The Galaxy S7 edge comes with a feature called Edge Apps that lets you quickly launch your favorite apps by swiping in from the edge of your screen. It's a natural and intuitive gesture, and as a result, we've seen a recent influx of apps that look to emulate this feature.

The only knock on Samsung's last round of flagship devices is that TouchWiz is still alive and kicking. Aside from this overbearing skin that's been applied on top of Android, the Galaxy S6, S6 edge, Note 5, and this year's Galaxy S7 models are some of the best phones money can buy.
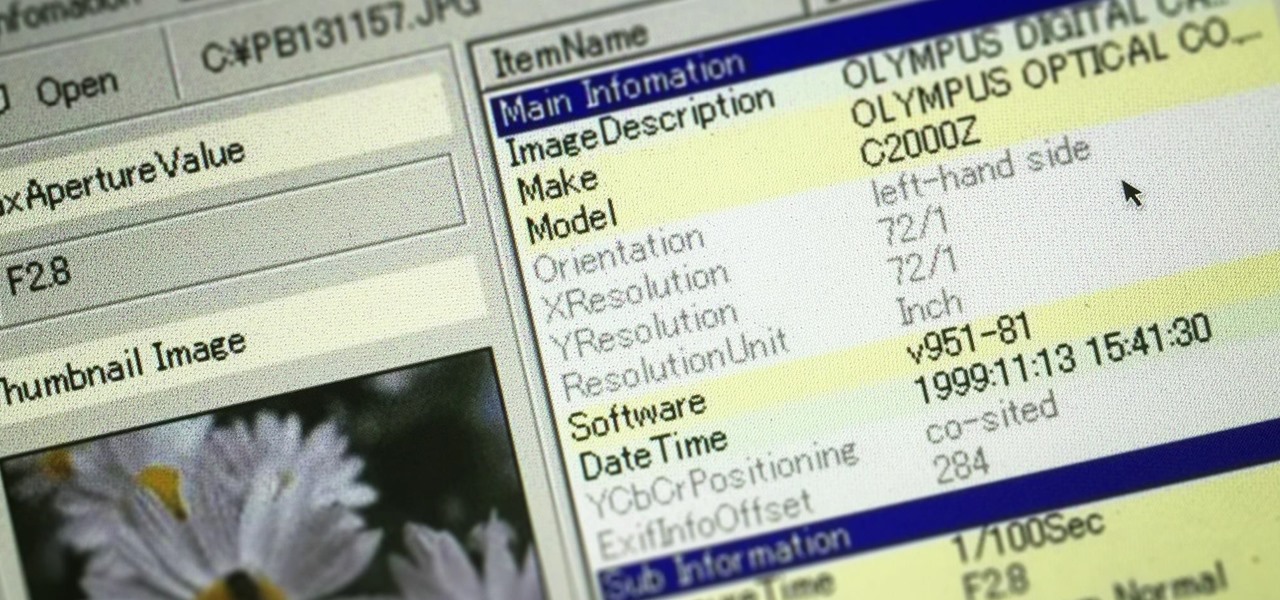
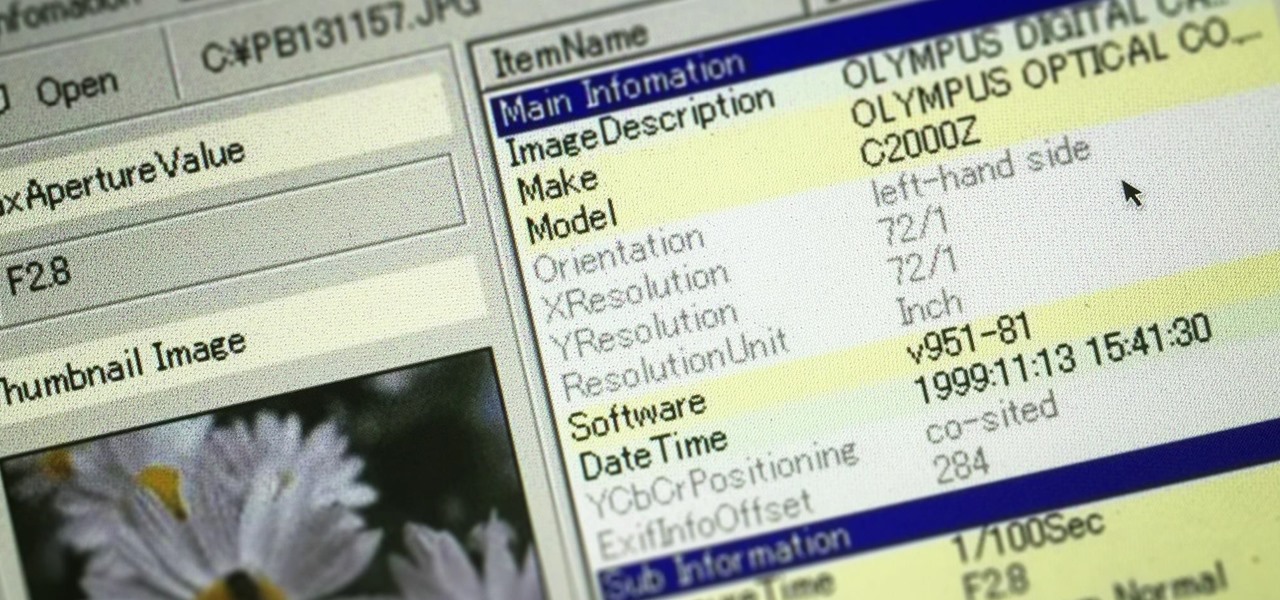
Welcome back, my greenhorn hackers! In many cases when a computer, phone, or mobile device is seized for evidence, the system will have graphic images that might be used as evidence. Obviously, in some cases these graphic images may be the evidence such as in child pornography cases. In other situations, the graphic images may tell us something about where and when the suspect was somewhere specific.
A little less than a year after announcing "Project Astoria," Microsoft announced Thursday, February 25th, that it will end the "Bridge," which would have brought Android apps to the Windows Store.

