New to Ubuntu Linux? This computer operating system could be a bit tricky for beginners, but fret not, help is here. Check out this video tutorial on how to install PhotoFilmStrip on Ubuntu Linux and Windows.

While many people back up their important files on a regular basis, few back up their entire computer. If your computer were to crash or be damaged, reinstalling the software for your system can mean hours or days of downtime. In this video tutorial, you'll learn how to use the PC Backup and Restore features in Microsoft Windows Vista. Take a look.

Have you recently switched to an Apple computer? This video how-to demonstrates three helpful techniques to make your transition from PC to Mac as smooth as possible. Specifically, this tutorial addresses workflow management and keyboard shortcuts. For more information, as well as to get started acclimating to your new operating system, take a look at this OS X tutorial.

Safari makes it easy to browse multiple web sites in the same browser window using tabs. In the latest version of Safari in Leopard, you'll find even greater flexibility in the way you deal with tabs. For a survey of the new features available to users of Apple Safarin in the Mac OS X Leopard operating system, watch this video tutorial.
Cancel or Allow? In this video tutorial, TigerTV Host Logan shows you how to get Microsoft's new operating system, Windows Vista, in line and singing your tune. To disable user account control pop-ups in Windows Vista, watch this how-to. Take a look!

This video demonstrates Mac foundation application with a eyebrow stencil package.

This is my first contribution in an ongoing series on detailing the best free, open source hacking and penetration tools available. My goal is to show you some of the quality tools that IT security experts are using every day in their jobs as network security and pen-testing professionals. There are hundreds of tools out there, but I will focus and those that meet four key criteria:

In this video, we learn how to install a Toad Stop braking system for towed vehicles. First, determine where you are going to install the braking system. Insert the electrical wires into the appropriate spots by reading the labels that are on them. After this, use a drill to lock down any parts that are loose. Once you place the braking system in, you will need to lock it down using the wires that come with it. Make sure these are installed properly throughout the entire vehicle up until you ...

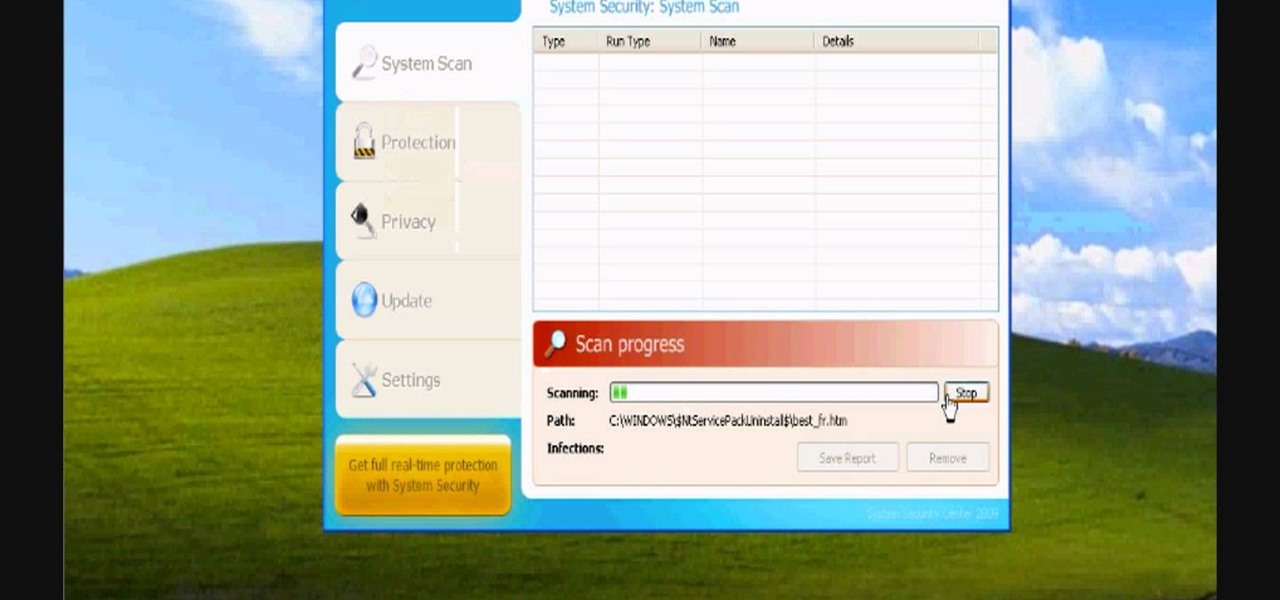
In this video, we learn how to avoid getting infected by "system security". Make sure you avoid the website that show the System Security Anti-Virus. Once you install this onto your computer it will pretend like it is doing a scan, but in reality is hurting your computer. It will pop up showing you that you have problems on your computer, but the alert will never go away. If you delete this, it will just re-install on your computer instead. To do this the correct way, you need to go to your m...

