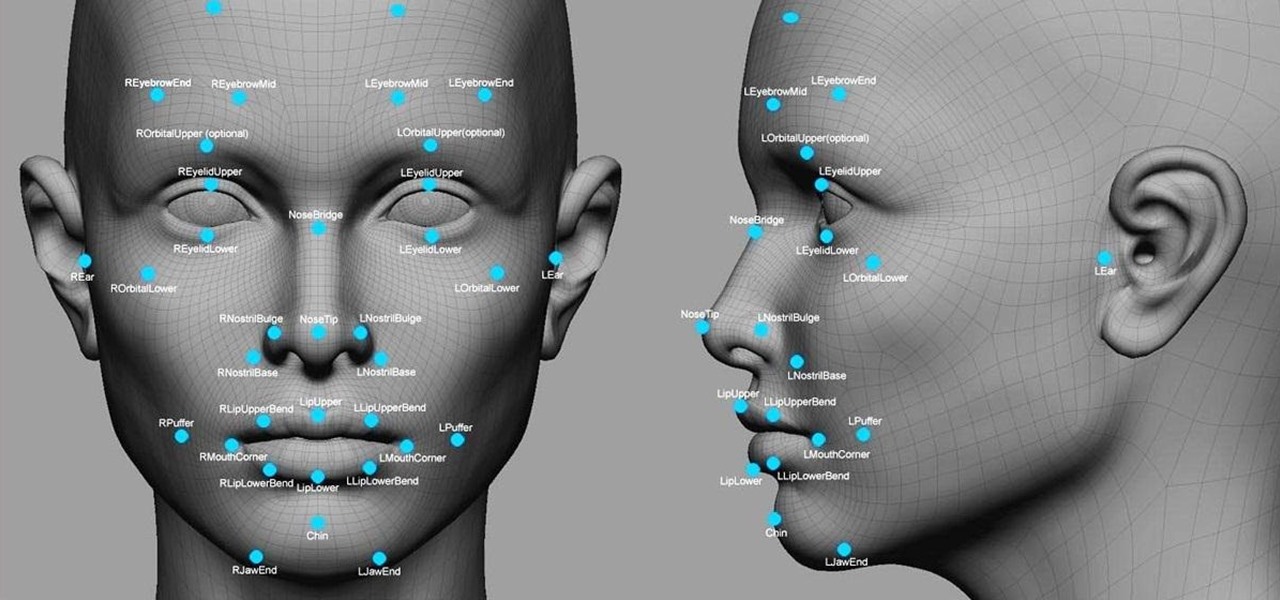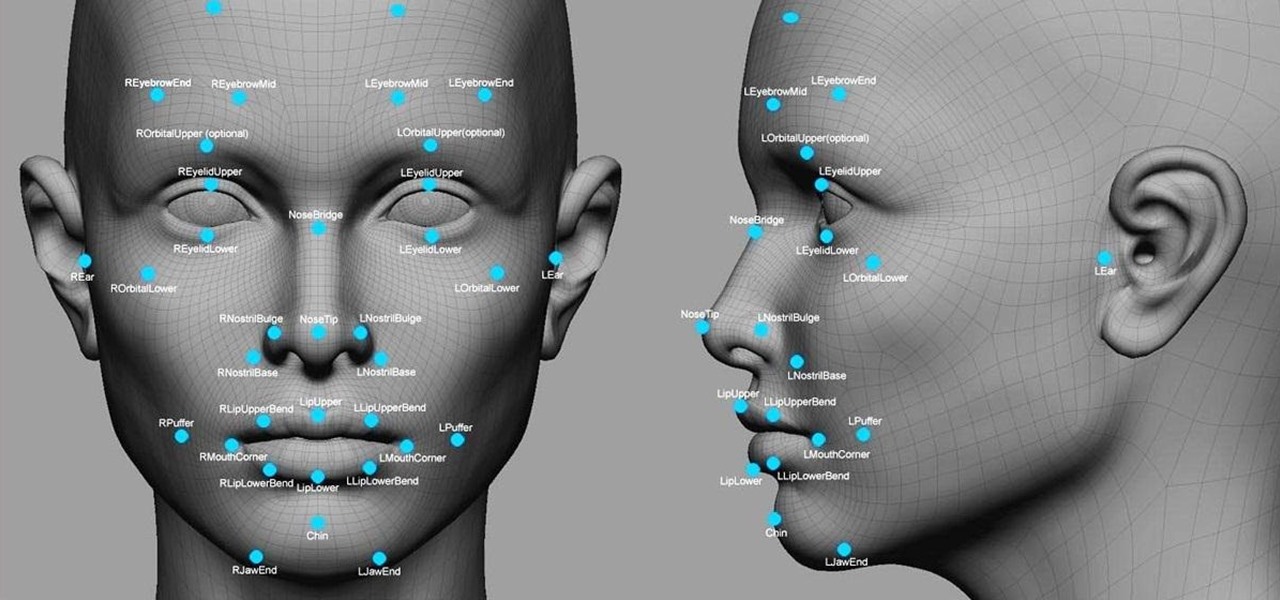
Facial recognition software is being more widely used with every passing day. Your local law enforcement is probably already using it, and it will be even easier for them now that the FBI handed out its own facial recognition software to state authorities. Even the fine folks at Facebook are using this technology. Obviously, this brings up some pretty serious privacy concerns amongst most people, because honestly, who wants to be tracked? Right now, there's not a lot we can do about it being ...

