Since I first announced the new Null Byte recognition for excellence a few weeks ago, several of you have written me asking, "How can I study for this certification exam, and what material will be covered on the exam?" Now I have an answer for you. The White Hat Hacker Associate (CWA) will cover 14 domains or areas. Everything you need to know is here on Null Byte. There will be no questions that are not covered here on this site, guaranteed.

Welcome back, my tenderfoot hackers! Well, the first season of Mr. Robot just ended and Elliot and fsociety successfully took down Evil Corp! They have effectively destroyed over 70% of the world's consumer and student debt! Free at last! Free at last! Of course, global financial markets crashed as well, but that's another story.

When most people think of "gaming computers," they're probably thinking of Windows-based PCs. They offer a huge variety of devices with better equipped software and hardware for a cheaper price, and there are more available games than there are for OS X-based systems.

Most of us only see our screen savers in passing, as some sort of slide show or animation as we glance up at the screen or walk by the computer. Usually, anything is better than a boring blank screen—even the classic Pipes screensaver is better than nothing.
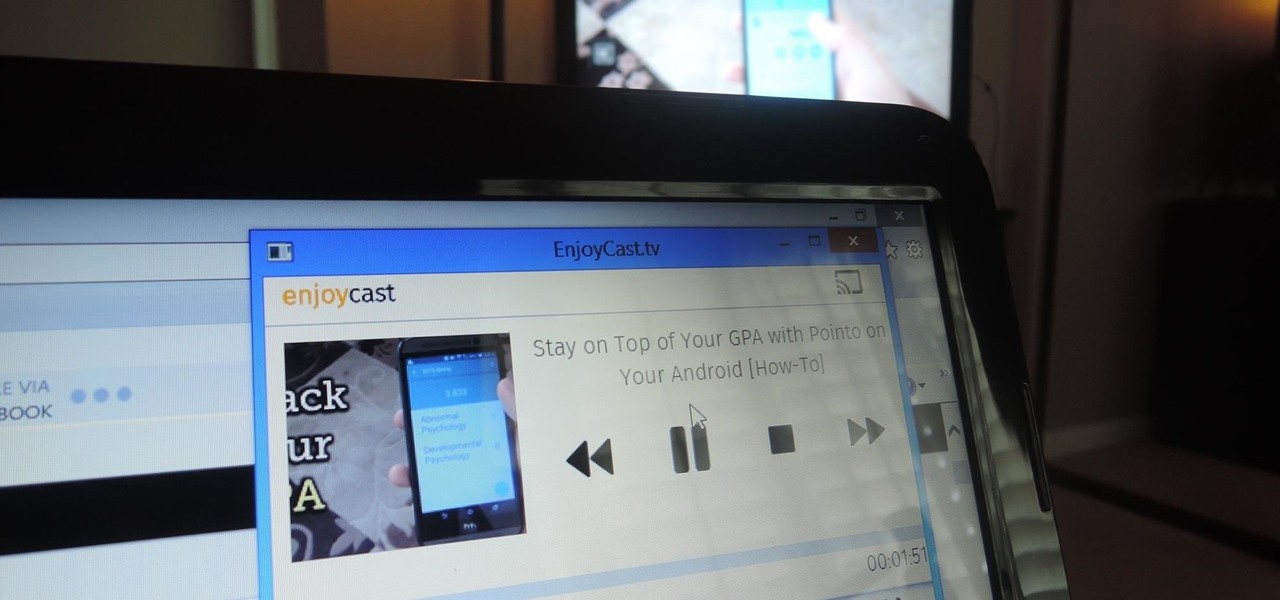
Google's Chromecast has been out for almost two years, and I can safely say it has changed the way I use my TV. At first it was a hassle to even get local media to play on it, but now casting has branched out to torrent streaming, which was a real game changer. Unfortunately, most apps only let you stream one video or song at a time, or you can't add magnet links or torrents to a playlist of local content.

This is a short explanation and tutorial on how to grab saved passwords from Google Chrome, ideally from a meterpreter session. The idea behind this is to understand how saved passwords work and how to keep them safe. Let's have some fun :D Understanding Google Chrome Saved Passwords

Welcome back, my fledgling hackers! Let's continue to expand our knowledge of digital forensics, to provide you the skills necessary to be a digital forensic analyst or investigator, as well make you a better hacker overall. In your attempts to enter a system or network undetected, it is key to understand what a skilled forensic investigator can learn about you, the alleged hacker.

