By now, there's no way you haven't stumbled upon a TikTok video, whether it was on Facebook, Instagram, Twitter, or YouTube. Just watching these addictive short-form videos is enough to make you want to join up and make your own, and when you do, we've got some tips that will help get your TikTok account in order.

The Raspberry Pi Zero W and Pi 3 Model B+ include integrated Wi-Fi, Bluetooth Low Energy, and more than enough power to run Kali Linux. They sound like perfect all-in-one penetration testing devices, but the lack of support for monitor mode and packet injection usually meant buying a supported Wi-Fi adapter. Now, it's possible to use monitor mode on the built-in Wi-Fi chip with Nexmon.

Cracking the password for WPA2 networks has been roughly the same for many years, but a newer attack requires less interaction and info than previous techniques and has the added advantage of being able to target access points with no one connected. The latest attack against the PMKID uses Hashcat to crack WPA passwords and allows hackers to find networks with weak passwords more easily.

Most companies have services like employee login portals, internal-only subdomains, and test servers they would prefer to keep private. Red teams and white hat hackers can find these obscure and often vulnerable services using a tool designed to help protect users from fraudulent certificates.

File inclusion can allow an attacker to view files on a remote host they shouldn't be able to see, and it can even allow the attacker to run code on a target.

Microsoft recently released "Seeing AI," an app aimed to help the blind understand their surroundings. As Microsoft puts it, "the app narrates the world around you by turning the visual world into an audible experience."

With some of the groundwork out of the way in getting a Mac set up for hacking, it's time to start looking at toolboxes. Our first toolbox is Git, which will be used throughout future tutorials.

Now that Google has announced its new Pixel smartphones, folks who rushed to buy an iPhone 7 might be experiencing a bit of buyer's remorse. The new Pixel and Pixel XL are packed to the brim with cutting-edge features and top-notch hardware, and Google seems to be taking direct aim at the iPhone 7 with its Pixel marketing (and their groan-worthy jokes during the keynote).

Greetings my fellow aspiring hackers, It's still Christmas and we have a lot of things and hugs and kisses and ... to share ( you know the things that you do ). I have never done this before but I just felt to encourage you on the quest for knowledge, security and defence, skills and a whole lot more that comes out as a result of pursuing hacking. What we mean by hacking on this forum is White hat Hacking and OTW has great articles on it and I don't need to explain myself on that one.

I am an English major physically allergic to all algebraic formulas, so you're unlikely to get any help from me when it comes to solving any expressions. But in the glorious technological age we live in, there are plenty of apps that actually make math and problem solving fun, even a little bit addictive.

About ten years ago, Western research figured out that green tea was a nutritional powerhouse. After all, in Asian countries where green tea is consumed throughout the day, cancer rates tend to be much lower, although there are probably other factors contributing to that fact, like less processed food and red meat in the standard Asian diet.

This two-part series (second part here) will teach you literally everything you need to know in order to make pretty much anything out of leather.

