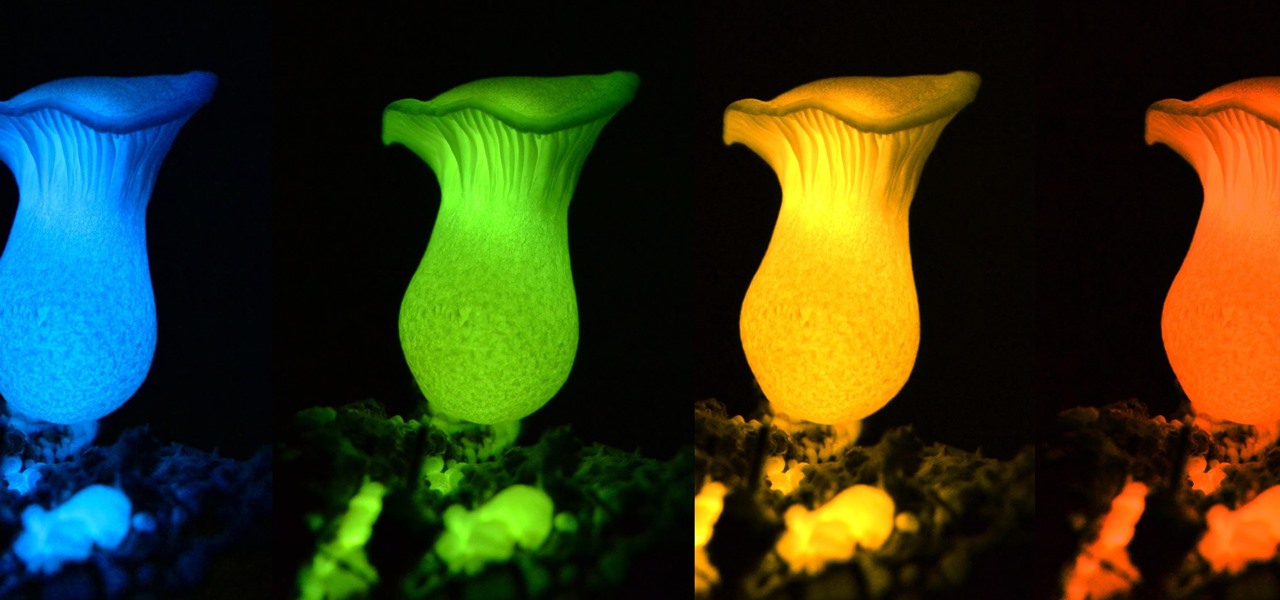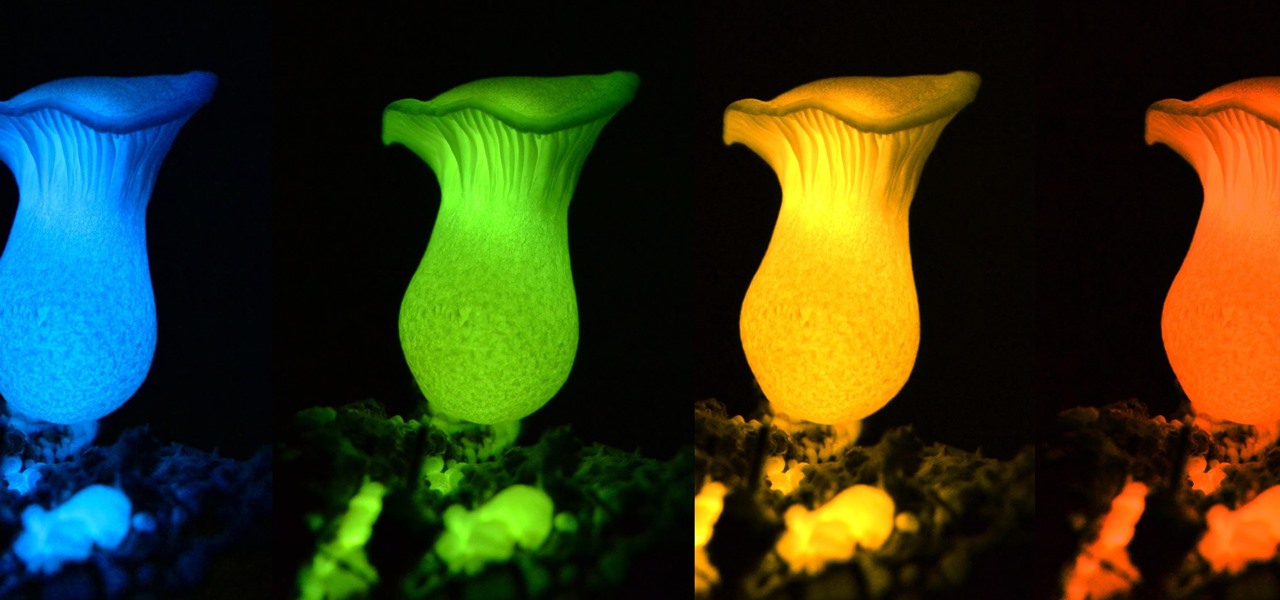
Bioluminescence — the ability of an organism to produce and emit light — is nature's light show. Plants, insects, fish, and bacteria do it, and scientists understand how. Until now, though, we didn't know how fungi glow.

