Playing dobro guitar involves using a slide made of steel or brass to sound notes on the fretboard, instead of the traditional method of pressing down with the fingers. In these online guitar lessons on video, learn techniques to play acoustic slide guitar music.

Penetration-testing frameworks can be incredibly useful since they often streamline certain processes and save time by having a lot of tools available in one place. Of course, the most popular pentesting framework is undoubtedly Metasploit, but there are many others out there that cater to particular needs. For auditing web applications and servers, Tishna comes in handy.

When you post a photo or video on Instagram, it's always nice to see positive comments from friends, family, and even fans. On the other hand, it's never fun to see spam or hate messages underneath your posts. Before, you'd have to delete these comments one by one, but now you can delete comments in bulk.

Your brand new iPhone SE packs the latest A13 Bionic chip into the form factor of the iPhone 8. With all that modern tech, you'd expect your iPhone to be unstoppable. That said, no smartphone is perfect, and sometimes, the iPhone SE will give you trouble. If your device is frozen, bugging out, displaying the wrong data, or won't shut down the usual way, you might want to try a force restart.

Though Microsoft has had trouble keeping up with the demand for HoloLens 2, the company has been able to supply modified headsets to the US Army.

The UK has officially exited the European Union, completing the long and tumultuous Brexit story and putting the storied nation once again on its own on the international stage.

What's the latest dance trend sweeping TikTok? The Shuffle Dance. If you just watch people doing the Shuffle Dance, especially the really good ones, you might think it's a bit complicated. In reality, it's really not that hard. It's just a handful of steps.

After leveraging the well-known intellectual property of Rovio's Angry Birds for its first game for the Magic Leap One, Resolution Games is singing a new song with a familiar refrain for its next game for the augmented reality headset.

At least one hurdle to China-based augmented reality startup Nreal going mainstream in the United States may be about to be knocked down, thanks to behind the scenes legal movements Next Reality has uncovered.

Just two days ago, on Nov. 18, Apple released iOS 13.2.3 to the general public, which included stability updates for bugs affecting iOS 13.2 and earlier. Today's update isn't for the general public, however. Instead, Apple just pushed out iOS 13.3 developer beta 3 for software testers.

Most augmented reality experiences are purely visual, with spatial audio gaining in popularity to make visual experiences more realistic. However, leveraging the sense of touch may be the next frontier for AR experiences.

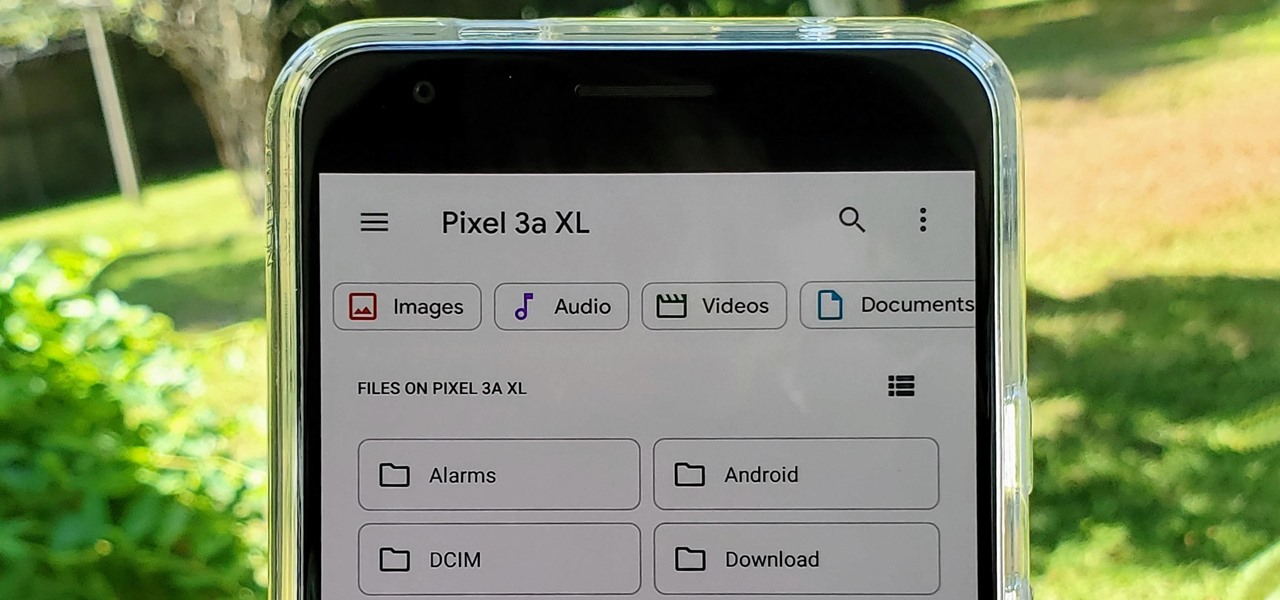
With the files on our devices getting more important as the years go by, the need to keep things organized continues to rise. The longer you have a device, the messier the internal storage might become. Having a file manager would be extremely useful in this situation. You could also reorganize the folder structure as well, just like you could on a desktop computer.

