
How To: Perform the Top Pop card trick
A tutorial for performing the Top Pop card magic trick.


A tutorial for performing the Top Pop card magic trick.

Learn how to perform a classic magic trick known as the Cups and Balls, and throw in a potato while you're at it.

Learn to perform the paper clip card magic trick.

Chuck "The Reverend" Grigsby explains how to perform a Kimora from guard with TJ "Da Spider" Obrien and Fernando "The Real Deal" demonstrating.

Perform a simple magic trick in which you appear to make a ring teleport from one hand to another.

Perform a magic trick in which you appear to tear a cigarette in half and magically put it back together.

Learn how to perform multiple dribbling moves in order to increase ball control when playing soccer.

Learn how to perform fascia stretching on the neck with Massage Nerd.

This video is a demonstration of how to perform the Greek rhythm sirto with buzuki ensemble. This video is primarily a performance demonstration, however, everyone's role in the ensemble and how they relate to the rhythm is very clear.

This video is a demonstration of how to perform the Greek rhythm Haftalik with a buzuki ensemble. This video is primarily a performance demonstration, however, everyone's role in the ensemble and how they relate to the rhythm is very clear.

You can learn how to perform a headspin which is a break dancing move. This is one of the more dangerous dance moves. You stand on your head and use your hands to spin yourself around in circles. Unless you understand Japanese, this video doesn't really help you learn anything.

Determining the antivirus and firewall software installed on a Windows computer is crucial to an attacker preparing to create a targeted stager or payload. With covert deep packet inspection, that information is easily identified.

Android phones have supported keyboards and mice for a long time, and you've even been able to use physical keyboards with iPhone and iPad models. But iOS 13 and iPadOS 13 finally include official mouse support. That means you can use a wireless or wired mouse and keyboard with your iPhone or iPad, though, a futuristic peripheral that combines the two may be even better.

So you can't seem to win in Mario Kart Tour? Whether it's your first game in the Mario Kart series or not, Mario Kart Tour can be challenging, especially when you don't know the tracks. Instead of struggling your way through the cups, try out these five tips to get a leg up.

The art of privilege escalation is a skill that any competent hacker should possess. It's an entire field unto itself, and while it's good to know how to perform the techniques involved manually, it's often more efficient to have a script automate the process. LinEnum is one such script that can be incredibly useful for privilege escalation on Linux systems.

A powered-off MacBook can be compromised in less than three minutes. With just a few commands, it's possible for a hacker to extract a target's password hash and crack it without their knowledge.

While the iPhone XS and XS Max come equipped with 4 GB of random access memory, and the iPhone XR with 3 GB of RAM, Apple's latest flagships are still susceptible to occasional slowdowns in performance in iOS 12. This can be fixed by clearing RAM, but the process is now a little trickier compared to iPhones with Home buttons.

With all the web applications out on the internet today, and especially the ones built and configured by novices, it's easy to find vulnerabilities. Some are more perilous than others, but the consequences of even the slightest breach can be tremendous in the hands of a skilled hacker. Directory traversal is a relatively simple attack but can be used to expose sensitive information on a server.

