The trend of online video sharing came to the mainstream with popularization of YouTube, which let users view, submit and share video clips. YouTube started off in the year 2005, and quickly became one of the most visited websites on the internet. Sensing the emerging trend, large companies like Google joined the trail and launched their own video sharing sites (Google later bought YouTube).

Some of you may stick with your iPads, but for those looking for a similar Android version, you finally have a winner.

Downloading images from Google Images search can be a time consuming and DANGEROUS process. On more than one occasion, while trying to save the full size image and being forced to the originating website, I have accidentally come across malicious websites.

Ever hear of Spokeo? No, it's not a city in Washington state. It's a website called Spokeo.com, and it marks the complete end of privacy on the internet. If your phone number and address has been posted in a phone book, it's on there. If you own a house, chances are there's a picture of it. If you have a Facebook profile, it's probably listed.

Square dancing, a fun American pastime! Learn square dance steps with this instructional animation. Fun fact about square dancing: 19 U.S. States deem it their official dance. Square dance is a folk dance with roots in Europe, eventually spreading to the states & becoming more of an iconic dance there. Square dancing consists of 4 couples arranged in a square formation. This square dance lesson is clear and to the point. Search "square dance instructional animation" on Wonderhowto for more sq...

Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server!

Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server!

If you're interested in bypassing Windows and Linux passwords, there is a great tool from the good people at Kryptoslogic. Have you ever forgotten your administrator password? Have you ever bought a used computer with a password on it? Well, Kryptoslogic have created a boot-disc call 'Kon-Boot', which allows you to bypass any Windows 32 or 64 bit OS, as well as Linux passwords. There is both a paid and freeware version available.

Ingredients ½ teaspoon active dry yeast

Despite the fact that you may not find this as a necessity, if you do follow this quick guide, you will wonder how you ever managed before. This tutorial is based on the assumption that you're using Google Chrome, so if you aren't, I advise you to download and install it. Furthermore, this tutorial is aimed towards beginners, however advanced users may also learn a thing or two.

Here's a quick, simple prank to pull on anyone in under 2 minutes. It works especially great for someone who has tons of icons on their desktop! It makes the computer look the same, but nothing on the desktop works!

Master Figure Drawing using an Eraser Having trouble with the human form in your figure drawing class? Or just looking to impress your girlfriend or boyfriend with your art skills with a beautiful drawing of their figure? Here is a simple tip to trick your brain into using more of the right, creative, side of your brain. You will need:

In this video, we learn how to express opportunity in English using "get to". "Get to" means opportunity, which is similar to "be able to". If you use this in the present tense, you can use either "gets to" or "is able to". It's an expression of opportunity, and it sounds like a good thing. Use this in several different sentences to show your student how this phrase can mean a number of different things. To make the negative in present tense you can use "don't" or "doesn't". Don't also means ...

There are two basic ways to twist hair so that it lies on the scalp. One way to twist the hair is to section the hair into the desired size of segments. Use one hand to twist the hair with the thumb and forefinger while holding the hair down secure with the other hand. Another way to twist hair is to separate the section into two pieces. Twist one section over the other and pick up another piece while twisting the strand around again. This will feel similar to braiding, but with only two stra...