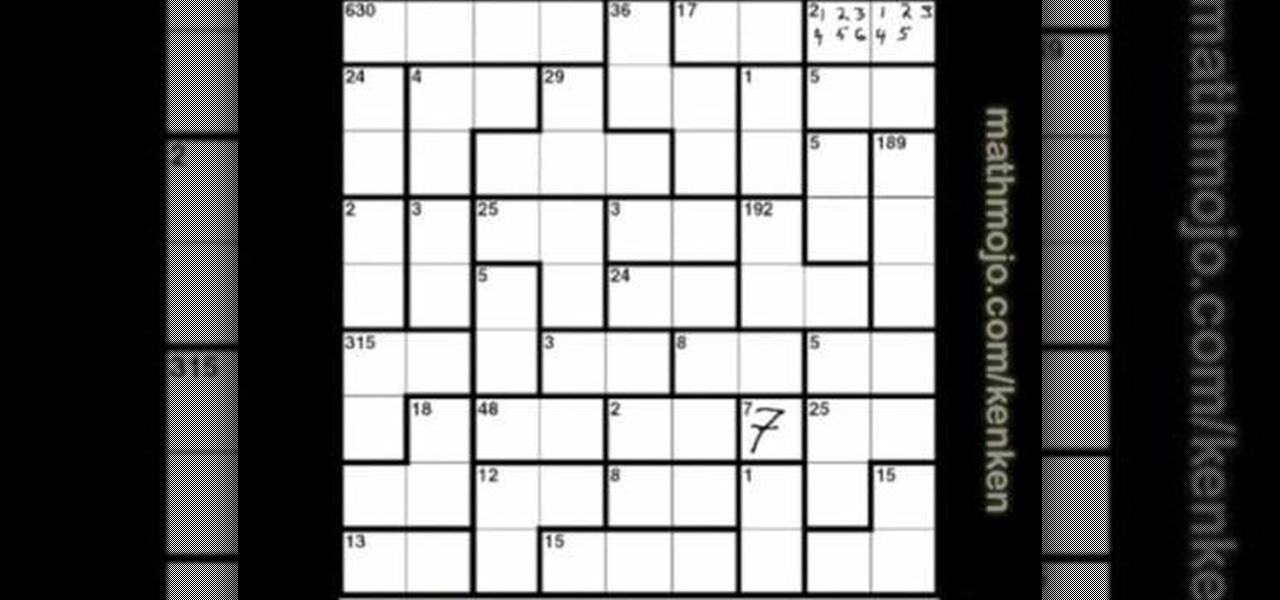
Bored with crosswords and sudoku puzzles? Well, try your hands at a new type of puzzle: KenKen logic puzzles.

This is easier than the divisibility by 3 rule, but still necessary for those starting out with simple division in math class. You can use the divisibility rule to see if a number is divisible by 2, 5 or 10. This video will show you how simple it is!

If you're looking for an easy way to determine if a number is divisible by 3, then look no further than the divisibility rule. It's a shorthand way to tell if any given number can be divided by 3, without actually performing the division. Take the number in question, and if the sum off all the digits is divisible by 3, then the original number will be, too. There are four examples in this math video.

In this tutorial, we learn how to get good grades in high school. First, make sure you get a good nights sleep and have a good breakfast. Also, make sure you are sitting next to people you don't want to chat with. Also, make sure you do your homework and have it ready before you go into class. Don't wait until last minute to study for your tests and always have a good attitude about school. Make sure you sit at the front of the class, and you will get better grades and listen to the teacher m...

In order to set up your email in Outlook Express IMAP, you will need open Outlook. In accounts, enter your user name in the box above: "for example John Smith". Switch the incoming mail server to IMAP. Fill in your server and outgoing mail SMTP.

Access your computer's BIOS settings

In this video from soxfan647 we learn how to access the system config screen on the iPod Nano. First reset it by holding the center and menu. Now when it resets, hold center and rewind. This is used for testing the LCD. You can click the center button to rotate between different colors of the LCD screen. This will only work on click wheel iPods. You can even use the click wheel to go through different screens in this mode as well. This will look different on different styles of iPods. To get ...