Android's Google Play Games app has let you track your feats and accomplishments in the games you play for quite a while now, but for some, the immersion experience might be broken after you finish dominating a game only to see your regular-ass name from your Google account on the leaderboard.

Even though the 88th Academy Awards have come and gone, there's a good chance you still haven't seen all the films that were nominated—or even those that won big.

Alright, this will be my first tutorial in C. Note that this guide is written for Linux.

Sony's Xperia smartphones are some of the most beautiful Android devices out there—but unfortunately, they're rarely promoted in the U.S. and are seldom available through major carriers (aside from the new Xperia Z5 devices), so not many Americans are aware of how awesome these devices really are.

Hello there Nullbyte users! This will be my first article here.

Hello fellow gray hat hackers, I wrote a program in python that helps me to fill up my proxychains.conf file, so I don't have to manually enter in the proxies. I figured I will give a little how-to of how I did it and maybe I could help some of you(hackers) out there to stay anonymous.

OK, In my last Tutorial we made a Server for sending Instructions to a Client. This time we will build the Client. Fire up your favourite Python environment and get the Code here.

The Nexus 5X and Nexus 6P have identical camera hardware—in fact, both use one of the highest-end camera sensors ever put into a smartphone. The only real difference between the cameras on Google's latest flagship devices is that the 6P natively supports electronic image stabilization (EIS) whereas the 5X does not.

Welcome back, my novice hackers! More and more, the world is turning to and adopting the smartphone platform as the digital device of choice. People are not only using smartphones for voice communication, but also web services, email, SMS, chatting, social networking, photography, payment services, and so on.

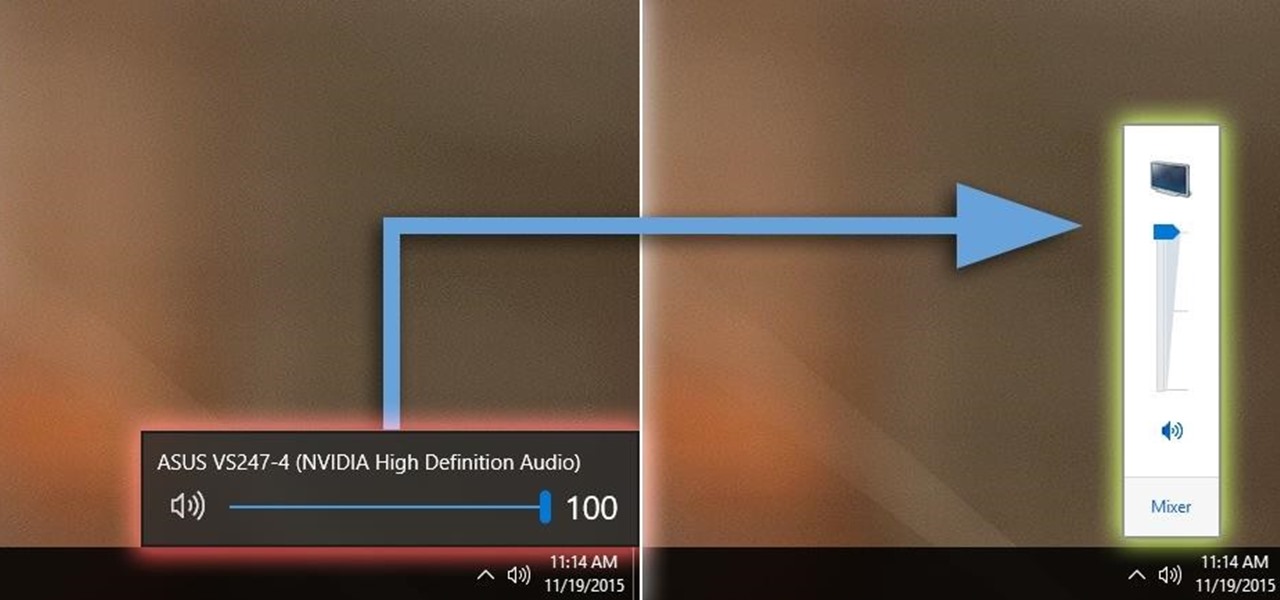
Windows 10 definitely has a sleek and modern look to it, but some of these visual changes have been made at the expense of functionality. For instance, the slider that appears when you click the volume icon in your notification tray now sports a completely minimalist look that lacks the quick link to the full volume mixer from past Windows versions.

