Thanks to augmented reality, fashion companies can let customers try on cosmetics, clothes, more cosmetics, and sunglasses from the comfort of their homes and through the non-judgmental eyes of their smartphone camera.
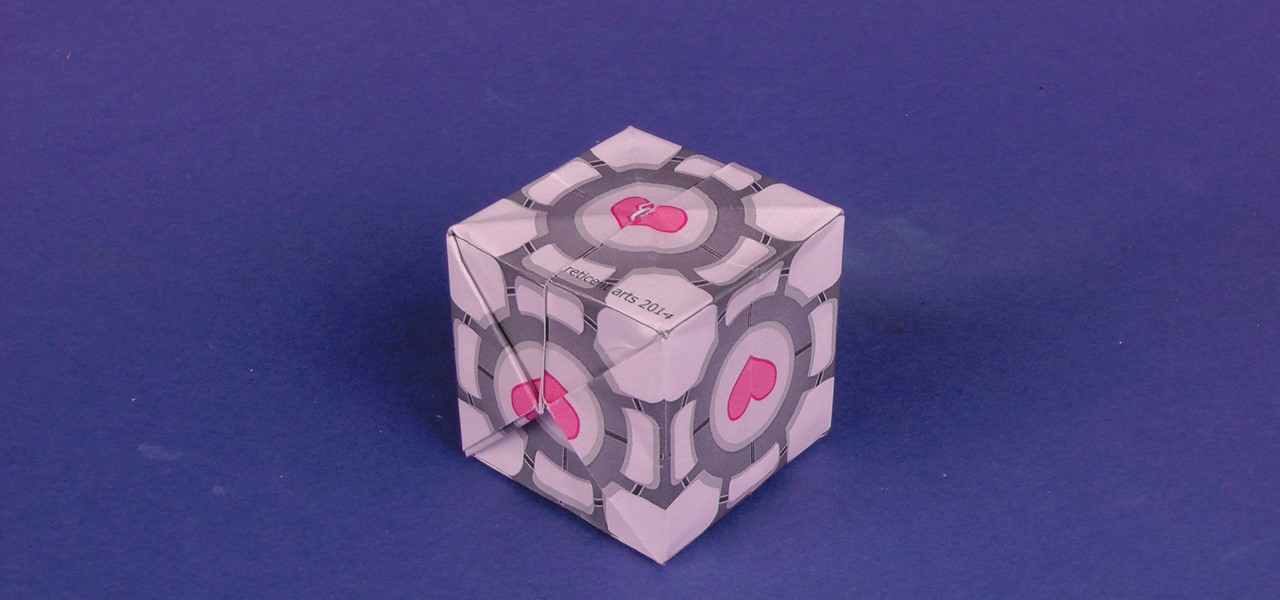
if you love the valve puzzle game portal but don't have the money to buy expensive merchendise, you came to the right place. here you will learn how to make your own companion Cube just from a printed template

Making a cool leather wallet is easy. Just get yourself some scrap strips of leather ant you are good to go. No special tool required. You can see full process of making this simple wallet in the video.

Being able to run mobile apps on a computer is nothing new. Maybe you don't have a mobile device, or maybe you just like seeing the apps on a larger screen. Whatever the reason, with programs like Bluestacks, you can use your laptop to Instagram, play Angry Birds, and run countless other apps made for smartphones.

There's a lot of firsts that President Barack Obama can claim, like being the first POTUS from Hawaii, the first to publicly support same-sex marriage, and of course, the first African American to hold office. One of his coolest firsts, though, is that he's the first American president to ever brew his own beer in the White House. And thanks to a Redditor who filed a Freedom of Information Act request, two recipes have been released so that home brewers everywhere can give them a try.

Canary tokens are customizable tracking links useful for learning about who is clicking on a link and where it's being shared. Thanks to the way many apps fetch a URL preview for links shared in private chats, canary tokens can even phone home when someone checks a private chat without clicking the link. Canary tokens come in several useful types and can be used even through URL shorteners.

It's easier than you might think to hack into Wi-Fi routers using just one unrooted Android phone. This method doesn't require brute-forcing the password, a Windows OS for converting PowerShell scripts into EXE format, a reliable VPS for intercepting hacked Wi-Fi passwords, or Metasploit for post-exploitation tricks.

Apple's macOS operating system is just as vulnerable to attacks as any Windows 10 computer or Android smartphone. Hacker's can embed backdoors, evade antivirus with simple commands, and utilize USB flash drives to completely compromise a MacBook. In this always-updated guide, we'll outline dozens of macOS-specific attacks penetration testers should know about.