I should start off by saying that this technique is of no real practical value, because this process is far more time-consuming than simply just manually trimming trees to meet your specifications. That said, it's an awful lot of fun to play with!
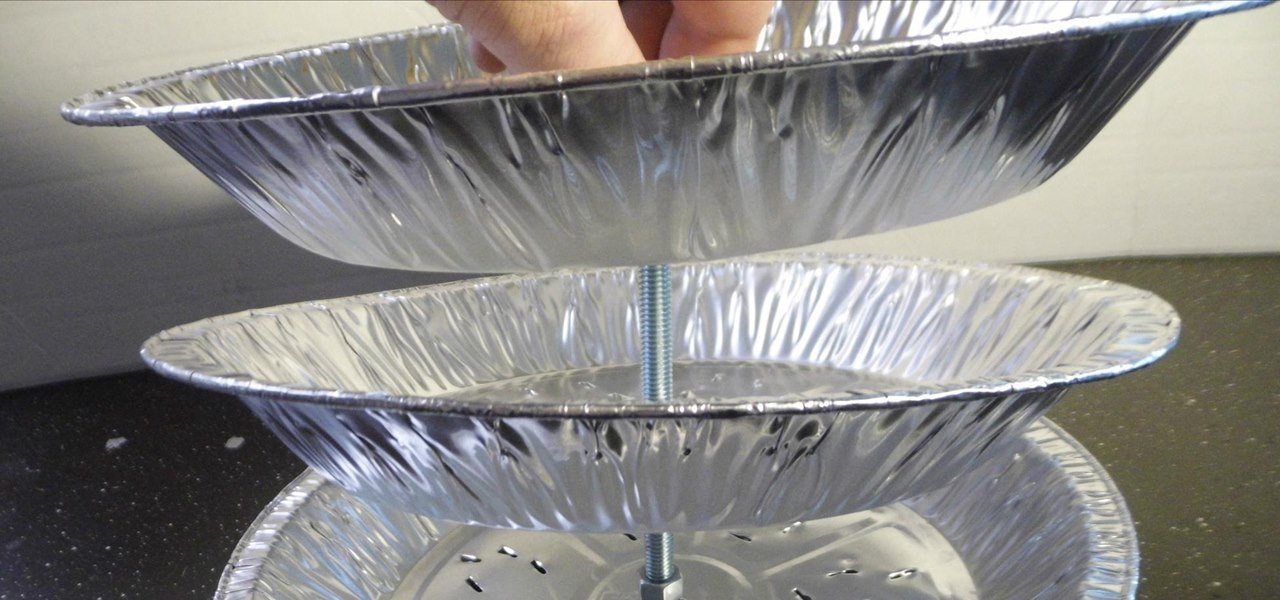
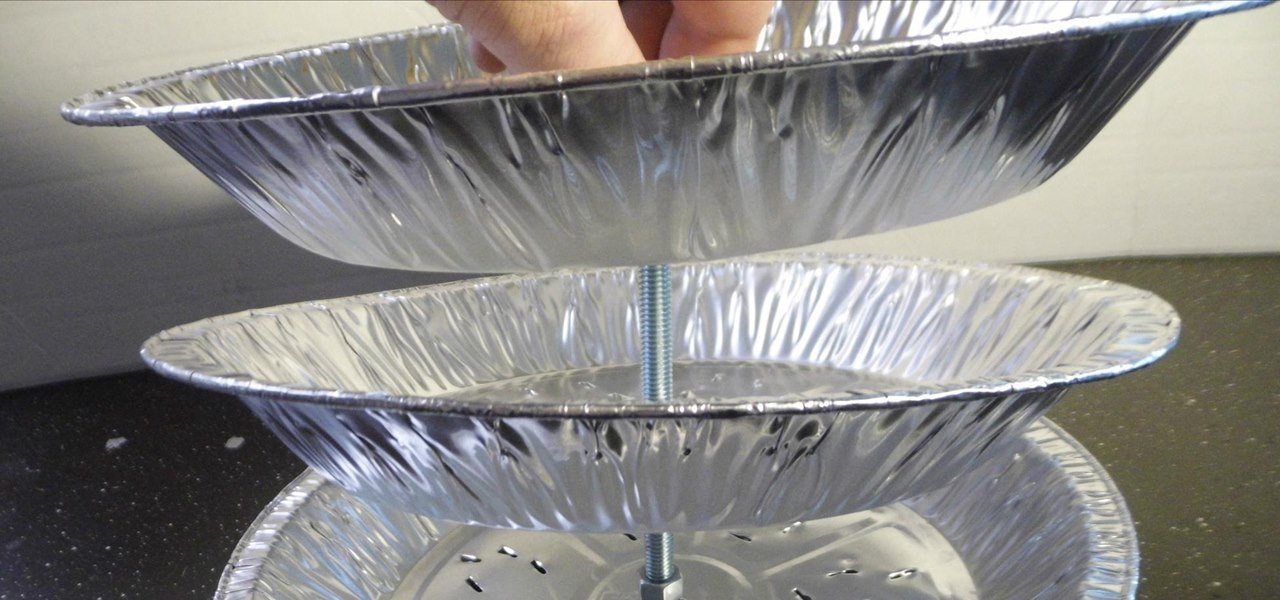
Steaming food has a lot of advantages over other cooking methods. The gentle heat of steam allows for meats, such as chicken wings, to become more moist after cooking.