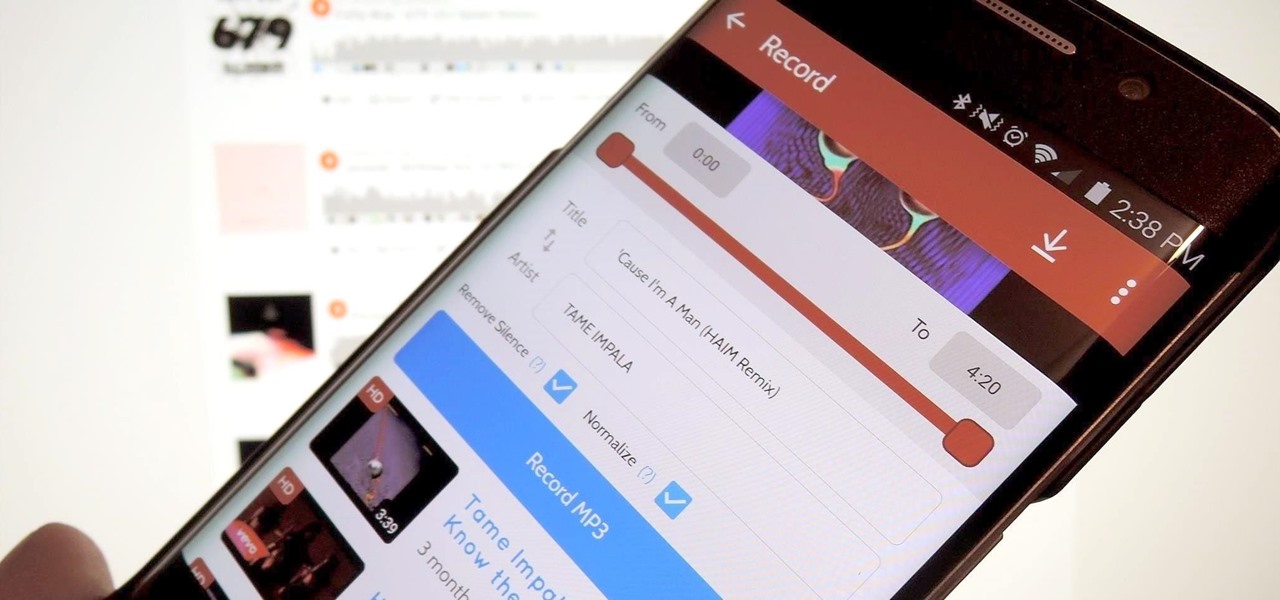
A growing trend for many artists (most recently Kanye West) is to offer exclusive or experimental tracks on music streaming sites like SoundCloud or YouTube before releasing them anywhere else. On rare occasions, some of these great songs never make their way onto an official album, which can be disappointing for die-hard fans who need to download every song available from their favorite artist or band.

Unless you have a newer iPhone 6S or 6S Plus, the front-facing "FaceTime" camera on your iPhone has a pretty weak, low-res sensor, which means unflattering selfies. You could use the rear "iSight" camera to take a high-res selfie, but framing your mug properly and hitting the shutter is difficult, takes many failed attempts, and usually results in a lackluster photo.

The new iPhone 6S and 6S Plus models have a really cool feature called 3D Touch that lets you perform app-specific Quick Actions from the home screen for apps that support it. The only downside is that this awesome new feature is not available on older iOS devices.

Hello, my web huggers! In today's tutorial we will learn how to use the Google Hacking Database (GHDB) developed by Exploit Database, to find vulnerable web servers and "juicy" information.

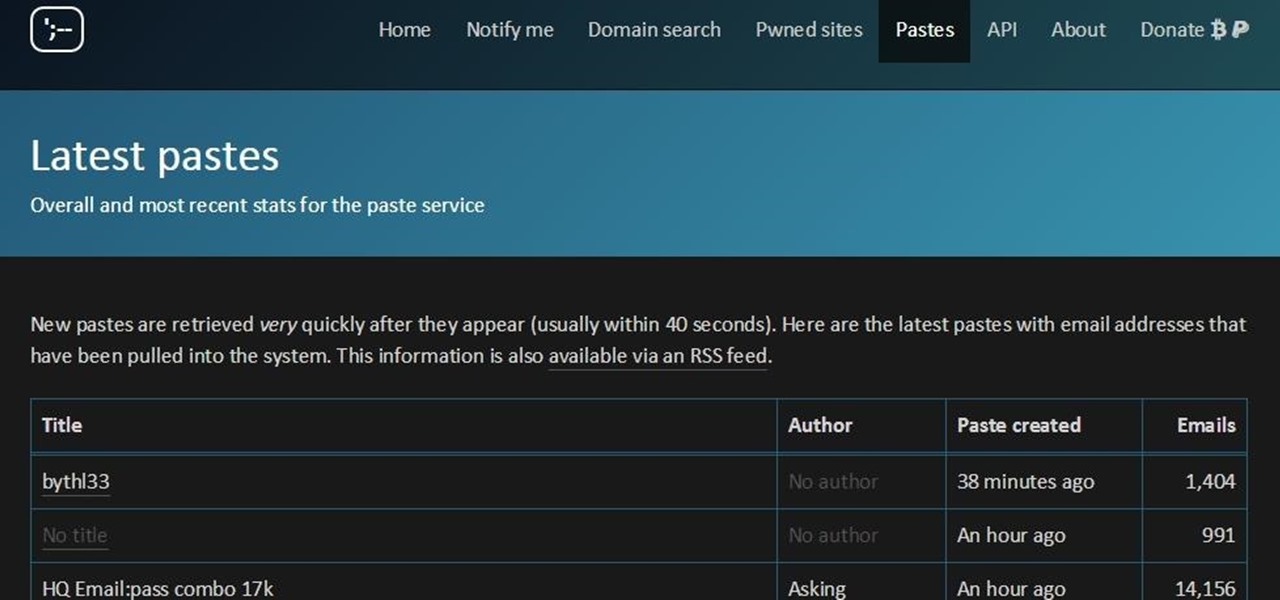
You must have read news about hackers dumping the data online, recent one was Ashely Madison. It's only the big companies' data, which gets noticed once it is out. There are many other small leaks which don't even get a mention. So this article is the first one of my series which will help you to find hacked accounts. Some of you must already know about this, but this post is intended for the new learners. This also serves as an example of my learning how a good service can be used in other w...