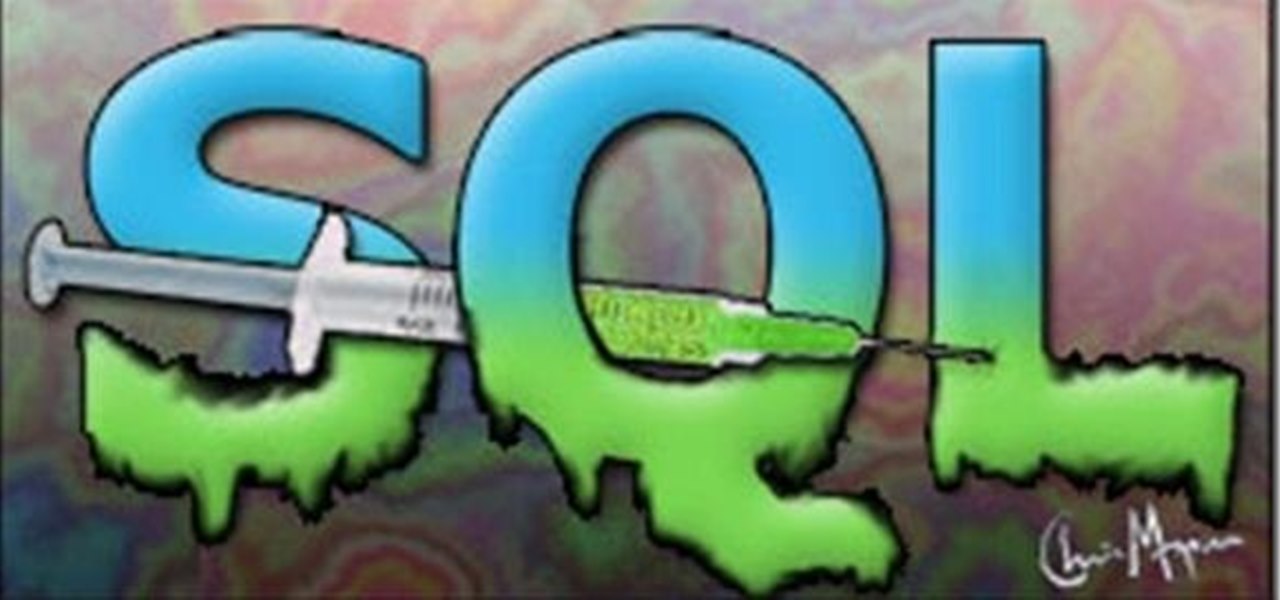
With all the web applications out on the internet today, and especially the ones built and configured by novices, it's easy to find vulnerabilities. Some are more perilous than others, but the consequences of even the slightest breach can be tremendous in the hands of a skilled hacker. Directory traversal is a relatively simple attack but can be used to expose sensitive information on a server.

Starting April 10th, you'll will be able to book 15-minute appointments online to try on an Apple Watch in person at Apple Stores across the world. With the April 24th release date just around the corner, making an appointment is a great idea for those who are unsure about which color and size to purchase—or if they'll even want one.

Apple's Gatekeeper security software for macOS (Mac OS X) is vulnerable to remote attacks up to version 10.14.5. An attacker that's anywhere in the world can exploit MacBooks and other Mac computers by sharing a single ZIP file.

Once a hacker has created a PowerShell payload to evade antivirus software and set up msfconsole on their attack system, they can then move onto disguising their executable to make it appear as a regular text file. This is how they will get a Windows 10 users to actually open the payload without knowing they are doing so.

In the years leading up to the release of the Apple Watch, we were frequently teased with concept designs of what Apple's smartwatch might look like. Of course, many of those outlandish designs were off the mark, but the attention to the idea itself hinted that the public was ready for a mainstream wearable from a high-end hardware maker like Apple. Now smartglasses are getting the same treatment.

