out into the world with me to test its mobile capabilities. But you may have been wondering how I carried the device with me. Did I just stuff my brand new $2,300, hard to obtain device in a backpack and hit the road? Hardly.

When Magic Leap One owners unbox their new devices over the next few months (or, if they are lucky, days), they will have some familiar augmented reality news content to consume.

For the first time since its inception, the famously hidden System UI Tuner has to be unlocked in a new way. No longer can you long-press the gear icon (found in Quick Settings) until it spins and reveals the hidden settings option. With Android 9.0 Pie, there's a new workaround to reveal the menu.

After weeks of teasing what many hoped might be a live, on-device demo of Magic Leap software to go along with the hardware glimpse we got last month, it turns out that all we got was a bit of new demonstration video footage.

Another entrant into the do-it-yourself AR content creation market has emerged, as Zappar has updated its ZapWorks Studio software to include features for development newbies.

Magic Leap just did something it didn't do during its recent Twitch hardware demo: show us some new demo footage of what augmented reality really looks like through the Magic Leap One.

On June 23, National Geographic will begin welcoming visitors to the world's first outdoor planetarium in Quebec, Canada, where an augmented reality experience overlaid on the night sky will replace the projection systems of traditional facilities.

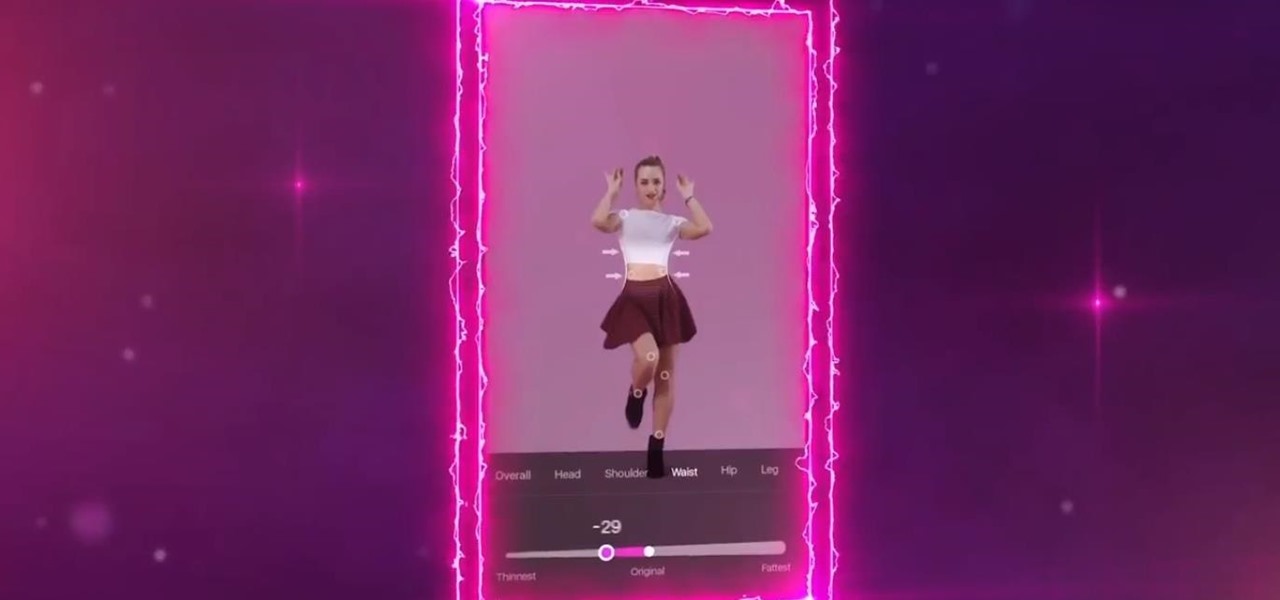
Usually, the camera adds 10 pounds, but with a new augmented reality effect in Like's mobile app, the camera can actually make you look slimmer.

The easiest way around a security policy is to find users who don't follow it. The Have I Been Pwned database identifies accounts with information breached by major third parties like Yahoo and LinkedIn. With Maltego, hackers can locate breached accounts created using company email addresses, potentially giving attackers access to a company account if the employee reuses a compromised password.

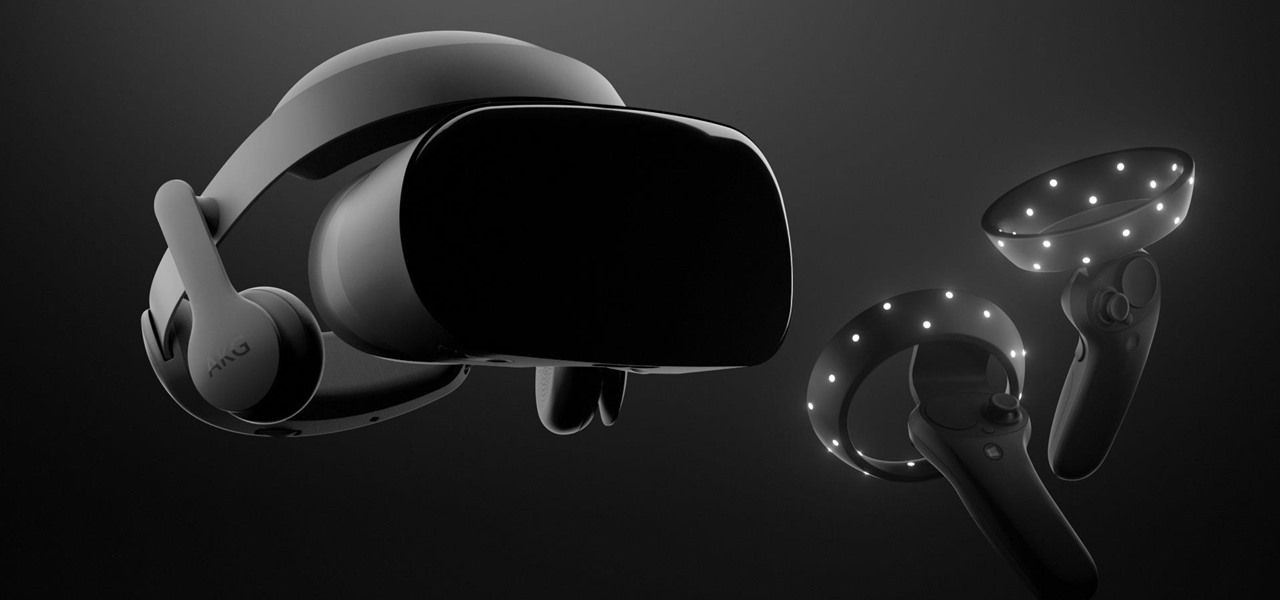
Mere weeks after rumors surfaced that Apple may be working on a headset capable of VR and augmented reality, it appears that Samsung is taking the same approach, but with an assist from Microsoft.