Water makes up about 60% of your body weight. Whether you like it plain, flavored, bubbly, or in beverages or food, we all need water daily to avoid dehydration and stay healthy. For communities in need of clean drinking water, new research using bacteria may offer a simplified, lower-cost method for boosting potable water supplies.

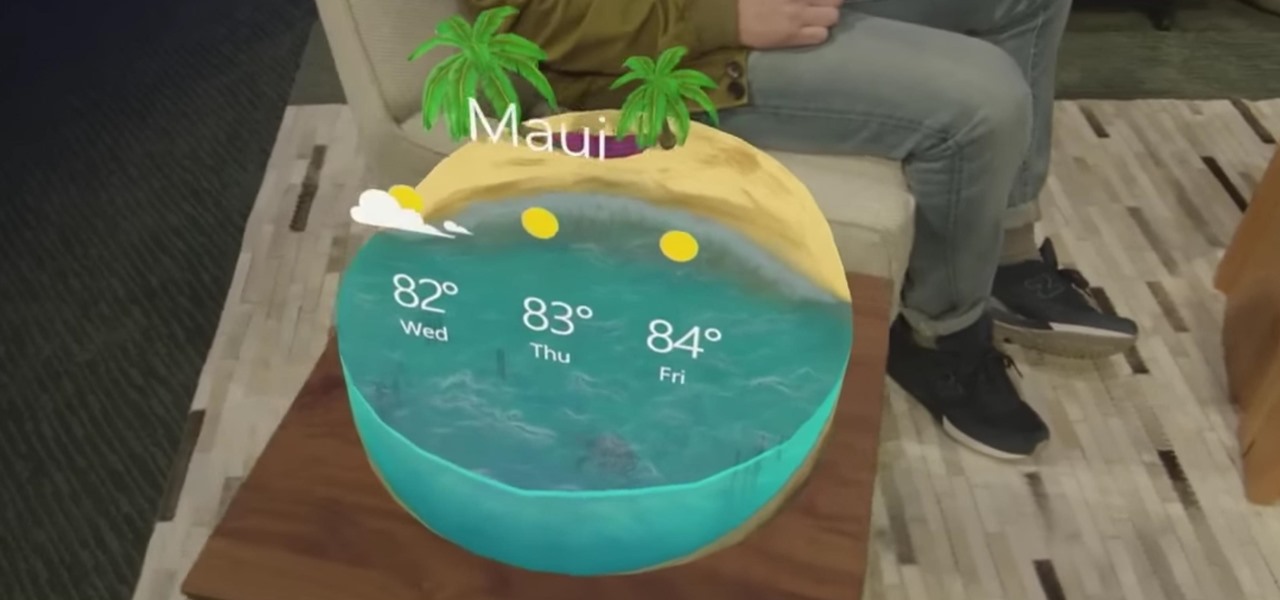
The hunt for the mixed reality use-case that wins over consumers' hearts and creates a critical mass is a problem every developer would love to solve. Not only would they find themselves rich and famous seemingly overnight, but they would also end up making one