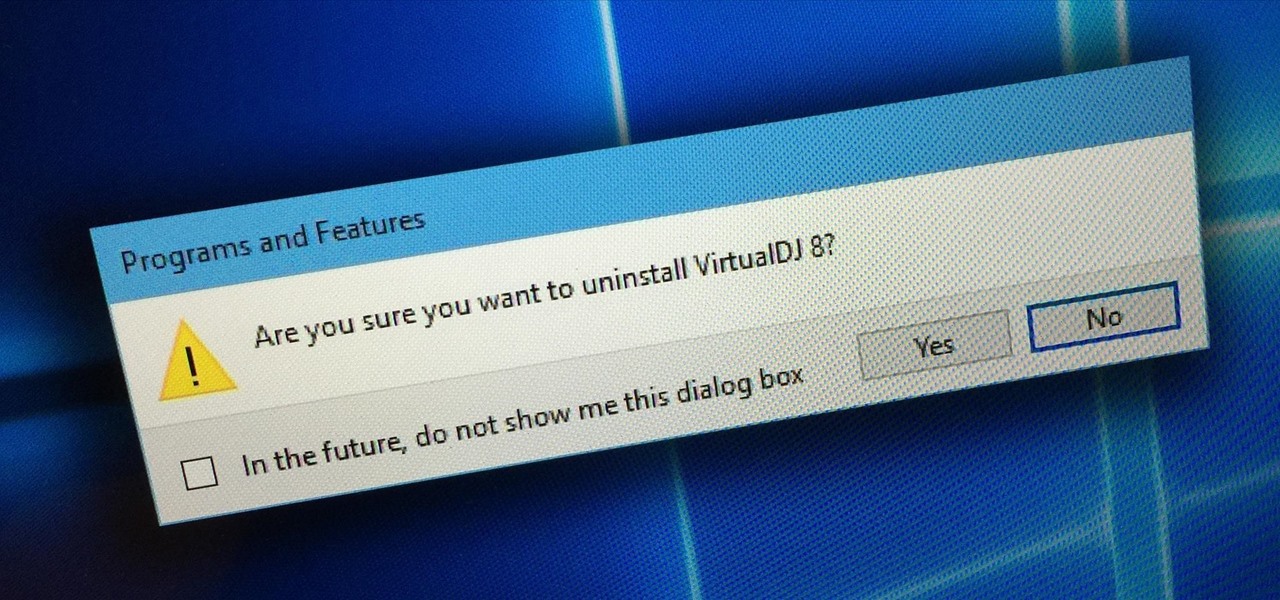
Uninstalling programs in Windows is not the nicest procedure. Some programs bundle a nice uninstaller with them which helps to ease the process. Other programs, mainly those that utilize the Windows Installer technology, begin the uninstall process right away. This can potentially be problematic for users who are trigger-happy with the mouse.

When you swipe from page to page on your home screen, the contents on your screen change, but the wallpaper always remains the same. And while Android does include plenty of ways to customize your device, setting a unique wallpaper for each home screen page isn't one of them.

You're smashing your keyboard to increase your screen brightness, yet it won't go any higher, but you know you've been able to set it higher before. Angered by this, you get up and move your laptop, only to suddenly notice that the display does in fact get a lot brighter.

