The world of CES, the annual technology conference in Las Vegas, usually brings a few surprises, but few expected Samsung to fire off its first real augmented reality salvo at the event.

Most of us have had a cloud-connected address book for years now. The result of this is an ever-growing contact list that will continue to get harder to navigate and manage. With the increased size of our contact lists, it becomes more important to sort contacts in a way that works best for us.
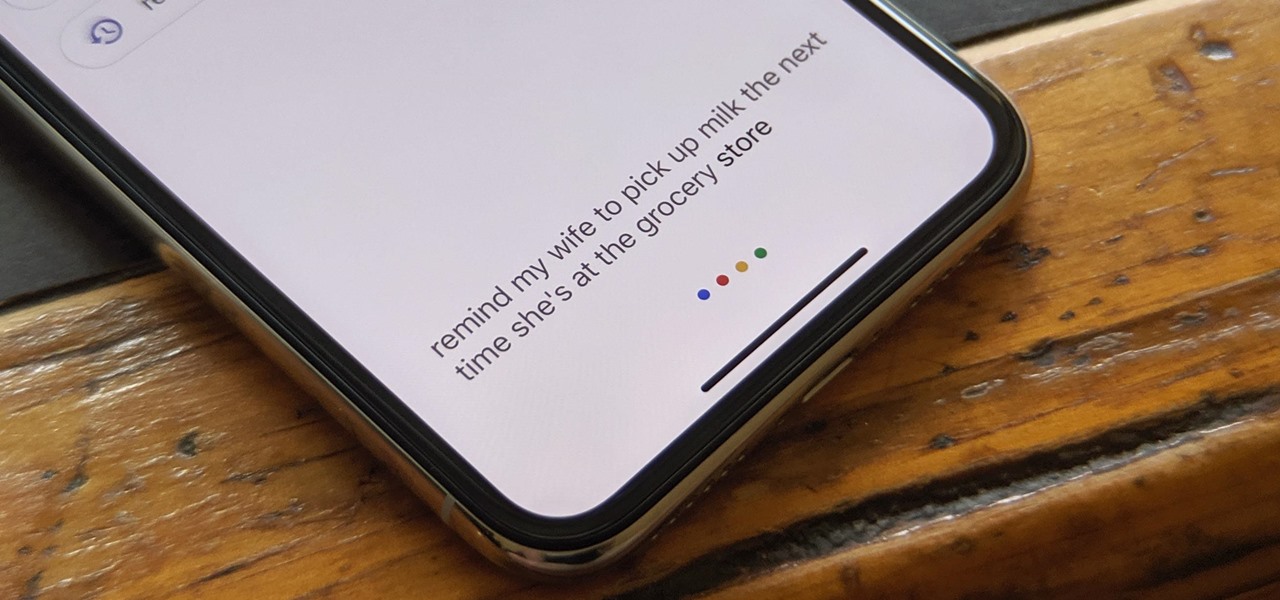
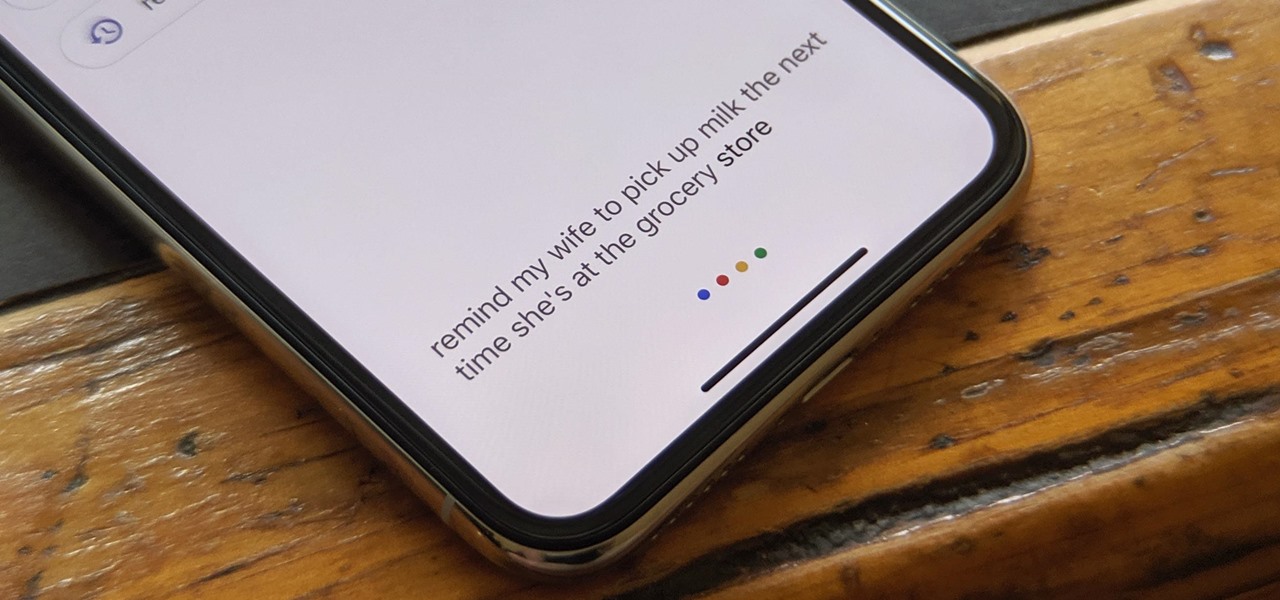
The Google Assistant is available almost everywhere. It powers smart speakers like the Google Home, it's built into Android phones, and it can even be installed on iPhones and iPads. So when Google adds a feature like the ability to send reminders to other people's Assistants, it's far reaching.

