
How To: Format and reinstall Windows XP
This video shows people how to format and reinstall Windows XP on their PC from a CD.


This video shows people how to format and reinstall Windows XP on their PC from a CD.

TWRP is the premiere custom recovery for Android because of how many devices it supports and how simple it is to use. But installing it in the first place hasn't always been the easiest thing to do — until now. With the help of a Magisk module, you can finally use one Android device to flash TWRP on another.

When using Group FaceTime with more than a handful of people, all of those participants in one chat can be difficult to follow. That's why Apple automatically enlarges the tiles for people who are currently speaking, bringing them into the forefront. However, all of that zooming in and out can get pretty distracting, and now there's a way to disable it whenever you need to.
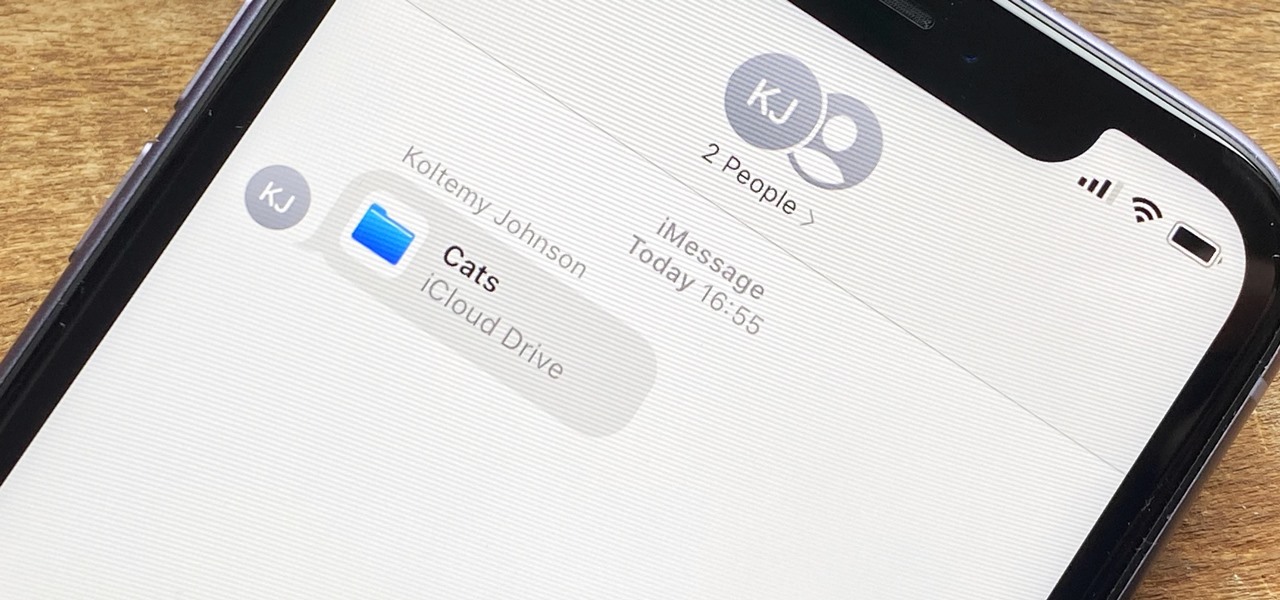
In the iOS 13.4 update, Apple added folder-sharing capabilities in the Files app. That means you can share multiple documents at the same time instead of doing it one by one. But that's not all — you can share folders with numerous contacts and even enforce access and permission settings.
On March 13, President Trump announced during a briefing in the Rose Garden that Google was building a COVID-19 screening website to help Americans understand if they might have the new coronavirus. If likely infected, the site would also include the location of a local drive-through testing site to visit. So how can you access the screening website?

Getting root is considered the Holy Grail in the world of Linux exploitation. Much like SYSTEM on Windows, the root account provides full administrative access to the operating system. Sometimes even a successful exploit will only give a low-level shell; In that case, a technique called privilege escalation can be used to gain access to more powerful accounts and completely own the system.