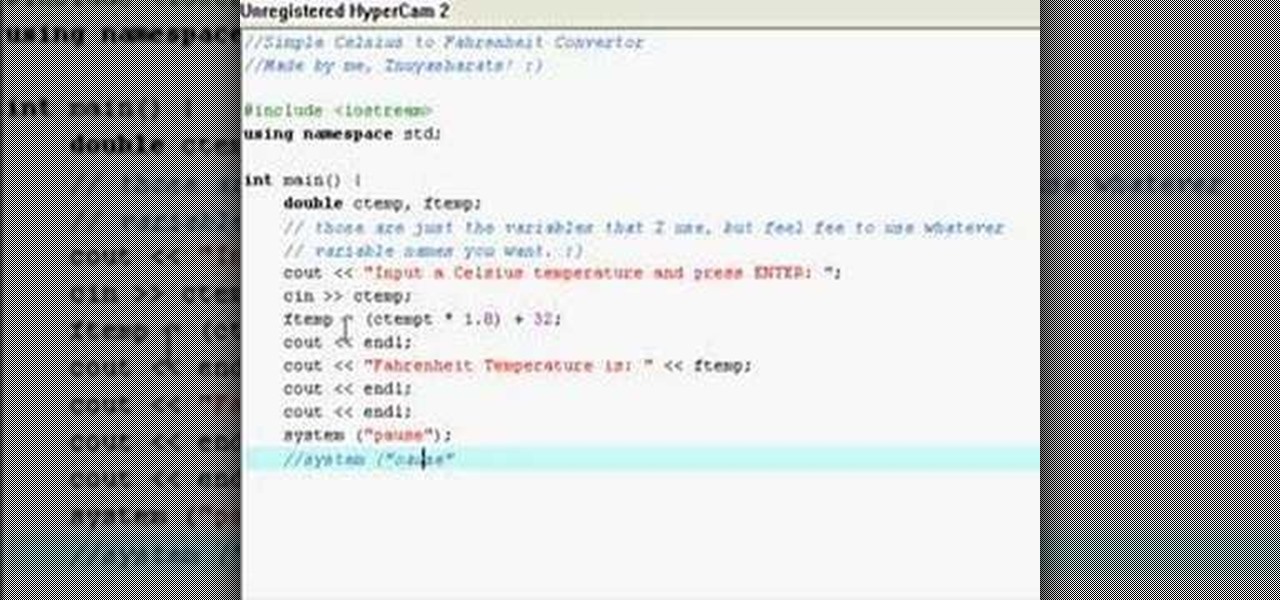
In this video, the instructor shows how to convert Celsius to Fahrenheit using a C++ program. This video shows how to do this by a live example where the instructor writes down the code to do it. First, code the basic structure of a c++ program that contains the include and all other statements. Now accept the value of temperature in Celsius from the standard input. Now multiply that value by 1.8 and add 32 to it to get the value in Fahrenheit. Display the value to the output. Finally, compil...

Here are some simple and easy to follow, step-by-step instructions for installing PSP Infcat and PSP Mugen on your Sony PSP. Make sure you get 1.50 core/php for your PSP version. The video is for Fat and Slim and has not been tested on PSP 3000 & PSP Go, because one does not exist. Leda will also be needed.

Joe Kelley puts his skills to the test and finds building a kite is easy; it's getting it up in the air that is the hard part. Greg Swanson tries to compete with his store-bought dragon, but has no luck either. Watch this video tutorial and learn how to make a kite.

This video tutorial shows how to mix your own clay body. Covered are the basic types of clay, fluxes, and fillers. When testing clay body mixtures, make 1000 gram batches dry, then add water to that. This way a percentage recipe can be taken and just by moving the decimal point can convert it to grams (25% = 25 grams or 250 grams, etc). Here is a clay-body recipe is as follows for those of who might care. Also, much of the mixture of a clay body is designed to match the glazes. It needs to me...

This video shows you how to control your computer from your iPod touch. 1. Go to UVNC. Click on Installation. This will take you to download options. Download the latest stable version. 2. Install Hamachi, which helps you find your computer's IP address. Click on Download Here link, fill in the registration information, and click submit. 3. Install a VNC listener on your iPod so it can connect to your desktop. Jailbreak your iPod, and open the installer. Click All Programs; scroll down until ...

You can make a delicious and sweet fruit spread, known as apple butter, in the comfort of your kitchen. You can have a fruity topping for bread or muffins by cooking down apples with spices and sugar until thick.