In this Disaster Preparation video tutorial you will learn how to make a candy stripe bar. The candy stripe bar is a slick way to create a strap of slanted lines. One of the many tying techniques used to create friendship bracelets, the bar can be modified to create stripes meeting at an angle. The line used in the video is a 450 test, 1/8” nylon parachute cord. To attach the cords to the ring, hang the ring on a hook, take two different colored cords and tie the cow hitch. For this, pass a...

Just like any meal choice you can make more or less healthy options when eating sushi. Some ingredients are particularly calorie packed. If you’re watching your weight know where the hidden calories are and if your really conscientious you can try sashimi.

It’s a game, it involves numbers, it’s fun, it’s KenKen! Understanding the goals and rules of this fun, numbers puzzle will give you the skills you need to win. Have fun working your brain and passing the time with KenKen.

In this video, we learn how to use the Warcraft III version switcher. First, go to Garena Forum and download the version switcher through the site. Next, place your Warcraft folder into the new software you just downloaded so it can find the file when it starts to load. Now, open up the link that is on your desktop, and the game should come up. This is a very easy way to use the version switcher and play the game you want to! Enjoy playing this and pass on this tip to others for future use.

Kev Porter shows how to purify water using tablets. Kev advises that the first thing to do is read the instructions on the back. He uses portable water tablets. You add two tablets to a quart or liter of water. Place the cap loosely on the water bottle, wait five minutes and shake it. After shaking, you have to wait another three minutes making sure you tighten the cap. Once three minutes pass, add the neutralizing tablets. Place cap back on the water bottle tightly and shake it. This takes t...

In this video tutorial, viewers learn how to rotate the hips to cure a push shot in golf. The mistake often happens at the start of the down swing. People tend to slide the hips too far out and pass the point of the target. This blocks your swing out from going to the target and makes the club swing out to the right, causing a push shot. The proper way to fix this problem is to shift the left leg and rotate the hip. This video will benefit those viewers who enjoy playing golf and would like t...

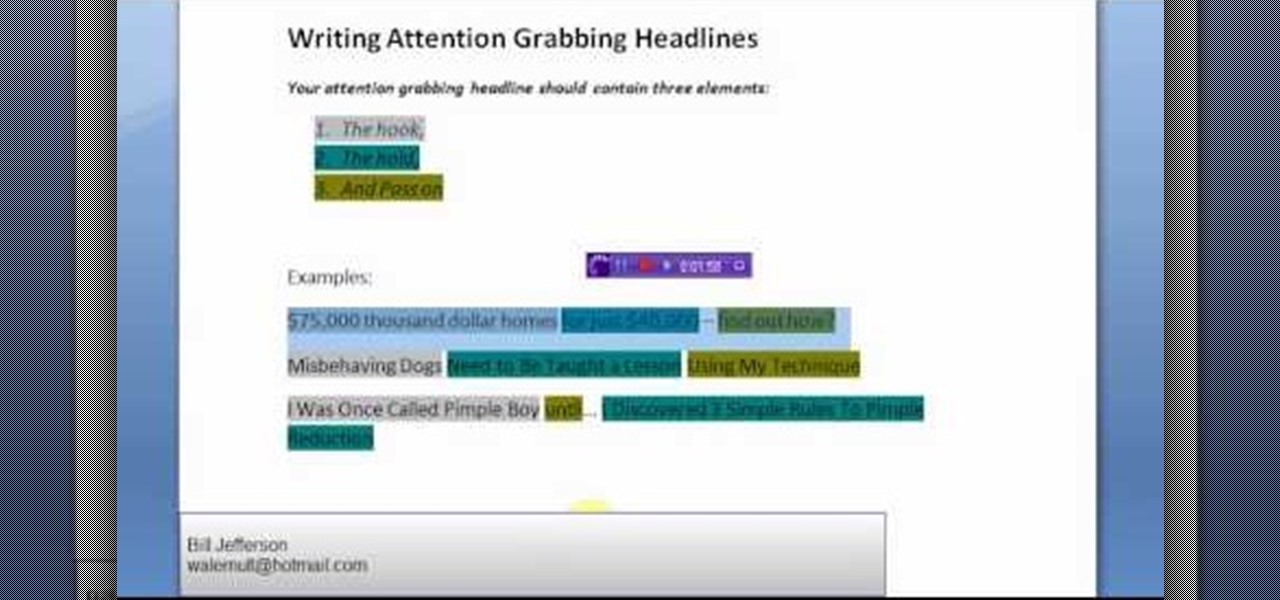
Not selling that much online these days? Maybe it's because your headlines just are reaching out to people the way they should. Good marketing means good writing in the web industry.

There are few projects that are so simple, and so immediately rewarding, as learning to play a favorite song on the guitar. Not only is it a wonderful way to pass the time but, by learning to play your favorite songs and riffs, you'll be better able to articulate (and otherwise translate) your musical ideas into great-sounding songs. In this guitar lesson, you'll learn how to play "All the Small Things" by Blink 182. While this tutorial is geared towards intermediate players, guitarists of al...

There are few projects that are so simple, and so immediately rewarding, as learning to play a favorite song on the guitar. Not only is it a wonderful way to pass the time but, by learning to play your favorite songs and riffs, you'll be better able to articulate (and otherwise translate) your musical ideas into great-sounding songs. In this guitar lesson, you'll learn how to play "What's My Age Again" by Blink 182. While this tutorial is geared towards intermediate players, guitarists of all...