Firewall solutions for macOS aren't impervious to attacks. By taking advantage of web browser dependencies already whitelisted by the firewall, an attacker can exfiltrate data or remotely control a MacBook, iMac, Mac mini, or another computer running macOS (previously known as Mac OS X).
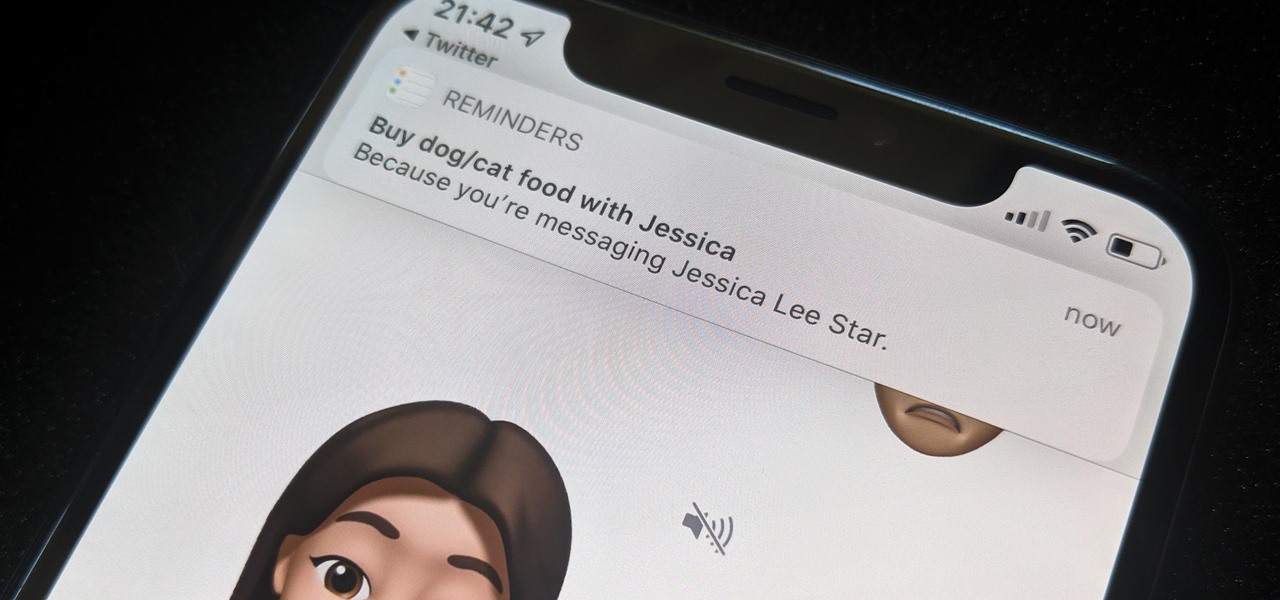
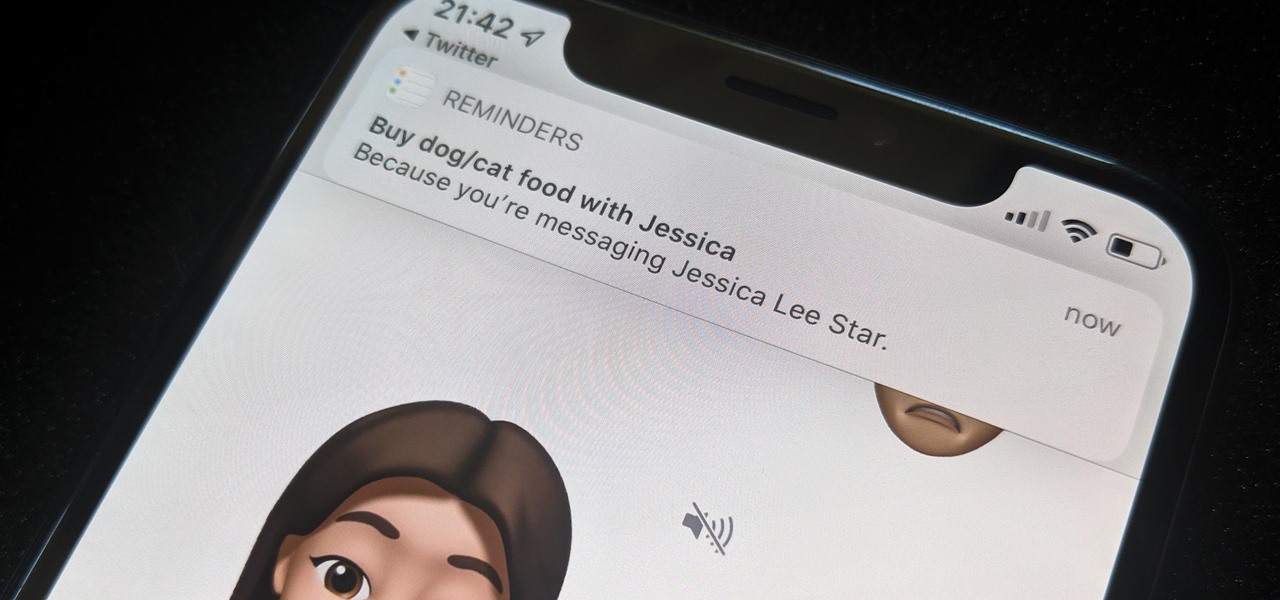
While iOS 13 might have made waves for some of its more prominent features — most notably system-wide Dark Mode — some of the more interesting tools lie with its smaller, unannounced updates. One of those updates is a new Reminders setting to tag contacts in a to-do task so that iOS pings you when texting that person in Messages.