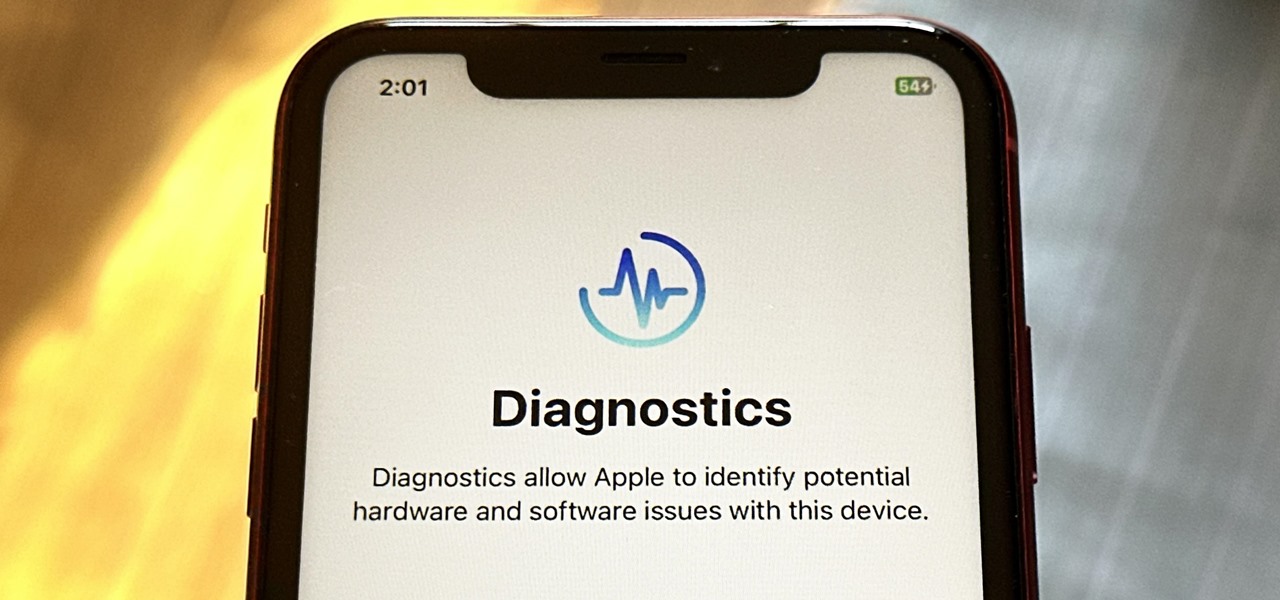
Your iPhone has hidden apps that work behind the scenes to filter SMS messages, trust computers, deal with payments, test ads, and perform other actions. You won't find any of them in your App Library, but there are tricks you can employ to unlock and use some of these secret apps.

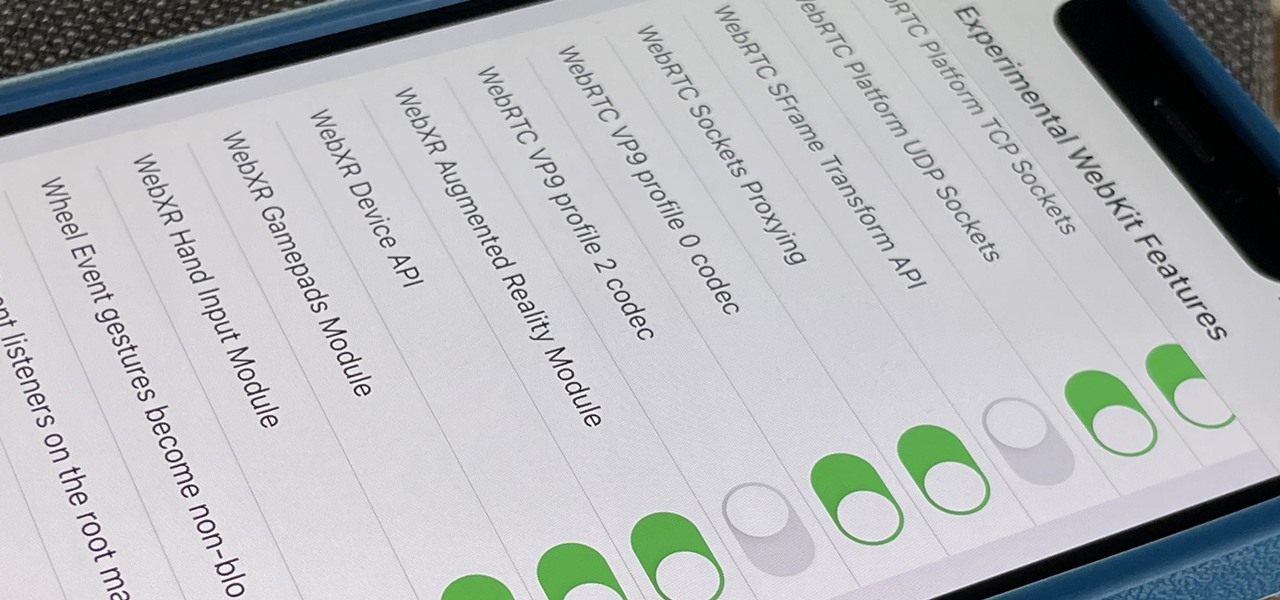
Safari's advanced experimental features give you access to new browser initiatives, upcoming web tools, element changes, behavior adjustments, and other preliminary feature tests in development by Apple. If you use them on your iPhone, you can either improve your Safari experience or wreck it. Resetting the flags provides a fresh start.