Sure, Tony Stark was able to build the original Iron Man suit in a cave with a box of scraps, but can the average do-it-yourselfer replicate the EDITH smartglasses from Spider-Man: Far From Home in a similar fashion?

With Snapchat making the leap into the smartglasses realm, Facebook had to find a way to try and steal its competitor's augmented reality thunder.

The art of privilege escalation is a skill that any competent hacker should possess. It's an entire field unto itself, and while it's good to know how to perform the techniques involved manually, it's often more efficient to have a script automate the process. LinEnum is one such script that can be incredibly useful for privilege escalation on Linux systems.

In the Tom Holland era, it appears to be impossible to promote a new Spider-Man movie without an augmented reality experience, a trend that continues with Spider-Man: Far From Home.

One of the masters of science fiction, Neal Stephenson, may be on staff at Magic Leap, but that doesn't mean he can't take a moment to visit the halls of competitor Microsoft, the maker of the HoloLens.

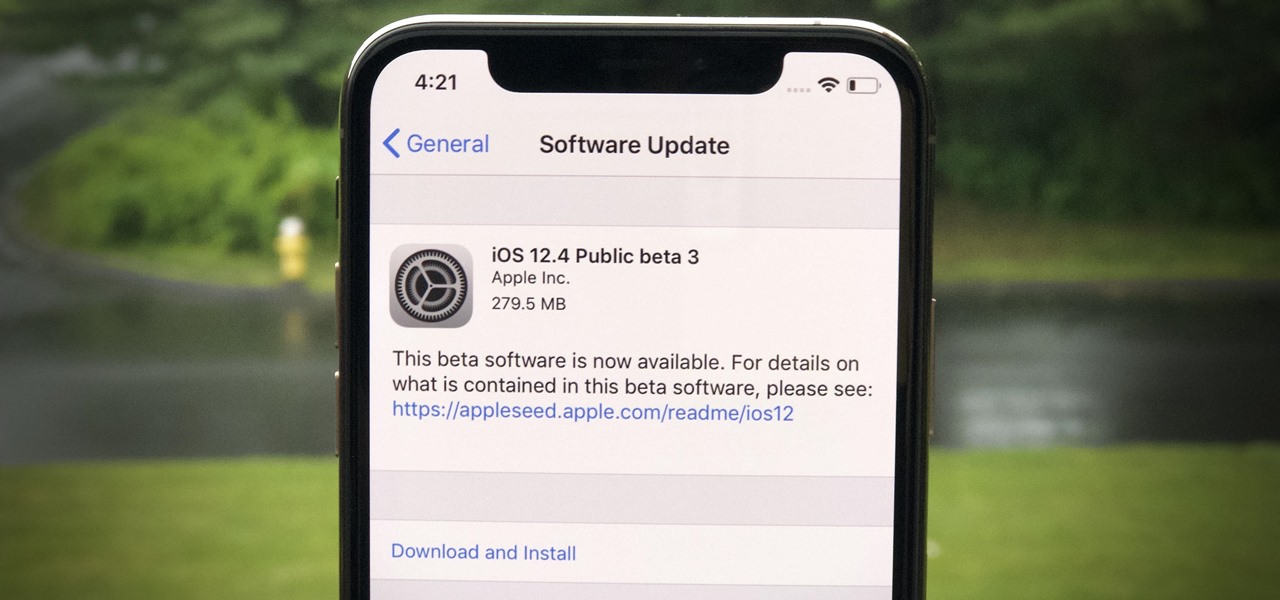
Apple released the third public beta for iOS 12.4 on the afternoon of May 28. The update arrives roughly three hours after Apple published 12.4's third developer beta, and eight days after 12.4 public beta 2. At this time, it seems beta 3 is a minor update for 12.4, which itself is a small upgrade to iOS 12 as a whole. We expect iOS 12.4's shining feature to be Apple Card support.

While AT&T is gradually showing off the powers of its 5G technology in the US via the Magic Leap One, another major wireless company is doing the same in the UK using the world of fashion.

The last few months have delivered some great new Magic Leap releases, but that doesn't mean the development team is resting on its laurels when it comes to the platform itself.