With a simple social engineering trick, sudo passwords can be captured in seconds without the target's knowledge. The passwords can then be saved to a file or exfiltrated to another computer on the network.

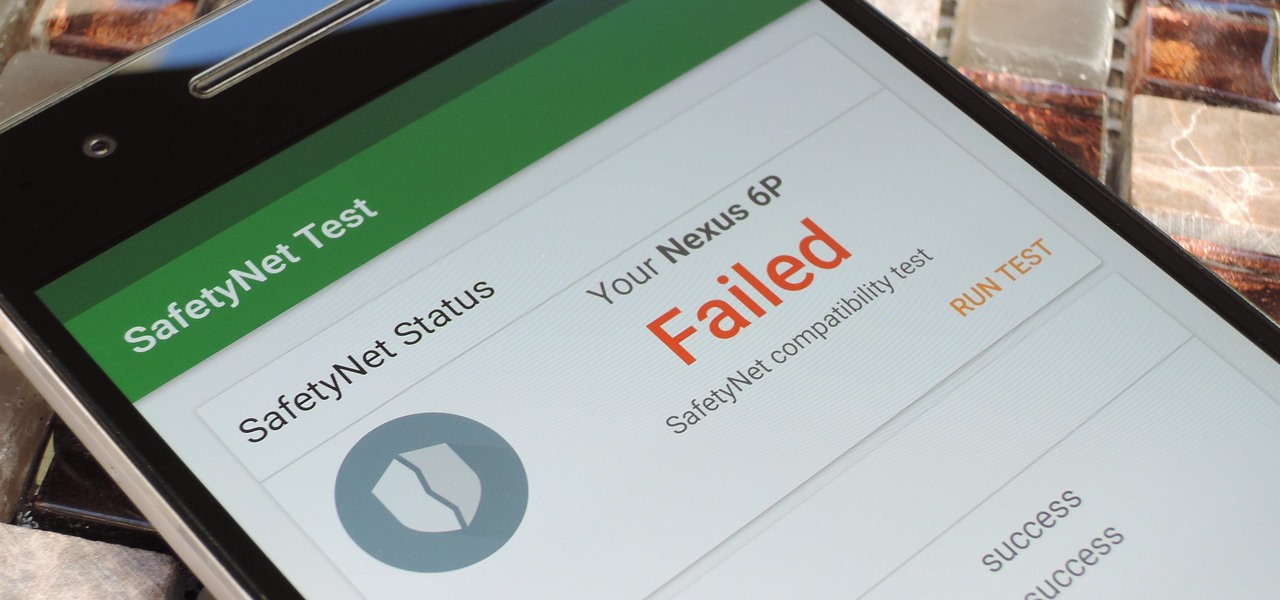
Perhaps you've thought about rooting your OnePlus 5, but thought again when you heard SafetyNet would prevent you from using apps like Google Pay, Pokémon GO, or Netflix. Those are valid struggles when you root using traditional methods. There are no such worries when using Magisk, as it masks the fact that your device has been modified.

Web 2.0 technology has provided a convenient way to post videos online, keep up with old friends on social media, and even bank from the comfort of your web browser. But when applications are poorly designed or incorrectly configured, certain flaws can be exploited. One such flaw, known as CSRF, allows an attacker to use a legitimate user's session to execute unauthorized requests to the server.

