From parents and other family members to friends and peers, personalities are built by environment. Though people are important in the development of our own individual personality, there are other, different influences, including what you choose to read. The books you take the time to enjoy can make you nicer and more understanding, or leave you overall unchanged.

Admit it: when nothing's at stake other than your boss's disapproval, you don't exactly feel the urge to get working. Finding the motivation to take on a task, whether at work or home, can be a constant struggle. Though working through your laziness might seem like the best course of action, a meaner method can make more of an impact on your productivity.

Welcome back, my greenhorn hackers! Before we attempt to exploit any target, it is wise to do proper reconnaissance. Without doing reconnaissance, you will likely be wasting your time and energy as well as risking your freedom. In previous guides, I have demonstrated multiple ways to perform reconnaissance including passive recon with Netcraft, active recon with Nmap or hping3, recon by exploiting DNS or SNMP, and many others.

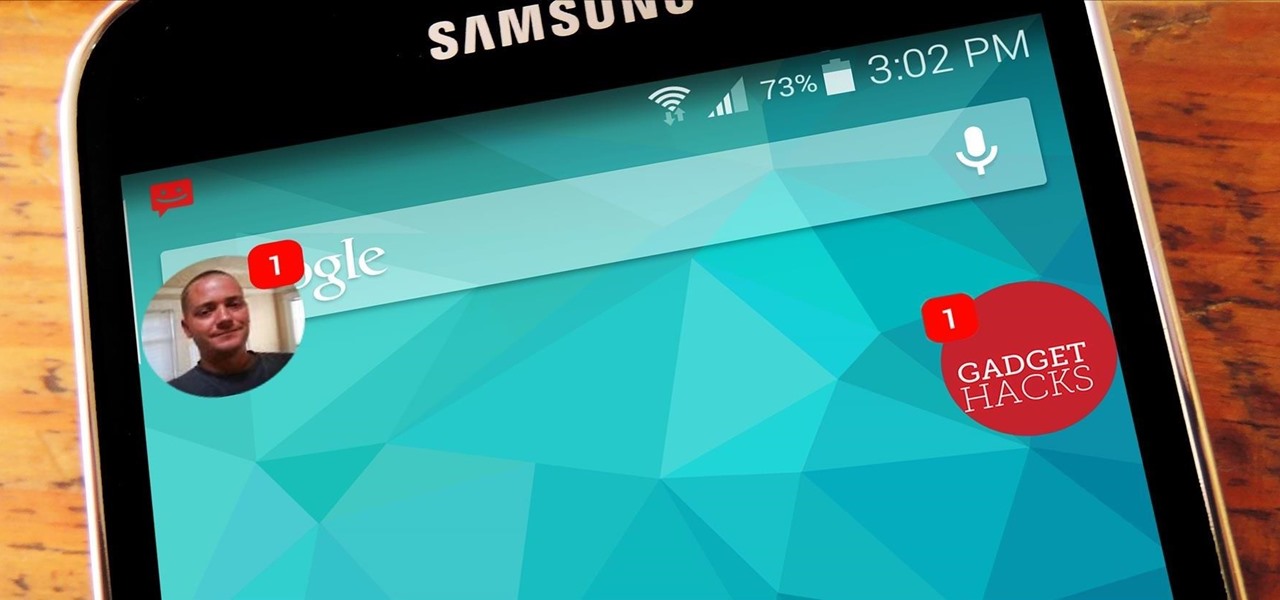
When Android 5.0 rolls out to the Nexus 5, several changes and new features will come along with it. The over-the-air update is already rolling out, and if you don't want to wait, you can get it right now.