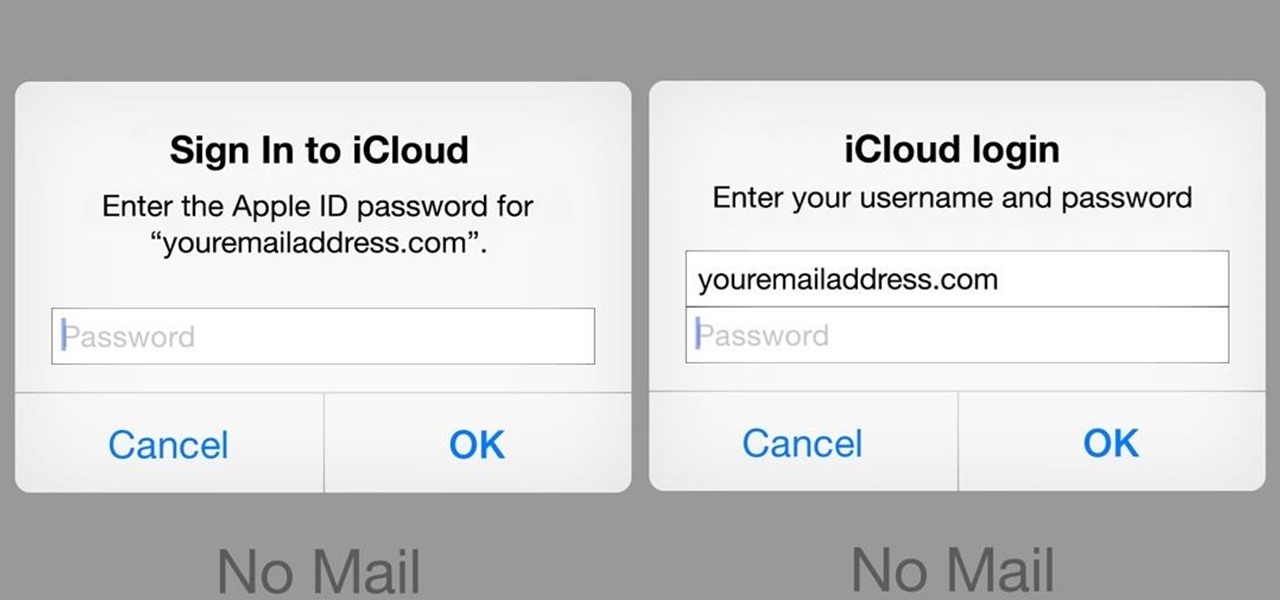
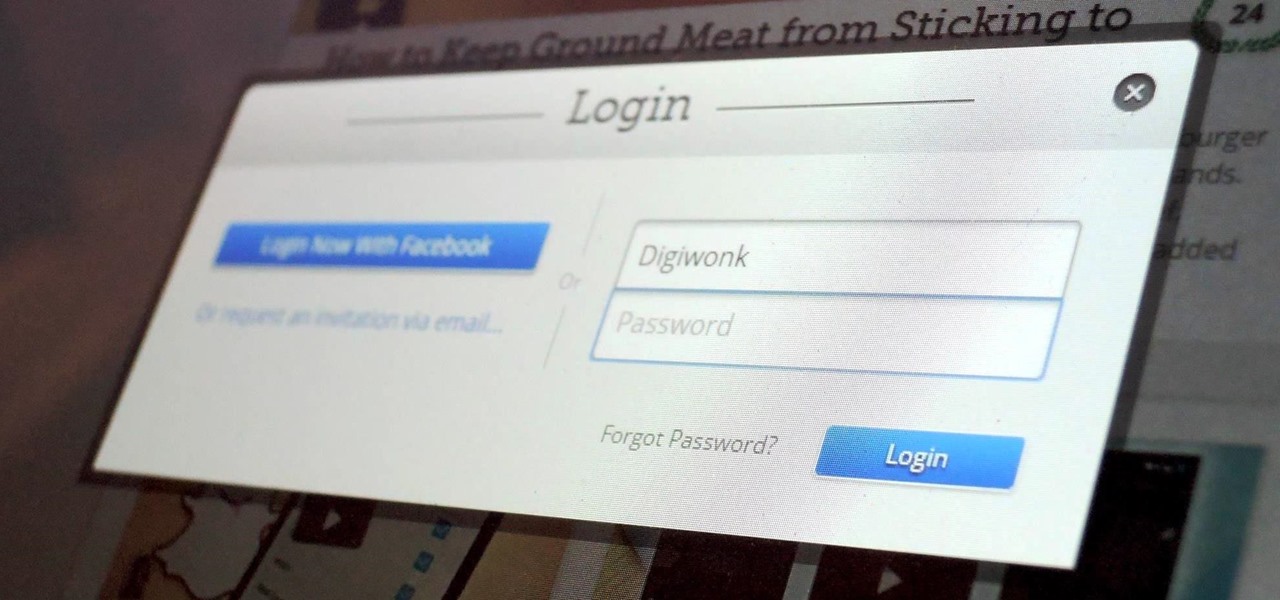
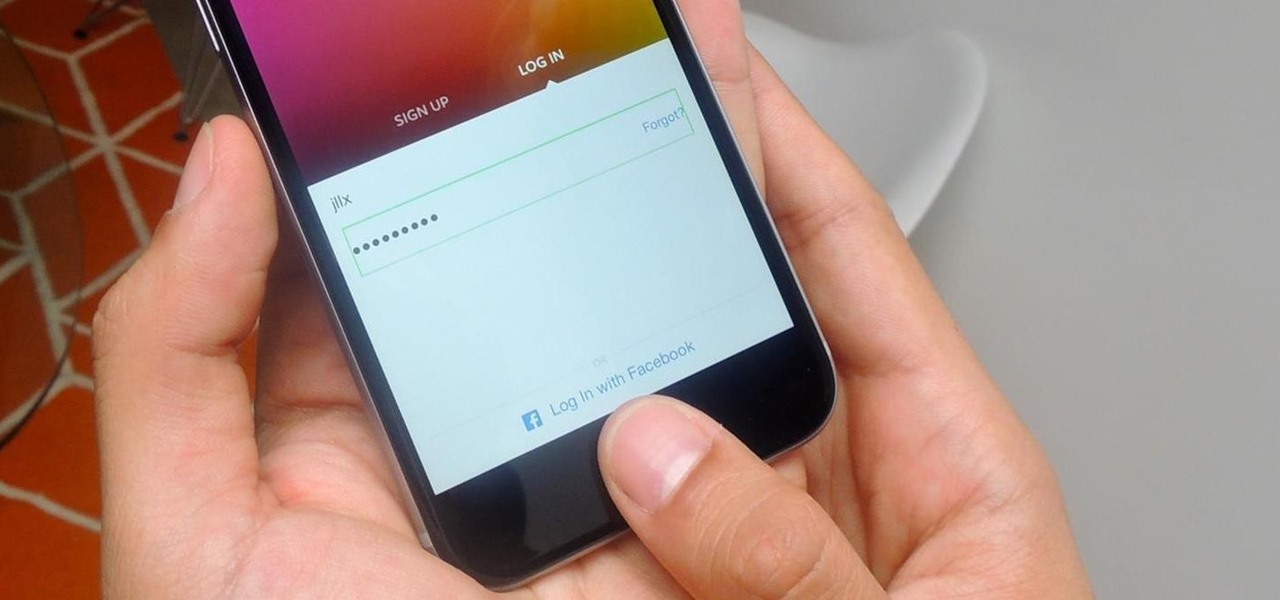
A recently discovered bug in iOS 8's Mail app by Jan Soucek can allow the maliciously-minded to quite easily phish your iCloud password without you ever thinking something has gone awry. Using a bug that allows remote HTML content to be loaded in place of the original email content, unsuspecting victims would be prompted for iCloud credentials in a popup that resembles the native one found on iOS.