Learning to play your favorite songs on your guitar is not only a wonderful way of passing the time–and impressing those whom you'd like to impress–, it can do wonders for your technique. In this song tutorial from Siggi Mertens' series of beginning guitar lessons, you'll learn how to play "Song of Joy." While this video tutorial is geared towards beginners, it assumes at least some prior knowledge of guitar playing and its jargon. Take a look to get started playing "Song of Joy"!

This short construction tutorial video shows how to build a small, simple stage from scratch specifically for animating a claymation or stop motion animation project. Construct the ideal world for your claymation characters or stop motion animation armatures and puppets. All you have to do is follow this video then drill holes wherever you want your tie downs to pass through and you're off to the races. Just use the following materials to build your own stage: an armature with foot tie-downs,...

We would never pass up a sweet treat like ice cream or classic American apple pie, but sometimes we get bored of the same old thing all the time, you know? Take your family's taste buds on an exotic vacation tonight for dinner by preparing Indian gajrela, or sweet carrot delight.

This video series shows you how to race on SyKart indoor kart track in Tigard Oregon. The first video takes you on a warmup lap and explains each turn, the second video shows you the proper line to follow, the third video shows you how to go quick and the last video shows you how to pass.

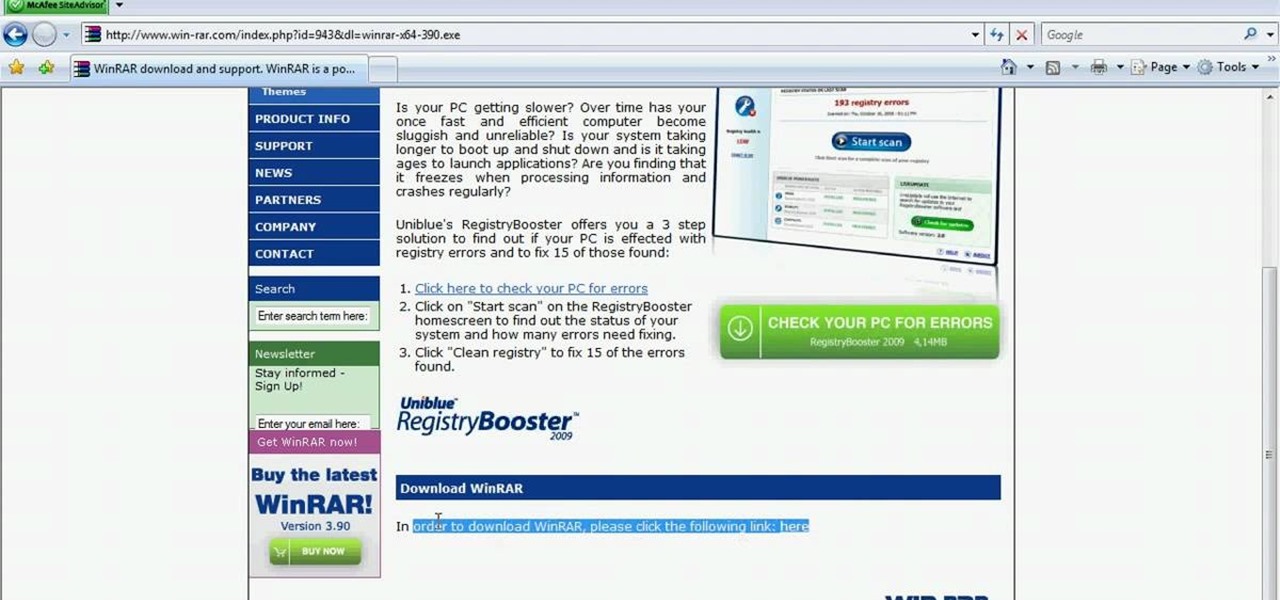
In this video tutorial, viewers learn how to unzip .rar files using Winrar program. Begin by opening your internet browser and download the program from the link in the video description. Wait for the time to pass and click Download. Select 32 bit or 64 bit, depending on your computer. Open the file and install the program by following the instructions. Once it's installed, select the file that you want to unzip. Right-click on the file and select Extract All Files. This video will benefit th...