of the various possible hardware solutions a viable place for other developers to put their time and energy.
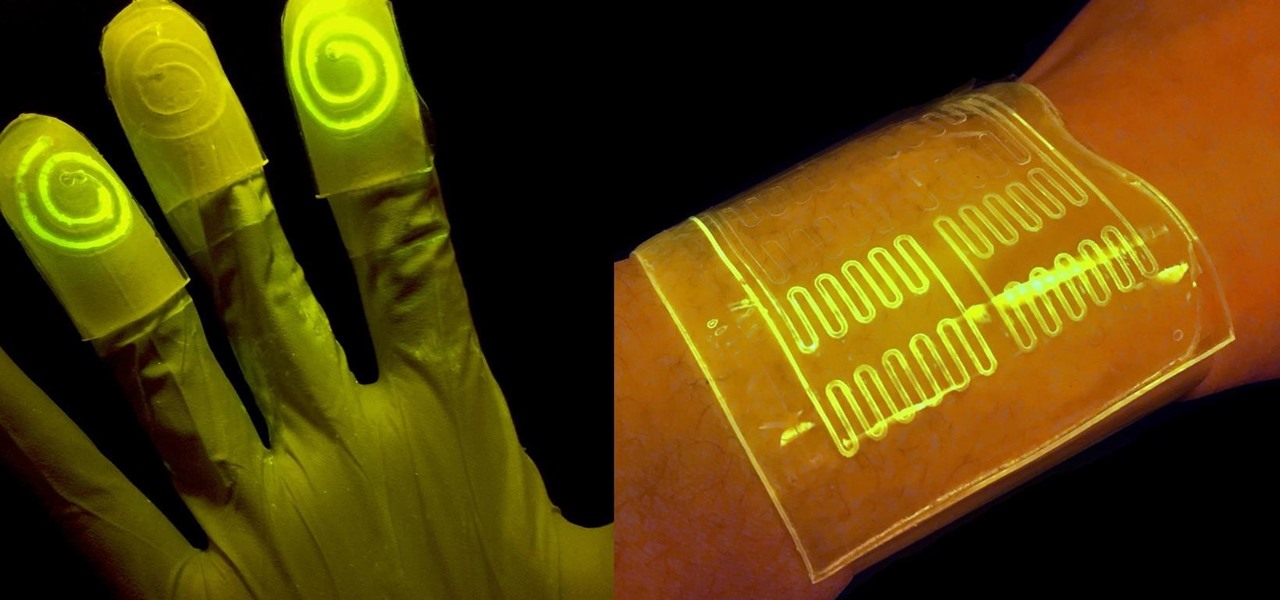
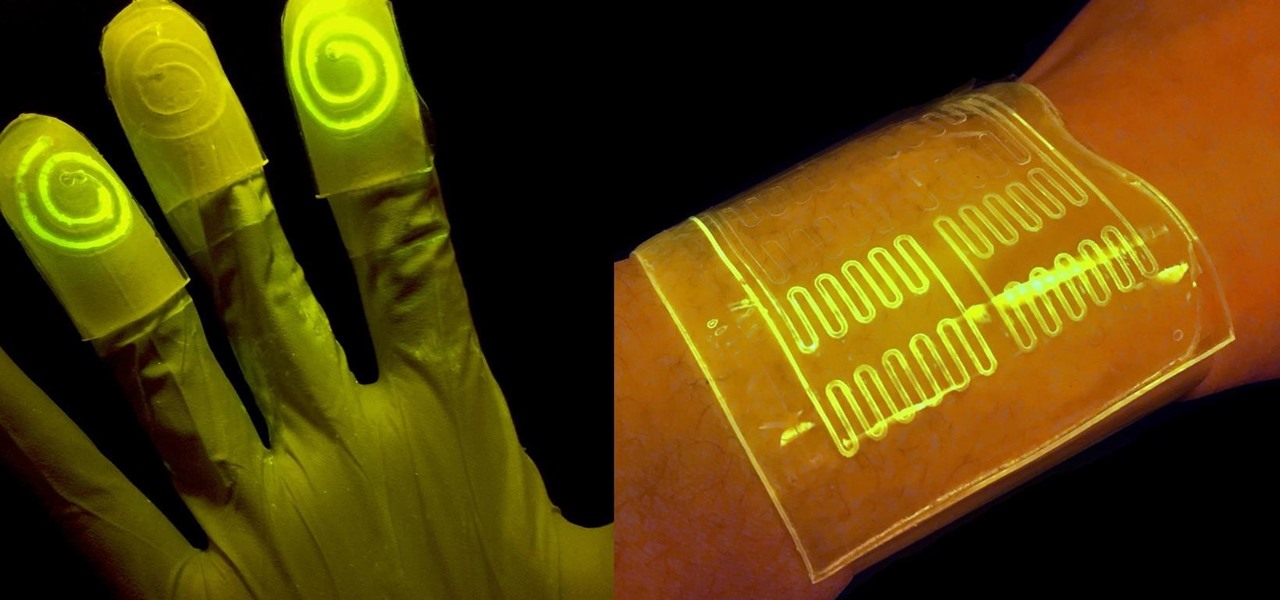
While at work, you notice your gloves changing color, and you know immediately that you've come in contact with dangerous chemicals. Bandages on a patient signal the presence of unseen, drug-resistant microbes. These are ideas that might have once seemed futuristic but are becoming a reality as researchers move forward with technology to use living bacteria in cloth to detect pathogens, pollutants, and particulates that endanger our lives.