Passwords and data stored in web browsers are extremely valuable to hackers. If not for financial gain, black hat hackers may still leak your passwords and personal information for amusement. Never undervalue what you're worth to a hacker.
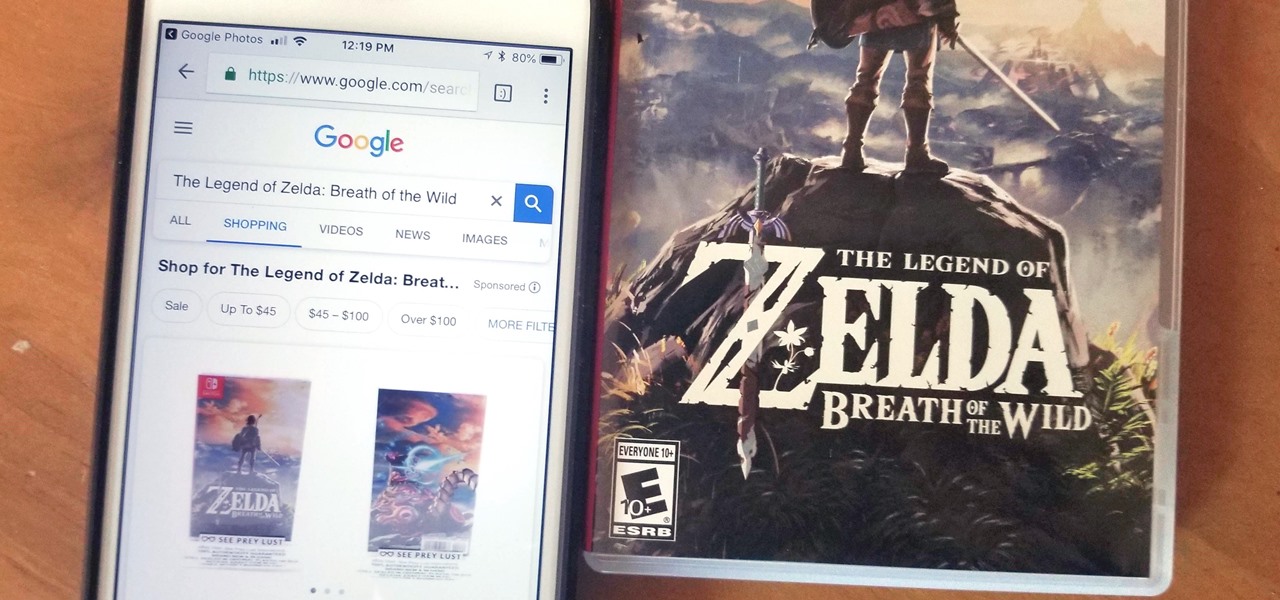
Google Lens is a fantastic addition to Google Photos for Android and iOS that allows your smartphone to identify a number of things in your pictures, like landmarks and contact info. Using this power, you can even find out how to buy almost any product you've taken a photo of — you don't even need the barcode.

The key to becoming a competent white hat is knowing how the technology that you are trying to exploit actually works. SQL injection is one of the most common methods of attack used today and also one of the easiest to learn. In order to understand how this attack works, you need to have a solid grasp of ... you've guessed it ... SQL.

Since its introduction, the Bixby button has been a big point of contention among Galaxy fans. Many view the dedicated button as a wasted opportunity, which they argue could be put to better use if Samsung would let them use it for other commands. Thanks to an awesome app, you'll be able to remap the Bixby button on your Galaxy S9 to perform almost any function.

As smartphones become more accessible, billions of people have come to depend on their features for daily life. One of the most important aspects these days is the camera. OEMs have been working for years to improve camera quality, and they seem to have finally figured it out — the best way to achieve DSLR-quality photos wasn't just with better sensors, but with better intelligence.

Because of the way Google Play works, Android has a "bad app" problem. Google allows any developer to upload an app to the Play Store, regardless of if it works, how it looks, or whether or not it can harm users. Malware scanning happens primarily after apps are uploaded, and though Google has recently taken steps to safeguard users with its Play Protect program, you don't have to depend on them.

The Samsung Galaxy S8's almost bezel-less display is truly a sight to behold, especially when set to Immersive Mode. While transparent when on the home screen, the navigation and status bars on the S8 will often turn opaque depending on what app you're using at the moment. This, in turn, can detract from the overall experience when viewing anything from the S8's display, as the bars along the top and bottom of the screen bump the phone's aspect ratio down to lower levels.

The international, Exynos-powered Galaxy S7 and S7 edge have had a working root method ever since a few days after release. But the North American variants—those using Qualcomm's Snapdragon 820 processor—have locked bootloaders, and have proven to be almost unrootable up until now.

Welcome back! In the last training session we covered how to write and execute scripts. But today we'll be getting back to the code!

Let's say you're flush with Google Opinion Rewards credits, or you just got a Google Play gift card for your birthday. This is a perfect opportunity to remove ads and unlock new features by upgrading some of your free apps to their paid counterparts, or to finally purchase that app you've been lusting after that doesn't offer a free version.