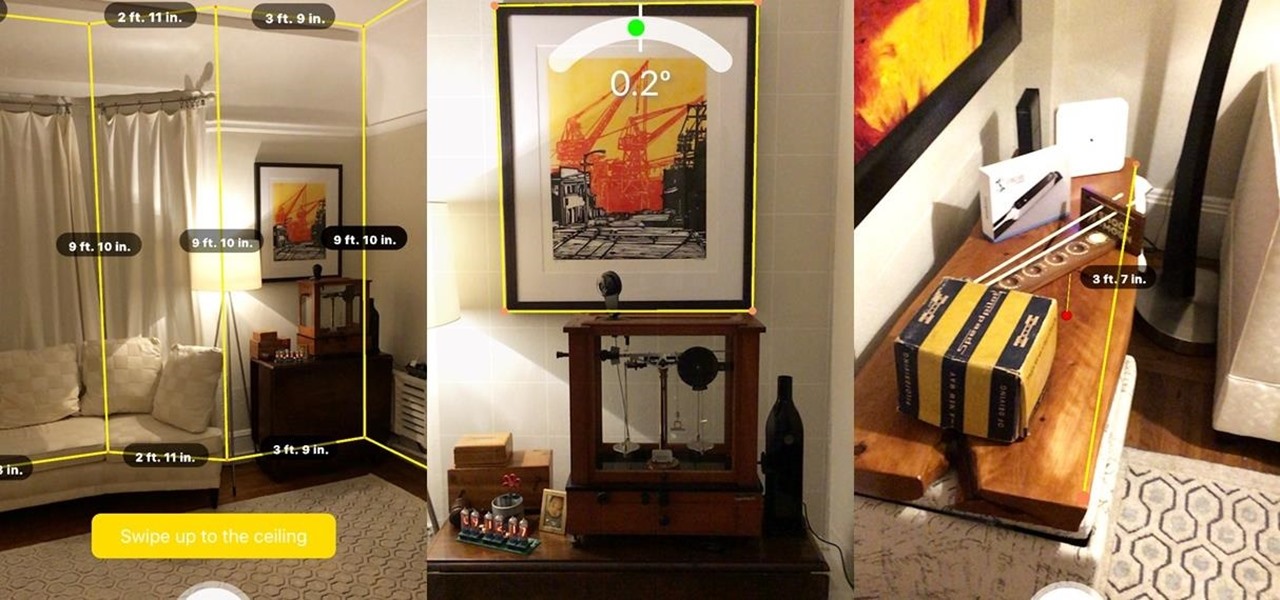
In off-record discussions with AR experts, the consensus on ARKit is that it takes a software approach to the depth-sensors available on Tango devices. As a result, the toolkit has shortcomings, such as detecting walls and vertical surfaces.

Welcome back my fellow army of hackers! Today we'll be hacking a website. Hacking is technically not the right word used here. It should be defacing! So we are going to deface a website...

Welcome back my fellow hackers! In my last few articles, I've concentrated on what is called a listener, which is basically the same thing as backdoor and rootkit, only "listener" sounds much less malevolent than the other two terms.

Don't spend all your hard-earned money on store-bought Christmas decorations this year. Spend it on cheap paper and make your own Christmas decorations, like this origami snowflake.

You may not know how to draw, but but don't let that discourage your from trying. This video will take your fears away and prove to you that anybody can draw if they want to! A little instruction is all anybody needs to succeed. But drawing hands is difficult, right? Sure, hands are one of the tougher parts of the body to sketch, especially when holding something, like the pencil in this drawing. But practice makes perfect, so don't give up.

Sleepy John Estes is known as one of the masters of Delta Blues, so when learning to play the blues, he's a good place to start with. In this video lesson, see how to play the song "Somday Baby" by Estes on your blues guitar in an Open G tuning with a slide.

Get a crash course on HScript Expressions, Variables, and Attributes in Houdini 10. If you don't even know what this means, then you probably need to check this video tutorial series out. Understanding how to massage data in Houdini is key to giving yourself the creative edge and allowing you to unleash mind-blowing visual effects. This 18-part video series covers a variety of simple yet essential weapons in your arsenal including Global, Standard and Custom Variables to Math and String Modif...

In this article, we will explore the basics of radare2, a powerful package that comes with Kali. We are going to write a simple program, and then disassemble it, to see what is really doing in the processor.

Being an Google fanboy means that I pretty much use anything with the company puts out, so it's no surprise that out of all the cloud services out there, I stick with Google Drive. But, this is way more than just some blind allegiance.

The newest version of macOS has arrived. While everyone's mind is being blown by Mojave's groundbreaking new Dark Mode, we'll be taking advantage of its insecure file permissions to establish a persistent backdoor with a self-destructing payload that leaves little evidence for forensics.

Welcome back, my rookie hackers! Many newbie hackers focus upon the technical aspects of hacking and fail to give enough attention to social engineering. In fact, I would say that technical hacks should ONLY be attempted if social engineering attacks fail. Why bother spending hours or days trying to hack a password if someone will simply give it to you?

Learn how to edit audio files using Audacity of the MAC. 1 Create an audio file by using the built in recording function in Audacity. Save the file prior to starting your editing. 2 Open the file that you created earlier and test the file by playing it. 3 You can copy, cut and paste different parts of the file by highlighting the section in your file and then right clicking (or option clicking) and choosing what you want to do from the pop up file. 4 You can also add effects by highlighting a...

