Part of the mainstreaming of augmented reality is learning to adopt new habits around the hardware delivering these groundbreaking next-gen interface experiences.
The makers of arguably the two most important mobile AR apps, Niantic and Snap, both had good news this week, with the former preparing to replicate its success with Pokémon GO for another franchise and the latter notching another popular augmented reality Lens for Snapchat.
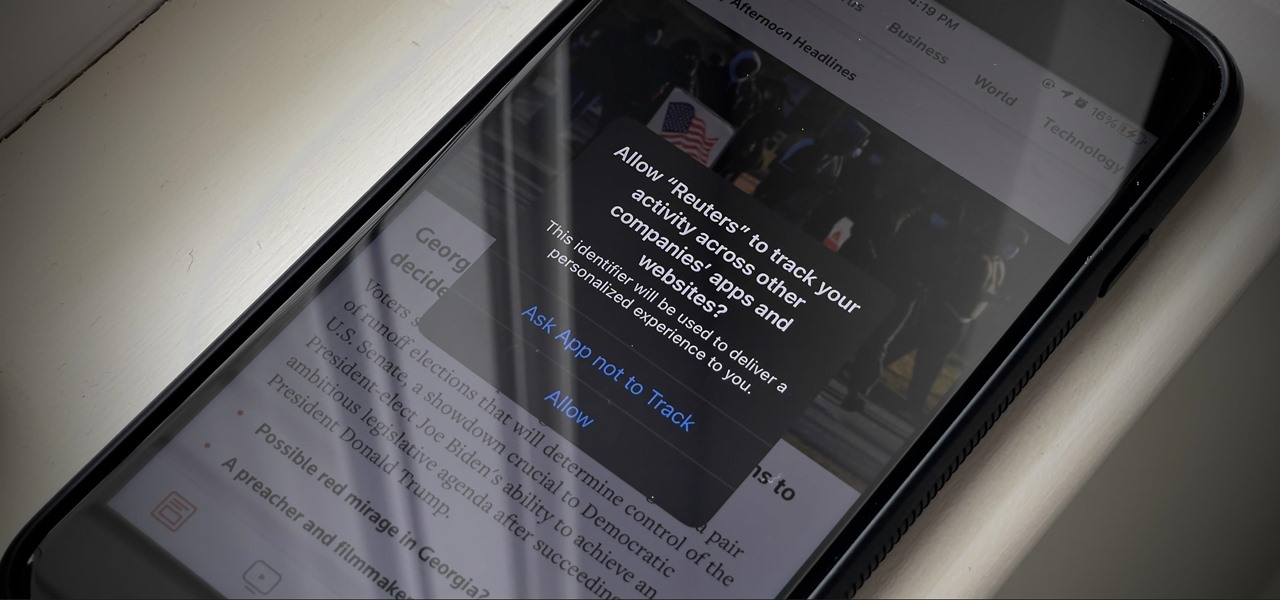
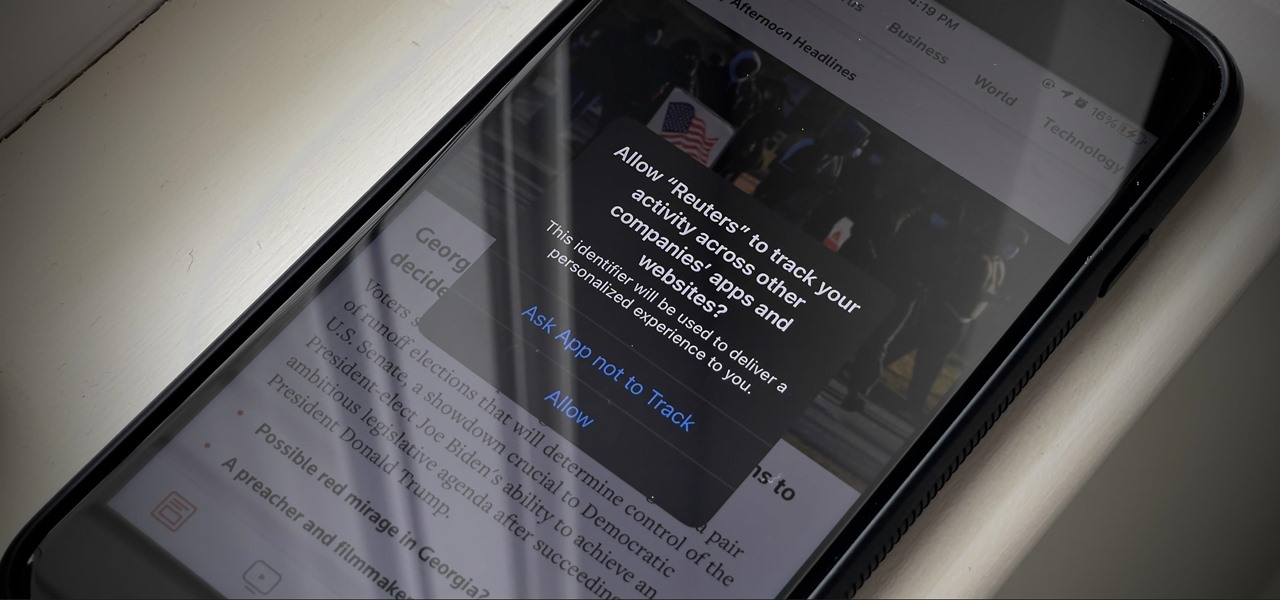
If you're like me, you're not too keen on being tracked. So when an app asks you if it can track your iPhone activity across other programs and websites for ads or data brokers, the answer is pretty much always "no." If you're tired of choosing "Ask App Not to Track" over and over again, there is a way to stop apps from even being able to ask in the first place.