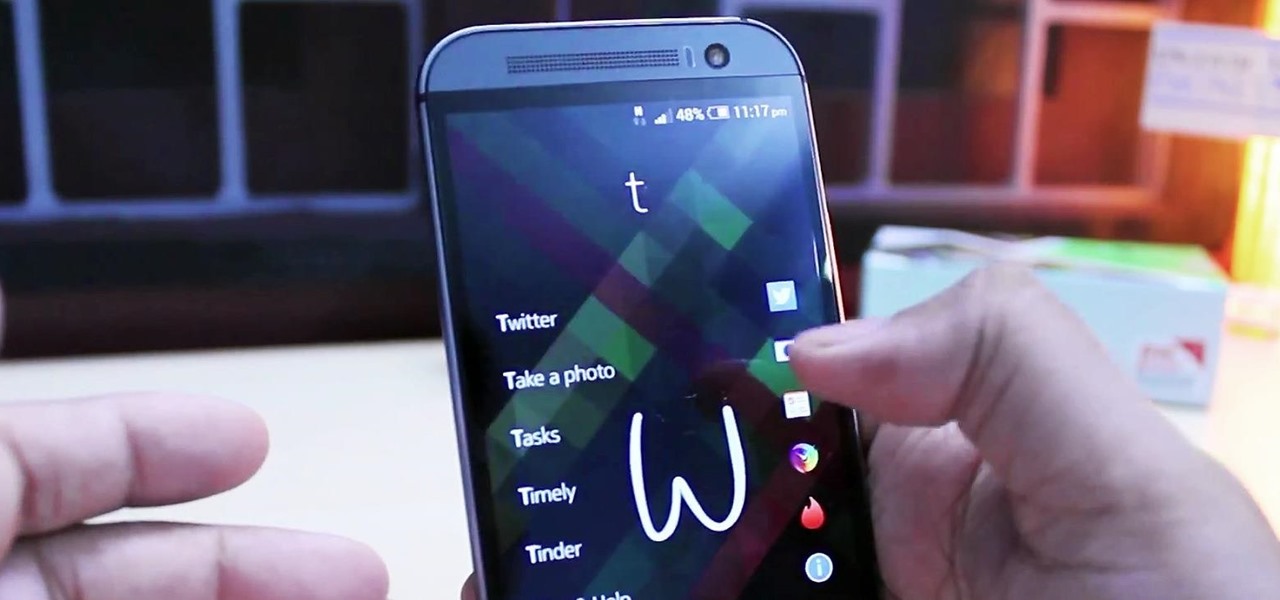
In my quest to find the perfect OS for my HTC One, I try any and every ROM I can get my hands on. This leads to countless repetitions of the wipe, install, and boot routine when I flash a ROM in recovery, especially when the newest ROM I try is a buggy piece of junk.

I have never been a morning person, and that's a trait that I don't think is going away. Combine my distaste for early hours with being a heavy sleeper, and it adds up to a lot of alarms being dismissed in a haze, with no real intention of ever waking up.

"Cooking" with liquid nitrogen seems like one of those activities that should be strictly limited to pros who are appearing on Top Chef, but it's the only way you'd ever be able to make Dippin' Dots at home. If that isn't enough of a reason for you to get some LN2 for your kitchen, check out this dose of pretty:

Pies and soufflés: these are two dishes that can try even the most experienced cook. Berry pies can be especially challenging, since the high water content of cherries, strawberries, blueberries, and blackberries often leads to a big, leaky mess once you cut into your beautiful pie.

When Android 4.4 was released, the massive changelog led to some awesome new features getting lost in the virtually endless list of new tweaks. One such change was the ability to set a default text messaging app, which streamlined the existing process of installing a third-party SMS client.

Pushbullet is one of those apps that helps separate Android from its competition. By pushing the boundaries of cross-platform data syncing and file sharing, the service truly demonstrates how flexible and robust the world's leading mobile operating system can be.

Believe it or not, but people are actually texting less than they did before, and that's all thanks to Facebook Messenger, Snapchat, WhatsApp, and other split-second communication services. However, one communication method that is still going strong—and dominating—is email.

Welcome back, my greenhorn hackers! Continuing with my series on how to crack passwords, I now want to introduce you to one of the newest and best designed password crackers out there—hashcat. The beauty of hashcat is in its design, which focuses on speed and versatility. It enables us to crack multiple types of hashes, in multiple ways, very fast.