If you want to make sure your sump pump is always working properly, a backup battery would be a good idea. But Basement Watchdog actually makes a combination sump pump power system that controls you primary (AC) power and has a backup battery (DC) for emergencies. This video shows you how to install the complete combo sump pump system to make sure the flooding never starts. Find out how to assess the sump pit, install the combo system, connect the sump pump to the standby battery and more. Ke...

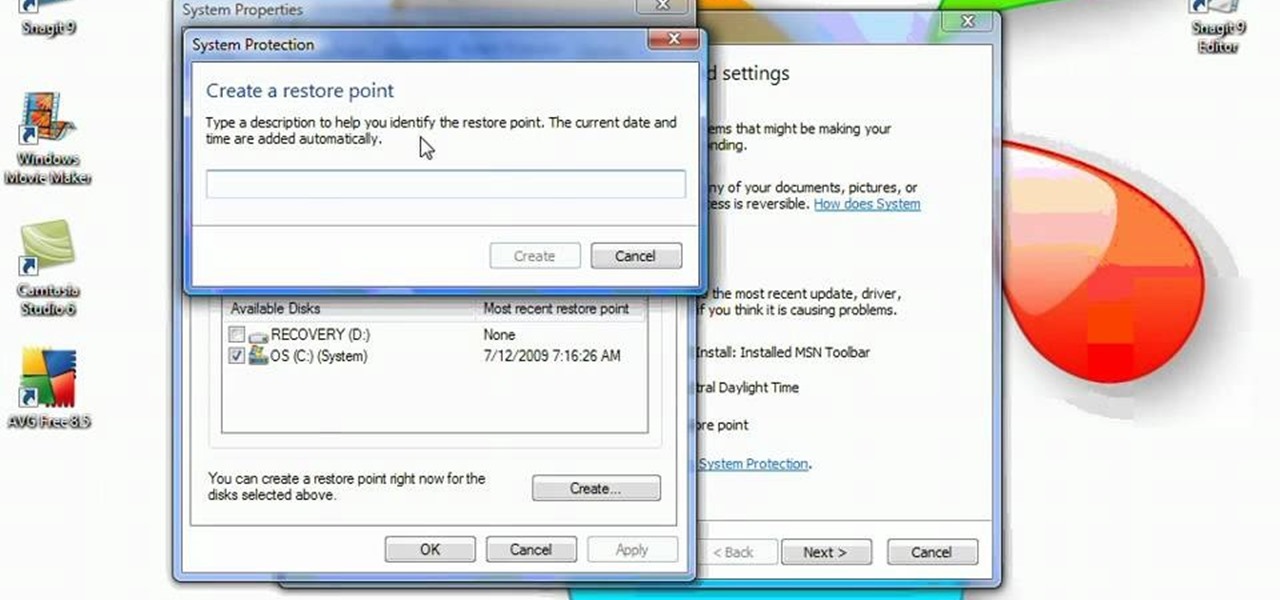
System Restore helps can help fixing the problems that might be making your Computer run slowly or stop responding. Please follow the steps below to restore the Computer running the Windows Vista Operating System.