It's no secret that exercise is good for you, but you may be surprised to know that a good workout can actually boost your memory, too. They key to giving your body and your brain muscles a good workout is by adding more weight and pushing hard for an extra 20 minutes.
No one wants to appear stupid. Whether you rely on lengthy, complicated vocabulary to show your smarts, or enjoy highlighting your speedy mental math skills, everyone prefers emphasizing intelligence over hiding it.
If you have a custom recovery installed on your Android device, the first thing you should have done as soon as you finished installing it was to create a Nandroid backup. But if you didn't, I'm not here to judge—I'm here to show you a much easier way.
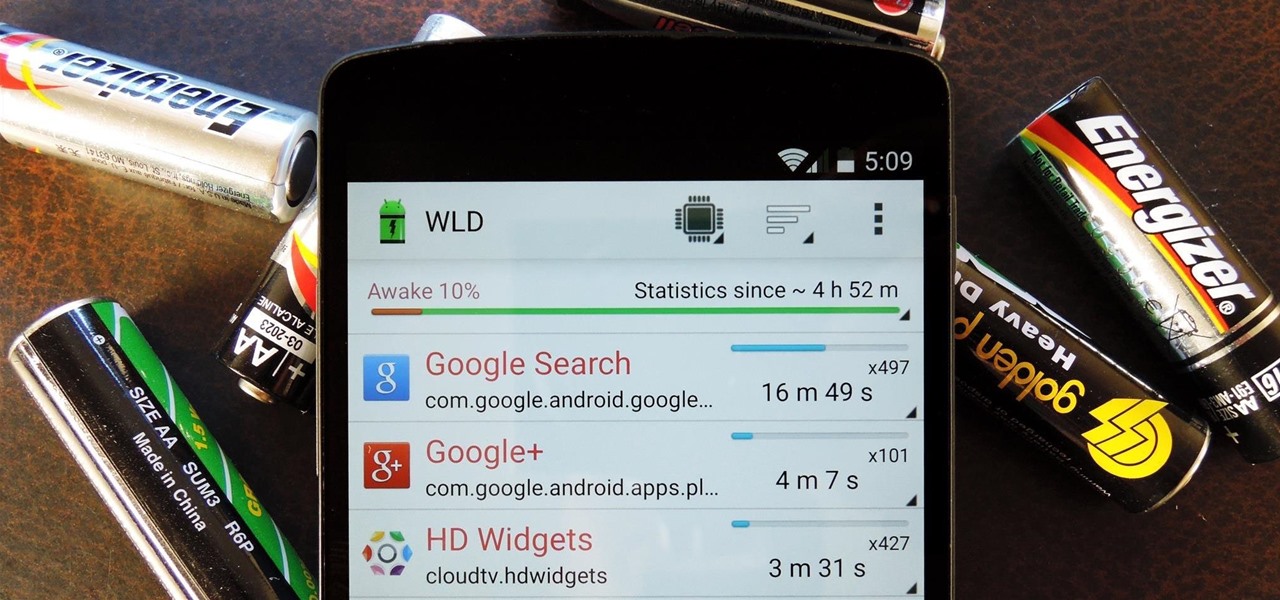
Android uses a set of permissions that apps can request to perform certain actions, and you're notified of these permissions each time you install an app. The problem here is the fact that you aren't given any built-in way to deny apps these permissions (although Danny just showed a workaround for this).

The Moto X introduced tons of cool features that have slowly been ported over to other phones, like Peek notifications and always listening "OK, Google" detection. Another such feature allows you to twist your wrist to bring up the camera app from any screen—even with the display turned off.

Will the predicted apocalyptic date—December 21st, 2012—really be the end of the world? In this ongoing five-part series, we examine what would happen if zombies, nuclear weapons, cyber wars, earthquakes, or aliens actually destroyed our planet—and how you might survive.

If you're looking to beef up your biceps, then this is definitely an exercise you'll need to perform. Watch this instructional video to see how to correctly do hammer curls sitting on a weight bench. Doing hammer curls really works out your biceps brachii and brachialis muscles.

