The top five apps of the 2010s were all social media apps of some kind, and the fact that's not surprising to you says a lot. We may use them for other reasons here and there, but our phones are social media machines at their cores. The thing is, some make better machines than others.
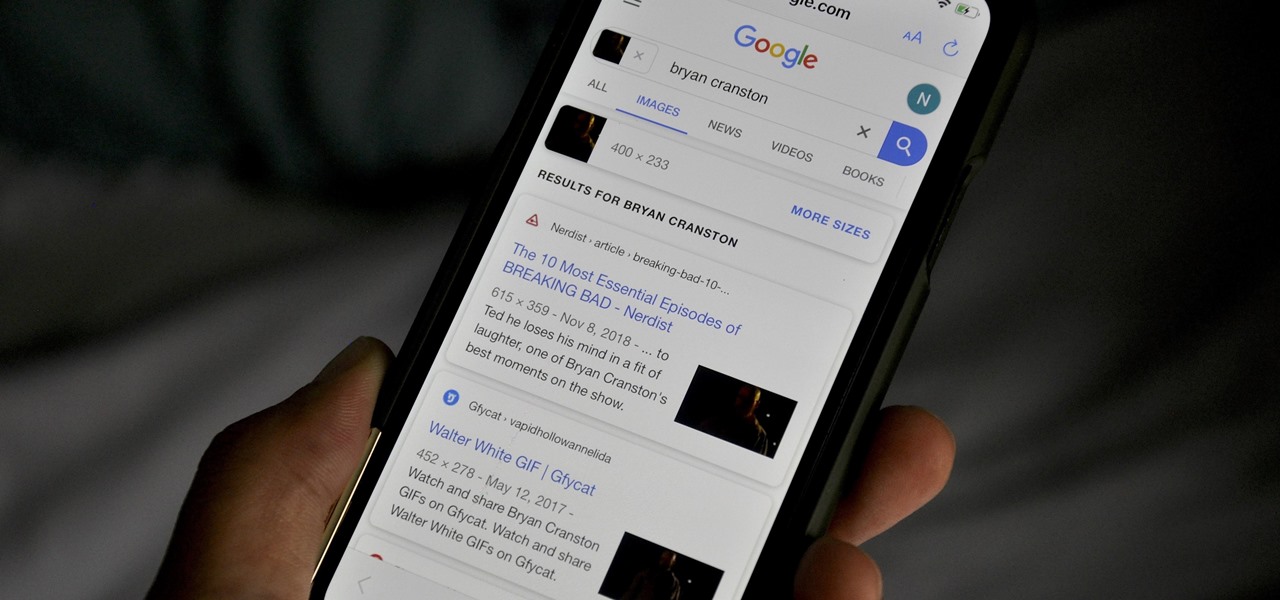
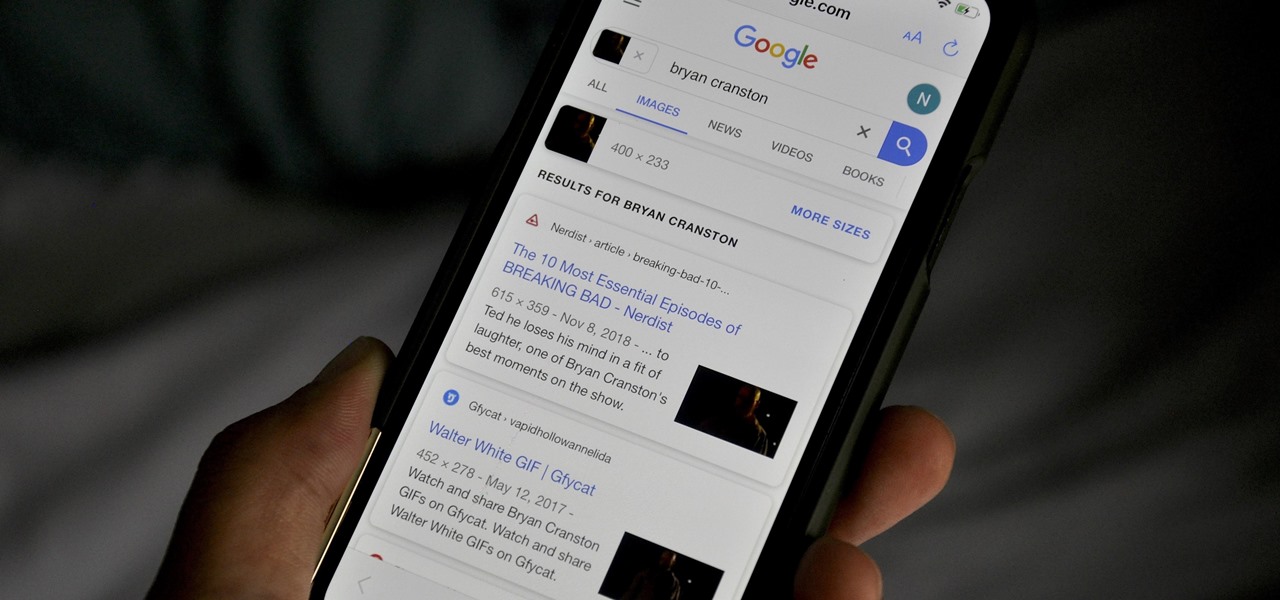
Google Images, TinEye, and other reverse image search engines can help you find where images appear on the internet. You can discover what TV show or movie an image comes from, who took a photo, and if the profile picture of someone you're talking to online is really them, among many other uses. And there's a shortcut for iOS that makes running a reverse image search easy.