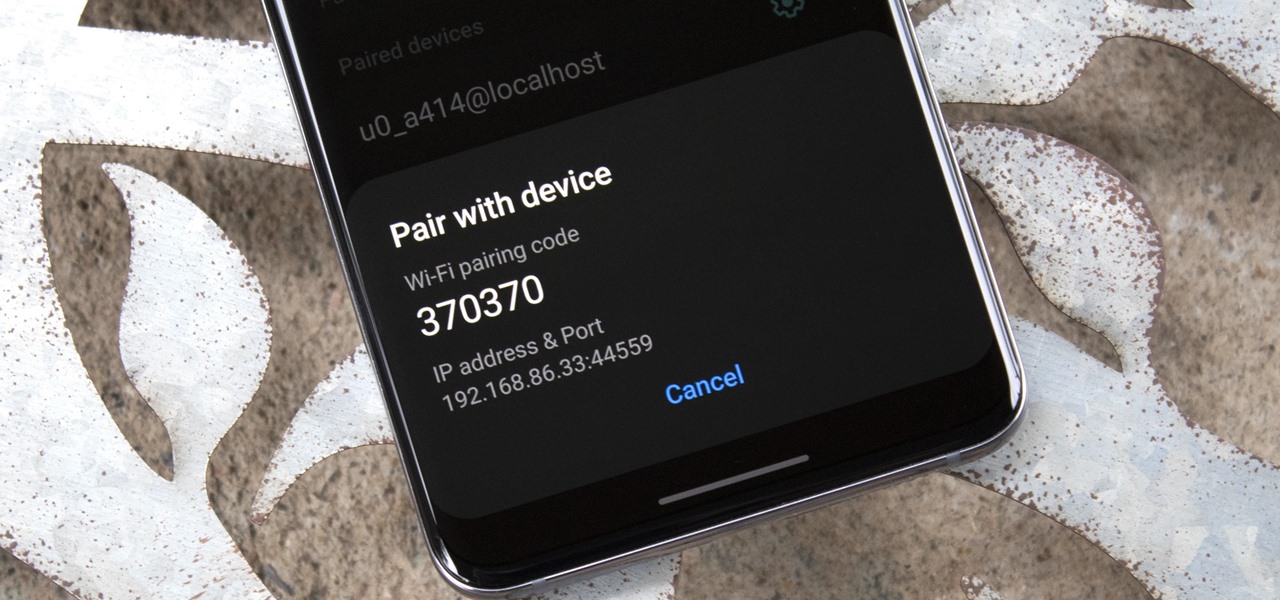
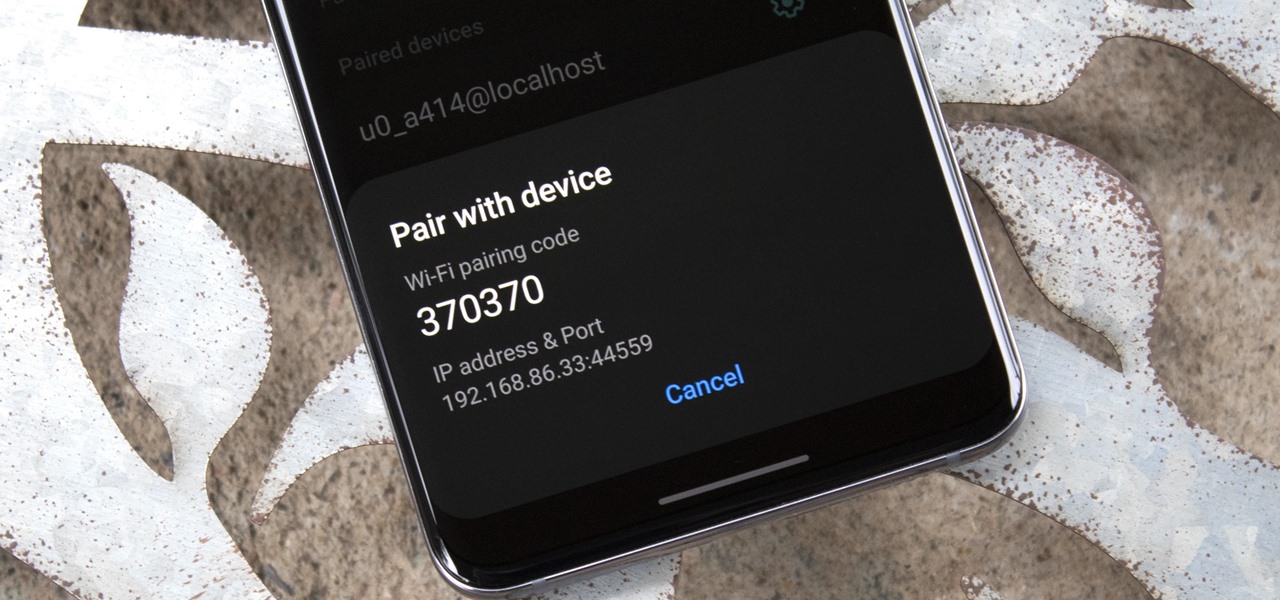
Samsung's One UI 3.0 skin is built on top of Google's Android 11 open source code base, which means you get all of the standard features, plus some cool bonus stuff from Samsung. However, it's one of those standard AOSP features that you might find most useful if you send a lot of ADB commands.