Although it is a rare and potentially frightening occurrence, knowing how to do a system restore in Windows XP is an important thing to know how to do. To get started with a system restore, select the Start menu in the lower right of your screen. Then select All Programs. Then from the All Program menu, select Accessories and then from Accessories, select System Tools. There are several items under System Tools, but you want to select System Restore. You will follow through the next few scree...

Check out this instructional climbing video that demonstrates how to set up the ascent system for crevasse self rescue. Hooking up the prussik is the subject of this video and stops at the second ascender required for upward mobility. Watch all the crevasse self rescue series and you may get the hang of this. It is best to practice this somewhere dry and safe before the real thing happens. When you are in the hole things get tougher.

Big Tony the plumber introduces you to the process of installing a residential lawn sprinkler system.

Perform cable management to improve cooling and system layout.

Understanding the Binary Numbering System and how to decode binary numbers.

Not all Kickstarters are created equal. Some take forever to get their products to supporters, and when the product does arrive (usually much later than promised) it's often very rough around the edges.

Bud Light being the official beer sponsor of the NFL just makes sense for American football. But what about the NHL, with hockey being the official winter sport of Canada by decree?

Prompt and frequent system updates are a big part of the Pixel's identity — we're even getting quarterly feature drops now. But not all devices receive these all-important updates at the same time because of Google's staged rollout system. If you want the update right away, there's a way to manually check without having to dig around in Settings every time.

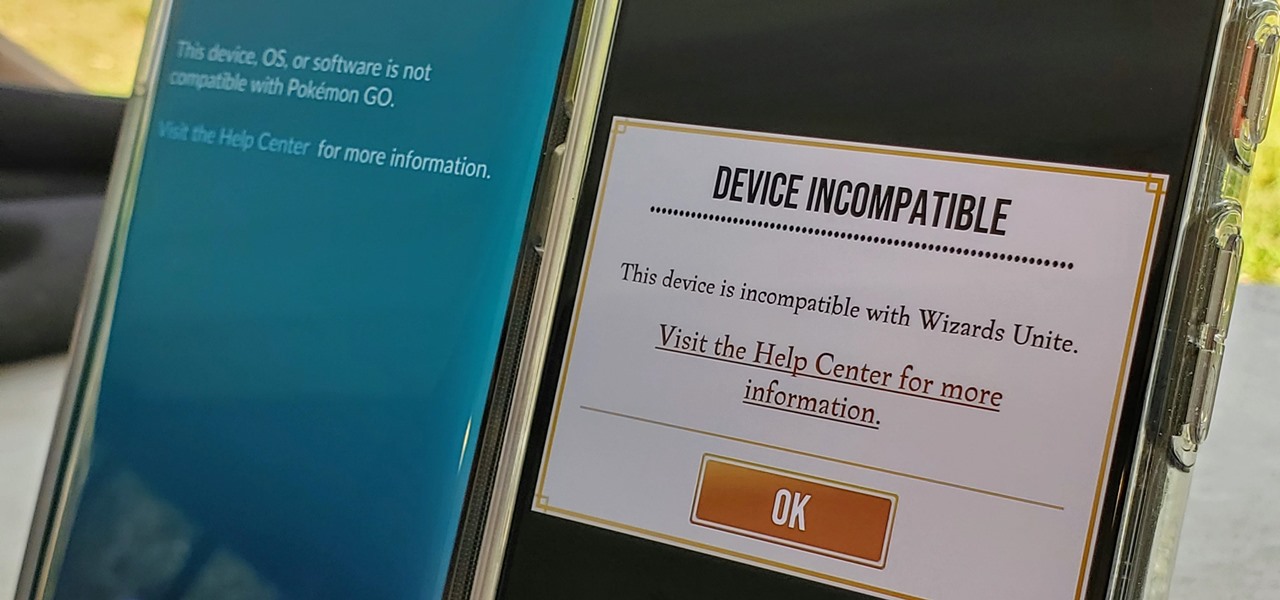
Both Pokémon GO & Harry Potter Wizards Unite are augmented reality games developed by Niantic, and neither needs much introduction. Pokémon GO, all by itself, created a worldwide phenomenon that still carries a strong fan base years later — Wizards Unite is working on doing the same. However, things are not all fun and games, as you might think in the world of monsters and magical creatures.