Away from the hype around Facebook's smartglasses, the high-end fascination with the Microsoft HoloLens, and the unending rumors about Apple's AR wearable is the small but powerful darling of the enterprise AR world—Vuzix.

It's all fun and games until the technology is actually put into use and you realize augmented reality is now part of Death Star.

After years of testing and modifications, the US Army is moving forward with its customized version of HoloLens 2 from Microsoft.

It is well documented that what you say and do online is tracked. Yes, private organizations do their best to protect your data from hackers, but those protections don't extend to themselves, advertisers, and law enforcement.

Apple just released iOS 13.5 for public beta testers today, Monday, May 18. The GM (golden master) for iOS 13.5 arrives just three hours after Apple released it to iPhone developers, and 12 days after the release of iOS 13.5 dev beta 4.

People use browsers for all types of things, and in general, we trust a lot of personal information to them. That's why browsers are a perfect attack surface for a hacker, because the target may not even know they are infected and feed you all of the information you could want.

No website, service, or platform is immune to being abused or exploited by hackers, and Google Analytics is no exception. To better understand how Google Analytics can help deliver payloads and bypass security protocols, one might want to learn how to use Google Analytics from a user's perspective first.

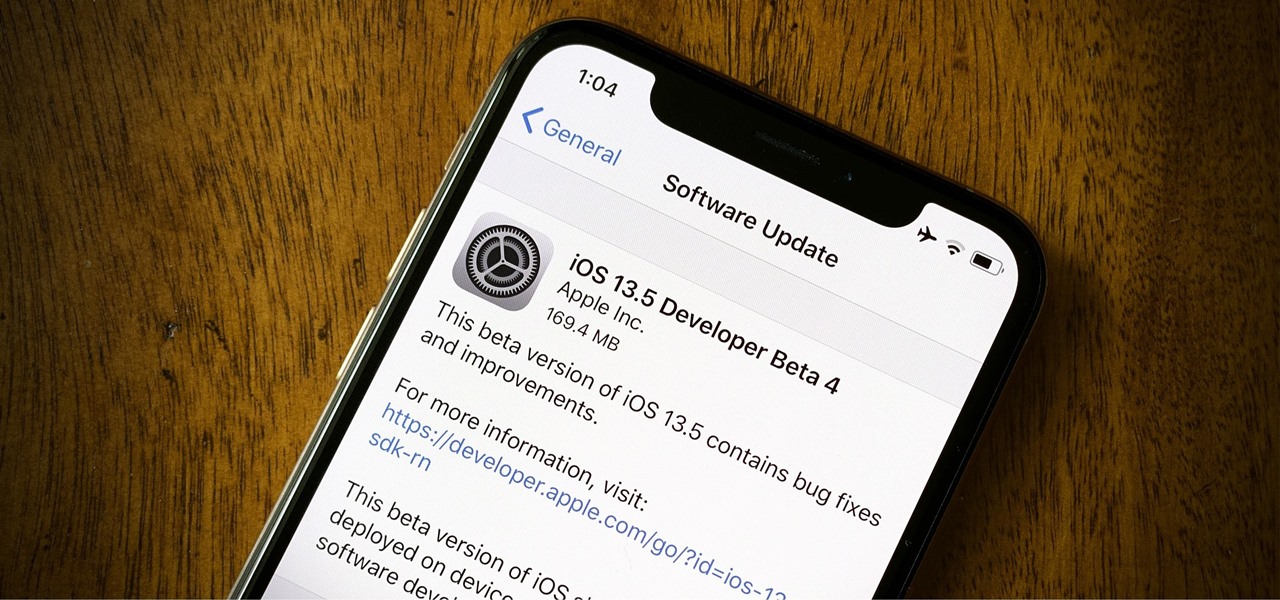
Apple released the fourth developer beta for iOS 13.5 today, Wednesday, May 6. This update comes one week after the release of iOS 13.5 dev beta 3, which introduced Apple and Google's joint COVID-19 exposure notification API to iOS for the first time. Apple updated that settings page to now include an "Exposure Logging" setting instead.