Apple Music's Replay feature sucks. Aside from not being very accessible, it offers a fraction of your history compared to Spotify Wrapped, which does a deep dive into what you listened to over the last year. Not only that but Spotify packages data into visuals you can share on social media. While you could share Replay screenshots, there are better options out there for Apple Music users.

The 2020 Chromecast is full of new features, but one glaring omission is Stadia, Google's cloud gaming platform. The search giant confirmed Stadia wouldn't officially arrive on the new streaming dongle until the first half of 2021 — but there's an unofficial way to get it now.

The gesture navigation introduced with Android 10 worked wonders by giving you more of your screen and less tapping. Android 11 offers the option to fine-tune the back gesture sensitivity for your screen's left and right sides. However, the issue still stands for people who like to use the left swipe menu within apps to open hamburger style menus.

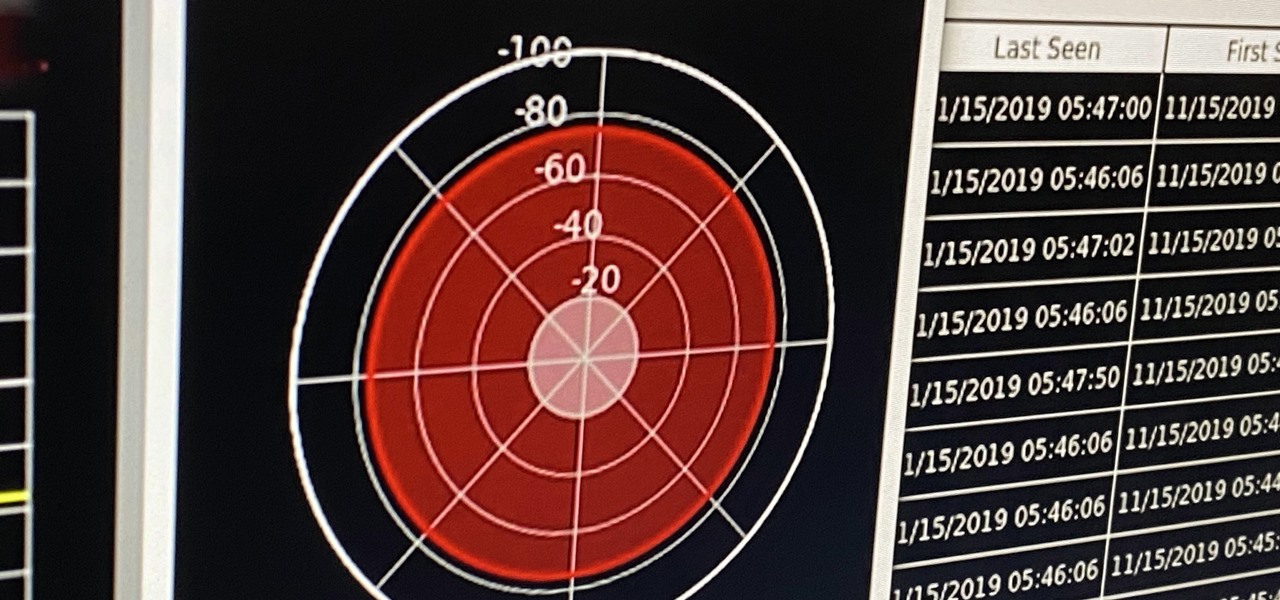
If you're ever in a situation where you need to take a peek at the wireless spectrum, whether it's for Bluetooth or Wi-Fi devices, there's a fascinating Python 3-based tool called Sparrow-wifi you should check out. It's cross-platform, easy to use, and has an impressive GUI that shows you the signal strength of nearby devices.

If you're in the market for a new smartphone, there are some pretty fantastic options for $400 or less. Both Apple and Google have unveiled budget smartphones with high-end specs in 2020, so you no longer have to suffer from subpar quality to save a few bucks. Low prices no longer mean cheap phones.

After years of complaining about rising prices, OEMs are finally listening to consumers. It couldn't have come at a better time thanks to potential recession due to COVID-19. As evident with the poor sales of Samsung's Galaxy S20 series, consumers are not looking to spending $1,000+ on a smartphone just for the latest specs.

I've covered augmented reality apps for about three years now and the most useful mobile app I've encountered over that time is Google Lens.

When it comes to modding your Android device, you'll want to be familiar with the TWRP name and what it stands for. It's a tool that you'll be using to make NANDroid backups or to install just about any mod file you can think of — the number of uses is quite awesome. You'll mostly be after Magisk for root access and potentially a custom kernel as well.

A hacker with privileged access to a Windows 10 computer can configure it to act as a web proxy, which allows the attacker to target devices and services on the network through the compromised computer. The probes and attacks appear to originate from the Windows 10 computer, making it difficult to detect the attacker's actual location.

The gig economy is thriving, and if you aren't already making money with your phone, you could be missing out on easy residual income. Some people just want extra cash, and some even manage to completely ditch the 9–5, enabling them to work at their own pace and set their own hours.

Whether you're in high school or college, you no doubt will have your iPhone in your pocket all day long. To make your iPhone last the whole time and even help you out with your studies, these are the accessories you'll want to get your hands on.

With an ordinary birthday card, we can introduce a physical device which contains malicious files into someone's home and deceive them into inserting the device into a computer.

As a developer, before you can make augmented-reality robots that move around in the real world, controlled by a user's finger, you first need to learn how to harness the basics of designing AR software for a touchscreen interface.