While Elon Musk is in Los Angeles showing off the future of personal transport via the Cybertruck, another, unaffiliated group is taking one of his most popular ideas to market, with augmented reality as a key part of the plan.

By now, you've probably been inundated with enough Baby Yoda memes to last you a lifetime. But if you don't have the new Disney Plus streaming service on your TV, you're probably wondering where all this is coming from. Well, lucky for you, just in time for the holiday season, we're here to guide you to the best ways to take part in all the streaming fun when you're not glued to your mobile devices.

Whether you love Motion Sense or think it's a gimmick, one thing we can agree on is that its functionality is limited. It's currently limited to switching tracks on a playlist, snoozing alarms, silencing calls, lowering the volume of alerts, and checking notifications. But a new mod will help you do so much more with it.

TWRP is a name many are familiar with since it allows your Android device to install any custom file of your choosing. You can create a NANDroid backup to keep your data safe or even use Magisk to achieve full root access. In fact, TWRP is often seen as the gateway to modding your system for creating a unique user experience.

The first thing you'll always have to do before getting your customization game on with most phones is to unlock the bootloader. Doing so opens the true potential of the device, allowing you to root, install TWRP, Magisk, custom ROMs, and other mods. No matter your wants or needs, there's no way around it — the bootloader must be unlocked to modify the system.

For many, the stock version of Android is often considered the epitome of what the operating system should look and feel like by default. It's clean and clear of unwanted extra apps that come pre-installed with the system, provides a fluid and fast user experience, and runs on just about any device that has an unlocked bootloader to install a custom ROM with the stock version ready to go.

While Leap Motion has given makers a DIY solution for building their own augmented reality headset with Project North Star, a self-described "AR wonk" has taken the blueprints one step further by creating an untethered version.

Before you can dive into customizing your OnePlus 6T, you must take the initial step of unlocking the bootloader to gain the ability to install TWRP, Magisk, custom ROMs, and other mods.

Single sign-on (SSO) lets users login across different sites without having to manage multiple accounts. I'm sure most of us appreciate the convenience of seeing "Sign in with …" buttons that let us login with a single username. Hackers, however, see a possible avenue for exploitation, and you'll soon learn how an attacker can exploit a SAML vulnerability to assume another user's identity.

After a long hiatus, we shall once again emerge from the shadowy depths of the internet to build an exploit. This time, we'll be looking at how to defeat a non-executable stack by using the ret2libc technique — a lean, mean, and brilliant way of exploiting a stack overflow vulnerability.

Not all microwaves are created equal, so when you use the recommended cooking time on any microwaveable meal, chances are you're actually cooking the food too much or not enough. And unless you're really good at mental math or have a virtual assistant that's smarter than Siri and Google, you have to do things the long way — but not with these helpful apps for iOS and Android.

Hacking from a host machine without any form of proxying is reckless for a hacker, and in a penetration test, could lead to an important IP address becoming quickly blacklisted by the target. By routing all traffic over Tor and reducing the threat of malicious entrance and exit nodes with a VPN, we can configure Kali to become thoroughly private and anonymous.

Augmented reality developer Blippar has created a new visual positioning service based on computer vision that is two times more accurate than GPS in urban locales.