A lot of time can be wasted performing trivial tasks over and over again, and it's especially true when it comes to hacking and penetration testing. Trying different shells to own a target, and testing out privilege escalation commands afterward, can eat up a lot of time. Fortunately, there is a tool called One-Lin3r that can quickly generate shells, privesc commands, and more.

In a bold move, Samsung has decided to forgo the Galaxy S11 moniker and jump straight to the S20. Perhaps it's marketing for the new 20:9 aspect ratio and 120 Hz display, or maybe it's just the fact that it's releasing in 2020.

Particular vulnerabilities and exploits come along and make headlines with their catchy names and impressive potential for damage. EternalBlue is one of those exploits. Originally tied to the NSA, this zero-day exploited a flaw in the SMB protocol, affecting many Windows machines and wreaking havoc everywhere. Here, we will use EternalBlue to exploit SMB via Metasploit.

While Microsoft dominated the augmented reality news at this year's Mobile World Congress, a small AR startup we've covered in the past arrived in Barcelona, Spain, to unveil the next phase of its mission.

The ability to stay organized and be resourceful with data gathered from recon is one of the things that separates the true hackers from the script kiddies. Metasploit contains a built-in database that allows for efficient storage of information and the ability to utilize that information to better understand the target, which ultimately leads to more successful exploitation.

One of the first steps in reconnaissance is determining the open ports on a system. Nmap is widely considered the undisputed king of port scanning, but certain situations call for different tools. Metasploit makes it easy to conduct port scanning from directly inside the framework, and we'll show you three types of port scans: TCP, SYN, and XMAS.

Using Netcat to backdoor a macOS device has its short-comings. If the compromised Mac goes to sleep, the Netcat background process will occasionally fail to terminate correctly; This leaves Netcat running infinitely in the background and the attacker with no new way into the device. As an alternative, we'll use the lesser-known Tcl shell which can handle abrupt backdoor disconnections.

The share menu is a vital part of Android that lets you send data between between apps. Many of your favorite apps support the feature, including the new Direct Share sub-menu, which can lead to a messy share menu. However, there are a number of tools to clean up this clutter, three of which don't require root.

In the Android community, there's a lot of discussion about how display notches should be used. For some, hiding the notch is more appealing, but others feel that hiding it wastes screen real estate. Well, Essential just provided another solution that should satisfy both sides.

When you don't want somebody you're calling to know the real phone number associated with your iPhone, whether it's for privacy reasons, to avoid being called back, or to prevent being ignored, there are multiple things you can do to block it on their caller ID.

Whether your palate runs to domestic or imported, a piece of cheese can be a real treat for the senses. Its smell, taste, and texture are all parts of its appeal. A big part of what makes that savory wonderfulness comes from the microbes in and on the cheese. Thanks to a team of researchers dedicated to studying those microbes, we have a better understanding of their importance to cheese and us.

One thing that I got more and more excited about as we got closer and closer to the Microsoft Build 2017 developers conference was finally learning about the new Acer Windows Mixed Reality head-mounted displays (HMD). Brandon Bray, Principal Group Program Manager at Microsoft, had teased us a few weeks earlier at the Vision Summit event in Los Angeles, California, and said there would be a lot more information at Build. Fortunately for us, he was right.

Not only has there been difficulty finding consensus on a name for driverless, autonomous, self-driving, or automated vehicles, there is also the issue of what we actually mean when we say a vehicle is self-driving, automated, and so on.

The food TV chefs prepare make our mouths water. From one scrumptious creation to another, they fly through preparation without frustration or error. They make us think we can do the same with similar ease and delectable, picture-perfect results. Some of us have noticed, though, that these TV chefs don't always adhere to the same safe food handling guidelines we've been taught to follow.

Whether you're riding the subway on your way home from work, or stuck in the backseat of the car on a long road trip, there are times when you need to entertain yourself without a mobile data connection. A good mobile game would pass the time perfectly, but not every game works without an internet connection.