While Apple keeps the Pro and Pro Max iPhone models nearly the same this year, there are still a few differences between the iPhone 16 Pro and iPhone 16 Pro Max. Knowing them may help you decide which Pro model to get.

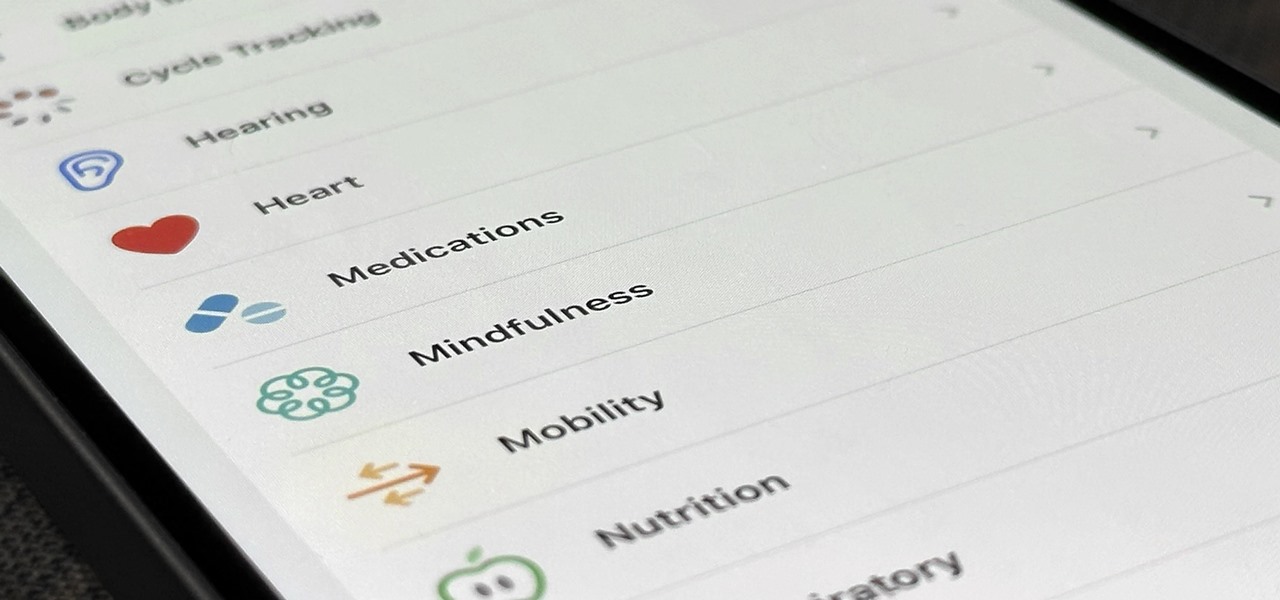
Your iPhone's Health app has a new medications hub that can be a one-stop destination for all the medicine, vitamins, and supplements you're taking. Adding new entries is easy and well worth the effort to get reminders to take your meds, learn about drug interactions, easily share your routine, and track your history to see what is and isn't working for you.

If you've recently built a Wi-Fi spy camera out of an ESP32-CAM, you can use it for a variety of things. A baby monitor at night, a security camera for catching package thieves, a hidden video streamer to catch someone going somewhere they shouldn't be — you could use it for pretty much anything. Best of all, this inexpensive camera module can perform facial detection and facial recognition!

Kali Linux is the go-to Linux distribution for penetration testing and ethical hacking. Still, it's not recommended for day-to-day use, such as responding to emails, playing games, or checking Facebook. That's why it's better to run your Kali Linux system from a bootable USB drive.