You're in your car. You've got a bag of piping-hot French fries with you. You want those fries in your mouth ASAP, but you also want to dip them in ketchup. So what do you do?

Coffee is a topic that everyone has a strong opinion about, especially when it comes to brewing the perfect cup. Even if you buy the best beans and grind them yourself, chances are you're skipping one necessary step to make sure your coffee tastes the best it can: cleaning your coffeemaker the right way.

Developing an imperceptible lie is difficult, especially when you're lying right to someone's face. Thanks to smartphones, getting people to trust you is now easier than ever. You can craft a lie in seconds and hit send, all without ever seeing their untrusting faces.

If you have a hard time remembering what you've just read on your iPad or Kindle, try changing the font next time. The typeface you use to read books, newspapers, and online articles is either hurting or helping your memory, and you'll be surprised which ones are killing your brain cells.

While their merger with Microsoft has lead to a seemingly complete halt of new device development, some Nokia employees are still hard at work to bring new software to the table.

While you may look ridiculous doing the potty dance and crossing your legs back and forth, holding it in can be worth the discomfort when you've got an important decision to make.

Welcome back, my newbie hackers! Recently, I "upgraded" to Kali as my hacking platform, despite my preference for BackTrack. I did this reluctantly, primarily because new readers here could no longer download BackTrack from their site. I want to point out here that we all must keep in mind that with any software—or for that matter, any product—that is newer is not necessarily better.

Aside from the newer HTC One M8 and Samsung Galaxy S5, the Nexus 5 still has one of the fastest processors on the market today. However, despite its superpowers, some graphically intensive games can still have a bit of lag to them during gameplay.

Most days, getting through an eight-hour work shift is a struggle. There are a million places you'd rather be, and none of them include your desk. It's difficult to find the motivation to tackle the growing number of emails in your inbox when your mind is back at home, comfortable in front of your gaming system.

I have an embarrassing habit: I type with six fingers. Just as your grandma pecks at the keyboard with her two index fingers, I rely solely on my index, middle, and thumb fingers only. But it's not as slow as you think, and I'm not the only one out there that does it.

How many times have you heard someone utter the phrase, "Now, let's break into groups"? From classroom discussions to workplace think tanks, gathering into groups to generate ideas is common practice. These forced get-togethers are intended to encourage creativity and unique thought, but they can actually do the opposite. More often than not, group brainstorming is annoying rather than encouraging, and these group sessions can actually be detrimental to your productivity. Getting together har...

You've got to be sick of it by now. Those meaningless and unsatisfying articles, lists, and videos you were duped into clicking on because their headline made them impossible to resist.