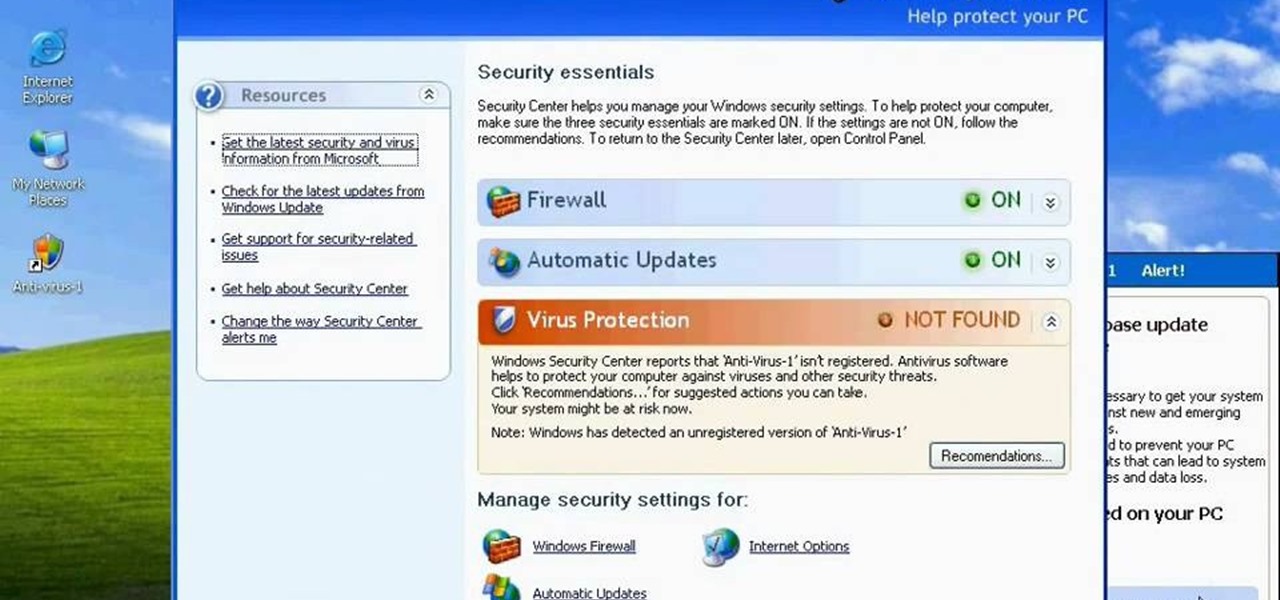
http://www.enigmasoftware.com/support... Having problems with your anti-virus software on Windows?

Who's heard of Arthur Alexander? He wrote and recorded some great songs but, ironically, it was other artists who made hits with their cover songs of his work. This is "Go Home Girl" - very similar to his other classic, "You'd Better Move On". Play a simple version in D with a touch of Ry Cooder's style on the "Bop 'Til You Drop" album.

Dolphins are some of the best, most graceful swimmers in the sea. Majestic and beautiful, they achieve both speed and form while looping from wave to wave.

Watch this instructional model making video to learn some of the pros and cons of making miniature game terrains out of wood. The wood models are certainly more durable, but they take a lot of work to build. The foam models go rather quickly and can take on more naturalistic contours. It's possile to coat wooden miniatures in plaster and texture for similar effects. Wooden miniatures are certainly more durable as outdoor and garden pieces.

Check out this video tutorial to see how to replace your rear disk, pads, and brake line on a Honda Civic EP3 (SI or SIR). This could be similar to other vehicles.

The two-step is a step found in many folk dances, and in various other dances. The Washington Post Two Step is a 19th Century name originating in the USA. It is similar to the traditional two-step dance but slowed down and a bit jumpier. This video is only a demonstration, and unfortunately it does not give step by step instructions.

This video demonstrates how to do a proper decline push-up. You need to prop your feet up on a bench or something similar 2-4 feet high. This exercise works primarily the middle and upper chest and secondly the shoulders and triceps. Do decline push-ups.

Justin Greer teaches you how to front feeble grind. This skateboarding move is similar to the 50-50 grind. You must olley and tweak your front truck over the rail. Front feeble.

Attacks against databases have become one of the most popular and lucrative activities for hackers recently. New data breaches seem to be popping up every week, but even with all of that attention, databases continue to be a prime target. All of these attacks have to start somewhere, and we'll be exploring a variety of methods to gather information on PostgreSQL databases with Metasploit.