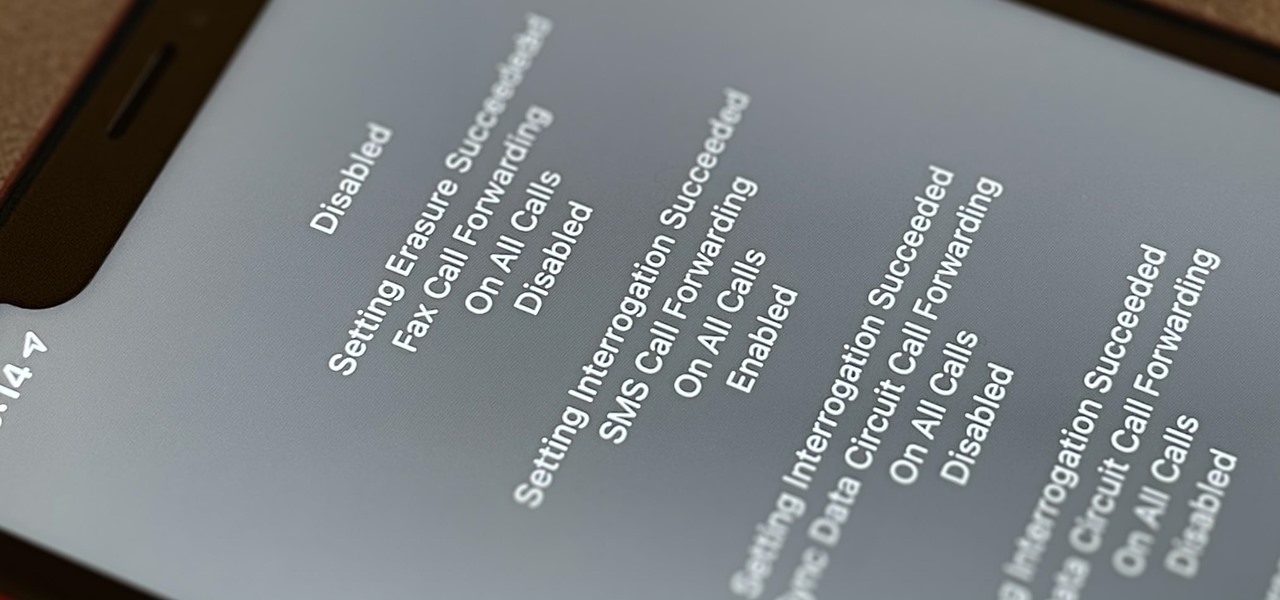
Malevolent hackers can divert your incoming calls and texts to any number they want, and they don't need to be a criminal mastermind to do it. Even friends and family members can reroute your incoming calls and messages so that they know exactly who's trying to reach you, and all it takes is seconds of access to your iPhone or wireless account. These secret codes can help uncover them.

For those of us without rice cookers, conventional wisdom tells us that the stove is our only real option (unless, of course, you dabble in microwavable rice). However, if you're only using the stove for cooking rice start-to-finish, you're missing out on the easiest way to make perfect rice every time.

Microcontrollers like ESP8266-based boards have built-in Wi-Fi, and that's really cool, but what's even cooler is that certain pro models of the D1 Mini also have a port where you can connect a directional antenna. This can give you exceptional range, but if you were to just plug one in after opening the package, it most likely wouldn't work.

The Nintendo Switch and Switch Lite are console gaming on the go — with zero regards for modern audio features. Headphone jack? Check. Bluetooth connectivity? Not so much. While Nintendo seems to think we're all happy to live like it's 2015, there's a way to use your AirPods with your Switch or Switch Lite for wireless and convenient entertainment.

Withstanding an attack from a motivated hacker is one of the most important responsibilities a system administrator must undertake. This is especially true for websites that may contain sensitive customer information and a high volume of users. So it's important for a sysadmin to take proactive measures to find and fix vulnerabilities in their websites.

The iPhone 12, 12 mini, 12 Pro, and 12 Pro Max all have positive coverage surrounding their refreshed design, camera upgrades, and 5G connectivity. One piece of negative press you might've seen, however, is about the charger. Specifically, that there's a Lightning to USB-C cable in the box but no power adapter. That means you'll need a charger, and we've got some good recommendations for you.

When approaching a target, having a precise and detailed plan of attack is absolutely necessary. One of the main goals is to increase the attack surface since the more opportunities there are for exploitation, the greater the chances of success. Subdomain enumeration is one method used to increase the attack surface, and we'll be using a tool called Subfinder to discover hidden subdomains.