In previous versions of Acrobat you could run PDFs against the Preflight tool and it would either pass or fail. If it failed you would then have to manually resolve the problems in the PDF or by generating a new PDF. In Acrobat 8 Professional you can now apply "Fix-ups" to correct the most common problems encountered in working with PDFs for print.

Ever wanted to crop a PDF? In this video we'll take a look at the various ways to do it and some reasons why you would. The nice thing about cropping a PDF is that the information that is cropped off is never actually deleted. Watch this Terry White's video now!

The science-fiction author, Arthur C. Clarke, once said, "That any sufficiently advanced technology is indistinguishable from magic". Who would have thought that we could create a wave of air with a piece of cardboard, and fly a folded sheet of telephone book paper on the wave of air? With this three-part video tutorial, you can find out how you can fly a piece of paper, making it surf on a wave of air. See how to make an origami tumblewing glider.

Enjoy a delicious Korean dish called Bibimbop with a Japanese twist! Join Gwyneth Paltrow and Chef Lee Gross in Paltrow's GOOP kitchen to learn how to make bibimbap (mixed rice, or roughly translated to "mix it up").

"Fast food" can be healthy and gourmet! Foodie Gwyneth Paltrow hosts this quick cooking show to take you through the steps of a roast chicken and potato meal. You'll need a chicken, a couple lemons, garlic, rosemary sage, thyme, pepper, olive oil, and fingerling potatoes. You don't need to be a fan of Gwyneth Paltrow's to enjoy the tasty meal prepared in this mini cooking show from her website GOOP.

DreamWelder Productions presents this video tutorial from their show Info Tech, hosted by Jay A. Kelley. They take an exciting new look into new equipment for the film and television industry, showing you the best gear for your movies and shows.

Copying a file's path on your Mac isn't always an easy task. Thankfully, this cool little OSX utility called Copy Path Finder helps solve this problem and lets you copy the path of a file in your file system to the clipboard so that you can paste it into a text editor later.

Computer Science Professor Francesco De Comité has a fantastic gallery of mathematical images on Flickr. As part of this collection, he has a few hundred images of real or rendered polyhedra made out of paper or playing cards which he calls "slide togethers." These are constructed by making cuts and then sliding one component into the other, creating a shape without using any glue. He constructed the entire set of the platonic solids—the cards form their edges—which can be seen in the image b...

In this video, you will learn how to create a custom gift bag. Before you watch, you will want to download the pdf template for the bag, by visiting artycrafty.wordpress.com. First, you will print the template out onto decorative craft paper, which should be A4 letter-sized. Next, you will cut around the solid lines, as shown on the template, and cut out any additional decorative stencils, as you wish. While watching the video, you are free to decorate the pieces of paper any way you would li...

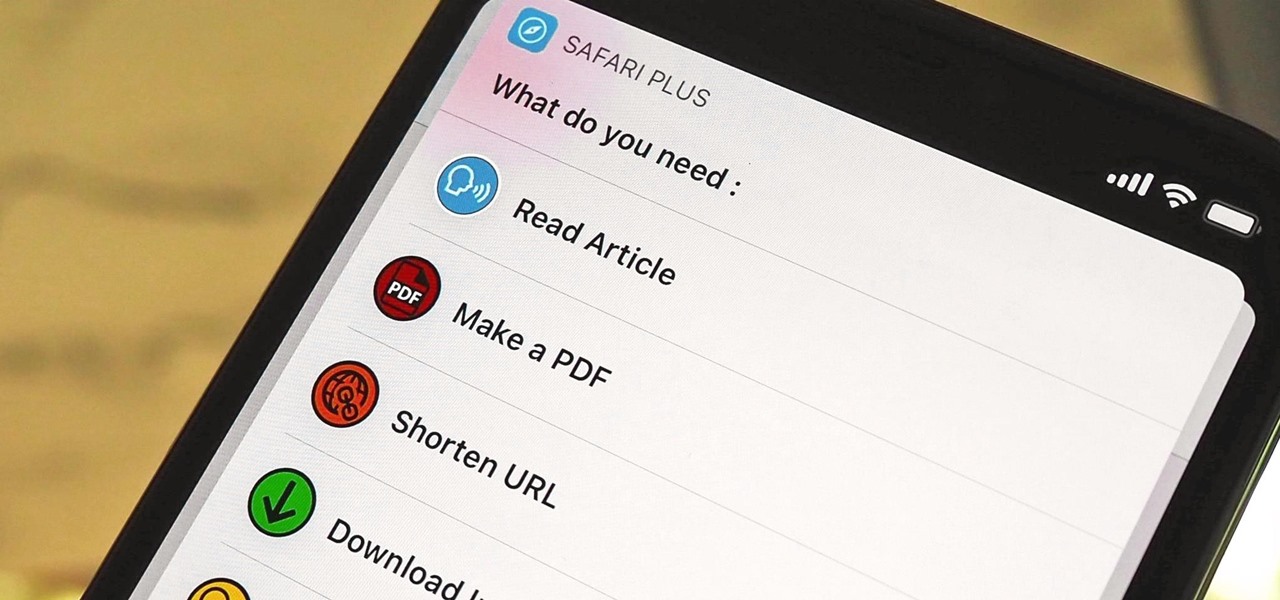
Safari saw many new features and improvements with Apple's latest iOS update, including webpage translations, privacy reports, and picture-in-picture. While the updates were well-received, Apple's mobile browser is still lacking some very basic features. Thankfully, there are shortcuts to bridge the gap.