Since the days of Android Jelly Bean, Samsung has implemented an energy preservation feature known as dynamic voltage and frequency scaling, or DVFS for short. What this essentially does is limit or adjust the frequency of the microprocessor to conserve power and prevent excessive heat from being generated.

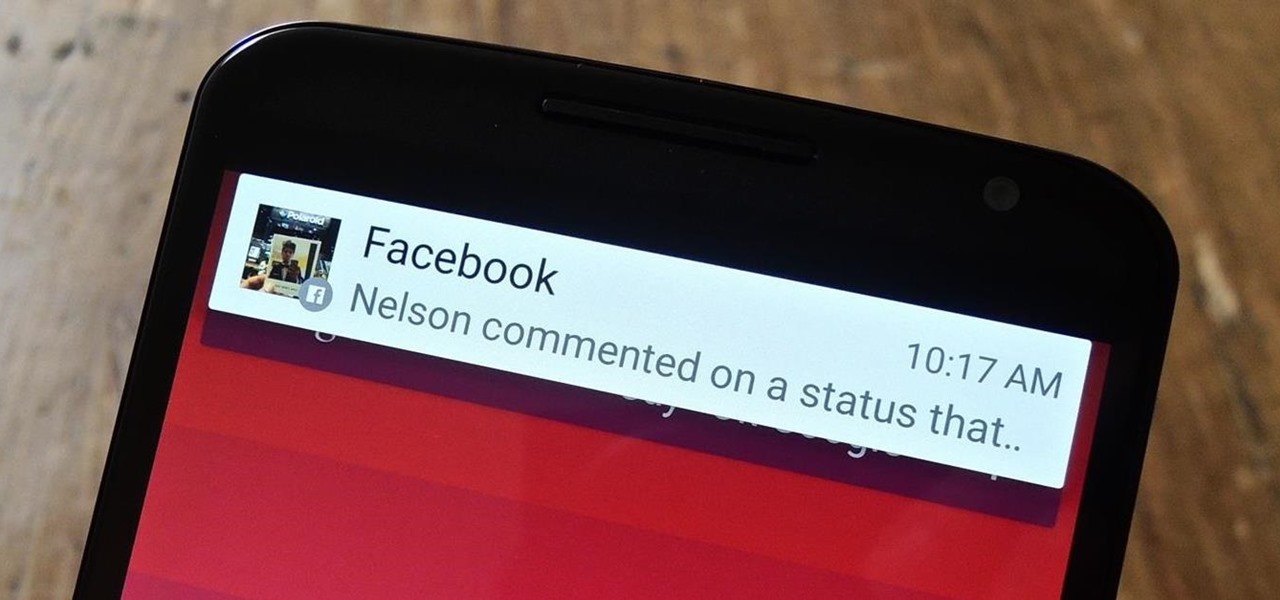
Android Lollipop, introduced an array of new features and aesthetics that pleased many loyal users. One of those additions being the new heads-up notifications. Taking subtle inspiration from iOS, these notifications are visually appealing and can be easily dismissed or expanded, but they do require that you take an action before they go away immediately. Of course, you can always wait 10 seconds for them to disappear, but that can be really annoying if you're in the middle of a game or editi...