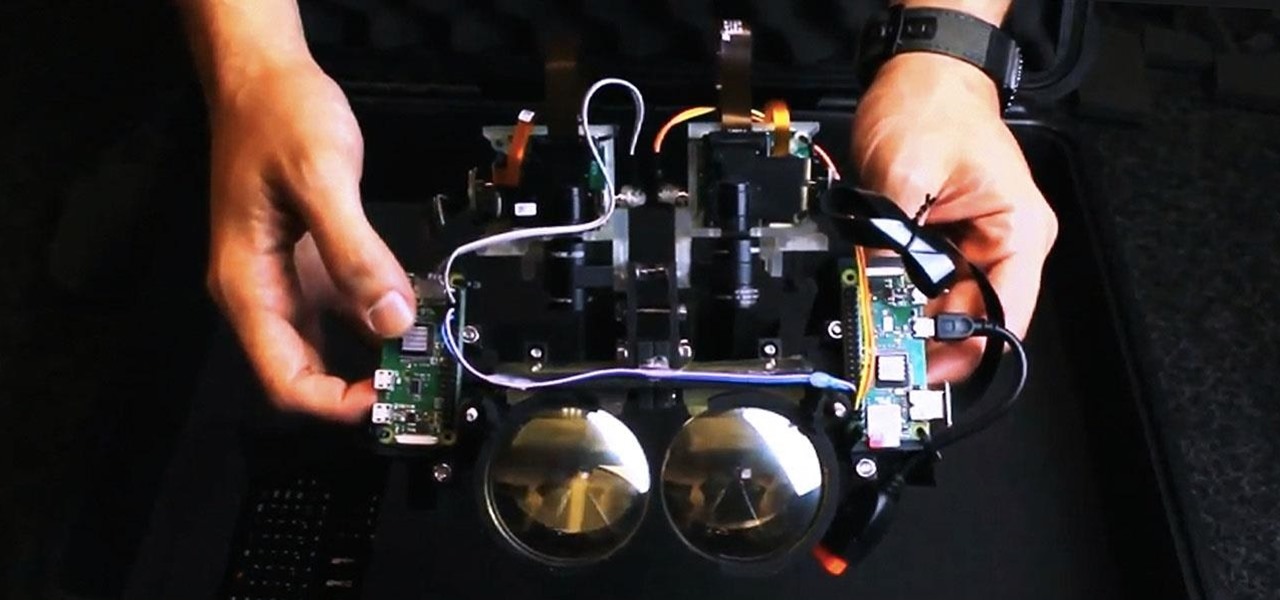
With all the hype around Magic Leap's recent launch, it's easy to forget that augmented reality hardware is still very much in its infancy. While we marvel at what is available now, researchers are still finding ways to design and produce more sophisticated components for next-generation wearables.

In most macOS hacks, a non-root terminal is used to create a backdoor into the device. A lot of damage can be done as a low-privileged user, but it has its limitations. Think twice before granting a file permission to execute — an attacker might be able to convert your harmless scripts into persistent root backdoors.

When it works, Android's Smart Lock feature is incredible. There's no need to enter your PIN when your phone "knows" it's in your hands — just unlock and go. But Smart Lock, particularly its Trusted Places feature, can be finicky sometimes.

On this, the most cherished day for Star Wars fans, May the fourth, Lenovo has released a significant new update to its Star Wars: Jedi Challenges app: real person versus person lightsaber battles.

While Apple has generally been more bullish on augmented reality as opposed to virtual reality, the latest whispers about its purported AR headset suggests that it may be giving VR another look.

Apple's iPhone X now has the power to turn anyone into a Japanese anime character, thanks to a new app that harnesses the device's TrueDepth camera.

One of the more unique aspects of Fortnite Battle Royale is the ability to create structures. Using in-game materials, players can create walls and ramps for cover and to extend mobility. But creating isn't limited to just the basic generic structures. To really maximize their benefits, great players edit their creations to fit their needs.

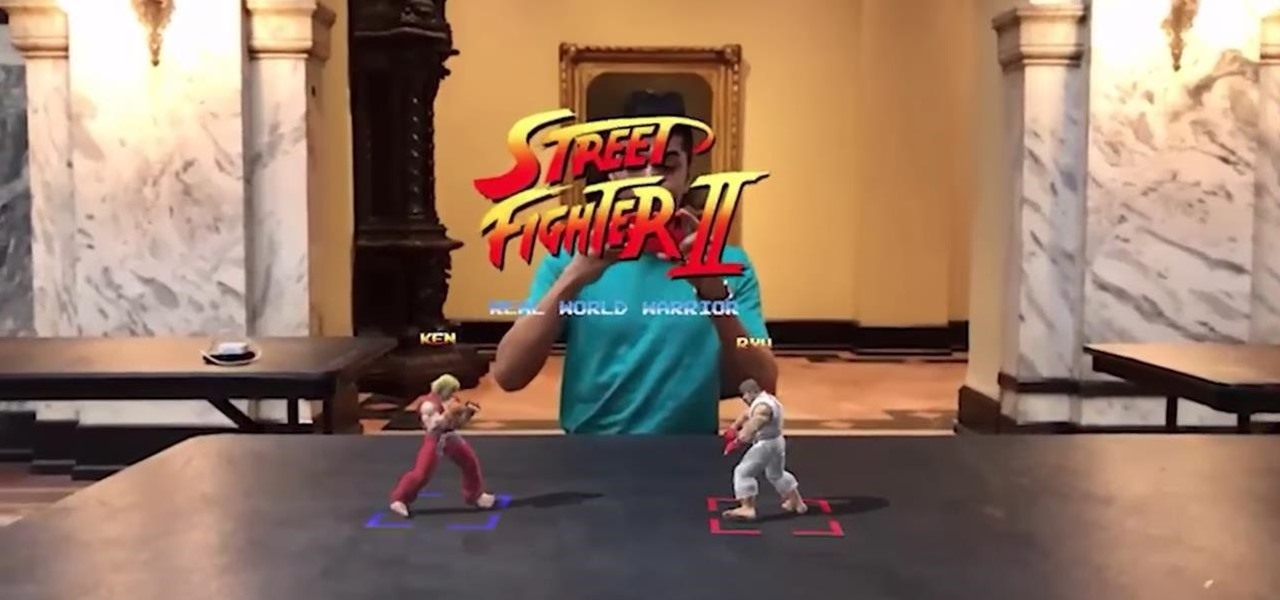
The guy who recreated Super Mario Bros. as a first-person obstacle course is back with an augmented reality take on another classic game.