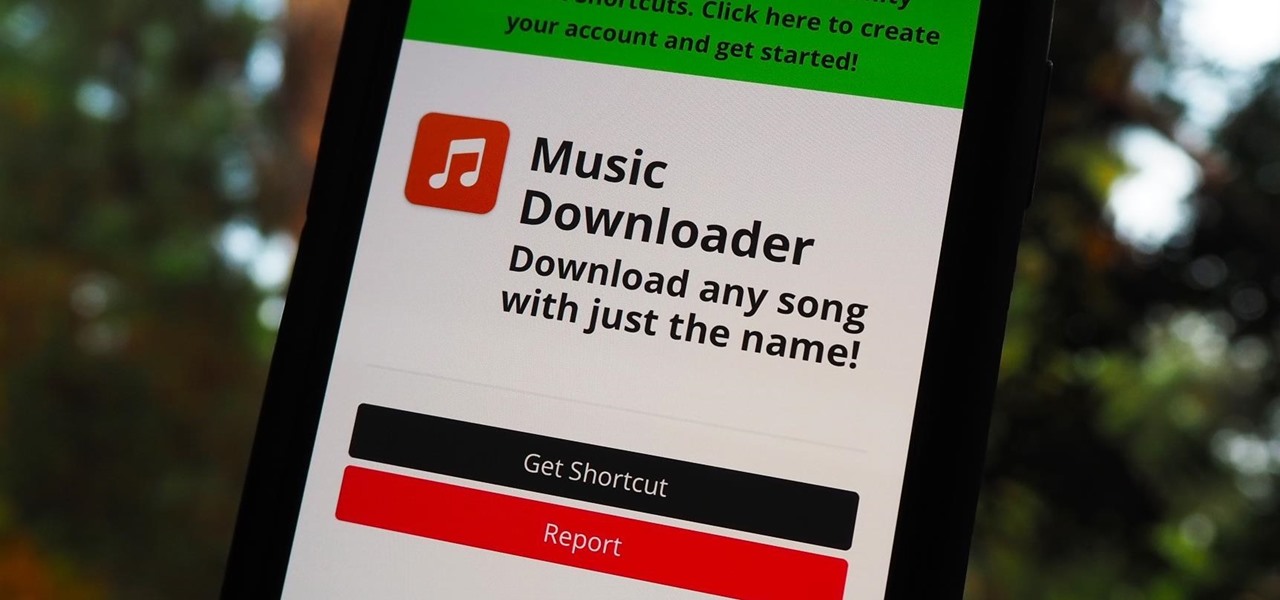
Music streaming services like Apple Music, Spotify, and YouTube Music make it easy to find and play your favorite artists and albums on your iPhone — but they cost upward of $14.99 per month. If you're more into listening to downloaded music, a shortcut can help you find free music online that you can get and playback in almost any media player of your choosing.

Since iOS 9, the iPad has had Picture in Picture mode, which lets you minimize a video that you're watching into a floating overlay so that you can multitask in other apps while it plays. For iPhones, it came a little later, first appearing in iOS 14. It's not just for the Plus or Max displays either — any size display works.

The art of fuzzing is a vital skill for any penetration tester or hacker to possess. The faster you fuzz, and the more efficiently you are at doing it, the closer you come to achieving your goal, whether that means finding a valid bug or discovering an initial attack vector. A tool called ffuf comes in handy to help speed things along and fuzz for parameters, directors, and more.

One of the most promising avenues of attack in a web application is the file upload. With results ranging from XSS to full-blown code execution, file uploads are an attractive target for hackers. There are usually restrictions in place that can make it challenging to execute an attack, but there are various techniques a hacker could use to beat file upload restrictions to get a shell.

Advancements in technology have made it perfectly possible to make a short film or even an entire movie with your iPhone or Android — as long as you've got the right gear. Lenses, stabilizers, tripods, lighting, microphones, chargers, and cases can make the difference between a good movie and a great film, all of which can make a great gift for those aspiring (or current) filmmakers in your life.

After an update on Sept. 22, 2020, the Checkra1n jailbreaking tool expanded its compatibility to include iOS 12.0 to iOS 12.2, as well as iOS 13.5.1 to iOS 13.7. More importantly, however, it now can jailbreak iOS 14 on select iPhone models, with more support coming soon.