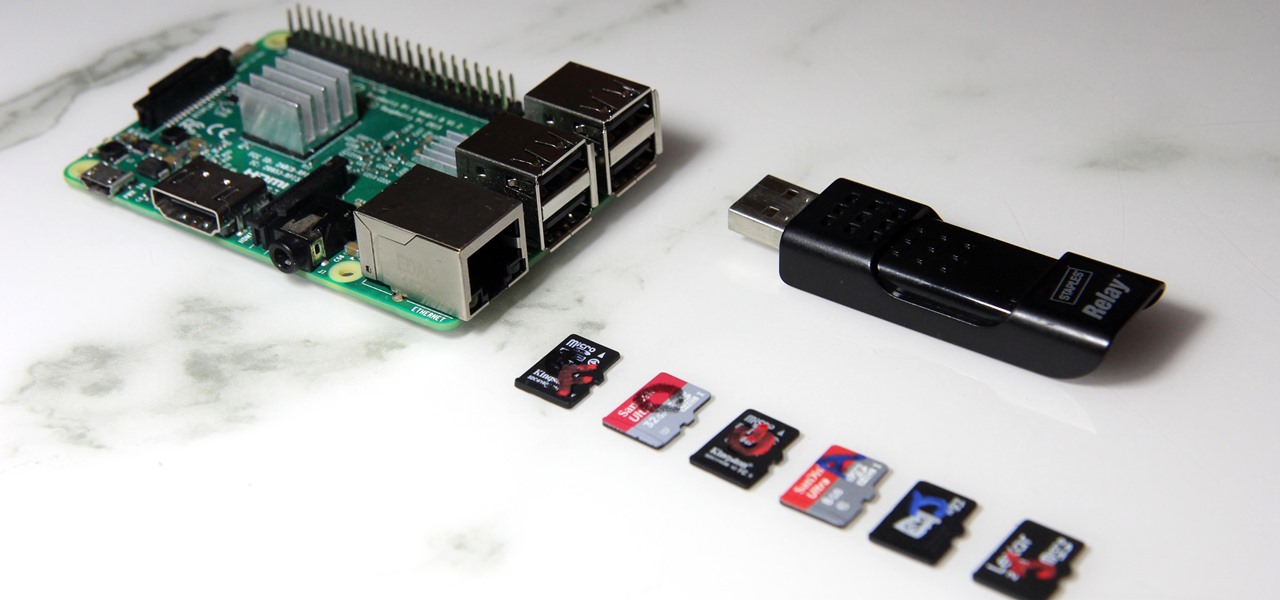
The Raspberry Pi loads an operating system from whatever SD card you insert, allowing you to keep different operating systems on separate SD cards depending on which OS you wish to run. A tool called BerryBoot cuts down on the number of SD cards needed by providing the ability to boot multiple operating systems from a single SD card, similar to Boot Camp for Mac computers.

German groups ZF Friedrichshafen AG and HELLA are collaborating to add to their autonomous portfolios with camera and radar development.

Google's Pixel phones claimed the top spot in our ranking of the best phones for rooting, but they do have one drawback from a modder's perspective: Because of their A/B partition layout for seamless updates, the devices don't have official support for Magisk. Thankfully, though, developer goodwin has stepped in with a fix, so we can now get Magisk working on the Pixel and Pixel XL.

Uber has been in the hot seat for awhile now, for many reasons, especially for being sued by Waymo over stolen LiDAR designs. But now, perhaps the attention will be taken off both Uber and Waymo as a new contender enters the LiDAR arena; A small, independent company called Luminar has finally let the world in on what it has been cooking up.

These days, if you walk through Best Buy, you will see an entire area designated to smart home technology. Thanks to the interest and growth of the Internet of Things (IoT), this exciting new technology has finally entered the mainstream. Appliances, thermostats, and even the lighting throughout your house can be controlled from your computer or smartphone. You could also use artificial intelligence; Simply tell Amazon's Alexa what you want your house to do, and she will do it.

Containers are isolated software instances representing applications, servers, and even operating systems—complete with all of their dependencies, libraries configuration files, etc.—and they're taking over the corporate world. The ephemeral, portable nature of containers help them stay current and speedy, and they can work on pretty much any computer, virtual machine, and cloud.

When you were unboxing your Galaxy Note7, you probably wondered why a little metal claw tool was included in the packaging. Then, if you looked closer, you saw there were five plastic sticks included with the claw tool that came in two different colors.