The tradition of using cutting edge technology to prepare for missions in space, in this case, augmented reality, continues with a new team of international astronauts slated to board the International Space Station (ISS) later this year.

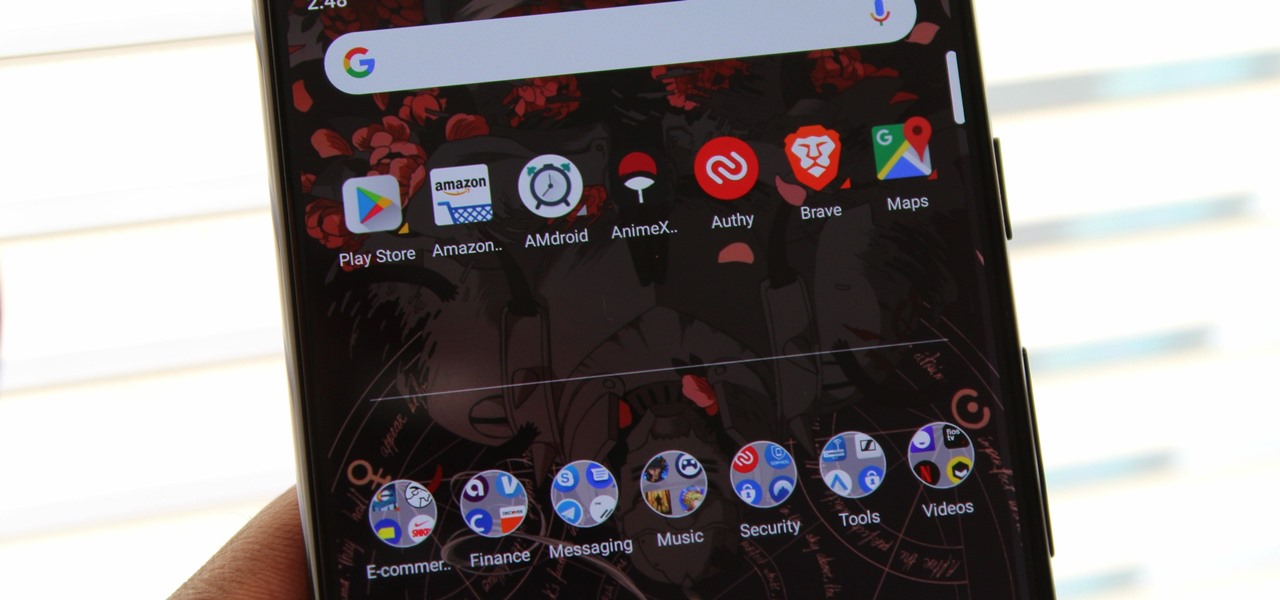
According to App Annie, the average person's phone contains 60–90 apps. Such a large amount can easily crowd an app drawer, especially since the same source states that only about 30 are used in a month. Having a way to organize apps in the app drawer can help you avoid wasting time searching.

The North remembers...that smartglasses are the future! Game of Thrones jokes aside, the smartglasses startup opened its doors, and we visited its Brooklyn store to get our hands the consumer-focused Focals smartglasses.

Election Day is like the Super Bowl for network and cable TV news, so ABC News is breaking out the big guns with a new augmented reality experience to win over eyeballs of viewers.

Despite the relatively small size of Magic Leap's first annual L.E.A.P. conference, there was a lot to see and experience. Apparently missed by many was one of the best experiences I had at the event: Wingnut AR's unreleased Pest Control game.

The latest business move by Magic Leap could result in a significant boost to its spatial computing platform's performance and headset design.

Venom, the latest in a long list of comic book characters to headline its own movie, is known by comic book fans by his catchphrase, "We are Venom."

Data breaches are all too common now, and the latest one you need to know about involves Timehop, a mobile app that makes it easy to reminisce over old photos. The breach, which took place on July 4, was revealed on Sunday, July 8. At the time, Timehop disclosed that 21 million users had been affected by the breach, but it now appears that all users were impacted in some way.

Two-factor authentication (2FA) is a great way to add another layer of security to sensitive third-party apps and websites like Venmo. However, before iOS 12, to log into a particular 2FA-secured app or site on your iPhone, you'd have to memorize or copy the SMS code from Messages, then jump back in a timely manner to log in. Apple's latest iOS version streamlines this process.

For years, Magic Leap has promised to deliver stunning augmented reality experiences that will outperform any other competitor, and a newly revealed partnership hints that the company may be able to deliver on those promises.

The NBA Finals is underway, and now basketball fans with iPhones and Android devices can get closer to the action for free than they ever could with expensive courtside tickets.