The 2020 iPhone SE had been through the rumor mill for a long time, but Apple finally unveiled the second-generation iPhone SE on Wednesday, April 15. While it doesn't sport the 4-inch design of the original SE, it combines a small form-factor with modern specs. The big question, of course, is when and how you can get your hands on one.

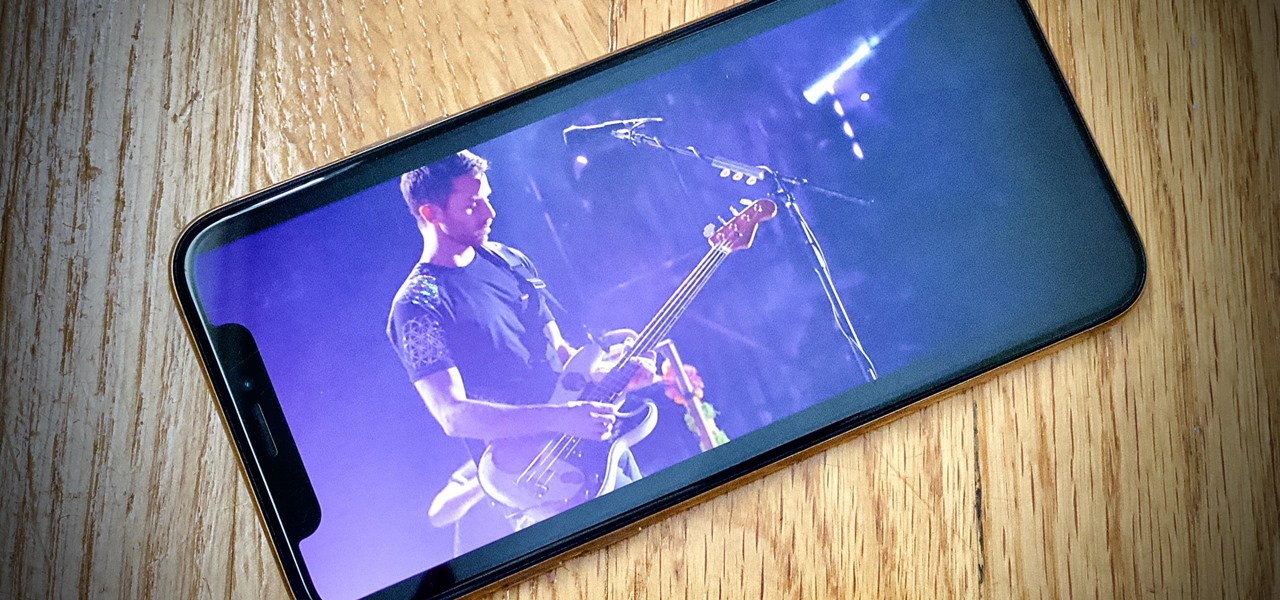
Remember concerts? Those were fun. While gathering in large groups to listen to live music might not be allowed at the moment, the live music part still is. Thanks to the internet, more and more musicians are taking the stage each day to perform for those of us stuck in social isolation due to the new coronavirus. The best part? Many of these concerts are 100% free.