The annual Coachella Valley Music and Arts Festival is one of those events that everyone talks about, so an augmented reality experience in the festival's mobile app and from one of its headlining acts, Eminem, basically means the technology is officially cool.

Fast-casual burger restaurant Bareburger expects to soon replace all of its paper menus with 3D models of its burgers and other items rendered in augmented reality, but for now, the company is preparing some rather interesting limited AR interactions.

Department store chain Zara is temporarily ditching its mannequins and dressing up its stores with augmented reality experiences featuring virtual versions of real fashion models.

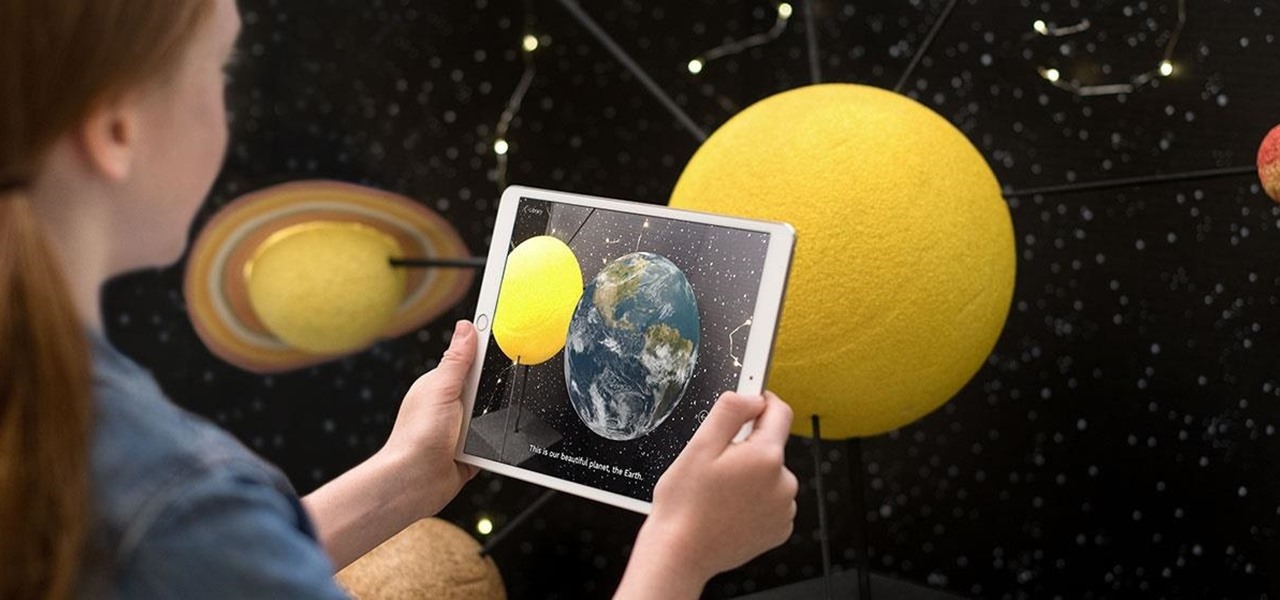
A report from app data firm Sensor Tower reveals that more than 13 million ARKit apps have been installed on iPhones and iPads within the first six months since the toolkit launched with iOS 11.

Thanks to Samsung Experience 9.0 on the Galaxy S8 (AKA TouchWiz Oreo), we know the upcoming Galaxy S9 is going to enjoy some of the new keyboard changes coming to Samsung's iteration of Android 8.0. Those who preorder the device on March 2 or pick it up on March 16 can expect these changes out of the box, as the S9 will be running Samsung Experience 9.0 on day one.

Apple CEO Tim Cook's most recent tech prophecy is that "AR will change everything." And now, that includes Apple's own website.

On Thursday, Snapchat opened up its walled garden of World Lenses to the masses of creators with the launch of Lens Studio.

The first teaser for Jurassic World: Fallen Kingdom just hit computer screens on Sunday, but now plans for an augmented reality book for the film have also emerged.

While most of Hollywood and its celebrity class are enthralled by virtual reality, a new augmented reality experience featuring some of the music and film world's top talent is preparing for virtual liftoff.

Microsoft's latest move to further secure its hold on the emerging mixed reality space comes in the form of two new Mixed Reality Capture Studios in San Francisco (the flagship studio) and London.

Typos are a constant annoyance that we all deal with thanks to the cramped touchscreen keyboards on smartphones. For many, nothing beats the feel of a good old physical keyboard when it comes to typing fast with minimal errors. Fortunately, WhatsApp has an awesome feature which lets you use their messaging service right on your computer.