While some in the augmented reality space are tweeting about future amazing immersive experiences and others are showing off cool experiments, Microsoft continues to move forward with tangible business solutions right now that show how the HoloLens can improve business.

The annual Coachella Valley Music and Arts Festival is one of those events that everyone talks about, so an augmented reality experience in the festival's mobile app and from one of its headlining acts, Eminem, basically means the technology is officially cool.

Instagram is no stranger to stealing features from Snapchat. Stories, originally a Snapchat invention, feels more at home with Instagram today. Now, Instagram is attempting to repeat this feat with nametags, a way to quickly add new friends akin to Snapchat's Snapcodes.

In the latest example of life imitating art, IBM has applied for a patent for a video censoring system that looks a lot like the "Arkangel" child monitoring system from the latest collection of modern sci-fi fables from Black Mirror on Netflix.

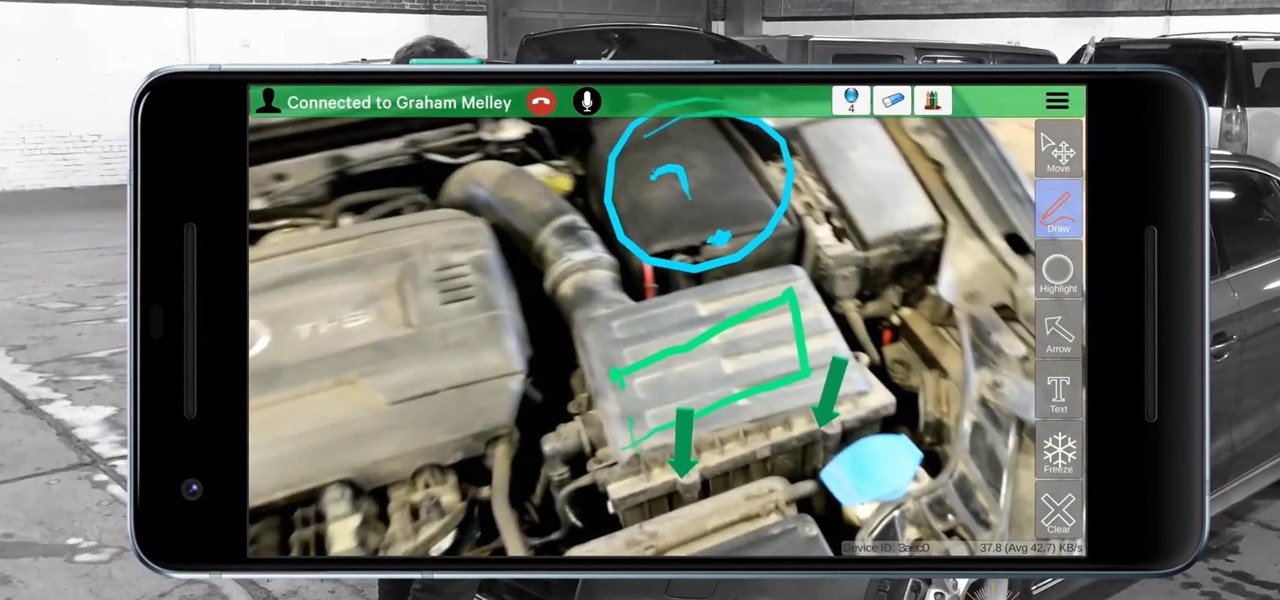
Scope AR has decided to take its live remote assistance enterprise application, Remote AR, further into the mobile augmented reality realm by harnessing the powers of Google's recently released ARCore.

Magic Leap's recent flurry of patent applications prompted us to look around for any trademark movements from the company, and it turns out that the Florida-based company has been quite busy.

The once blurry and mysterious vision of Magic Leap's future is slowly coming into focus in the present, despite the company's obsessive attempts to keep any and all information under wraps until the next reveal is absolutely necessary. A new tidbit of information hints at an addition to the company's unfolding story that almost no one had accounted for: retail stores.

Among the revelations uncovered during the December unveiling of the Magic Leap One: Creator Edition was the fact that the Lightwear augmented reality headset would be tethered to a wearable computer called the Lightpack.

Update: Monday, 11 p.m. ET: In a report from Bloomberg, eMagin CEO Jeffrey Lucas has contradicted what appeared to be investor information found in SEC filings that surfaced on Monday. Although Apple is listed among several other investors in the company in filing, Lucas told Bloomberg that Apple is not, in fact, an investor in the company. Offering further clarification, Lucas told the news site that eMagin "listed those companies in the filing because it had discussions with them at industr...