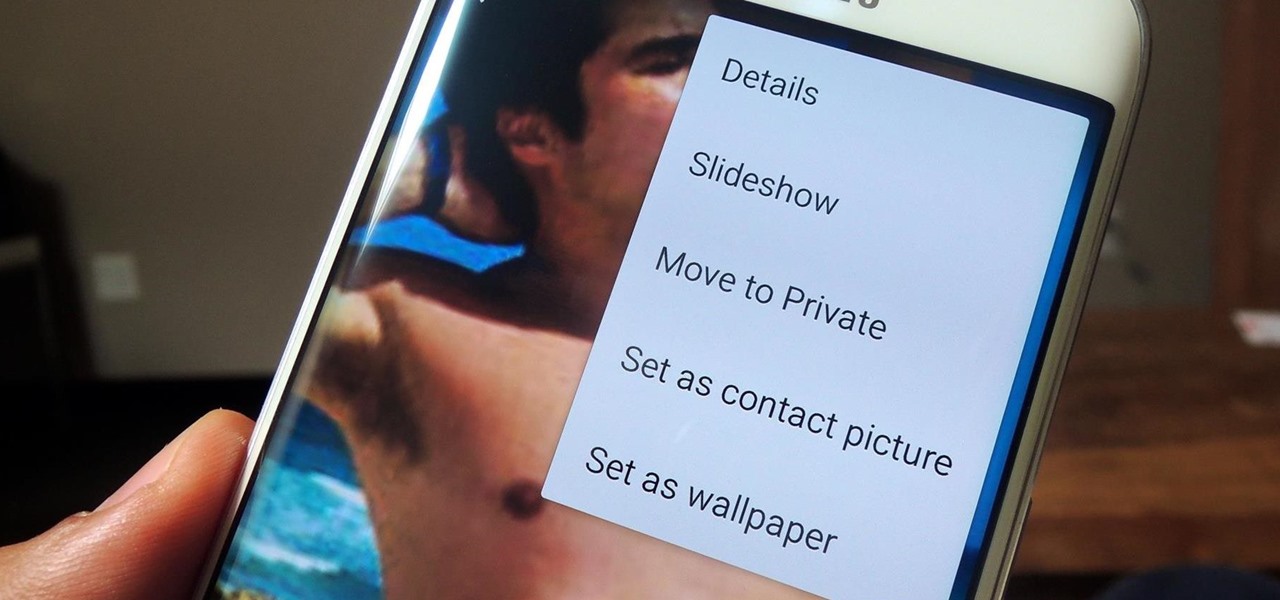
If you have a smartphone, chances are you have something on it you don't want others seeing. Whether it be photos, videos, or documents, some things are best left private. Not everyone is a saint, after all.

Accessing and getting in touch with your favorite contacts has never been easier thanks to the "Friends" feature on the Apple Watch. However, this only applies to users who are running watchOS 2.2.2 and lower. When Apple issued watchOS 3, the "Friends" option was completely removed. So if you're running watchOS 3 or higher, you won't be able to follow these instructions.

In the shadow of Facebook's announcement for third-party app development on Messenger, the company has announced the release of a whole new application called Riff, a creative tool for making videos with friends.

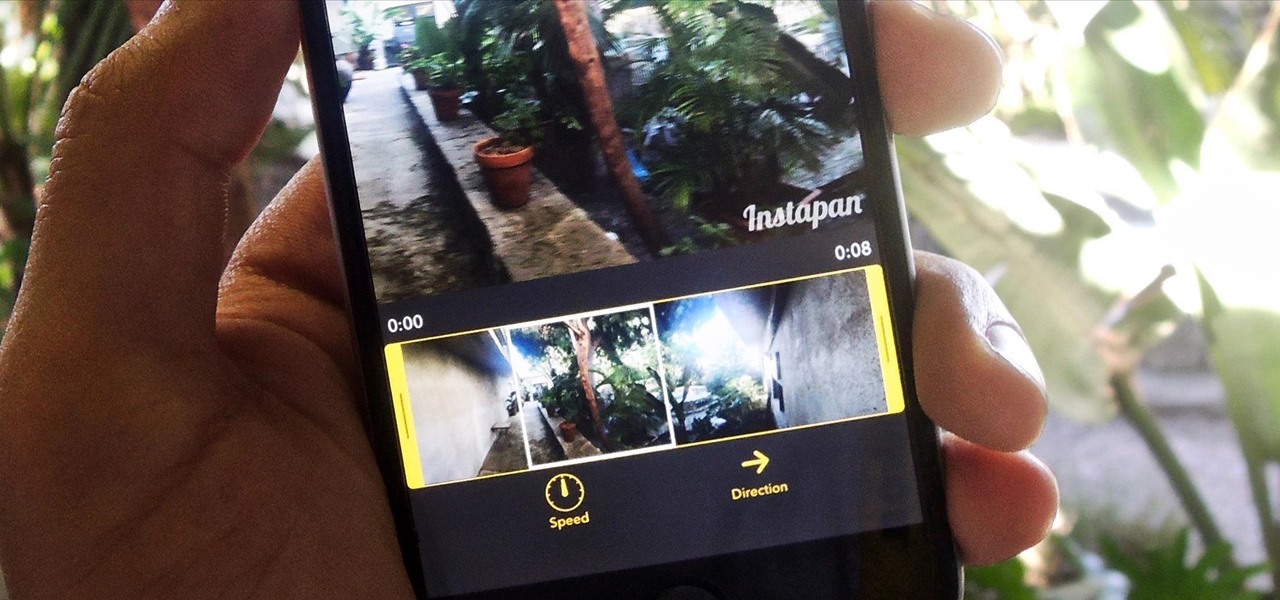
Using your iPhone camera's panorama feature is great way to capture wide-angle views of scenery, such as sweeping cityscapes, broad landscapes, and seemingly never-ending skies, as well as that awesome party or get-together you just threw.