Our quest to find new antibiotics has taken a turn — a turn down the road, that is. A team of scientists from the University of Oklahoma is scooping up roadkill and searching for bacteria on them that might yield the world's next antibiotic.

In the ongoing search to find better ways to use antibiotics, an extract made from maple syrup has some surprisingly important medical benefits.

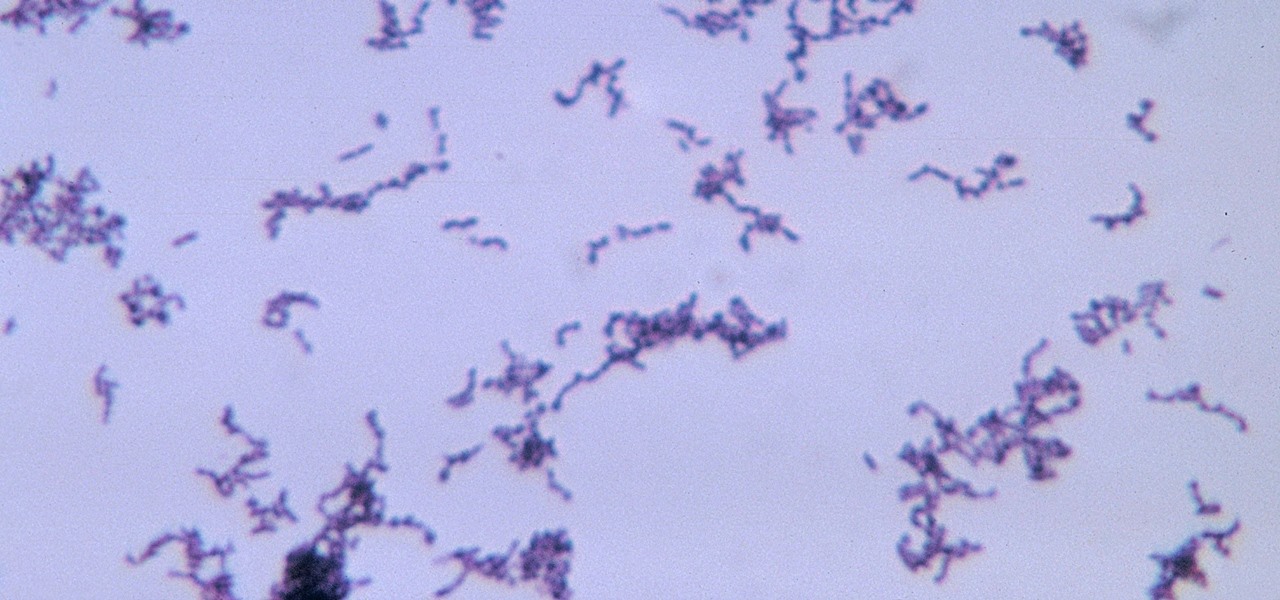
The squiggly guys in this article's cover image are Propionibacterium acnes. These bacteria live in low-oxygen conditions at the base of hair follicles all over your body. They mind their own business, eating cellular debris and sebum, the oily stuff secreted by sebaceous glands that help keep things moisturized. Everybody has P. acnes bacteria—which are commonly blamed for causing acne—but researchers took a bigger view and discovered P. acnes may also play a part in keeping your skin clear.