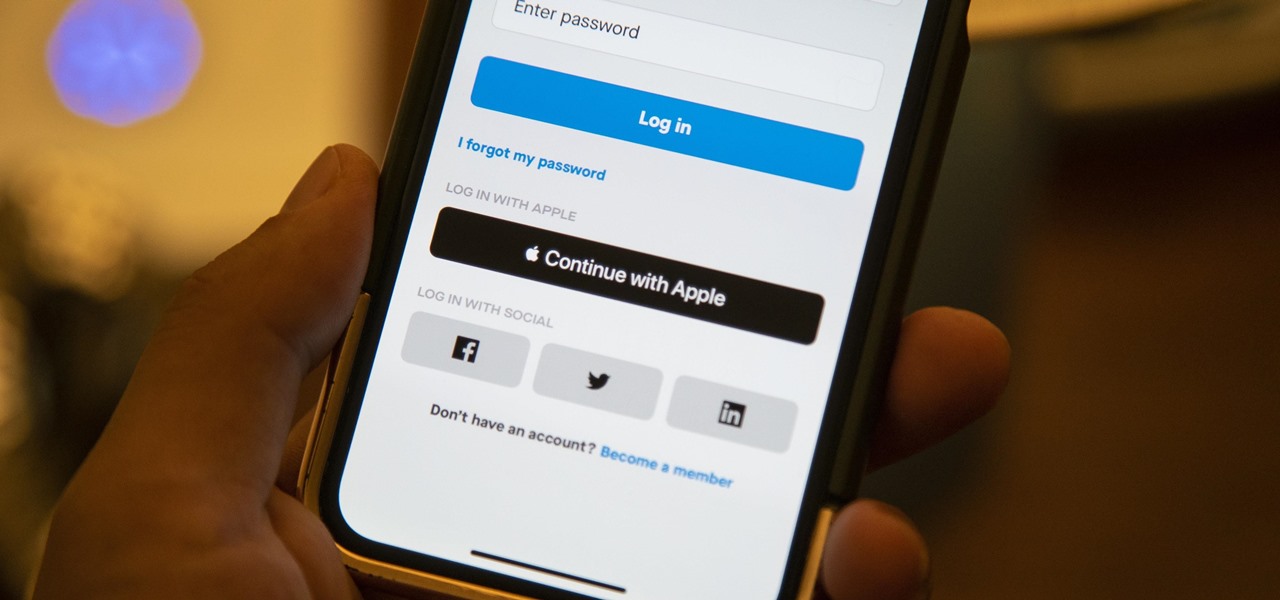
We've all seen the login pages that allow you to log in to third-party accounts using your credentials from Facebook, Google, or Twitter. It saves you the trouble of creating another account and remembering more passwords — but it can also become a privacy and security issue, which is why Apple created the "Sign in with Apple" feature for iOS 13.

So you can't figure which one to buy. It's understandable. Apple released three iPhones, each designed for a different segment of the market. But which one is right for you? The iPhone 11, iPhone 11 Pro, or iPhone 11 Pro Max? That's a good question.

So the new iPhones have arrived. Like last year, Apple released three iPhones in three different sizes that vary in price and specs. There's the base model iPhone 11, and then there are the real deal, premium models, the iPhone 11 Pro and Pro Max.

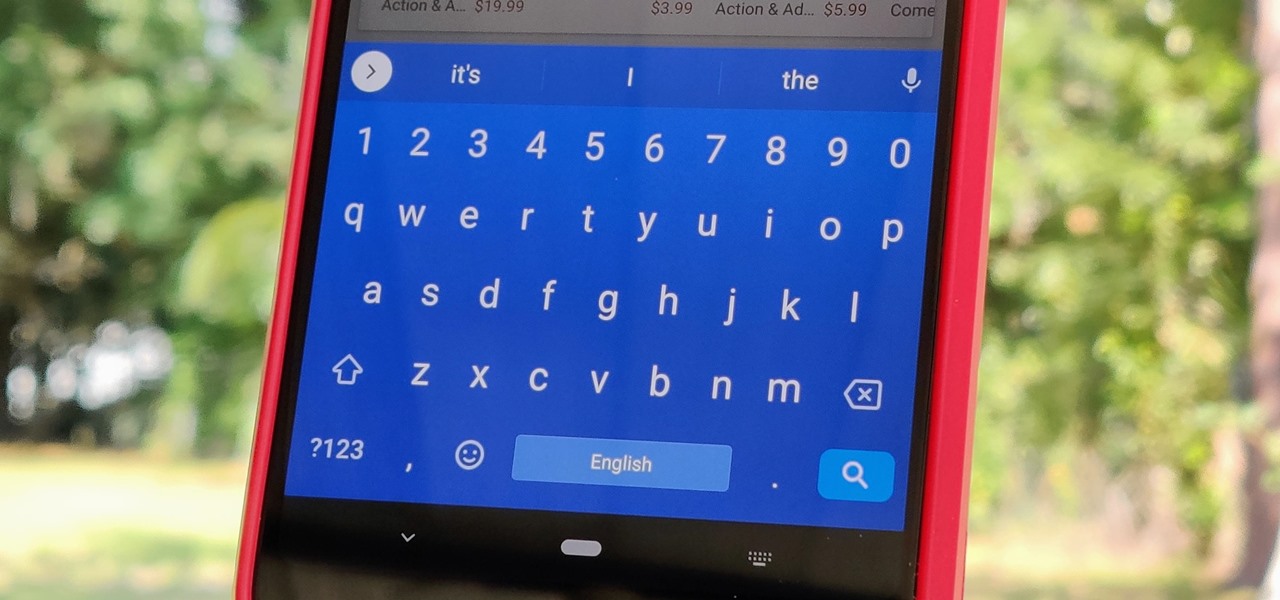
Your phone's keyboard is one of the most commonly used apps. Whether you're typing out status updates, sending private messages, or just bombarding everyone in sight with as many emoji as you possibly can, you probably couldn't get by without a good keyboard app.