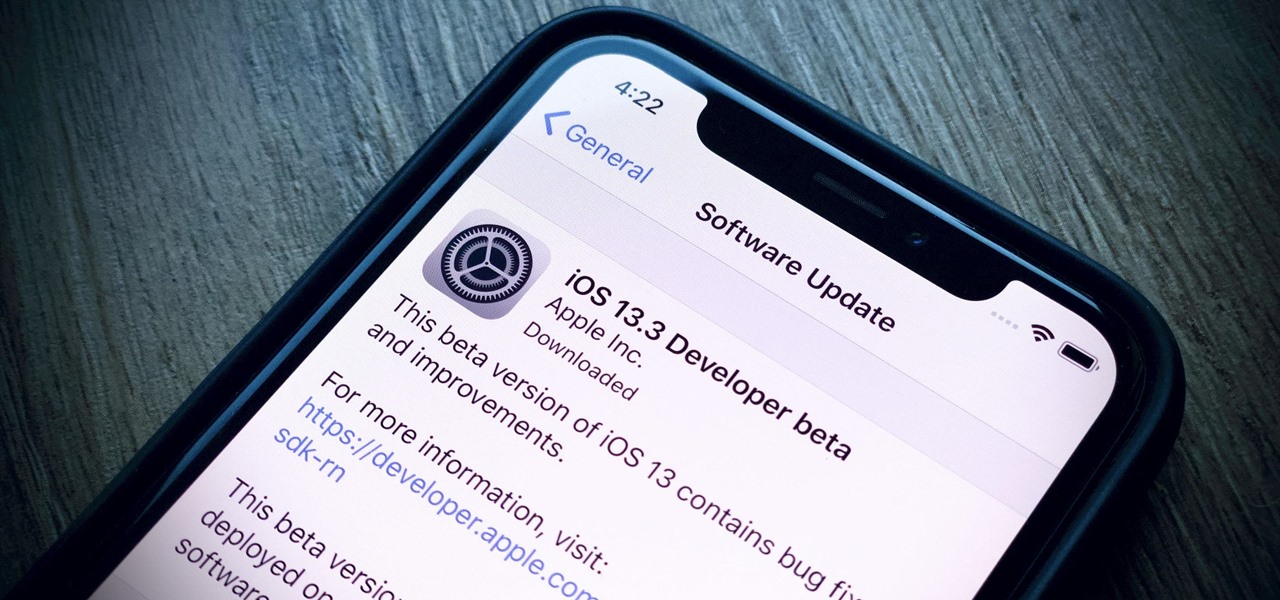
Apple's already gone through iOS 13.0, 13.1, 13.2, 13.3, 13.4, and 13.5 betas, and now it's time for iOS 13.6. If you want to try out new features on your iPhone before the masses, install either the developer or public beta.

Unlike the realm of virtual reality, augmented reality is less about losing yourself in some fantasy environment, and more about getting things done in the real world. So while we've seen some great games that capture the imagination on devices like the Magic Leap One and the HoloLens, when it comes to real-world usage, the biggest developments coming for AR apps that are the more practical ones.

For many, phones are starting to replace televisions as the primary device for watching videos. Thanks to their portability and easy to use apps, it's often simpler to watch Netflix, Hulu, YouTube, or Prime Instant Video on the smaller screen. But not every phone is suited to fit this need, so we did some testing to find the best of the best when it comes to streaming videos.

If you have ever wanted to mod your Android device, your new best friend is easily going to be Team Win's TWRP custom recovery. This gives you access to file flashing on the fly, which can include such things as Magisk for root access, or even a custom ROM to replace the stock firmware that came with the device.

Windows 10 and macOS have poor reputations when it comes to customer privacy and user policies. Our hacking Windows 10 and hacking macOS articles might make it seem like a reasonably secure operating system doesn't exist. But I'm here to tell you that there is a viable alternative that could provide some sense of security and trust.

A mention of the deep web can bring to mind images of drugs, hackers, and other criminal activity. Despite the presence of these elements, the Tor network is a valuable tool for preserving privacy and anonymity. And browsing the deep web and any hidden services can be as simple as downloading the Tor Browser.