I wrote a python script that allows you to easily ask what service runs on a specific port and vice-versa. Now, I am sure that such a program already exists on our lovely linux OS's, but... I didn't think of that before I started, and haven't found it yet. So if you haven't found it yet either, maybe you'll find this of some use. It's just called getport. If I have a port number, and want to know what services run on that port, I do:

Welcome back, my novice hackers! Previously in my "Spy on Anyone" series, we used our hacking skills to turn a target's computer system into a bug to record conversations and found and downloaded confidential documents on someone's computer. In this tutorial, I will show you how to spy on somebody's Internet traffic.

In this simple tutorial you will be shown step-by-step how to write local shellcode for use on 64-Bit Linux systems. Shellcode is simple code, usually written in assembly that is used as payload in exploits such as buffer overflow attacks. Payloads are the arrow head of an exploit: though the rest of the arrow is important for the delivery of the attack, the arrow head deals the killing blow. In reality, payloads are slightly less exciting yet far more interesting and intelligent than medieva...

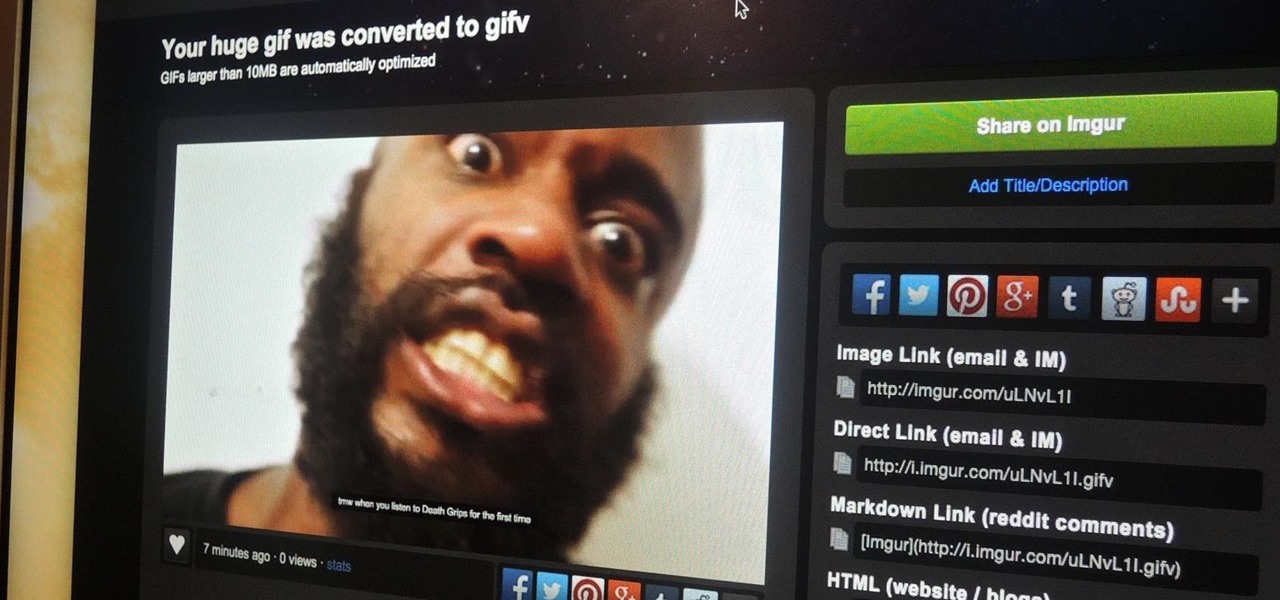
Imgur has just released a brand new feature to make GIFs better than they ever have before. Video to GIF is a tool that allows you to quickly paste any video link, easily select a clip from that video, and turn it into a very high-quality GIF, called a GIFV.

To play Minecraft with mods you will need to install Forge. Most people think this is hard to do, not so. It is very simple and in less than 5 minutes you can be playing Modded Minecraft.

The OnePlus One comes with CyanogenMod 11S built in, but there are certainly some traditional CyanogenMod features missing from this version. One of the most obvious missing ingredients is the lack of a native SuperUser app, most likely to prevent inexperienced users from causing unintentional damage to their device's software.

For the most part, Finder has had the same basic functionality through the various releases of OS X. But Apple's lack of interest in adding new bells and whistles to the backbone of their operating system simply means that 3rd-party developers get to shine, and Tran Ky Nam is one such developer. He created his own extension for Finder that adds tabbed browsing, dual pane mode, cut & paste functionality, and much, much more.