While photography usually gets all the love, our phones have gotten really good at capturing video. Think about it — when was the last time you needed a camcorder for a vacation? With mobile cameras getting better each year, we're now at a point where smartphones can be used for pro-level videography.

There's a lot of misinformation about VPN services, and it stems from the fact that not all of them are created equal. Some focus on privacy, others on security, and a few VPNs are seemingly even purpose-built for the polar opposite: data collection. We made this guide to help clear the air on some of these issues while objectively ranking the best of the best.

Update: The LG G8 ThinQ has been announced. You can read all of the official specs at our full article on the new phone.

Many of us rely on our smartphones for all our media needs. Now more than ever, we're using Bluetooth connections to play audio over speakers, headphones, car sound systems — the list goes on. If you own a Samsung smartphone like the Galaxy S9, there are a number of Bluetooth tweaks and hidden tricks that can maximize your audio experience.

In July 2017, LG announced a new smartphone lineup, the Q series. These devices focus on providing some flagship features at a more affordable cost — features such as an 18:9 1080p display. LG's goal here seems to be adding value for the more budget-conscious users, and in 2018, they've continued the series with the Q7.

An incorrectly scaled object in your HoloLens app can make or break your project, so it's important to get scaling in Unity down, such as working with uniform and non-uniform factors, before moving onto to other aspects of your app.

Koadic allows hackers to monitor and control exploited Windows systems remotely. The tool facilitates remote access to Windows devices via the Windows Script Host, working with practically every version of Windows. Koadic is capable of sitting entirely in memory to evade detection and is able to cryptographically secure its own web command-and-control communications.

While there aren't as many ways to customize your iPhone like there is on Android, there are still a lot of apps out there that can help streamline and enhance your experience beyond Apple's own default options — and we've hand-picked over 100 essentials.

The public leaks of NSA tools and information have led to the release of previously secret zero-day exploits such as EternalBlue, which was used in the notorious WannaCry ransomware attack. Despite multiple patches being released, many users have failed to update their systems, so many devices are still vulnerable to these now-public attacks.

An attacker with shell access to a Linux server can manipulate, or perhaps even ruin, anything they have access to. While many more subtle attacks could provide significant value to a hacker, most attacks also leave traces. These traces, of course, can also be manipulated and avoided through methods such as shell scripting.

The iPhone X was released in November 2017, and the iPhone 8 and 8 Plus dropped right before it, but the hottest news right now revolves around the 2018 iPhone releases. The rumor mill regarding the iPhone X's successor started churning out speculations on names, cameras, display size, and more almost immediately after last year's devices, and there have been many new leaked details since.