You're on your computer a lot, so it only makes sense that you download the best apps and software for it. The Official Cyber Monday Mac Bundle Ft. Parallels Pro & Luminar 4 is available for only three weeks at an additional 40% off the sale price of $69.99. Just use the promo code CMSAVE40 at checkout.

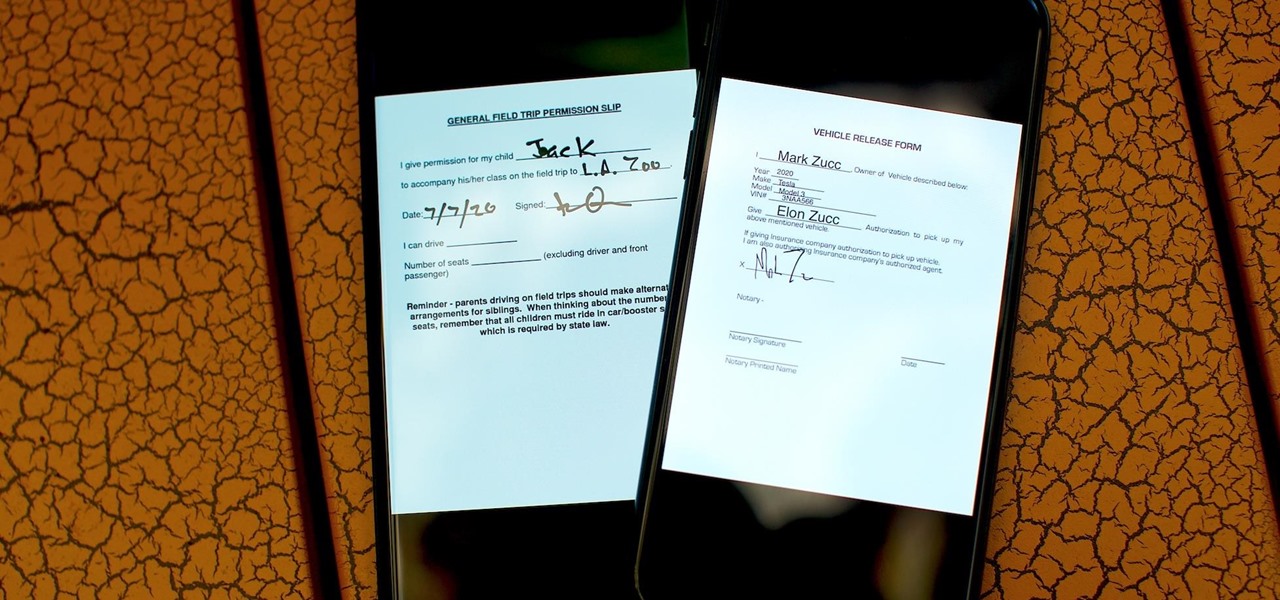
As paper forms become a thing of the past, it's becoming commonplace to fill out contracts, rental agreements, waiver release forms, and non-disclosure agreements online. You can easily fill out forms on your laptop, but how can you best do this using your iPhone or Android device?

iOS 12 has a feature that lets you instantly share saved Wi-Fi passwords with other iPhone users, but it can be finicky when you're sharing with multiple people. Then there's an even more pressing question: How do you share your password with Android users? Thankfully, there's a Shortcut that can solve these problems.

The macOS 10.14 security update tried to make parts of the operating system difficult for hackers to access. Let's take a closer look at how its new feature works and what we can do to spoof the origin of an application attempting to access protected data.

Passwords and data stored in web browsers are extremely valuable to hackers. If not for financial gain, black hat hackers may still leak your passwords and personal information for amusement. Never undervalue what you're worth to a hacker.