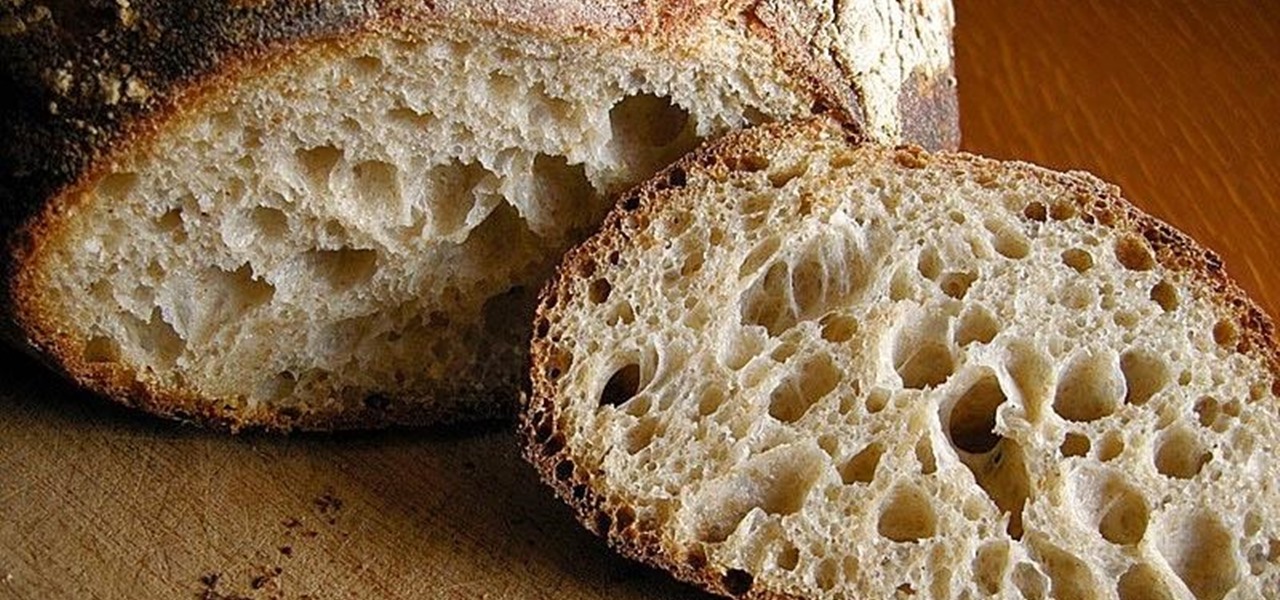
What is gluten, why do some people think it is pure culinary evil, and why are there more and more products devoted to being free of this mysterious substance? Here's what one person thinks: What Is Gluten Really?

Online gaming is nothing new, and with live YouTube streams becoming ever more popular, there always seems to be a way to watch people play video games. Twitch TV offers the same spectator experience you've come to know and love, but the people over at TwitchPlaysPokémon have gone a step further and made it so that the spectators are the ones playing the game.

Sometimes you've got a head of lettuce that you want to eat but it lacks a certain youth. In other words, it's wilted and browning at the edges. Other times, you get to the grocery store near the end of day and the only lettuce or greens available look a little on the sad side. Never fear. You're not doomed to a meal of fast food or mouthfuls of soggy salad. You can easily revive those leaves and have something crisp, green, and delicious for your next meal, so don't dump it in the trash.

Welcome back, my apprentice hackers! As many of you know, I have been hesitant to adopt the new Kali hacking system from Offensive Security. This hesitancy has been based upon a number of bugs in the original release back in March of 2013 and my belief that BackTrack was easier for the novice to work with.

You've probably seen someone in your family truss the turkey on Thanksgiving before roasting it, even if you don't recognize the word. To truss a bird or roast just means to wrap it up as compactly as possible before placing it in the oven, and it's usually done by tying it with string. Trussing a bird is a tradition that's been around for a long time, and a lot of home cooks do it religiously even if they don't know why. It's a highly debated topic with fierce supporters on both sides, but f...

What do Hulu Plus, Pandora, and YouTube all have in common? Ads—and lots of them. Sometimes, an advertisement or two isn't a big deal, but when you're bombarded with them daily on your iPhone, they can get old really quick, and might even lead you to delete the apps entirely.