Everyone should know basic first aid, and the hearing impaired are no different. Deaf people can save a life just like any other, so this video is designed specifically for the hearing impaired, in sign language.

Everyone should be able to perform basic first aid, even those with hearing impairment. Deaf individuals are just as likely to save a life as anyone else, but they need to know how, just like everyone else. This video is signed to help those with hearing problems learn about strains and sprains treatments. Although strains and sprains are not a serious injury, they are still very painful for the sufferer, and the only way to make sure they heal properly is to make sure they get immediate atte...

There's no getting around it: if you want to get good at playing the ukulele or any other instrument, you'll need to practice. Fortunately, the Internet is awash in free uke lessons, like this one from Ukulele Live, which make the task not only easy but fun. This clip, in particular, demonstrates how to perform old-school jazzy introductions and outros on the uke.

Looking for a sure fire way to win a bar bet? Check out this tutorial. This super easy magic trick will amaze even the most skeptical of audiences and guarantee you free drinks all night!
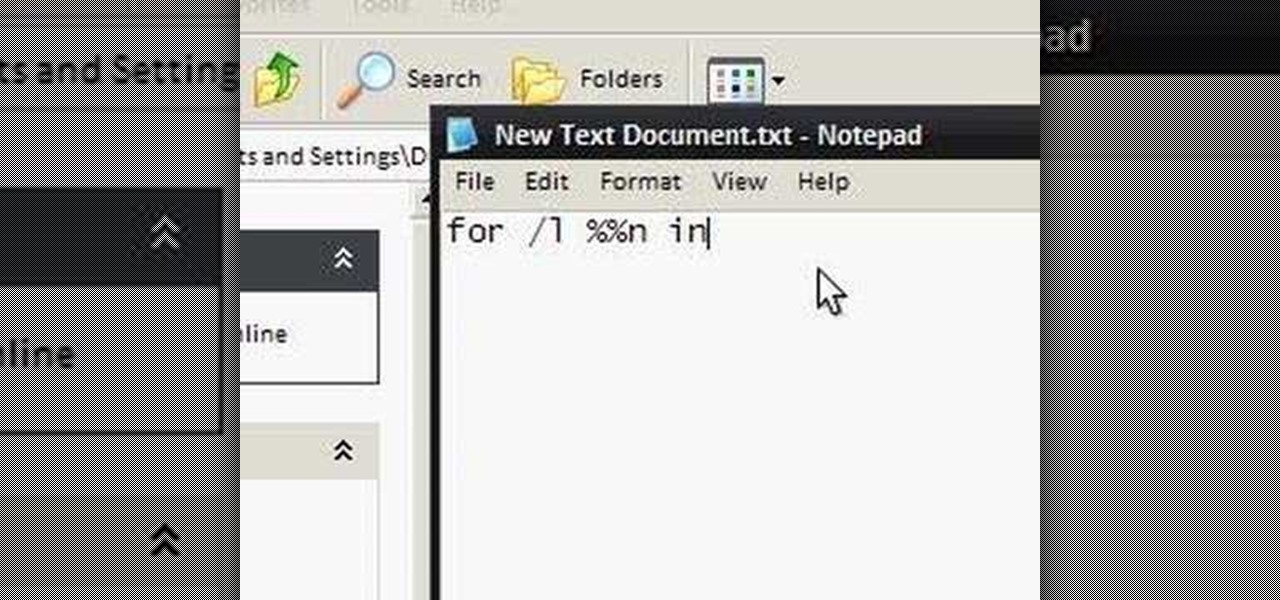
To make an annoying batch file to prank your friends you need to first right click on your screen and go to New and then Folder. In this New folder make a Text file and type in "for /l %%n in (1,1,10) DO md %%n" and that is it. Now this will loop from 1 - 10 and make a new folder for whatever n is. You can change the command if you would like to! Now, you can change this text file to 'Folder' and allow for this to be clicked. You can change the number "10" to any large number so the folder co...