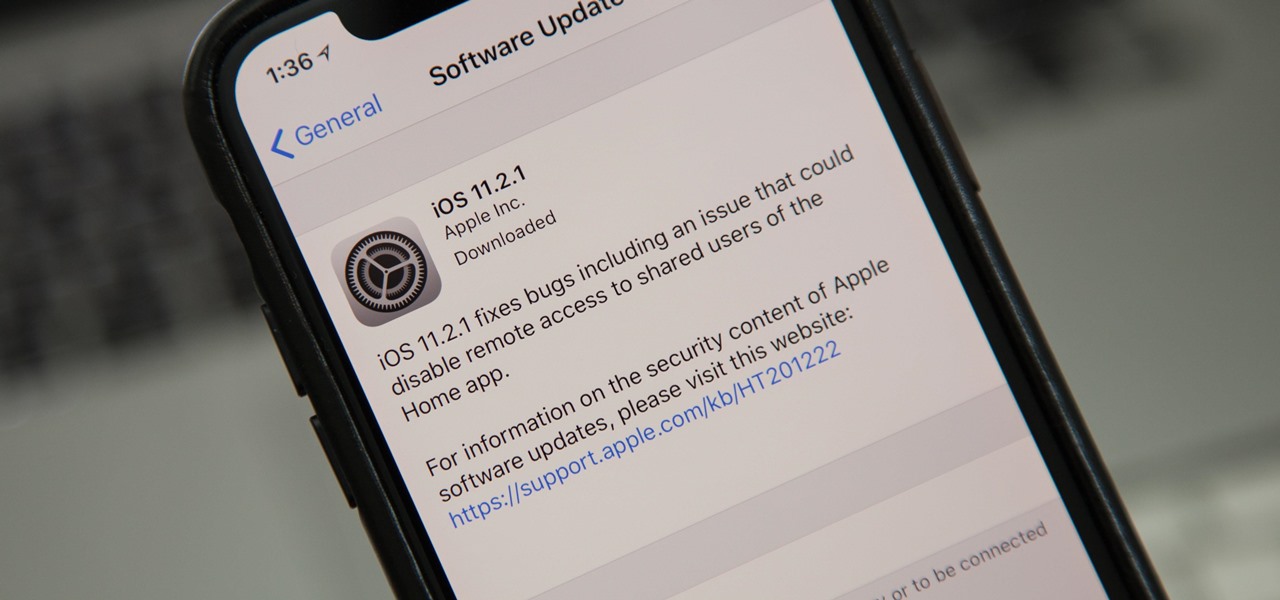
Just nine days after the official release of iOS 11.2, Apple has released iOS 11.2.1. The update initially seems to have been seeded to only a handful of users and is intended to fix bugs in 11.2.