Any internet user will need to download files eventually, and most simply have faith that what they are downloading is trustworthy. This doesn't give much clarity into the contents of the file, but if the file's author published the original checksum, comparing it to the SHA-256 hash of the downloaded file can ensure nothing was tampered with.
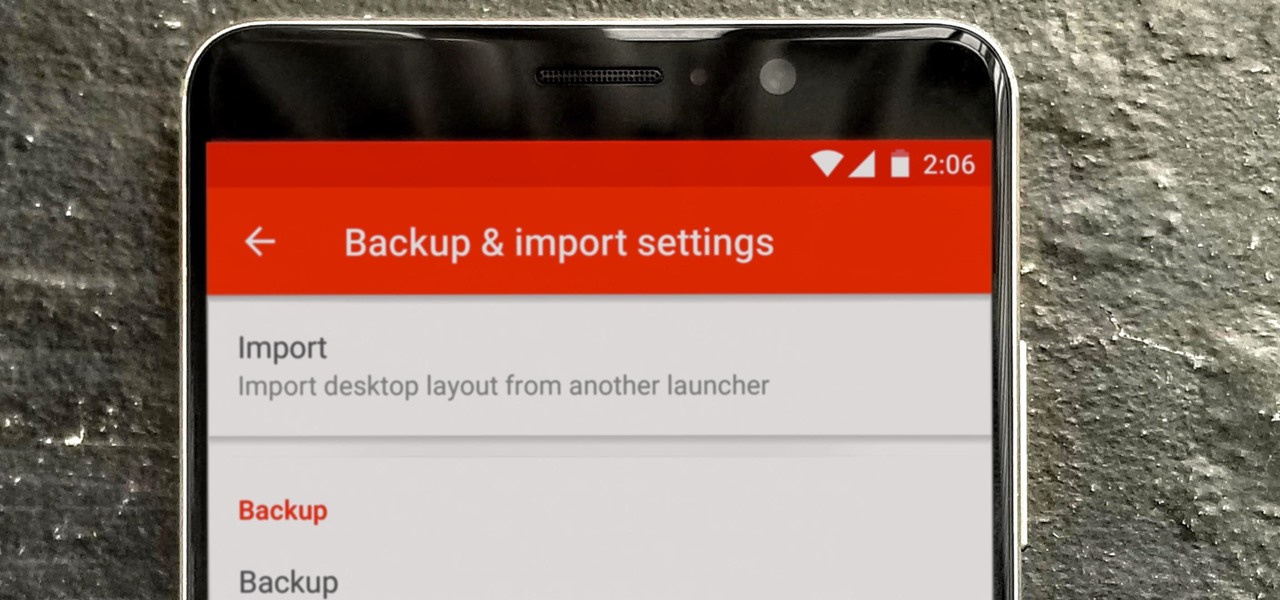
So you spent all day customizing your phone. You tinkered with all the settings, searched the web high and low for the perfect wallpaper, and found an ideal icon pack to complement the color scheme. You go to sleep, proud of the work you accomplished when the unspeakable happens — your phone freezes and tech support is telling you to do a factory reset to fix the problem.

According to a new study from the Reuters Institute and the University of Oxford, people are getting their news from ... unexpected sources. Put away your CNN app and stop checking the New York Times because a familiar app is now keeping you up to date on current events: WhatsApp.

Update 6/16: This number is now way higher. In just the first two days of this sale, over 350,000 people have pre-registered for the phone.

It's no secret that devices leak data, but sometimes they do so in ways you may not expect. Your phone, laptop, printer, and IOT devices leak Wi-Fi information that can (and is) used to track you.
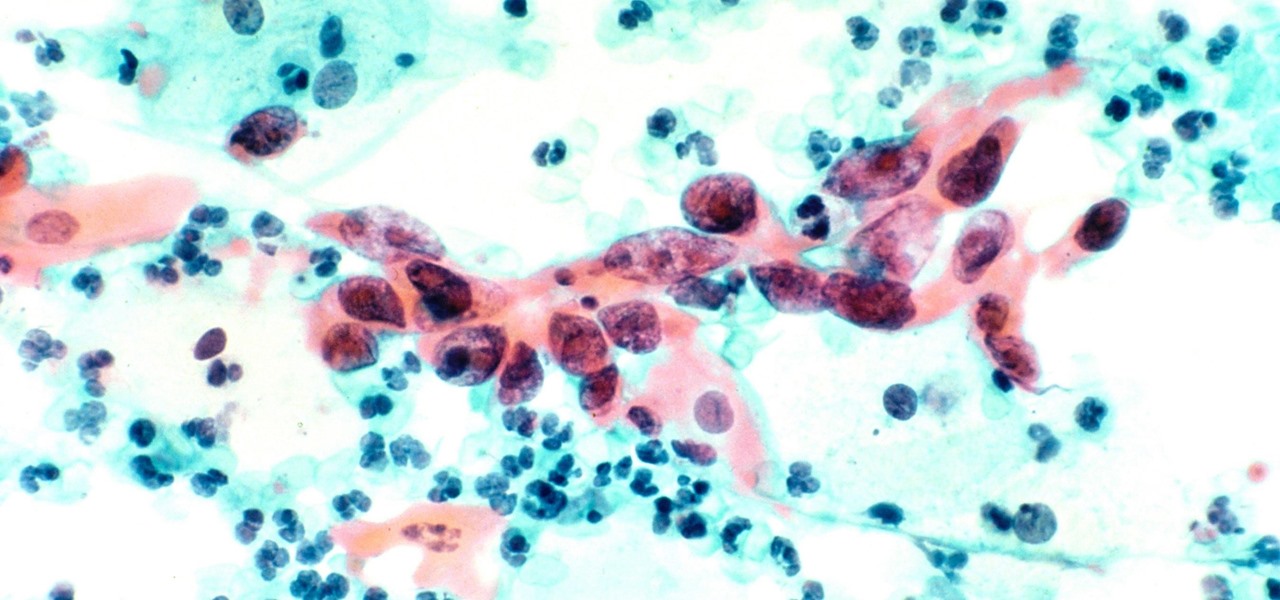
Usually, we think of vaccines as preventative, a shot we get to prevent the flu or some childhood disease like measles or mumps. But there are vaccines for other purposes, such as the ones studied by researchers from the Netherlands.