Without a comprehensive root method for all Android phones and tablets, a device-specific approach is needed. And since we always cover new rooting methods for all the popular phones here at Gadget Hacks, we've built this always-updated guide to rooting many mainstream Android devices.

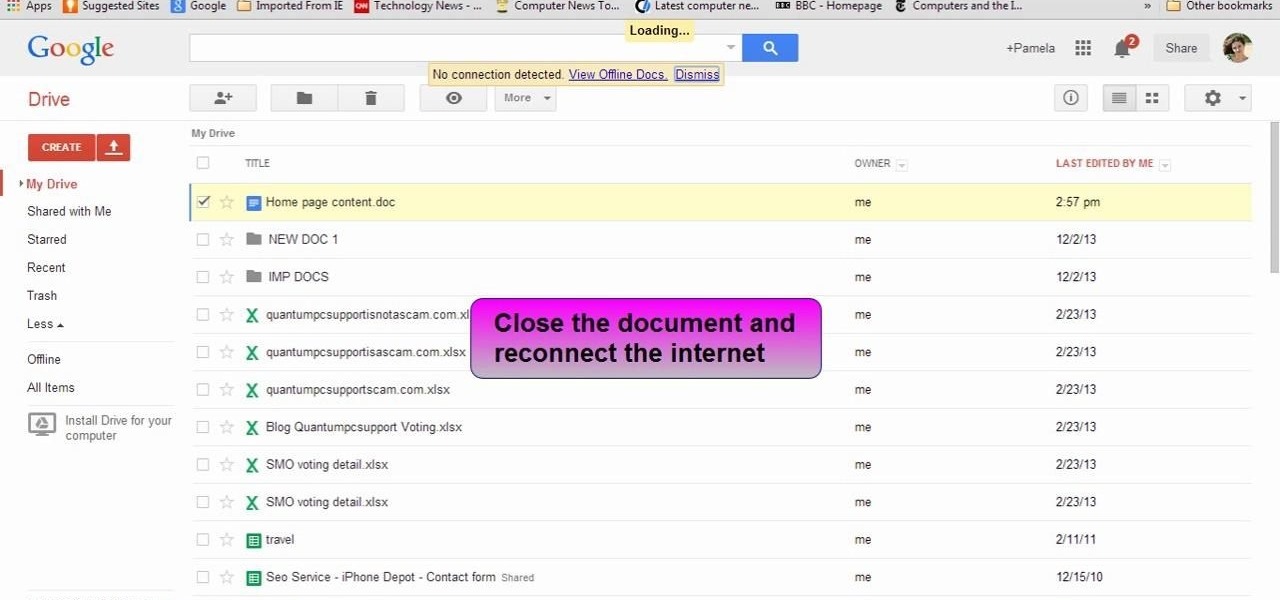
This video will show you how to view and edit Google drive documents offline. You could do this only in Google Chrome browser. If you are editing or viewing a Google drive file and suddenly internet connection is gone, you can still view and edit. You should only download an app for it. It will save your changes offline and will automatically update when you will reconnect with internet. Follow the video and do it in your Google Chrome browser.

Welcome back, my rookie hackers! Now that nearly everyone and everyplace has a computer, you can use those remote computers for some good old "cloak and dagger" spying. No longer is spying something that only the CIA, NSA, KGB, and other intelligence agencies can do—you can learn to spy, too.

Welcome back, my rookie hackers! I recently began a series on using Metasploit, and my goal with it is to teach you the very basics the incredibly powerful hacking tool has to offer while progressively moving on to the more advanced features.

My OnePlus One easily gets over a day of battery life without a problem, but when I try to charge it, it seems to take just as long. For some reason, no matter what charger you plug your OPO into, it never gets more than USB-level power, meaning that charging times are more than double when compared to traditional AC-charging.

One day I was contemplating about a canard paper airplane design. After several attempts, here is what I got - the Eurofighter Paper Airplane.

Welcome back, my neophyte hackers! I have already done a few tutorials on password cracking, including ones for Linux and Windows, WEP and WPA2, and even online passwords using THC Hydra. Now, I thought it might be worthwhile to begin a series on password cracking in general. Password cracking is both an art and a science, and I hope to show you the many ways and subtleties involved.

Fish is delicious, and as the Harvard School of Public Health points out, incredibly good for you. There are many studies that show regularly consuming a couple of servings of fish per week can help prevent heart disease and may well reduce your chances of stroke, depression, and getting Alzheimer's. After all, there's a reason why fish is called "brain food."