Most females have had at least one urinary tract infection in their lifetimes. Recurrent UTIs are particularly problematic in young, sexually active women, where about 80% of the infections are caused by the bacteria Escherichia coli, better known as E. coli.

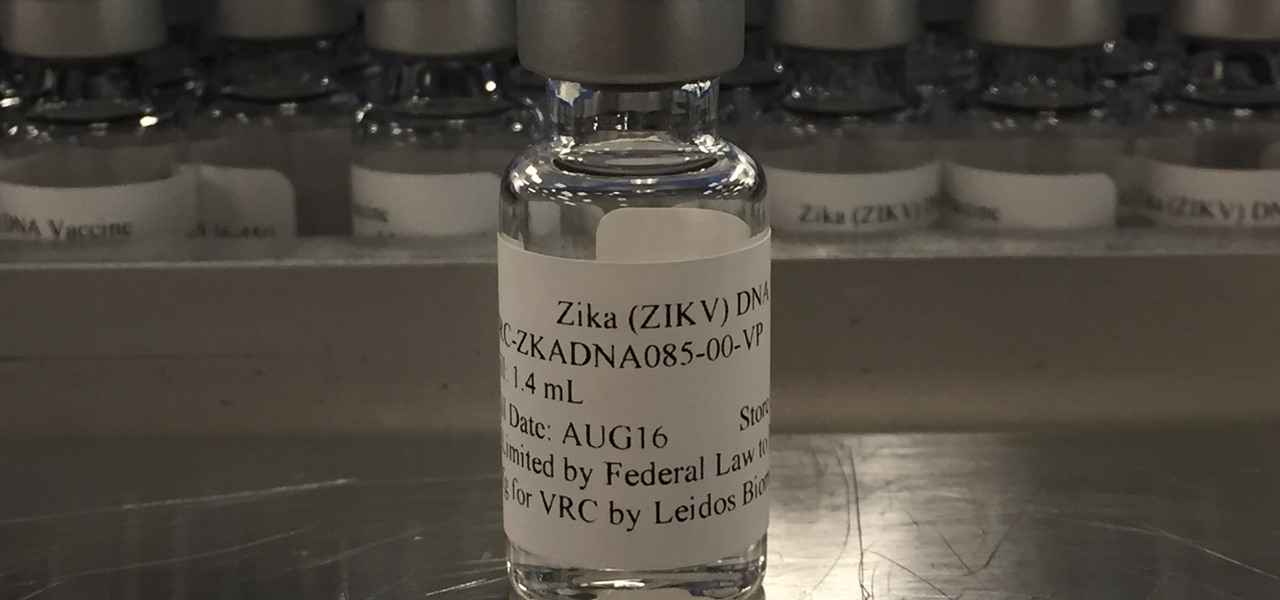
Phase 2 of a Zika vaccine trial began in the United States this week, along with Central and South America.

The culprit probably wasn't what doctors were expecting when a 57-year-old man in Hong Kong came to the hospital. The patient was admitted to the intensive care unit in critical condition. A clue to the cause of the infection would lie in the man's profession—he was a butcher.

Have you ever had the stomach flu, aka the 24-hour flu? Well, chances are high that you never had influenza, but an intestinal infection called gastroenteritis.

Over 6,500 waterfowl—mostly ducks—have died in Canyon County, Idaho, stricken by avian cholera. The outbreak started in February, and before it's over, it may not only be Idaho's largest outbreak, but one of the largest in the country.

Somewhere around 600–800 million people in the world are infected with whipworm (Trichuris trichiura), an infection they got from ingesting soil or water contaminated with feces of infected animals or people containing the parasite's eggs.

We may not fully appreciate all the important roles wheat plays in our lives until it's gone—or at least, when it's in very short supply. What would a world be like without bread, cakes, cereal, pasta, or wheat beer? If the dire warnings about an impending stem rust fungus come to pass, we may know all too soon.

With new diet and health claims coming at you everyday, it's sometimes hard to know what to believe. Well, here's a bright spot: A pair of studies confirm that whole grains are healthy for you, and for the diversity of microbes living in your gut.

Before you bite into that beautiful tomato in your garden, the tomato fruitworm, or the Colorado potato beetle, might have beat you to it.