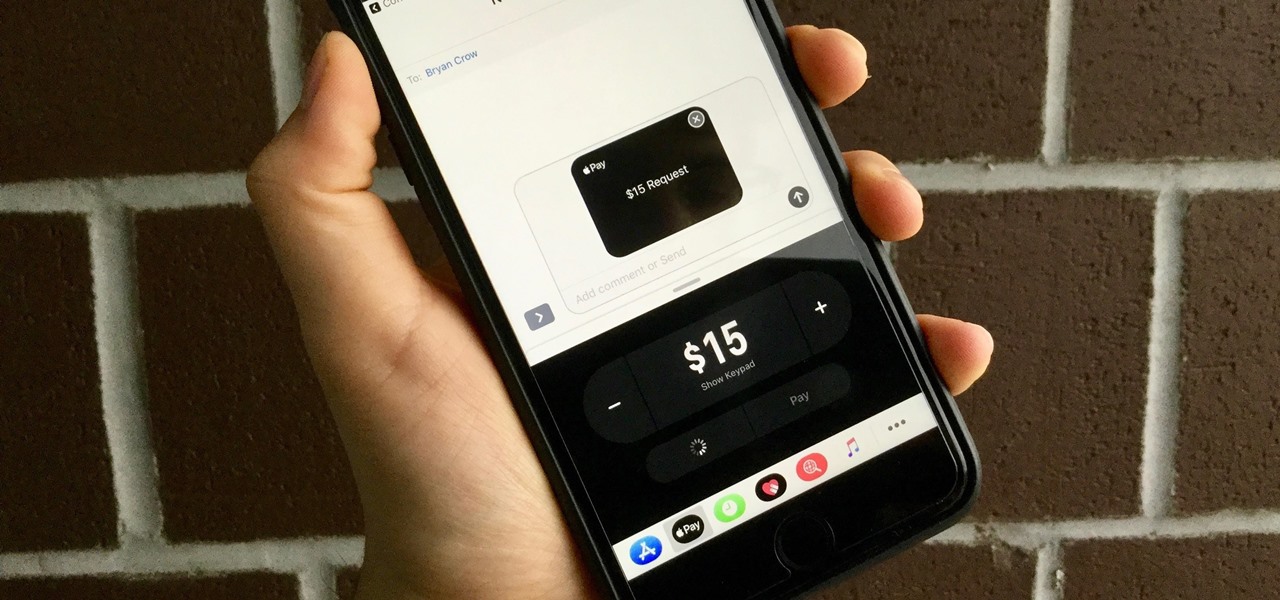
With the release of iOS 11, Apple promised to give us person-to-person transactions by way of iMessages. In the iOS 11.2 update, the new Apple Pay Cash system is now ready for you to send money to family and friends right from your iPhone — and there are multiple ways to get it done.

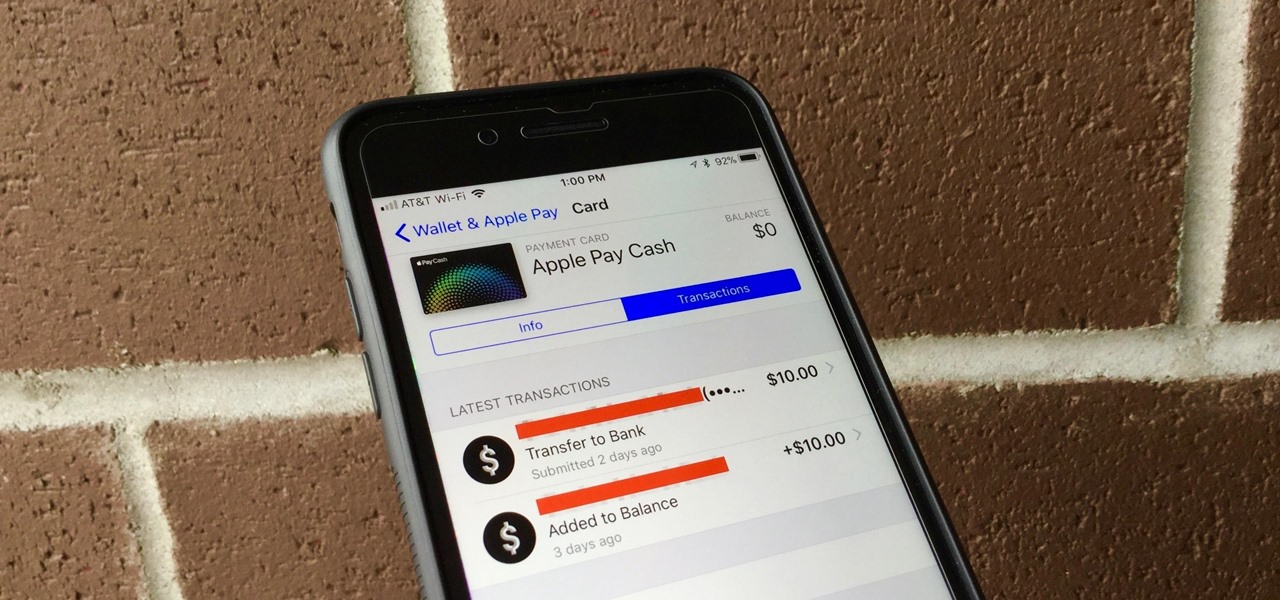
With Apple Pay Cash, sending and receiving money with fellow Apple users has never been easier. One big plus about Apple's new Apple Pay Cash card is that all of your transactions are available just a few taps away, so you can see all your person-to-person payments, balance additions, and bank transfers.

Group messages are great when you want to talk to multiple people at the same time. However, things can get disorderly real fast in the Messages app, especially if the same person is in multiple group conversations. That's where custom group names come in, which helps you make sense of all those disorganized threads with multiple names/numbers attached.

The gaming company Ivanovich Games has created a sort of "game-ception" using Apple's ARKit. They have designed a Steam-powered playable arcade machine game called "Operation Warcade" which can now be projected into real life using augmented reality, creating a true "go inside the video game" experience.