This video will show you how to change the default downloading folder for your downloads. When you download a video or file it is saved in the default downloading folder in our PC. You have to go to that folder then copy or move the folder in a specific location. But you can get rid of such extra work by setting your downloading folder in a different location you want. The next time you download something that will be saved in your specified location. Watch the video.

Adding to the recent recent slew of bugs and issues within iOS 7, it now seems that emails sent with attachments are not encrypted, despite Apple's claims that they are.

The Android 4.4.2 KitKat update is available via firmware upgrade for the international GT-N7100 variant of the Samsung Galaxy Note 2, about a month after we saw its first leak. The update is available via Kies in France, with and OTA update soon to follow. Details courtesy of SamMobile are as follows:

As with most OEMs, HTC would like you to think that you can do virtually anything with your new HTC One M8, but as a softModder, you know that isn't true. To actually unleash the full potential of that device, you need access to the whole system, not just the parts that HTC deems okay for you to mess with.

That didn't take very long! Yesterday, after a lengthy delay, Google opened up the development kit for their Chromecast HDMI dongle.

Welcome back, my hackers novitiates! As you read my various hacking tutorials, you're probably asking yourself, "What are the chances that this hack will be detected and that I'll land behind bars, disappointing my dear mother who already thinks I'm a loser?"

Scrolling through Instagram, you're going to come across a lot of photographs and videos that you "like." But sometimes, you're going to want to remember a photo, and naturally want to save it to your device so you can look at it for forever and ever.

The iOS 7 release brought with it many new aesthetic upgrades, from new flat, vibrant icons to a sleeker text messaging interface. Another small, yet noticeable, difference is the minimal and clean lock screen, which removed the overbearing "Slide to Unlock" background bar in lieu of just the text.

Welcome back, my fledgling hackers! As nearly everyone has heard, Target Corporation, one of the largest retailers in the U.S. and Canada, was hacked late last year and potentially 100 million credit cards have been compromised. Happening just before Christmas, it severely dampened Target's Christmas sales, reputation, and stock price (the company's value has fallen by $5B).

If you have an older Samsung Galaxy Y smartphone, one thing you should be doing is using an microSD or microSDHC memory card to help improve your Android's processing speed and make it easier to transfer large or small files easily. These cards are also compatible with certain cameras and can be inserted into some computers. While all this is all good and well, you'll still need to know how and where to put your SD card in order to indulge in any of these benefits. Your Samsung Galaxy Y (the ...

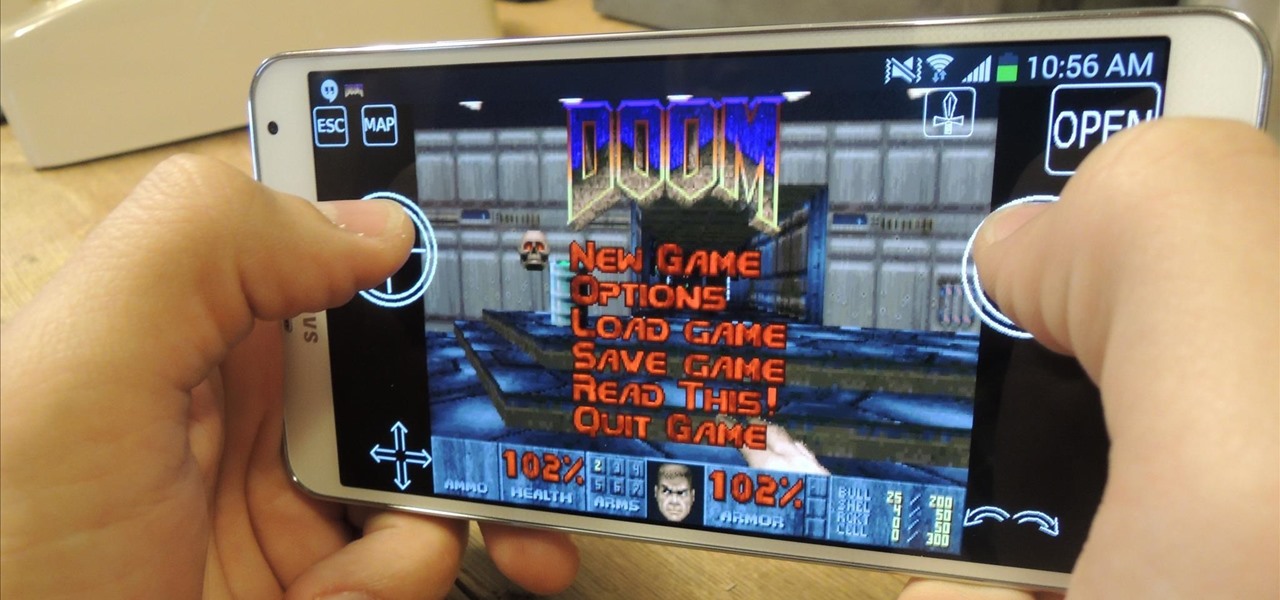
In the wake of its 20th anniversary, the folks over at Eltechs have released Original DOOM, a full shareware version of the revolutionary first-person shooter DOOM for Android, available for free on the Google Play Store. It's unmodded and unaltered from the original FPS classic.