Doxing is the act of finding one's personal information through research and discovery, with little to no information to start with. You may have seen doxing in the news, for instance when not so long ago, hacker team Anonymous doxed and reported thousands of twitter accounts related to ISIS. Doxing can be useful for finding the address of a coworker, or simply investigating people on the internet. The tutorial I will provide to you now will teach you the basics of doxing and how you can prot...

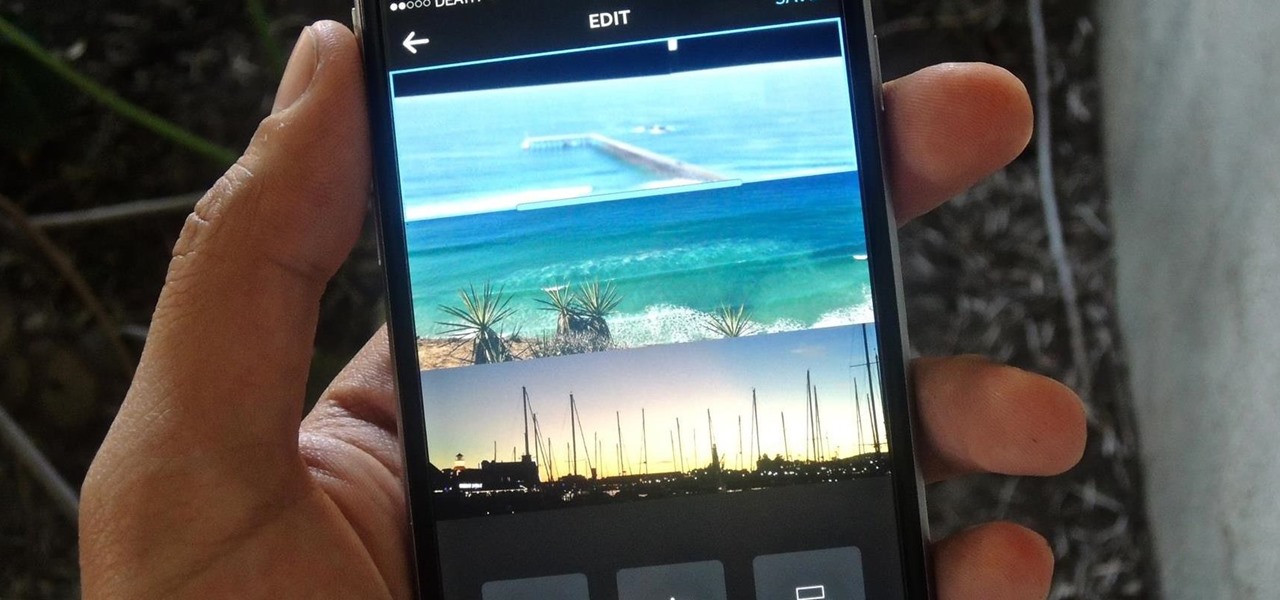
If you're one of the many that likes to upload collages to Instagram, the Facebook company has a new tool for you. Instagram released a brand new app in March called Layout to help facilitate the process of creating photo layouts to post onto social media or just share with friends.

The 13-megapixel camera on the OnePlus One is capable of taking some pretty impressive shots, but the stock CameraNext app doesn't do the hardware justice. When compared to the camera app that ships on the ColorOS version of the One, you can immediately see an increase in clarity and low light performance.

After I traded in my Samsung Galaxy S5 for an iPhone 5S, the one feature I truly missed was the Smart Remote app. My television remote was broken and the S5 saved me from, you know, actually having to get up and change the channel.

Before phones became mobile-gaming, music-playing, app-downloading devices, they were used simply to make convenient, cordless phone calls. There's so much on phones these days that a passcode is needed to keep everything secure, and making calls is now more complicated.

Whether you're a secret spy or just a regular person with a few secrets, you may want to keep certain information on your smartphone private, and it's totally possible on Android to do so.

My college days are long behind me, and while I don't necessary miss them, I am jealous of all the countless resources available to students these days. Apps like PhotoMath are something I wish I had access to in my student days, making assignments less strenuous and easier to complete.

A group ironically called the "Guardians of Peace" hacked into Sony Pictures' computer systems and released a mountain of internal information such as medical records, leaked scripts, work complaints, and even celebrity aliases.

There were over 1.2 million changes made to Android when the OS got updated from KitKat to Lollipop, but a minor front-facing modification has many users in an uproar.

Apple introduced Touch ID on the iPhone 5S back in 2013, which let you unlock the device with your fingerprint. While it was an impressive feature, it could only do that one thing—unlock the device.

If you've ever tried to record a Snapchat video of a song playing in your car, you know that it's impossible to do if the song is playing on the same device that you're Snapchatting with.