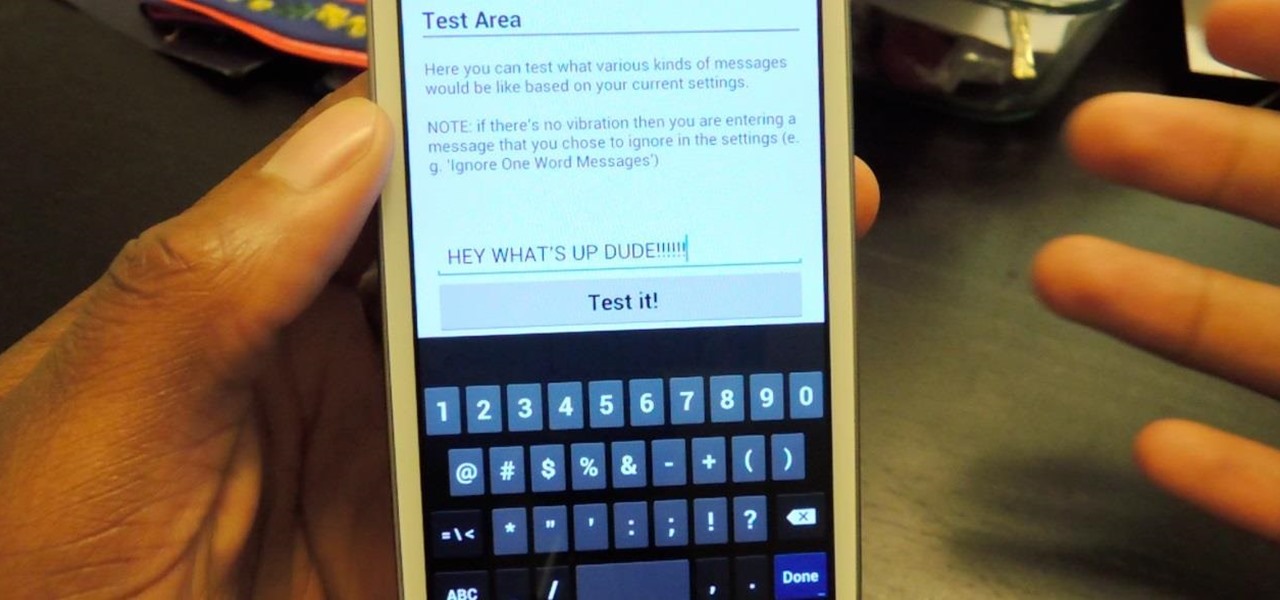
Toast notifications are a type of pop-up alert built into Android, letting us know when an app has performed a certain action. Whether it's Gmail saving a draft or Firefox opening a new tab, toasts are meant to be informational while not being totally intrusive.

The bread at your local supermarket will most likely always be fresh, but how do you know which loaf is the freshest out of the bunch? You can squeeze and inspect them like an annoying TSA agent, but there's actually a much simpler way to do it.

The constant stream of beeps and the buzzes coming from your Samsung Galaxy S3 can soon begin to fade into the background and remain forgotten. With smartphones vibrating for email alerts, Candy Crush notifications, phone calls, and text messages it can become difficult to tell which alert is which.

Welcome back, my tenderfoot hackers! I recently began a new series on digital forensics to help tenderfoot hackers from being detected and ultimately, incarcerated. In this installment of that series, we will look at recovering deleted files. This is important to hackers because you need to know that even when you delete files on your computer or on the victim's computer, a forensic investigator can usually recover them.

We're only years away from a complete Robot Revolution and Google Inc. will surely be leading the charge.

With only a few days left until Halloween, your options might be rather limited if you still don't have a costume. You may have laughed while some people spent the entire month of October painstakingly crafting their ridiculously detailed costumes, but now that the big day is so close, the joke's on you because you still have nothing to wear.

Welcome back, my neophyte hackers! In today's hack, we're going to have a bit of Halloween fun. Have you ever had a boss who made you miserable with his micro-management and nagging? Maybe you thought he unfairly fired your friend/colleague? Well, now here's your chance to get a bit of revenge and keep him or her off your back!

Apple may have made Mavericks more accessible to Mac users everywhere at the fair price of zero dollars, but unfortunately, they made it trickier to create a bootable install drive of the Mac OS X 10.9 operating system.

For over 20 years, a tiny but mighty tool has been used by hackers for a wide range of activities. Although well known in hacking circles, Netcat is virtually unknown outside. It's so simple, powerful, and useful that many people within the IT community refer to it as the "Swiss Army knife of hacking tools." We'll look at the capabilities of Netcat and how the aspiring hacker can use it.

Welcome back, my greenhorn hackers. When Wi-Fi was first developed in the late 1990s, Wired Equivalent Privacy was created to give wireless communications confidentiality. WEP, as it became known, proved terribly flawed and easily cracked. You can read more about that in my beginner's guide to hacking Wi-Fi.