"Necessity, not novelty," is a phrase I use often when it comes to HoloLens development. It would be fair to call it my mantra, or mission statement, as I prototype and explore software creation on this new frontier of mixed reality.

The pathogen referred to as a "nightmare bacteria" is quietly adapting and spreading faster than anticipated.

The largest and arguably most widely known event of its type, especially in the US, the Sundance Film Festival is an annual celebration of independent film—ones made outside the Hollywood system. This year, a new type of experience appeared at the Sundance Film Festival in an installation called "The Journey to the Center of the Natural Machine." This mixed reality presentation offered the user the newest type of storytelling in a long and important line—continuation of the species kind of im...

In the summer of 1976, 4,000 American Legionnaires descended upon the Bellevue-Stratford Hotel in Philadelphia, Pennsylvania, for a four-day convention. Several days later, many of the attendees experienced symptoms of severe pneumonia. By the beginning of August, 22 people had died. The Centers for Disease Control and Prevention (CDC) estimate that about 180 people were sickened and 29 people died before this mysterious outbreak burnt out.

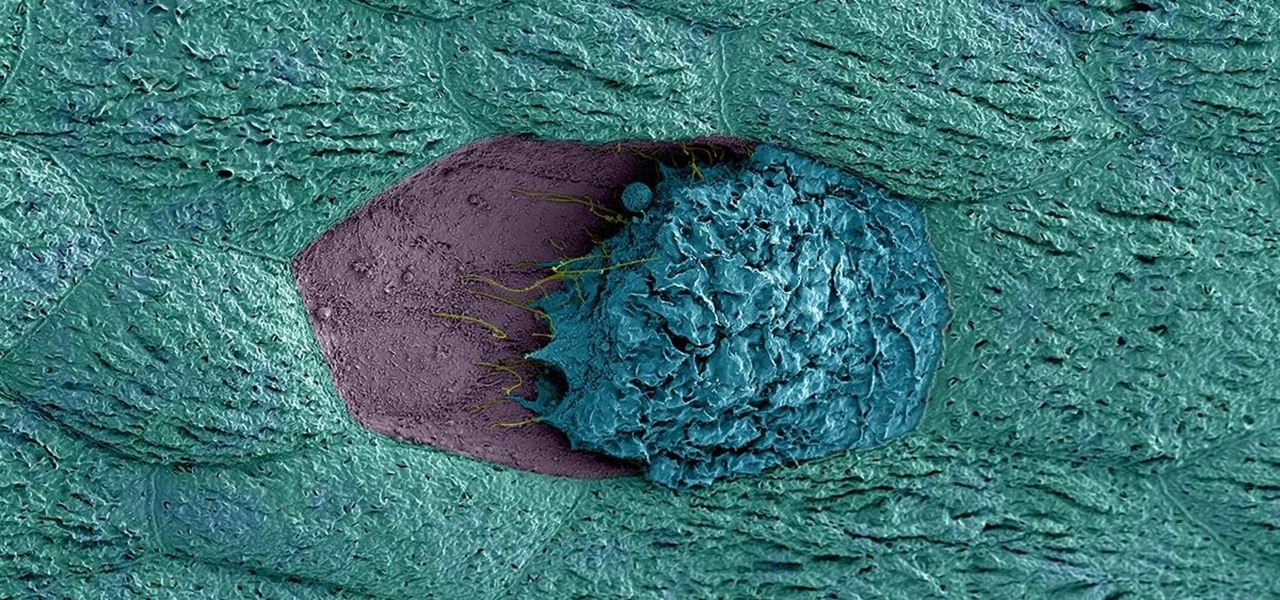
Over 1.2 million people in the US are infected with human immunodeficiency virus (HIV)—and one out of eight of them don't know it. Even after decades of intense research into the virus, there's still no cure for it. One of the big problems is that the virus hides out in certain cells of the body, resisting treatments that kill it.

Despite the availability of a vaccine against it, almost 50% of men aged 18-59 in the US are infected with the human papillomavirus (HPV). Why?

After California college student Luis Ortiz blacked out and was taken to the hospital in 2015, doctors were startled to discover the reason his brain was swelling—a one-centimeter long, wriggling tapeworm living within a ventricle in the middle of his brain.