Welcome back, my hacker apprentices! Metasploit framework is an incredible hacking and pentesting tool that every hacker worth their salt should be conversant and capable on.

This tutorial is about how to create the floating bar with social media buttons on a weebly website. Weebly has change its layout on the dashboard. Its a new video of new layout of weebly dashboard. I found many quesiton regarding 4 different HTML files instead of one index.html. Users were asking about in which they have to change the code so here is the solution. Watch the video, drop your comments and feel free to ask.

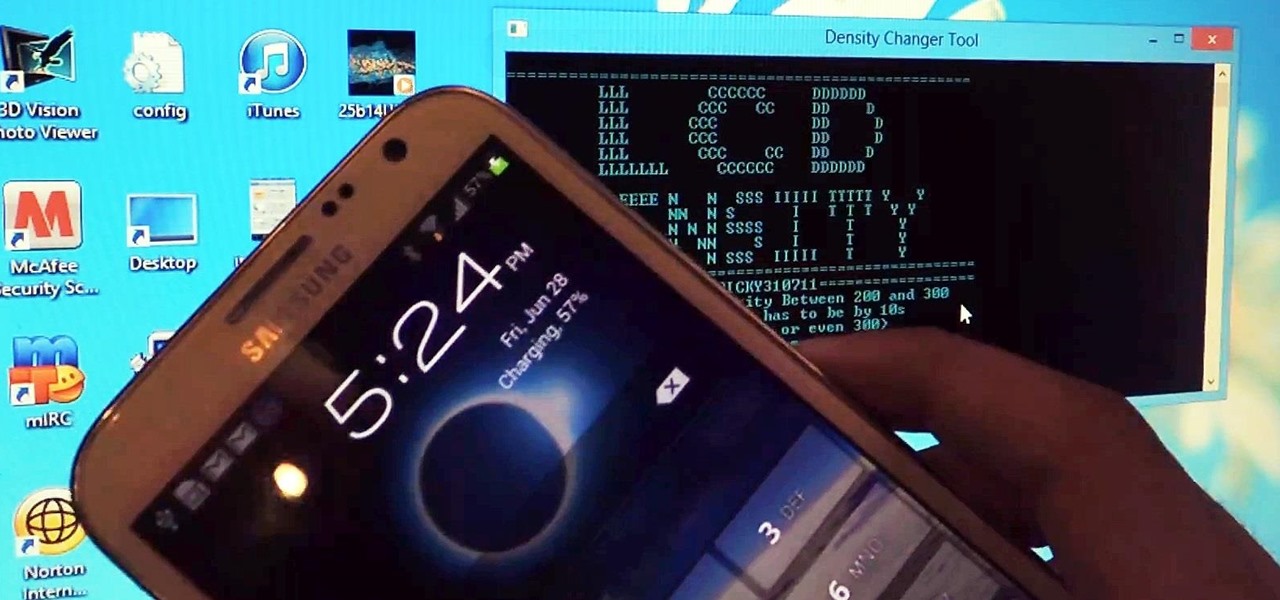
There are a ton of cool features available on your Samsung Galaxy Note 2, but if you're a softModder, you can make your phone do just about anything.

If smartphone video games have a weakness, it's probably their inability to emulate the riveting and immersive experience that consoles offer.

I find that little annoyances are always far more irritating than their larger counterparts, especially if there's no obvious way to get rid of them.

The rumors are flying everywhere about the Samsung Galaxy Note 2 getting updated to Jelly Bean 4.2, but as of now, we have no freakin' idea when. Among all of the features sported in the update, Photo Sphere is one of the more popular, allowing you to snap incredible and immersive 360 degree photographs. So, until that update comes, you're probably still marooned with Jelly Bean 4.1.2 on your Note 2, and that means no Photo Sphere camera.

This step-by-step tutorial will show you how to install Mac OS on Windows 7 on Virtual Box. Video: .