Responding to the emergence of Zika in the US, researchers investigated what type of repellent works best to reduce your odds of a mosquito bite from Aedes aegypti, the mosquito species that spreads the Zika virus.

I mentioned in one of my earlier articles something about ghost hackers, and very shortly stated a thing or two of what they do.

Before I continue with a topic on strings, we first require some fundamental understanding of how memory works, i.e. what it is, how data looks in memory, etc. as this is crucial when we are analyzing vulnerabilities and exploitation. I highly suggest that your mind is clear and focused when reading the following article because it may prove to be confusing. Also, if you do not understand something, please verify all of your doubts, otherwise you may not completely understand when we touch on...

Mirror, mirror on the wall, who is the fairest of them all? Besides being one of the most notorious misquotes of all time (the line is "Magic Mirror on the wall, who is the fairest of them all"), it's a question that men and women probably have asked themselves more than once.

Imagine that Tinder fornicated with Facebook and had a baby. The product of that union would be the hideous, yet overwhelmingly interesting SocialRadar, an app dedicated to stalkers and stalkees.

It's rare that a developer listens to the wishes of the masses, but that's exactly what CyanogenMod has done with their new CyanogenMod Installer, which automates the entire ROM installation process on your HTC One or other Android device. Previously, upgrading from the stock HTC One ROM to CyanogenMod required an unlocked bootloader, a custom recovery, the latest CM version, and Gapps. Let's be honest—unlocking the bootloader is a pain the ass, and probably the only reason stopping most peop...

Sometimes, doing the right thing is way more difficult than it should be, like trying to return a lost smartphone. Despite having the best intentions, it's often hard to track down the rightful owner, especially if the device is armed with a passcode. On the other hand, there are plenty of people who see an unattended iPhone or Samsung Galaxy S3 as a chance for profit. In 2011 alone, the number of lost and stolen cell phones in America was worth over 30 billion dollars. That's right, billion....

Video: .
When LinkedIn first arrived on the scene, I thought it was a great resource for staying connected and getting in touch with those people in your desired career path. Keyword: Thought. Like most businesses, money and shareholders seem to have taken over the driver's seat, pushing the company towards a business-first, users-second approach.

Living in Los Angeles has taught me one thing—parking is a luxury. If you are lucky enough to find street parking anywhere near your desired location, do not pass it up thinking you will get an even closer one. It does not exist. Looking for free parking? Get real. You can't even park at a busted meter in Los Angeles, despite state law saying otherwise. Now, finding a good parking spot is not just relevant for Los Angeles, but for other large cities and any other crowded areas, be it a shoppi...
This most recent school shooting, one of the worst in history, has devastated our country. That such an act can be performed not by a begrudged child, but by one or more adults, is nearly unthinkable.

TIFF 2012 Wrap-Up - Pounds Personally Gained: 4.5

Until recently, brainwave-reading devices have pretty much only existed in science fiction. Sure, electroencephalography (EEG), the technology that powers these devices, has been used in medicine and psychiatry since the late 1800s, but diagnosing people's brains and reading their minds are two totally different things. The first EEG headsets available to the public were used mostly in gaming and even in fashion, but in the last few years, they've gotten a little more sophisticated.

In addition to being a great way to share content and information that are also using Google+, additional sharing features in Google+ allow you to send content and information to other individuals who do not use the service. You can even import your address book to make sharing even easier.
The Google+ Sparks feature is a kind of social search that allows you to find and read different articles and websites that have been selected by the people you follow and other Google+ users. It can help you find interesting posts and information on a specific topic.