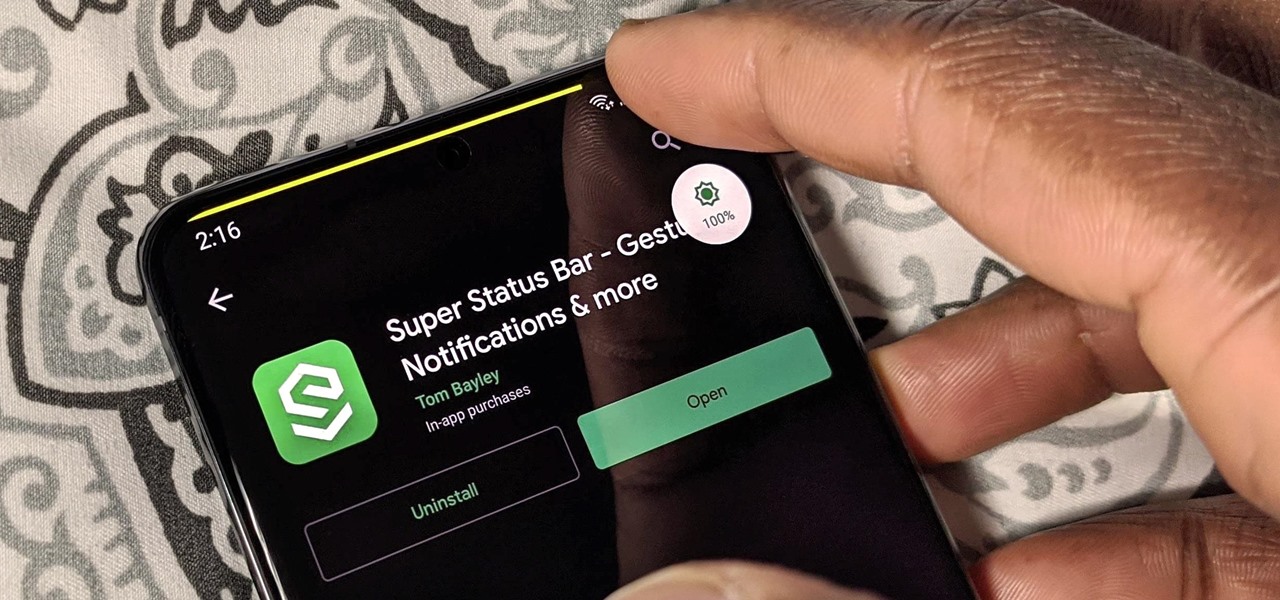
For Android smartphones, the latest craze is high refresh rate displays, and many popular flagships have them. But until now, there has been no way to confirm it is, in fact, running at higher hertz besides a menu option. Android 11 changes this.

Choosing which programming language to learn next can be a truly daunting task. That's the case regardless of whether you're a Null Byter just beginning a career in development and cybersecurity or you're a seasoned ethical hacking and penetration tester with years of extensive coding experience under your belt. On that note, we recommend Python for anyone who hasn't mastered it yet.

OnePlus releases some unique and exciting features before they start catching on with everyone else. Their OxygenOS is often considered the cleanest and most useful variant of Android. However, there are still a few key features OnePlus has yet to bring to their devices. This includes a proper lift to wake option.

LineageOS is great and all, but custom ROMs were at their peak when CyanogenMod reigned supreme. It had all sorts of innovative features that have since been copied by Google and Samsung and the like. But one thing that still hasn't been adopted into stock Android or One UI is CM13's easy way to adjust screen brightness.

Without admin privileges, installing additional software, or modifying the Windows 10 firewall, an attacker can alter a router and perform a variety of exploits. It's accomplished by forwarding requests from Kali through a backdoored Windows computer to the router gateway with simple SSH tunnels.