A gold-medal winning entry into the iGEM synthetic biology competition could change the way we look at Esherichia coli, the bacteria better known as E. coli.

It's become a routine for many of us to ring in the New Year with pledges to finally get our budgets and finances under control. Unfortunately, it's also quite difficult to to keep those promises. Some of us will just dive into our resolutions and wing it as we move forward, which usually ends in failure. But even for those of us who plan carefully, obstacles along the way can spell doom for New Year's resolutions.

I used to brag that I could make a swan out of an apple, but chicks don't dig swans—they dig roses. So now I'm going to brag about making apple roses, because you would, too, if you could get them to look like this: Now that's an apple tart that will win the ladies over. (And definitely 100% tastier than the usual bouquet of roses, and 100% less greasy than a bouquet of bacon.)

Before the iPhone 7 was launched and all the unrealized reports about the phone's features were tucked back into their annual rumor mill, there was some speculation about wireless charging. Specifically, whether or not the iPhone 7 and 7 Plus would support it. We now know they don't, and here's why.

Among the many changes in Android 7.0 Nougat, a less talked-about feature may very well be one of the most interesting. As part of a new system-wide API, apps can now create their own Quick Settings tiles, and it doesn't require any complicated workarounds like it has in versions past.

Fondant looks pretty, but man, it sure does taste weird. Don't Miss:

Chris' Outrageous Cheesecake, a decedent combination of chocolate cake, brownies, cheesecake, and coconut-pecan frosting, is easily one of The Cheesecake Factory's most popular desserts. But, the price of fulfilling your cravings for this addictive treat can get up there (at about $8 a slice), and when you eat it at the restaurant you likely are limited to only one small piece.

Pie crusts are pretty intimidating if you're an at-home baker with little experience, since there's a lot of science behind making them. A perfectly flaky crust that's golden brown—not charred and black along the edges—requires careful attention, a foolproof recipe, and some decent baking skills.

A stack of light-as-air pancakes can make a weekend morning truly golden. While fluffy pancakes may not seem like rocket science, the reality is that there are many little details that can contribute to a pancake fail that's either too dense or too crumbly.

We love standing around a barbecue with an icy cold beverage in hand, enjoying the delicious smell of smoky food and chit-chatting with pals. Grilling season — it's our favorite time of the year.

Store-bought marinades and sauces have an ability to jazz up the simplest items. But after a while, those favorite tastes seem a bit repetitive and mundane, and that got us to experimenting with different add-ins to make our marinades stand out. Fruits, herbs, spices—all of the usual suspects were delicious, but not spectacular.

Whether you're performing a factory reset to get your device ready for sale or trade-in, or you're wiping your device in the hopes of fixing software issues, there's a right way and a wrong way to go about it. Sure, it seems like a simple task on the surface, but if you're not careful, you could end up wasting a lot of time or losing precious data.

Using a technology we like to call "Hive Computing," several Android apps allow you to contribute idle processing power to help further scientific research. This basically means that when you're not using your phone or tablet, it can join forces with other idle devices to form a supercomputer that scientists can use to potentially make a world-changing breakthrough.

Everyone has their own reality, and in that same vein, everyone has their own guidelines for what makes the "perfect fried chicken." Now, I'm not saying that my version is the ultimate for everyone, but it's definitely a crowd pleaser in my experience.

Welcome back, my budding hackers! Metasploit, one of my favorite hacking/pentesting tools, has so many capabilities that even after my many tutorials on it, I have only scratched the surface of it capabilities. For instance, it can be used with Nexpose for vulnerability scanning, with Nmap for port scanning, and with its numerous auxiliary modules, nearly unlimited other hacking related capabilities.

Most home bakers rely on vanilla extract as a flavor component to their cakes and cookies, but little do they know what they are missing until they trade in their extract for whole vanilla beans. The rich complexity and different notes of flavor of a true vanilla bean are often washed out and distilled into a one-note sweetness, especially if the extract is cheap or imitation. If you want to get more serious about baking, you need to get serious about using vanilla beans.

Welcome back, my neophyte hackers! Metasploit is such a powerful tool that I can only scratch the surface of its capabilities here. As it has developed over the years, it is now possible to use Metasploit for nearly everything from recon to post exploitation to covering your tracks. Given its versatility, every aspiring hacker should have at least a tentative grasp of Metasploit.