Hack a pair of sunglasses to secretly record audio and video and spend less than $40 in the process with this how-to video. To replicate this hack for yourself, you will need a spy camera and black solar shield sunglasses. For detailed, step-by-step instructions on building your own spy recorder sunglasses, watch this hacking how-to from Kip Kay of Make Magazine.
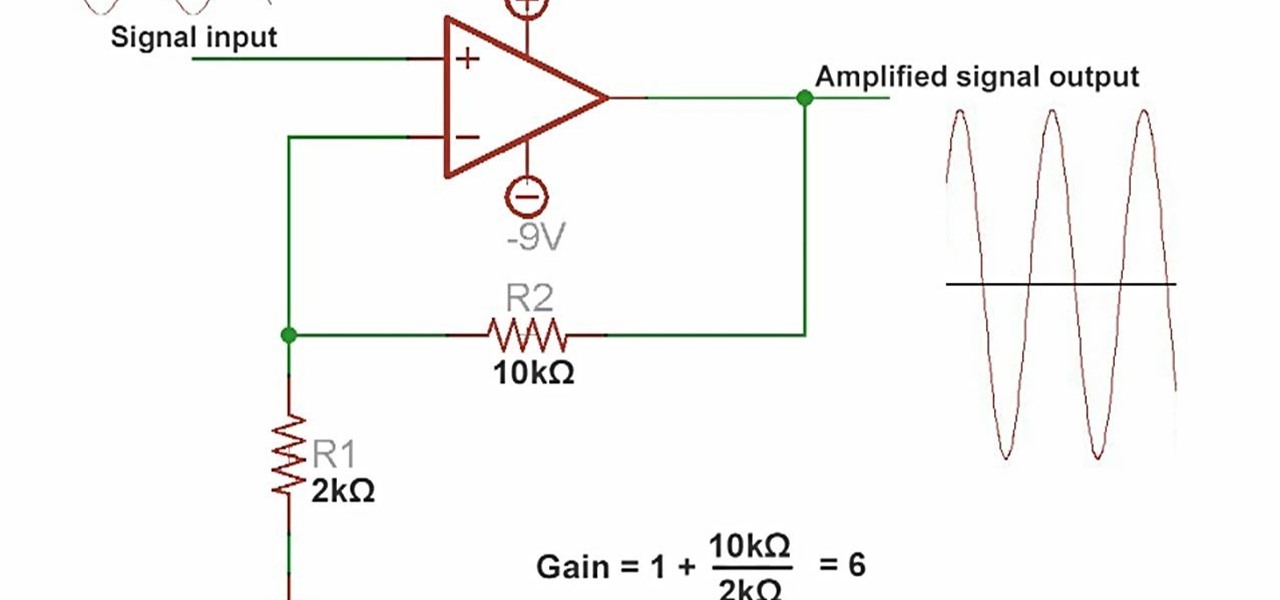
An amplifier is something that amplified the voltage on a circuit. The most basic kind is an operational amplifier, and this video will show you how these work and how to use them in your electronics. As an example you'll learn how to make a microphone circuit for spying on people or listening to your heartbeat.
The Bruno Mars single "Grenade" is taking him to a whole 'nother level of stardom, especially in light of his amazing performance at the Grammy's. This video will show you how to play a cover of the song on acoustic guitar and woo yourself some people.
Lots of people have problems with XBox Live matchmaking due to the NAT for their network not being Open. It's not readily apparent how to make your NAT open, but this video will show you how to do it.

The Assault class in Battlefield Bad Company 2: Vietnam is a nice simple class that can kill people quickly and support your team by providing them with extra ammo packs. This video will teach you some strategies for dominating as the Assault and also analyze the different weapons you can choose for the class.

Firesheep is a packet sniffing browser exploit that can access the exposed accounts of people on Facebook and Twitter while they use public Wi-Fi connections. This video shows what steps can be taken to protect yourself against someone accessing your Facebook account.
One of the greatest tools of email scam artists is spoofing, the process by which you can send emails that appear to come from a different account than the one from which they were sent. This video will explain spoofing to you, how to do it, and how to tell if a message you've received has been spoofed and avoid it.
The Amazon Kindle 2 has changed the way millions of people read books, but many of you aren't taking full advantage of your device's many advanced features. This video will show you how to use some advanced features of the Kindle 2, including how to highlight text, annotate text, and add a bookmark.

Sure, the iPhone is a phone, but why use your phone service to call people when VOIP is cheaper? This video will teach you how to use a new App called Viber to make free VOIP calls on the iPhone.
Magic tricks that will work well in crowd on drunk people are some of the most useful ones you can learn, and this trick is that in spades. It's called Healed n' Sealed, requires the construction of a trick can, and you will learn how to do it in this video.

Are you the kind of person who's always looking for a new way to scam people into buying them beer with one-sided bets? Then this is right in your wheelhouse. Watch this video to learn why it is impossible to blow a folded bottle cap into a bottle from it's rim and how you can use this to trick bar patrons and partygoers.

Glowing substances have always held a powerful appeal to people, and making new ones can be a lucrative business. If you need some glow powder for a project of yours, watch this video to learn how to make DIY glow-in-the-dark powder out of normal household chemicals.

Most long-haired men and women in America have a hair tie on them most of the time, sometimes more. All you need are two different-colored ones to do this awesome mind game / bar trick on someone! It involves tying the two ties together surreptitiously, and you'll learn how to do it in this video.