The USB Rubber Ducky comes with two software components, the payload script to be deployed and the firmware which controls how the Ducky behaves and what kind of device it pretends to be. This firmware can be reflashed to allow for custom Ducky behaviors, such as mounting USB mass storage to copy files from any system the Duck is plugged into.

Put yourself in Google's shoes: You know that business is becoming increasingly mobile, but the mobile operating system you maintain is wide open by design, and it's garnered legions of loyal fans that love to explore and exploit every aspect of it. There's a clear conflict of interest developing.

It's about time people acknowledged that judging drug users would do nothing productive to help them. In the US this week, two new programs are launching that should help addicts be a little safer: Walgreens Healthcare Clinic will begin offering to test for HIV and hepatitis C next week, and Las Vegas is set to introduce clean syringe vending machines to stop infections from dirty needles.

Nineteen days ago, several hundred people could have been exposed by a traveler with measles in Nova Scotia, Canada. The next day, someone flying from Minnesota to Nebraska may have spread the measles to other passengers. A couple weeks ago, it's possible that a man and his six-month old child spread the measles in several Seattle-based locations. Authorities are trying to locate persons who may have been in contact with these people. None of the persons with measles were vaccinated. Why?

The theme running throughout most of this year's WinHEC keynote in Shenzhen, China was mixed reality. Microsoft's Alex Kipman continues to be a great spokesperson and evangelist for the new medium, and it is apparent that Microsoft is going in deep, if not all in, on this version of the future. I, for one, as a mixed reality or bust developer, am very glad to see it.

Don't Miss: The Difference Between Virtual, Augmented, & Mixed Reality

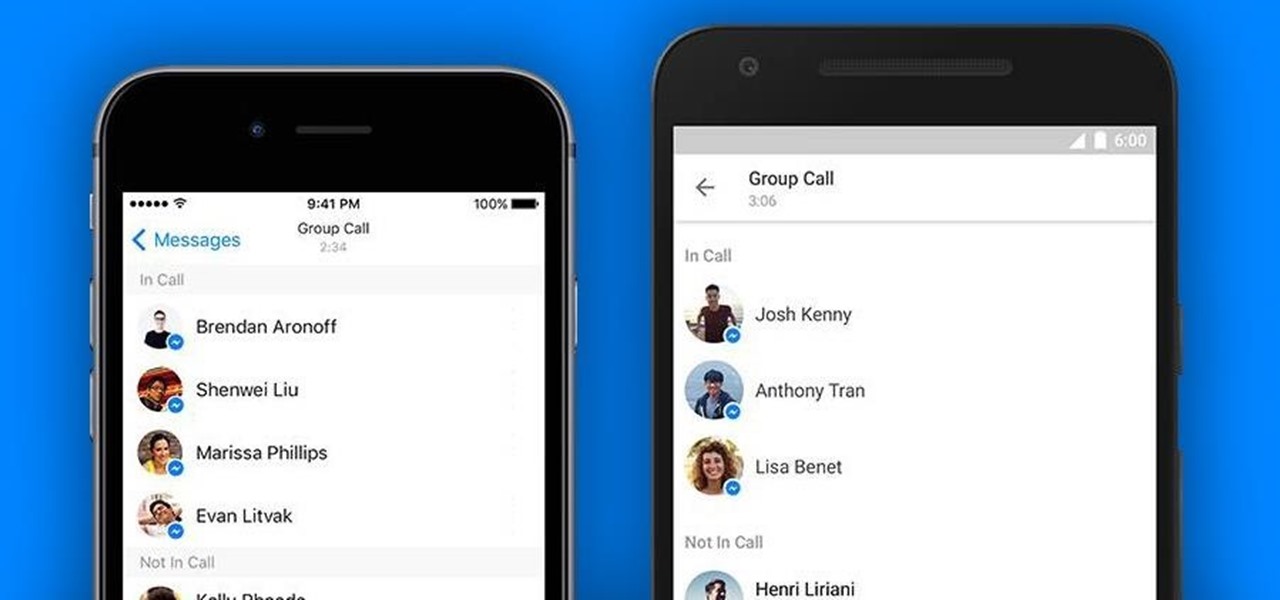
Facebook just added another feature to Messenger as part of its quest to have their service become an all-encompassing communications app. This feature lets you make free group calls using Messenger's VoIP service, and you can chat with up to 50 people at once.

One of the first orders of business after purchasing a new smartphone is to load up your shiny new toy with phone numbers, email addresses, and general contact information for all the important people in your life.

Both the Galaxy S6 and S6 Edge have had root methods available to them before the phones were even released, but the problem with these existing root methods is that they would trip the KNOX counter on your device.

UPDATE NOVEMBER 2015: The root process has changed for the Nexus Player now that the device is running Android 6.0 Marhsmallow. I've updated this article with detailed instructions on the new root process, but the video below still depicts the old process for Android Lollipop.