Access your computer's BIOS settings

When hitting a fade shot in a golf game, it is important to remember this is only for shots that are about five to eight yards. Ten through twenty yards would be a slice. When you're coming to the impact area, the face of the club should be just slightly behind your hands. Fades seem to land more softly on the fareway and has more carry to it than the hook. The club should be slightly open when it comes in contact with the ball. If the club passes your hands on impact, the ball is going to drop.

It is a video about how to apply three eye shadows. For that start with a small eye shadow brush. Then apply the shadow to the inner part of the eye. Eye shadow should stop where your pupil starts. After that take a bigger eye shadow brush and apply the second color, which should go passed your iris of the eye. The second color is applied over the eyelid. Now take an angled eye shadow brush. The angle will help to apply the color in to the crease. Third color is applied over the left part of ...

Although mainly demonstrational, this video shows you how to play the "Fingerbuster" on guitar. This video is intended for advanced players who learn easily by watching or listening. Read the useful tips posted below to aid your guitar learning:

Playing backline in rugby is an important position on the field. Learn how to play rugby, including rules and skills, in this video rugby lesson.

Learn how to design a defense to stop dribbling penetration or passes to the middle. If you're a basketball coach, you'll definitely want to utilize this two-three zone defense.

In general, hacking and information security is not just one discipline, but a number of them, and today we will look into some of the networking concepts.

Why pay for a movie when you can get it for free? Thanks to Movies Anywhere, you can claim and download a video for your digital film collection right now at no cost. And getting your freebie flick couldn't be any easier.

With the Wigle WiFi app running on an Android phone, a hacker can discover and map any nearby network, including those created by printers and other insecure devices. The default tools to analyze the resulting data can fall short of what a hacker needs, but by importing wardriving data into Jupyter Notebook, we can map all Wi-Fi devices we encounter and slice through the data with ease.

TWRP won't be ready for the Pixel 4 and 4 XL until months after release. But since you can already root with Magisk and tinker with the OS, you might find yourself in a situation where your phone won't boot, yet you don't have a custom recovery installed to fix it. Luckily, there's still a way around this.

QR codes are everywhere, from product packaging to airline boarding passes, making the scanners that read them a juicy target for hackers. Thanks to flaws in many of these proprietary scanning devices, it's possible to exploit common vulnerabilities using exploits packed into custom QR codes.

The year in augmented reality 2019 started with the kind of doom and gloom that usually signals the end of something. Driven in large part by the story we broke in January about the fall of Meta, along with similar flameouts by ODG and Blippar, the virtual shrapnel of AR ventures that took a wrong turn has already marred the landscape of 2019.

Microsoft Office files can be password-protected in order to prevent tampering and ensure data integrity. But password-protected documents from earlier versions of Office are susceptible to having their hashes extracted with a simple program called office2john. Those extracted hashes can then be cracked using John the Ripper and Hashcat.