Common knowledge is a funny thing: it represents a majority's opinion on a particular subject and somehow makes that opinion fact. If that 'fact' goes unopposed and unchallenged, then it is passed on and preserved from one generation to the next—regardless of whether it is true or not.

I've been involved in the Android scene for a very long time and have grown to develop a love/hate relationship with CyanogenMod. While I do like the stability they offer in their custom ROMs, they don't always include the flashy features on top of their vanilla Android base.

hello my dear colleagues, I made a visit to nullbyte and found that there is not a complete tutorial about the google dorks, so I felt the need for this tutorial, and seeing that there are many newbies around, so here's a tutorial that will teach you how to use google to hack.

A picture is worth a thousand words, and depending on what you're taking a picture of, it could be worth a lot more. Our phone's camera can easily capture high quality photos, scan barcodes, and make us Instagram famous. You can compare prices of items and download applications just by scanning a QR code. Of course, we can always do this stuff a little bit better on our iPhones.

Welcome back, my tenderfoot hackers! This is the third installment of my series on basic Linux skills that every hacker should know. Although some hacking tools are available for Windows and Mac, every real hacker uses Linux—for good reason.

You can use conditional formatting in Microsoft Excel to create an easy attendance report for you classroom. This can also be applied to other similar types of reports. The report in this video includes the names of the students, the total possible days of attendance, the actual amount of days attended by each student, the percentage of attendance, and their rank in the class. Just follow along with the video to see how it's done.

Use this method to make a glowing, burning flower similar to the glowing tomato. Makes a cool trick to impress your friends.

Ties and slurs look very similar but are not the same musical notation. This music theory how to video teaches you the difference between ties and slurs and how to play them.

A scribe is an easy way to fit material to irregular surfaces. Bob Schmidt shows you the proper way to trace using a scribe which is a tool similar to a compass.

This is basically a reverse Mill's Mess, also known as the Flipped Mess. A very similar pattern to Mill's Mess.

This is the edited version of the video that I shoot while preparing the silicone rubber layer for my homemade multitouch display. The original video is nearly two hours long so I speed up it and edited with some useful informations as titles. I hope it may help anyone who's going to prepare a similar compliant surface.

Qatayef is a traditional Arabic sweet that is served during the month of Muslim fasting, Ramadan. It is very similar to pancakes but it is filled with all kinds of treats. Two fillings are shown in this video but you may get creative and use fillings of your own.

This is a video demonstration of mid 19th Century dances. The polka-mazurka is a dance, musically similar to the mazurka, but danced much like the polka. The mazurka is a Polish folk dance.

Learn how to install a hard drive into an external casing.

Try out this basic hot milk sponge cake, which is a kind of egg foam cake, that you can use as a base for any cake art creation. It's super tasty, and you can add anything you want to it. Try it out and see for yourself.

Learn a little Swedish magic! Learn how to perform the World's Best Card Trick. If you're just starting out with your magic skills as a magician, this video will help you along your way with your illusions and tricks. See how to do the worlds best magic card trick.

Learn a little Swedish magic! Learn how to perform the World's Easiest Card Trick. If you're just starting out with your magic skills as a magician, this video will help you along your way with your illusions and tricks. See how to do the worlds easiest magic card trick.

Wax 2.0 is a high performance and flexible video compositing and special effects software. In this Wax 2.0 tutorial you will learn how to use the Quick 3D portion of the program, including how to zoom, crop and move.

Do you need to get some extra performance power out of you Windows XP pc? This video tutorial will show you how to access the control panel and make adjustments so that you can extend your RAM memory.

In this article, I'll show you how to make a portable prank stun-baton. Powered by static electricity, simply charge up the baton, and discharge it for a static surprise. The concept behind this device ties in with Leyden jars, and their tendencies to retain static electricity.

Having bills to pay is one of the worst parts of life, especially around the holidays. And if you're extremely unlucky, you might also have to pay some hefty medical bills. This can put a heavy damper on plans, wants and needs. What's worse? The people that you owe money to are pushy and always bother you to pay in a more timely fashion, or worse, pay bigger premiums.

If you’re unfamiliar with League of Legends, you’re either not into PC gaming or you haven’t spent much time on the internet. Riot Games officially released League almost two years ago, and since then it’s become a huge hit. In fact, the Santa Monica based company recently announced that the DOTA inspired game has 15 million registered users, 4 million unique logins each month, and 500,000 people playing the game at any given moment.

Like a great acting performance, making a really good game is all about choices. While creating or playing a game, those involved have to constantly make small choices that will affect the outcome, either positively or negatively. And the only thing worse than choosing wrongly is not choosing at all. Too many games, especially today, stick to what they're supposed to do from the get-go and avoid making difficult, small, meaningful choices to differentiate themselves and make their performance...