As much as it pains me to say it, without my phone, I would pretty much be useless. I can barely remember what I had for lunch yesterday, let alone all of the hundreds of numbers in my contact list. That's why whenever I forget my phone at home, I am pretty much stuck having to choose whether I want to be late to wherever I'm going, or feeling completely lost and disconnected for the rest of the day.

Theming and modding are a big part of the softModder community, but there are endless ways to customize our Android devices. Which ones should you download? Which ones should you avoid? It's extremely frustrating to find them all—and pick and choose.

Send an email prematurely? Forgot to attach a file? Accidentally addressed it to the wrong person? It happens to the best of us. But what can you do to get it back? Hack into the other person's email account and delete the email before they get a chance to see it? Unless you're a hacker extraordinaire, that option is unlikely. So, what can you do? If the email has already been sent, you're probably out of luck. Even if they didn't read it yet, your chances of retrieving it are slim. But some ...

All kinds of people pretend to be someone they're not on the internet, including scammers, people attempting to wind others up, hackers and web predators. Almost all of these people will leave bases uncovered and they're all easy to expose when you understand how to. Here are my favorite ways of finding out when somebody is lying quickly. Image Search

Hate answering the door, but don't trust your friends with a set of keys? This RFID front door lock made by Steve Pomeroy will solve all your party-hosting problems. It reads the RFID tags in his friends' public transit cards and decides who's allowed in based on "groups" that Steve defines. And I have to say, it's also rather stylish. It's controlled by an Arduino serial console and a custom Android app to add and remove cards. The reader can store 50 or 100 tags at a time and allows 7 diffe...

Who could forget the spectacular conclusion to the "Back to the Future" trilogy? The scene where Marty and Doc Brown use a train to push the DeLorean to 88 miles an hour so Marty can return to the 1980s has become iconic. With this tutorial, you can recreate the scene in miniature using fairly inexpensive props.

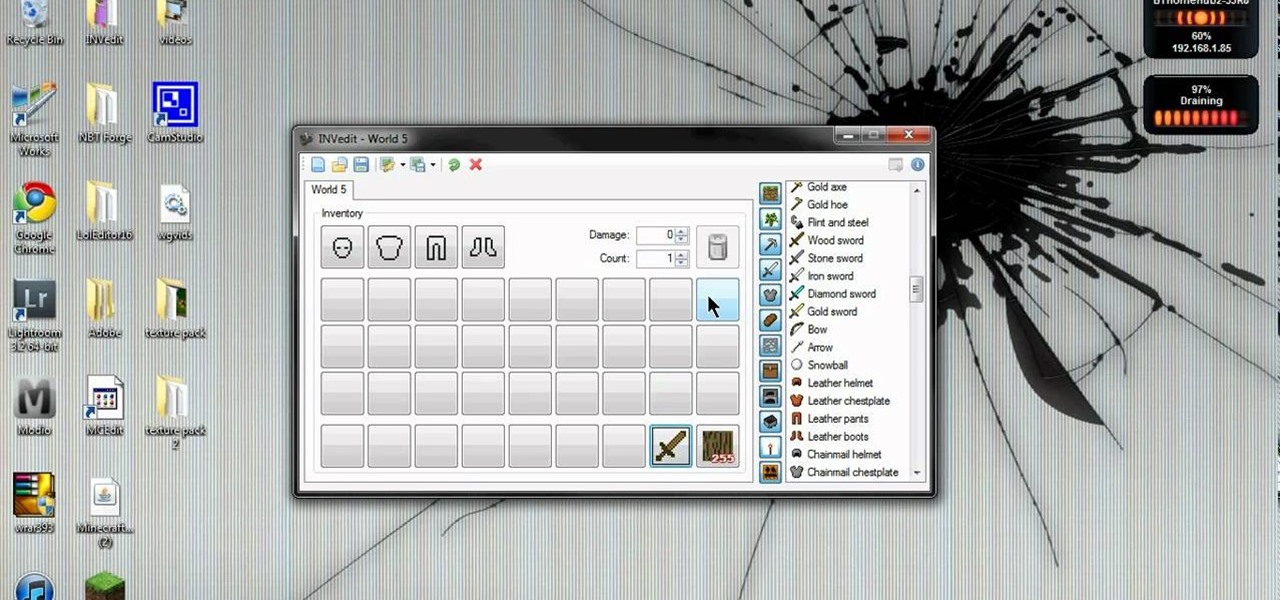
INVedit is an inventory modification program that you can use to hack into your character's inventory when playing Minecraft. Give yourself more items of one time, unlimited resources or whatever else you feel like. Fill a whole island with diamonds or TNT!

If you have already made a paper gun that can shoot paper bullets, then maybe it's time you upgraded that paper pistol with a cartridge— a holder for your paper bullets. You can modify or adjust this design in any way you see fit, to adapt it onto your creative paper gun.

This video drawing tutorial demonstrates the quick sketching of a hot anime girl character in Open Canvas. Use the method as a basic guideline for your own sketches, modifying stance, pose, proportion, and other finer details to make the work of art your own. Check out this video art lesson and learn how to draw a hot Ecchi girl on Open Canvas.