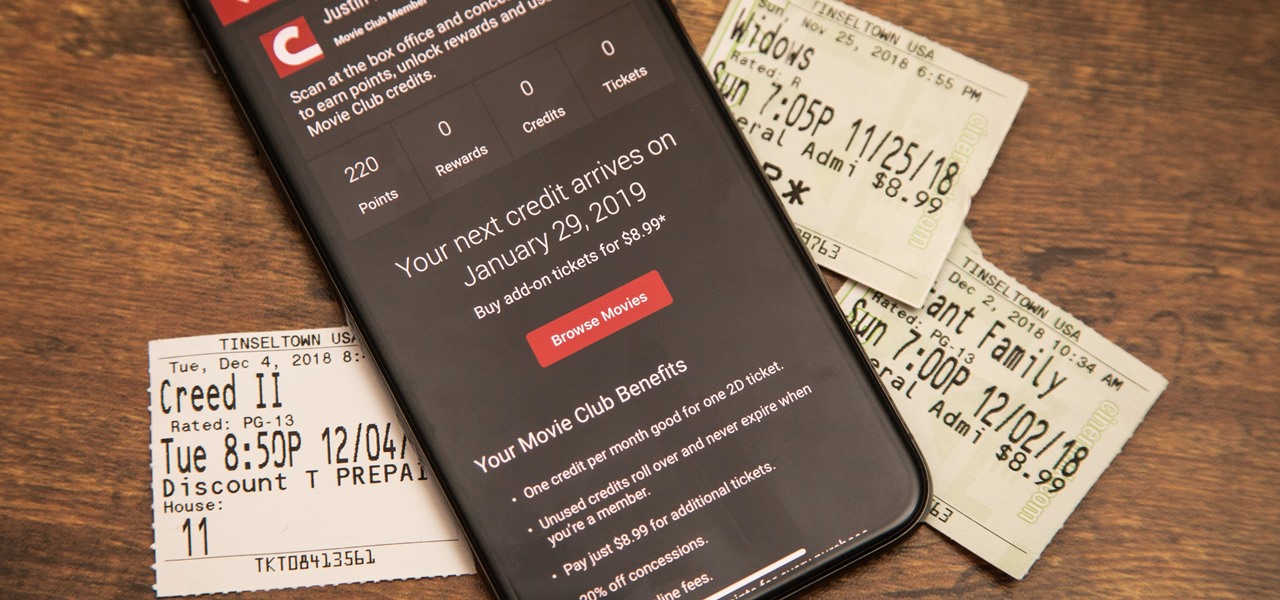
Cinemark may not be as big as AMC Theatres, but it also has a subscription if you want cheaper access to movie tickets. There aren't as many theaters, but if there's no AMC around you, there will likely be a Cinemark to save the day. But is the price of its Movie Club plan worth it?

The Pixel 3 XL versus Galaxy Note 9. Stock Android versus Samsung Experience. When I began this comparison, I thought the Pixel 3 XL would be unfairly outmatched. But after looking at the specs side-by-side, you'll see a different picture. This year, Google delivered a worthy alternative to Samsung's best offering.

With just one line of Ruby code embedded into a fake PDF, a hacker can remotely control any Mac computer from anywhere in the world. Creating the command is the easy part, but getting the target to open the code is where a hacker will need to get creative.

After gaining access to a root account, the next order of business is using that power to do something more significant. If the user passwords on the system can be obtained and cracked, an attacker can use them to pivot to other machines if the login is the same across systems. There are two tried-and-true password cracking tools that can accomplish this: John the Ripper and Hashcat.

Since early March, iOS users have been able to enjoy the most popular video game sweeping the rounds. Android users have been left envious as they wait for a "few months," the only vague release date given by Epic Games. In the meantime, there are a few ways we can still satisfy our urge to play.

One of the most critical bugs to come out in the last five years was Shellshock, a vulnerability which allows attackers to execute arbitrary code via the Unix Bash shell remotely. This vulnerability has been around for a while now, but due to the ubiquity of Unix machines connected to the web, Shellshock is still a very real threat, especially for unpatched systems.

As the official release of iOS 12 nears closer each day, Apple continues to update its betas. The company released the fourth beta of the upcoming software to developers Tuesday, July 17, exactly two weeks after the release of the third developer beta which came out just a few days before the second public beta.

Database technology has vastly improved the way we handle vast amounts of data, and almost every modern application utilizes it in one way or another. But the widespread use of databases naturally invites a slew of vulnerabilities and attacks to occur. SQL injection has been around for awhile, and as such, there are many defense methods in place to safeguard against these types of attacks.

The one thing that separates a script kiddy from a legitimate hacker or security professional is the ability to program. Script kiddies use other people's tools, while hackers and security pros write their own tools. To that end, we're going to see how a stack overflow vulnerability allows us to flood a variable with enough input to overwrite the instruction pointer with our own commands.

Being able to write your own hacking tools is what separates the script kiddies from the legendary hackers. While this can take many forms, one of the most coveted skills in hacking is the ability to dig through the binary files of a program and identify vulnerabilities at the lowest level. This is referred to as binary exploitation, and today we're going to check out a tool known as Protostar.